
- Products
- Learn
- Local User Groups
- Partners
- More
Stop Babysitting Rules.
Go Agentic
Step Into the Future of
AI-Powered Cyber Security
The State of Ransomware Q1 2026
Key Trends and Their Impact
AI Security Masters E8:
Claude Mythos: New Era in Cyber Security
Blueprint Architecture for Securing
The AI Factory & AI Data Center
Call For Papers
Your Expertise. Our Stage
CheckMates Go:
CheckMates Fest
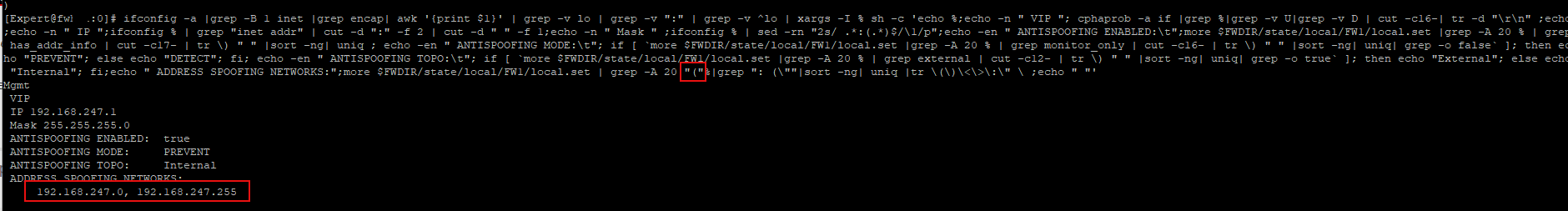
This CLI command shows you the address spoofing networks as list and the IP settings per interface. Type this command on security gateway.
Last version from 30-10-2025- command:
ifconfig -a |grep -B 1 inet |grep encap| awk '{print $1}' | grep -v lo | grep -v ":" | grep -v ^lo | xargs -I % sh -c 'echo %;echo -n " VIP "; cphaprob -a if |grep %|grep -v U|grep -v D | cut -c16-| tr -d "\r\n" ;echo;echo -n " IP ";ifconfig % | grep "inet addr" | cut -d ":" -f 2 | cut -d " " -f 1;echo -n " Mask " ;ifconfig % | sed -rn "2s/ .*:(.*)$/\1/p";echo -en " ANTISPOOFING ENABLED:\t";more $FWDIR/state/local/FW1/local.set |grep -A 30 % | grep has_addr_info | cut -c17- | tr \) " " |sort -n| uniq ; echo -en " ANTISPOOFING MODE:\t"; if [ `more $FWDIR/state/local/FW1/local.set |grep -A 30 % | grep monitor_only | cut -c16- | tr \) " " |sort -n| uniq| grep -o false` ]; then echo "PREVENT"; else echo "DETECT"; fi; echo -en " ANTISPOOFING TOPO:\t"; if [ `more $FWDIR/state/local/FW1/local.set |grep -A 30 % | grep external | cut -c12- | tr \) " " |sort -n| uniq| grep -o true` ]; then echo "External"; else echo "Internal"; fi;echo " ADDRESS SPOOFING NETWORKS:";more $FWDIR/state/local/FW1/local.set | grep -A 30 %|grep ": (\""|sort -n| uniq |tr \(\)\<\>\:\" \ ;echo " "'
Now you can see the states of:
- ANTISPOOFING ENABLED
- ANTISPOOFING MODE
- ANTISPOOFING TOPO
Here is a demo video:
This CLI command shows you the address spoofing networks as list and the IP settings per interface. Type this command on security gateway.
Last version from 30-10-2025- command:
ifconfig -a |grep -B 1 inet |grep encap| awk '{print $1}' | grep -v lo | grep -v ":" | grep -v ^lo | xargs -I % sh -c 'echo %;echo -n " VIP "; cphaprob -a if |grep %|grep -v U|grep -v D | cut -c16-| tr -d "\r\n" ;echo;echo -n " IP ";ifconfig % | grep "inet addr" | cut -d ":" -f 2 | cut -d " 
This one-liner is very helpful. Can you also add routes for the interface? This makes it easier to see which networks are missing.
