- Products
Network & SASE IoT Protect Maestro Management OpenTelemetry/Skyline Remote Access VPN SASE SD-WAN Security Gateways SmartMove Smart-1 Cloud SMB Gateways (Spark) Threat PreventionCloud Cloud Network Security CloudMates General CloudGuard - WAF Talking Cloud Podcast Weekly ReportsSecurity Operations Events External Risk Management Incident Response Infinity AI Infinity Portal NDR Playblocks SOC XDR/XPR Threat Exposure Management
- Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- AI Security
- Developers & More
- Check Point Trivia
- CheckMates Toolbox
- General Topics
- Products Announcements
- Threat Prevention Blog
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- Bulgaria
- Cyprus
- APAC
AI Security Masters
E1: How AI is Reshaping Our World
MVP 2026: Submissions
Are Now Open!
What's New in R82.10?
Watch NowOverlap in Security Validation
Help us to understand your needs better
CheckMates Go:
Maestro Madness
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Network & SASE
- :
- Security Gateways
- :
- Re: NAT and encryption domain
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
NAT and encryption domain
Hello,
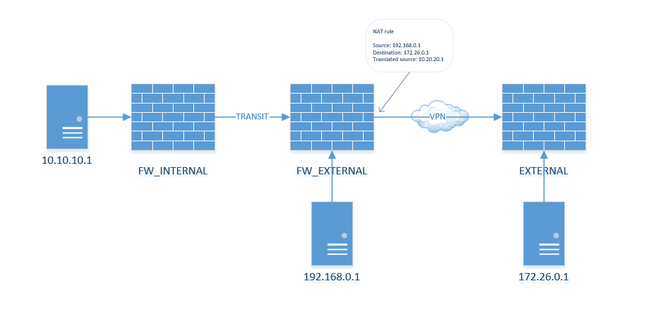
I have a question about NAT and encryption domain. My setup is as per below:
There is a VPN tunnel between FW_EXTERNAL and EXTERNAL. 192.168.0.1 is in the encryption domain and it accesses 172.26.0.1. I also perform NAT and translate the source to 10.20.20.1. Everything works fine.
Now I'd like to allow 10.10.10.1 to access 172.26.0.1. Is there any way to achieve that without adding 10.10.10.1 in the encryption domain on FW_EXTERNAL?
Thank you.
9 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
As far as I'm aware, the firewall needs to tag the packets for encryption and this is based on the real IP (pre-NAT), then to actually route it in the tunnel, the NATed IP should be defined. So you need both the real and the NATed IPs in your encryption domain.
So short of NATing the source on FW_Internal, you will need to add the real to the encryption domain on FW_External. R80.40+ allows you to specify Encryption domains per VPN community (not just RA) if you're worried about overlap.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is mostly a result of how Check Point handles domain-based VPN. The VPN routing logic is basing itself on the encryption domains. NAT is happening later in the firewall chain so the packets being tagged for VPN routing has already been taking place.
But if you happen to utilise VTI instead of domain-based routing the negotiated encryption domain doesn't take any part in the actual VPN routing. 0.0.0.0/0 will be used as the encryption domain and whatever traffic you are routing through the virtual interface (VTI) determine what is going to be sent over the VPN tunnel so this should make it possible without having to deal with the encryption domains.
But setting up VTI on Check Point is rather different and less normal than configuring domain-based VPN so this will most likely just become more confusing compared to simply adding the address to the encryption domain.
Certifications: CCSA, CCSE, CCSM, CCSM ELITE, CCTA, CCTE, CCVS, CCME
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The Encryption Domain must include everything that needs to talk on the VPN.
That obviously has implications when negotiating a VPN with a third party.
See: https://community.checkpoint.com/t5/Security-Gateways/NAT-Before-VPN/m-p/122828#M17586
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I agree with phoneboy as well...I am pretty sure vpn domain must include 10.10.10.1 IP. I dont know, maybe there is some convoluted way of doing this otherwise, but Im not aware of it if it has to go through VPN tunnel.
Best,
Andy
Andy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That point was proven out in the thread I linked to. 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I just ran in to this yesterday. We're doing NAT for both incoming and outbound traffic on a policy-based VPN (aka "one tunnel per subnet" in CheckPoint speak) and found the VPN needed to include the NAT IPs for incoming traffic but true IPs for outgoing. This is consistent with how firewall rules must be configured, but counter-intuitive because you'd think the CheckPoint would NAT the traffic first prior to encrypting it to be send across the tunnel.
I've yet to find an official CheckPoint document that explains this requirement. With other vendors (Cisco, Palo Alto, etc) there is no such requirement to have the true IP address in the encryption domain.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We need to know what traffic is "interesting" as far as encryption goes, particularly when using domain-based VPNs (versus route-based).
This is done by way of defining the encryption domain to include the real IPs.
In a route-based VPN, this isn't necessary, since traffic will only be "interesting" if it is routed out the relevant VTI.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Well, that still doesn't explain the requirement, because the SAs (traffic selectors / crypto maps / proxy ids / whatever you want to call them) get built using the NAT IP addresses. This is what shows up when running vpn tu tlist on the gateway.
Thus, the "interesting" traffic has already been defined.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, but the decision to encrypt or not is made before SAs are negotiated.
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 22 | |
| 17 | |
| 11 | |
| 8 | |
| 7 | |
| 3 | |
| 3 | |
| 3 | |
| 3 | |
| 3 |
Upcoming Events
Thu 18 Dec 2025 @ 10:00 AM (CET)
Cloud Architect Series - Building a Hybrid Mesh Security Strategy across cloudsThu 08 Jan 2026 @ 05:00 PM (CET)
AI Security Masters Session 1: How AI is Reshaping Our WorldThu 18 Dec 2025 @ 10:00 AM (CET)
Cloud Architect Series - Building a Hybrid Mesh Security Strategy across cloudsThu 08 Jan 2026 @ 05:00 PM (CET)
AI Security Masters Session 1: How AI is Reshaping Our WorldAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2025 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
About Us
UserCenter