- Products
- Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- Bulgaria
- Cyprus
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
Step Into the Future of
AI-Powered Cyber Security
When the Agents Attack
A Live Look at Agentic Exposure Validation
Bridge the CAASM Gap
with Exposure Management
AI Security Masters E8:
Claude Mythos: New Era in Cyber Security
CheckMates Go:
CheckMates Fest
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Hybrid Mesh
- :
- SASE and Remote Access
- :
- Multiple Remote Access Communities (GW Version?)
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jump to solution
Multiple Remote Access Communities (GW Version?)
Hello, when playing around in R80.10-Management today, I discovered that it's now possible to define multiple remote access communities (including defining different vpn domains for each RAC). First of all, thank you CheckPoint - I've been waiting for this feature for so long. [edit 07.01.: more a bug than a feature, see below]
I couldn't find any hints regarding multiple RACs in the R80.10 Release Notes/HFA Notes/Support-Center.So my questions are:
Is there any official statement whether the GW has to run R80.10 or can this be configured for a R77.30 GW (managed by R80.10 SM) as well?
(added) Any experiences/considerations when using on VSX?
Thanks in advance!
Greetings Christoph
1 Solution
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
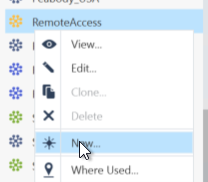
to be honest, I didn't have time to test it so far which means that I don't know if the configuration actually verifies or can actually be deployed, but I managed to configure it the following way (R80.10 Smart Console):
Right-click on existing RemoteAccess-Community -> New... (in the objects bar, not the object explorer) - this allows the creation of another RemoteAccess-Community-Object (Maybe this is the part that should not be possible to do as the "standard" menu to create a new object "New... -> More -> VPN Community" does not offer a RemoteAccess-Community). Afterwards you can define different VPN-Domains in the topology settings of the participating gateway object.
30 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
To be honest, I haven't heard anything about this myself.
I suspect if this were not allowed, you'd have issues pushing policy.
Have you tried doing so?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I can remember that a developer told me about it at CPX, but more as an upcoming R80.20 feature.
No, I didn't have the opportunity yet, but I'll try it next week.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Curious, how you managed to do this?
I can't get SmartConsole to allow this in R80.10 or R80.20.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
to be honest, I didn't have time to test it so far which means that I don't know if the configuration actually verifies or can actually be deployed, but I managed to configure it the following way (R80.10 Smart Console):
Right-click on existing RemoteAccess-Community -> New... (in the objects bar, not the object explorer) - this allows the creation of another RemoteAccess-Community-Object (Maybe this is the part that should not be possible to do as the "standard" menu to create a new object "New... -> More -> VPN Community" does not offer a RemoteAccess-Community). Afterwards you can define different VPN-Domains in the topology settings of the participating gateway object.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Huh, interesting, that does seem to work.
From what I know, this isn't supported.
The fact you can create more than one Remote Access community would be considered a bug.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Could we get a confirmation if this works to the point where you may also have different rules set up or is it just the fact that you have 2 RACs.
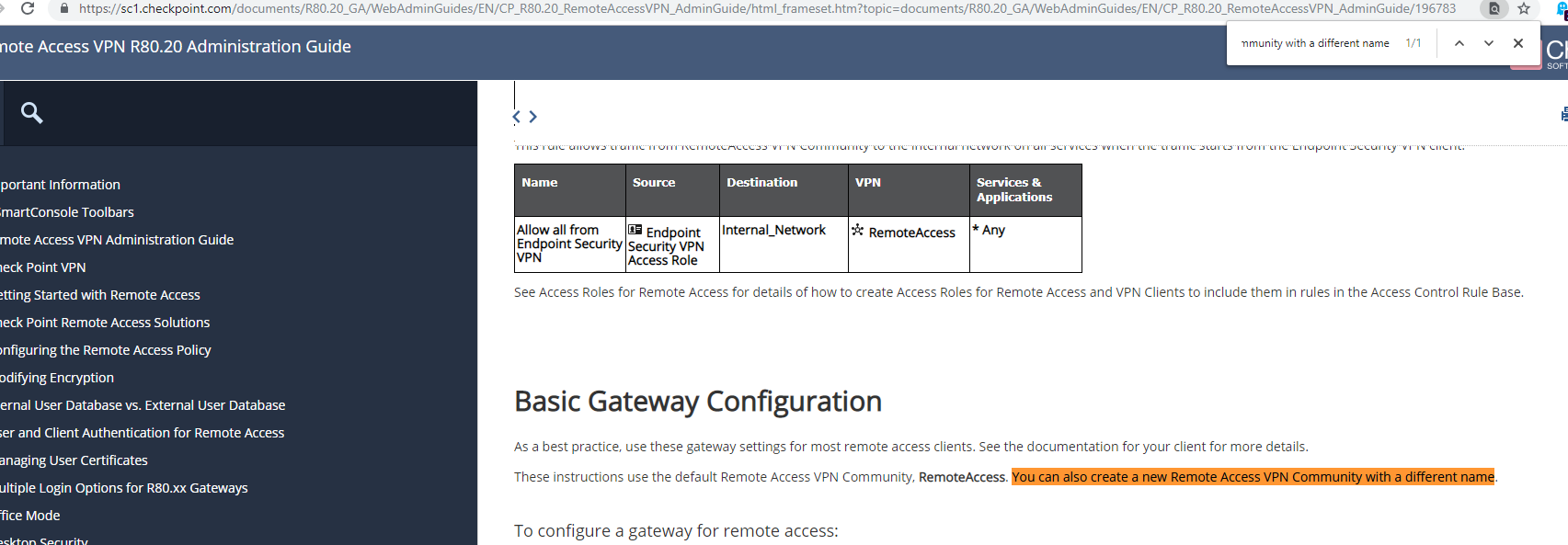
According to the Admin Guide you can create a new Remote Access community but it never mentions how. However it doesn't mention that you can use more than one in the policy.