Thanks to Danny Jung (One-liner for Address Spoofing Troubleshooting) for the inspiration and to Timothy Hall (CLI Anti-Spoofing Information ) for the infos.
THX
Thanks to Danny Jung (One-liner for Address Spoofing Troubleshooting) for the inspiration and to Timothy Hall (CLI Anti-Spoofing Information ) for the infos.
THX
;Glad to see such a great tool. Also wanted to mention this SK detailing a situation in which performing a "Get Interfaces WITHOUT Topology" will change the antispoofing state from Disabled to Enabled (with Prevent) on firewall interfaces! Needless to say this can result in some unexpected issues:
sk136372: Get Interfaces without topology resets anti-spoofing to Enabled/Prevent
This may necessitate disabling gateway anti-spoofing enforcement "on the fly" as detailed in my presentation here:
The fix for this issue was rolled into R80.10 GA Jumbo HFA 154:
R80.10: New Jumbo Hotfix (Take 154) GA-Release
--
Second Edition of my "Max Power" Firewall Book
Now Available at http://www.maxpowerfirewalls.com
Glad to see such a great tool. Also wanted to mention this SK detailing a situation in which performing a "Get Interfaces WITHOUT Topology" will change the antispoofing state from Disabled to Enabled (with Prevent) on firewall interfaces! Needless to say this can result in some unexpected issues:
sk136372: Get Interfaces without topology resets anti-spoofing to Enabled/Prevent
This may necessitate disabling gateway anti-spoofing enforcement "on the fly" as detailed in my prese
...;Hey buddy. Was this tested with R77.30 as well or just R80.10? On one of my old clusters that runs R77.30 it returned ton of false results as it greps too far when looking for spoofing subnets. Maybe worth adding a note if it only works or was tested on R80.10 ![]() Or even better, doesn't run on R77.30
Or even better, doesn't run on R77.30
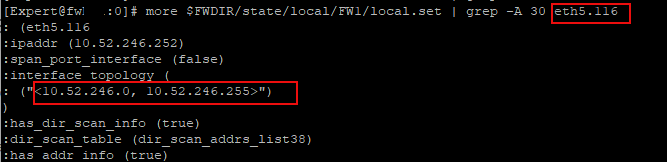
To give you an example
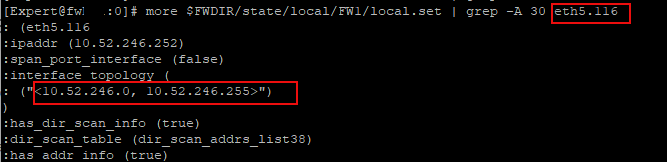
but with the current command following 30 lines you will get 2 extra subnets reported:

reducing grep search to 25 lines helps but I'm not too sure how would it behave in case you had very long list of subnets ![]()
might need to re-think the approach for filtering those subnets ![]()
Hey buddy. Was this tested with R77.30 as well or just R80.10? On one of my old clusters that runs R77.30 it returned ton of false results as it greps too far when looking for spoofing subnets. Maybe worth adding a note if it only works or was tested on R80.10 ![]() Or even better, doesn't run on R77.30
Or even better, doesn't run on R77.30
To give you an example
but with the current command following 30 lines you will get 2 extra subnets reported:

reducing grep search to 25 lines helps but I'm not too s
...;Also Mgmt interface may return a lot of rubbish as it may match string "Mgmt" in the file, it's a fairly common string

Better is to add leading bracket
Great command, certainly very useful.
As an aside, can either this command be adapted, or is there an alternative for pulling this information from a VS or VR on VSX? I am right in thinking the local.set file contains only the interface configuration for the VSX GW and not the VRs or VSs.
Thanks,
Great command, certainly very useful.
As an aside, can either this command be adapted, or is there an alternative for pulling this information from a VS or VR on VSX? I am right in thinking the local.set file contains only the interface configuration for the VSX GW and not the VRs or VSs.
