- Products
- Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- Bulgaria
- Cyprus
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
Step Into the Future of
AI-Powered Cyber Security
When the Agents Attack
A Live Look at Agentic Exposure Validation
Bridge the CAASM Gap
with Exposure Management
AI Security Masters E8:
Claude Mythos: New Era in Cyber Security
CheckMates Go:
CheckMates Fest
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- General Topics
- :
- Re: Check Point DPD (Dead Peer Detection) - Questi...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jump to solution
Check Point DPD (Dead Peer Detection) - Questions
Hi all,
I have two questions regarding the Dead Peer Detection between our Check Point Cluster and other existing VPN connections to non-Check Point Gateways.
1. Does enabling DPD (Responder Mode) has any impact on existing VPN connections? Can I enable it "on-the-fly" without having any disconnects to the VPN? I haven't found an answer on that yet.
2. If I change a VPN community with non-Check Point Gateways to "Permanent Tunnels" in order to active DPD with GuiDBedit does this have any impact on existing connections?
Thanks in advance for any help
1 Solution
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
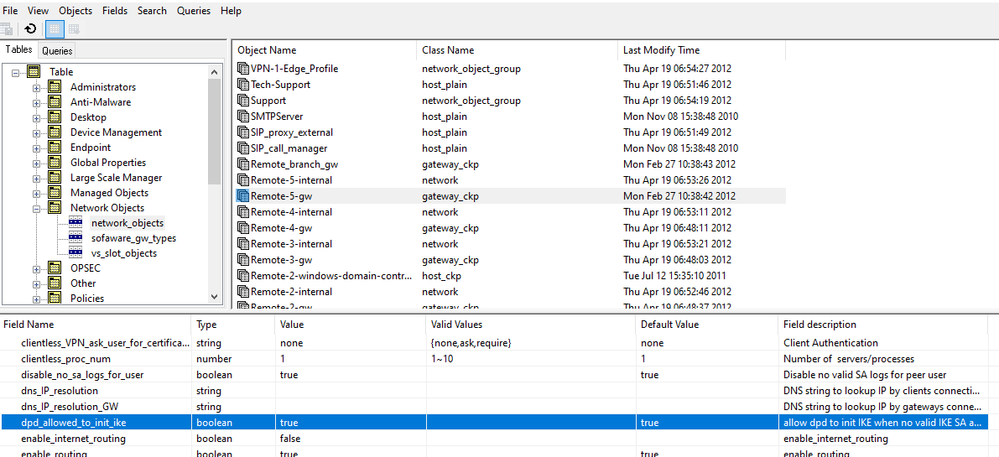
Yes, there is. You can check with the GuiDBedit tool under Network Objects >> network_objects:
I hope this helps.
13 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
quickly though:
Ad.1 - it will re-estab SA/SPI indeed
Ad.2. - it will re-estab the tunnel
ps. any changes to the proxy-id or any crypt.conf params will re-key and re-estab SA/SPI
Ad.1 - it will re-estab SA/SPI indeed
Ad.2. - it will re-estab the tunnel
ps. any changes to the proxy-id or any crypt.conf params will re-key and re-estab SA/SPI
Jerry
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the quick reply. That means that we have to announce it so that if there is any issue our partners know about it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
it will in 100% impact/affect an existing tunnel(s) so yes, that should be announced and planed for so called "maintenance window" 🙂
cheers
cheers
Jerry
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is there any way to check if DPD is enabled?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, there is. You can check with the GuiDBedit tool under Network Objects >> network_objects:
I hope this helps.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
My pleasure!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can we achieve VPN redundancy with 3rd party Gateways by enabling DPD(In R80.10 or R80.20) ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can we enable Dead Peer detection on the third party devices only? Or do we have to enable it on the checkpoint gateways also? My understanding is if enabled on the checkpoint gateways it affects all other VPNs?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can set DPD per remote gateway via the tunnel_keepalive_method variable in GUIDBedit as described in this lengthy thread, you don't have to change this value for your Check Point gateway:
https://community.checkpoint.com/t5/Next-Generation-Firewall/Enable-DPD-on-R80-20/m-p/32605
Starting in R81 tunnel_keepalive_method will be set to DPD by default on all Interoperable Device object types.
New Book: "Max Power 2026" Coming Soon
Check Point Firewall Performance Optimization
Check Point Firewall Performance Optimization
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
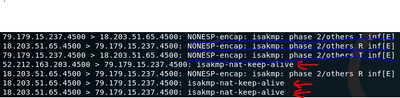
Do you know how to capture DPD packets in any way? I could see tunnel test in the logs, but seem to be missing how to spot DPD packets. I can't see them in TCPDUMP as they are encrypted. I would really appreciate some guidance on this. I am working on an AWS VPN issue where I think the tunnels are being shut down regularly and I would like to spot what is going on. I have a TAC case open but every time I ask the question they seem to swerve around it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
fw monitor should show the packets as they are encrypted/decrypted.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
AWS sends "isakmp-nat-keep-alive" packets that are outside the DPD tunnel health monitoring, please see the packets in red (the ones in blue are for the actual DPD that keeps the tunnel status up and alive)
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 8 | |
| 5 | |
| 5 | |
| 4 | |
| 3 | |
| 3 | |
| 3 | |
| 3 | |
| 2 | |
| 2 |
Upcoming Events
Wed 10 Jun 2026 @ 01:00 PM (EDT)
Deep Dive: When the Agents Attack: A Live Look at Agentic Exposure ValidationThu 11 Jun 2026 @ 11:00 AM (EDT)
Tips and Tricks 2026 #8: Say Yes to AI Without Saying Yes to RiskFri 12 Jun 2026 @ 10:00 AM (CEST)
CheckMates Live Netherlands - Sessie 47: Continuous Threat Exposure ManagementTue 16 Jun 2026 @ 05:00 PM (CEST)
Under the Hood: Check Point SASE | Internet Access Optimization & Performance TuningWed 10 Jun 2026 @ 01:00 PM (EDT)
Deep Dive: When the Agents Attack: A Live Look at Agentic Exposure ValidationThu 11 Jun 2026 @ 11:00 AM (EDT)
Tips and Tricks 2026 #8: Say Yes to AI Without Saying Yes to RiskFri 12 Jun 2026 @ 10:00 AM (CEST)
CheckMates Live Netherlands - Sessie 47: Continuous Threat Exposure ManagementTue 16 Jun 2026 @ 05:00 PM (CEST)
Under the Hood: Check Point SASE | Internet Access Optimization & Performance TuningThu 18 Jun 2026 @ 10:00 AM (CEST)
The Cloud Architects Series: Check Point WAF - The Next Generation of AI powered protectionAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2026 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
About Us
UserCenter