There is also a definition of Encryption Domain on the Gateway object itself so having 2 RACs on the Same Gateway would imply using the same Encryption Domain.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Like I said, the fact the GUI allows you to create more than one Remote Access community is a bug.
Where in the documentation does it state you can create a second Remote Access community?
The only place where I could see it being useful is if you could also define the encryption domain for the different communities.
But since the encryption domain is defined on the gateway, and it would be the same for all communities, I don't see a real benefit to different VPN communities for Remote Access.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Well, the thing is, that the GUI actually allows you to define a separate encryption domain per remote access community. (GW-properties -> Network Management -> VPN Domain -> Set domain for Remote Access Community...). I didn't want to deploy that on productive environment (therefore my question), so I don't know if the policy installation is allowed, but you can configure it in R80.10 SmartConsole (that led me to the assumption that this might be a new feature...).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dameon Welch-Abernathy wrote:
Like I said, the fact the GUI allows you to create more than one Remote Access community is a bug.
Where in the documentation does it state you can create a second Remote Access community?
The only place where I could see it being useful is if you could also define the encryption domain for the different communities.
But since the encryption domain is defined on the gateway, and it would be the same for all communities, I don't see a real benefit to different VPN communities for Remote Access.
Well here is the place it says you can create "a new Remote Access VPN Community" with a different name. This to my understanding is equivalent with a second Remote Access Community as it is new and does not replace the existing one. However it never states anywhere in the manual how to actually create it. I would say it's a more a feature and less a bug.
@Christoph Holzinger i will test this in production and update soon.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
HI,
I have just tested this possibility but It's not working!!! The policy installation fail said that we can use ANY or "RemoteAccess" as Community name

Some one know how have the possibility to view just one gateway on the VPN Client instead of all Gateways contained into the community?
Best Regards
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
ok interesting, thanks for testing.
Regarding your question: If you mean the dropdown that appears after the first successful connect, I think the solution you are looking for is sk78180. (at least it solved the same issue for me ![]() ).
).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have tried the sk78180.... only on a secondary gateway but doesn't work? Do I need to implement on all gateways?
My goal is to remove the dropdown list that shows all gateways in the remote community!
thaks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I made the change on both gateways....the dropdown list is removed but the client is still connecting to the "primary" site....
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I solved with your SK!
Thank You very Much!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Greetings,
Has there been a definitive answer if multiple remote access community, with separate encryption domains applied to each community, and then installed to the same gateway or different gateways is a supported feature? This functionality is something a customer is currently looking for as they want to disable split-tunneling for some users while allowing split tunneling for others. Having only one encryption domain is a limiting factor. Being able to push down a different routing table based on user, say Identity Awareness credentials would be a great option as well.
Regards
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Add on to the above post, for Endpoint there is an option of creating a new *.ttm. file that hands out configurations based on group membership. sk114882. I haven't found any documents as to how this would be deployed with the Mobility Blade and SSL Extender. Having the capability to assign users to a different remote access community at the management level would be a great feature if it is truly supported.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
As I said previously, even if you could define more than one Remote Access community, there is only one encryption domain.
The fact you can even define a second Remote Access community in a particular circumstance is a bug—I confirmed this with R&D.
The fact you can even define a second Remote Access community in a particular circumstance is a bug—I confirmed this with R&D.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I know this is an old thread but the bug (?) still exists in R80.40 HFA91 - right-click RemoteAccess in the Objects bar and select New. sk160892 states this "problem" was "fixed" in R80.20 - what exactly did this fix entail - enabling support in the software for multiple RACs or remove the option to create a new one in the Objects bar?