Thanks,
;Hi, I prefer using Danny Jung one-liner for getting spoofing info. So it will work on any VS as long as you set vsenv x environment beforehand manually
echo; egrep -B1 $'ifindex|:ipaddr|\(\x22<[0-9]|has_addr_info|:monitor_only|:external' $FWDIR/state/local/FW1/local.set | sed 's/[\x22\t()<>]//g' | sed 's/--//g' | sed 'N;s/\n:ipaddr6/ IPv6/;P;D' | sed '/IPv6/!s/://g' | sed 's/interface_topology/\tCalculated Interface Topology/g' | sed '0,/ifindex 0/{/ifindex 0/d;}' | sed '/ifindex 0/q' | sed '/spoof\|scan/d' | sed 's/has_addr_info true/\tAddress Spoofing Protection: Enabled/g' | sed 's/has_addr_info false/\tAddress Spoofing Protection: Disabled/g' | sed -e '/Prot/{n;d}' | sed 'N;s/\nmonitor_only true/ (Detect Mode)/;P;D' | sed 'N;s/\nmonitor_only false/ (Prevent Mode)/;P;D' | sed 'N;s/\nexternal false/ - Internal Interface/;P;D' | sed 'N;s/\nexternal true/ - External Interface/;P;D' | tac | sed '/ifindex 0/I,+2 d' | sed '/Address/,$!d' | tac | sed '/ifindex/d' | sed 's/,/ -/g' | sed 'N;s/\nipaddr/ >/;P;D' | sed '/ - /s/^ /\t/' | egrep -C 9999 --color=auto $'>|IPv6|External|Disabled|Detect'
Hi, I prefer using Danny Jung one-liner for getting spoofing info. So it will work on any VS as long as you set vsenv x environment beforehand manually
echo; egrep -B1 $'ifindex|:ipaddr|\(\x22<[0-9]|has_addr_info|:monitor_only|:external' $FWDIR/state/local/FW1/local.set | sed 's/[\x22\t()<>]//g' | sed 's/--//g' | sed 'N;s/\n:ipaddr6/ IPv6/;P;D' | sed '/IPv6/!s/://g' | sed 's/interface_topology/\tCalculated Interface Topology/g' | sed '0,/ifindex 0/{/ifindex 0/d;}' | sed '/ifindex 0/q
...;Thanks Kaspars.
I did have the vsenv set to the correct environment, but I was running Danny Jungs CCC script, and running the command through there, which must default to the VS 0.
Works a treat when ran directly. Thanks! ![]()
This is an interesting one-liner. I think considering the length of this, it might be better to make it into a script. That way it can be aliased for people who want to use this often.
It would also gain the ability to adapt to where it is being run from if it was a script (some checks for VSX or any other system that we might need to treat differently). I'll play with this next week.
I've modified slightly to improve internal code styling (consistent use of spaces in pipelines, for example) and to improve code correctness (I have an incredibly weird firewall which hits basically every edge case ever; this version works on it). One specific correctness change I made was wrapping the "VIP" section in a test to see if we're on a cluster in the first place. That whole line should now be silently omitted when run on a non-clustered firewall.
The other big one relates to the awk nightmare in the middle. The problem I ran into is $FWDIR/state/local/FW1/local.set contains data for both members of a cluster, not just the member you're on. Rather than dumping the contents and parsing them repeatedly, I try to get just the lines for the interface we want, and just on the member we're running on. My awk-fu is weak, so I'm sure that expression's correctness can be improved. Still, it's a bit better than just deduplicating, since interfaces can have different exact configuration. This is the expression I was playing with before I had to put this down for a while:
awk "/^: \(@$/,(/^: \([^\)]+$/ && ! /^: \(@$/)" $FWDIR/state/local/FW1/local.set
It returns both instances of the interface from the local.set file, and I'm not sure yet how to filter it to just the one I want.
