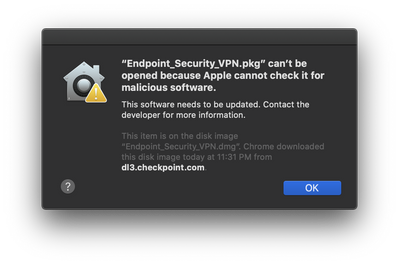
This is still not resolved as of 8-18-2020. Running macOS 10.15.6 and with the latest version of CP Endpoint Security (E83.20). The last I heard from support was that it would not be resolved until the end of this calendar year.
Support for Apple Mac is a very low priority for Check Point as you can tell from the fact that the VPN client just now got support for Multiple Authentication Factors, 3+ years after that feature was mainstream for Windows platforms. What I don't get is why Check Point can't spend the $99 for an Apple Developer Account and take the extra 3 steps to notarize the PKG file in the build process. It literally took me 30 minutes the other day to find a nice write-up someone did online on signing a PKG file using the command line tools and to sign and notarize the PKG for installation.
It may be possible to re-sign the PKG file if you happen to have your own Apple Developer Account (and Developer ID Installer certificate) and then submit that to Apple for notarization. This may be the only way for users that are using a UEM/MDM platform to manage their Mac computers as there is no other way to automate the Gatekeeper approval otherwise.
The PKG is already signed, they just either didn't notarize it or didn't stable the notarization to the PKG:
heath@Heaths-MBP ~ % pkgutil --check-signature ./Endpoint_Security_VPN.pkg
Package "Endpoint_Security_VPN.pkg":
Status: signed by a developer certificate issued by Apple for distribution
Signed with a trusted timestamp on: 2020-08-03 17:17:39 +0000
Certificate Chain:
1. Developer ID Installer: Check Point Software Technologies (TZ3UEPFYKD)
Expires: 2022-02-08 14:55:35 +0000
SHA256 Fingerprint:
F9 2B BE 97 52 FE 57 7A F6 A3 8C CE 22 72 58 0C F8 DA BA 05 B2 5A
B8 50 D2 9D BC EB CB 37 BC 31
------------------------------------------------------------------------
2. Developer ID Certification Authority
Expires: 2027-02-01 22:12:15 +0000
SHA256 Fingerprint:
7A FC 9D 01 A6 2F 03 A2 DE 96 37 93 6D 4A FE 68 09 0D 2D E1 8D 03
F2 9C 88 CF B0 B1 BA 63 58 7F
------------------------------------------------------------------------
3. Apple Root CA
Expires: 2035-02-09 21:40:36 +0000
SHA256 Fingerprint:
B0 B1 73 0E CB C7 FF 45 05 14 2C 49 F1 29 5E 6E DA 6B CA ED 7E 2C
68 C5 BE 91 B5 A1 10 01 F0 24
heath@Heaths-MBP ~ % stapler validate --verbose Endpoint_Security_VPN.pkg
Processing: /Users/heath/Endpoint_Security_VPN.pkg
Properties are {
NSURLIsDirectoryKey = 0;
NSURLIsPackageKey = 0;
NSURLIsSymbolicLinkKey = 0;
NSURLLocalizedTypeDescriptionKey = "Installer package";
NSURLTypeIdentifierKey = "com.apple.installer-package-archive";
"_NSURLIsApplicationKey" = 0;
}
Sig Type is RSA. Length is 3
Sig Type is CMS. Length is 3
Package Endpoint_Security_VPN.pkg uses a checksum of size 20
We do not know how to deal with trailer version 29928. Exepected 1
Endpoint_Security_VPN.pkg does not have a ticket stapled to it.