My need for multiple RACs relates to a migration PoC I am running for a customer, we have a new cluster we wish to test Remote Access on without existing clients seeing the new gateway (I'm assuming MEP will allow clients to use the new cluster before it is commissioned / 'blessed' with the default RAC, I want to avoid touching the current gateway as much as possible).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The fix was to prevent you from creating more than one RemoteAccess community.
As of right now, you can only have one RemoteAccess community defined and it needs to be called RemoteAccess.
You'll probably have to use MEP to achieve the requirement at the moment.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks dude, appears the bug still exists in R80.40:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Probably needs a TAC case so an appropriate bug can be filed.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
Can you please explain the motivation to have 2 different RCA's?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Llya,
The attraction of having multiple Remote Access Communities would be to have different configurations for different user base, including but not limited to different encryption domains, different approved sites or whitelist of sites, rules based on the community the user joined. Some of this can be accomplished by modifying local .ttm files on the gateway, but this functionality should be part of central management, not custom files on a gateway that has the chance of being overwritten during a fresh install/upgrade.
Current need it to have split tunneling enabled for some remote users but not others, allow a few approved public sites to go local from the remote device (Microsoft Updates for example) while forcing all other Internet traffic through the tunnel.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
While I understand most of the other issues, I don't quite get the need for different Remote Access Communities.
What a given user can access is determined entirely by policy, not what the encryption domain is.
Maybe the disclosure of the various subnets is an issue, not sure.
What a given user can access is determined entirely by policy, not what the encryption domain is.
Maybe the disclosure of the various subnets is an issue, not sure.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
PB,
First off, cool running into you this summer.
Here's a very specific use case for multiple remote access encryption domains. We are being required to send all our users data to our gateway BUT we have a few business units that do NOT have this requirement. Being a very large global company, we use the same gateways for all of our 50 business units.
As you can see, how would you do a remote access community for some people to route all through the gateway and then have a few users here and there route only what is needed (our internal networks) and allow the rest to go out locally?
BTW, one caveat is that we also need to break out skype traffic from going down the tunnel, so we cannot do route all through gateway, we kinda have to do a group with exclusion of 0.0.0.0/0 minus our skype servers if that makes sense.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The different Remote Access communities can be solved by using VSX to some extent (different termination for different users) or different physical gateways.
You can decide to "route all traffic" based on user group.
See: https://community.checkpoint.com/t5/Remote-Access-Solutions/Exclude-Subnet/m-p/23608
You can decide to "route all traffic" based on user group.
See: https://community.checkpoint.com/t5/Remote-Access-Solutions/Exclude-Subnet/m-p/23608
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi, i know its a old Thread but still there a needs for this topic, is there naything new in Year 2023/2024 about htis topic ? We also faced the issue that we need to deploy 2 gateways in order to manage one group of employees to get route all traffic and the other group not to.
Other Firewall manufacturar got profiles for this and you can manage this thinks you guys brought to the table. We have these different use cases and do not want to deploy 3 different Gateways for it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Unfortunately, this has not changed in current versions.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Regretfully, this is a sticking point for a couple of my clients and is driving them away from checkpoint for a remote access solution. This is also influencing their future direction with checkpoint as the firewall also.
The business need was to have access to different business units with different authentication methods enforced that have access to different groups of networks. If we split off management for these business units, it's a non issue, but the management expertise is not there for all of the business units.
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 3 | |
| 2 | |
| 1 | |
| 1 | |
| 1 | |
| 1 | |
| 1 | |
| 1 |
Upcoming Events
Wed 10 Jun 2026 @ 01:00 PM (EDT)
Deep Dive: When the Agents Attack: A Live Look at Agentic Exposure ValidationThu 11 Jun 2026 @ 11:00 AM (EDT)
Tips and Tricks 2026 #8: Say Yes to AI Without Saying Yes to RiskFri 12 Jun 2026 @ 10:00 AM (CEST)
CheckMates Live Netherlands - Sessie 47: Continuous Threat Exposure ManagementTue 16 Jun 2026 @ 05:00 PM (CEST)
Under the Hood: Check Point SASE | Internet Access Optimization & Performance TuningWed 10 Jun 2026 @ 01:00 PM (EDT)
Deep Dive: When the Agents Attack: A Live Look at Agentic Exposure ValidationThu 11 Jun 2026 @ 11:00 AM (EDT)
Tips and Tricks 2026 #8: Say Yes to AI Without Saying Yes to RiskFri 12 Jun 2026 @ 10:00 AM (CEST)
CheckMates Live Netherlands - Sessie 47: Continuous Threat Exposure ManagementTue 16 Jun 2026 @ 05:00 PM (CEST)
Under the Hood: Check Point SASE | Internet Access Optimization & Performance TuningThu 18 Jun 2026 @ 10:00 AM (CEST)
The Cloud Architects Series: Check Point WAF - The Next Generation of AI powered protectionAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2026 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
About Us
UserCenter