I have a security gateway being managed by a SMS over a VPN. I realize this isn't the best solution, but it is a temporary setup.
I've read through all the posts I can find, relating to removing services from implied_rules.def on the Management Server and repushing policy, in order for the traffic to be caught by a regular VPN rule.
Such as:
https://community.checkpoint.com/t5/Management/Exclude-CPM-traffic-from-implied-rules/td-p/3934
https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solut...
https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solut...
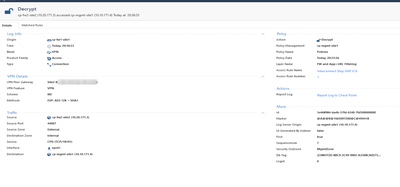
So far so good. I am able to manage the gateway, retrieve its topology, push policy and the gateway is even sending logs back to the SMS. I'm now attempting to access the gateway remotely from home via Checkpoint ENDPOINT VPN. It is connecting but failing on "Failure to retrieve CRL". I have narrowed it down to FW1_ICA_Services and I can see on every attempt the gateway attempts to reach the gateway, but the log entry certaintly shows its being picked up by Implied Rules:
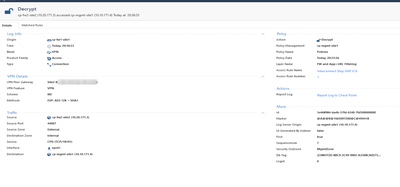
As opposed to something like CPD or CPMI currently leveraging the VPN tunnel:
This KB kindly lists the VPN services required:
https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solut...
Great I thought, I must have forgotten to disable something from implied_rules.def. I close down SmartConsole as per the kb, but I already have fw1_ica_services disabled. I made sure to push policy again (to both gateways), but implied_rules are still picking it up. Here's what my implied_rules.def looks like right now:
#define ENABLE_FWD_TOPO
/* #define ENABLE_FWD_SVC */
/* #define ENABLE_CPMI */
/* #define ENABLE_CPD */
/* #define ENABLE_CPD_AMON */
#define ENABLE_FW1_SAM
/* #define ENABLE_FWD_LOG */
#define ENABLE_IKE
#define ENABLE_NATT
#define ENABLE_OFFICE_DHCP
/* #define ENABLE_FW1_ICA_PULL */
/* #define ENABLE_FW1_ICA_PUSH */
/* #define ENABLE_FW1_ICA_SERVICES */
#define ENABLE_CP_RTM
#define ENABLE_CP_REDUNDANT
#define ENABLE_CP_REPORTING
/* disable SC R60 policy server */
/* #define ENABLE_FW1_PSLOGON_NG */
(All of this will be rolled back in a few weeks when I have an inter connect up and working)
Any idea what I could be missing?