Here is my modified version of the whole script as a one-liner:
interfaceAddress="";interfaceData="";ifconfig -a | grep -B 1 inet | grep encap | awk '{print $1}' | grep -v lo | grep -v ":" | xargs -I @ sh -c 'echo @;if [ $(cpprod_util FwIsHighAvail) -ne 0 ]; then printf " VIP %s\n" $(cphaprob -a if | egrep "^@ +[0-9]" | awk "{print $2}");fi;interfaceAddress=$(ifconfig "@" | grep "inet addr" | cut -d ":" -f 2 | cut -d " " -f 1);printf " IP %s\n" $interfaceAddress;printf " Mask %s\n" $(ifconfig "@" | sed -rn "2s/ .*:(.*)$/\1/p");interfaceData=$(awk "/^:ipaddr \(${interfaceAddress}\)/,/^:mss_value \([0-9]+\)/" $FWDIR/state/local/FW1/local.set);echo -en " ANTISPOOFING ENABLED:\t";echo "${interfaceData}" | grep has_addr_info | cut -c17- | tr \) " ";echo -en " ANTISPOOFING MODE:\t";echo "${interfaceData}" | grep monitor_only | grep false > /dev/null;if [ "$?" -eq 0 ];then echo "Prevent";else echo "Detect";fi;echo -en " ANTISPOOFING TOPO:\t";echo "${interfaceData}" | grep external | grep true > /dev/null;if [ "$?" -eq 0 ];then echo "External";else echo "Internal";fi;echo " ADDRESS SPOOFING NETWORKS:";echo "${interfaceData}" | grep ": (\"" | sort -ng | uniq | tr \(\)\<\>\:\" \ ;echo ""'
The attached text file is the same script broken out into many lines to make the internal logic flow more obvious.
I've modified slightly to improve internal code styling (consistent use of spaces in pipelines, for example) and to improve code correctness (I have an incredibly weird firewall which hits basically every edge case ever; this version works on it). One specific correctness change I made was wrapping the "VIP" section in a test to see if we're on a cluster in the first place. That whole line should now be silently omitted when run on a non-clustered firewall.
The other big one relates to
...;
Thanks for this command. I added this into a script file and changed the following:
ifconfig -a $1
So it's also possible to only get the Output on a specified interface, for example "scriptname eth1"
--------------------------------------------------------------------------------------------------
more $FWDIR/state/local/FW1/local.set | grep -A 30 \(%
Added \( before %, because there were strange outputs on the Sync and Mgmt Interfaces
Here is the one liner again to insert into a script or run as command by changing $1 (at the beginning) to the specified interface:
ifconfig -a $1|grep -B 1 inet |grep encap| awk '{print $1}' | grep -v lo | grep -v ":" | grep -v ^lo | xargs -I % sh -c 'echo %;echo -n " VIP "; cphaprob -a if |grep %|grep -v U|grep -v D | cut -c16-| tr -d "\r\n" ;echo;echo -n " IP ";ifconfig % | grep "inet addr" | cut -d ":" -f 2 | cut -d " " -f 1;echo -n " Mask " ;ifconfig % | sed -rn "2s/ .*:(.*)$/\1/p";echo -en " ANTISPOOFING ENABLED:\t";more $FWDIR/state/local/FW1/local.set |grep -A 30 \(% | grep has_addr_info | cut -c17- | tr \) " " |sort -ng| uniq ; echo -en " ANTISPOOFING MODE:\t"; if [ `more $FWDIR/state/local/FW1/local.set |grep -A 30 \(% | grep monitor_only | cut -c16- | tr \) " " |sort -ng| uniq| grep -o false` ]; then echo "PREVENT"; else echo "DETECT"; fi; echo -en " ANTISPOOFING TOPO:\t"; if [ `more $FWDIR/state/local/FW1/local.set |grep -A 30 \(% | grep external | cut -c12- | tr \) " " |sort -ng| uniq| grep -o true` ]; then echo "External"; else echo "Internal"; fi;echo " ADDRESS SPOOFING NETWORKS:";more $FWDIR/state/local/FW1/local.set | grep -A 30 \(%|grep ": (\""|sort -ng| uniq |tr \(\)\<\>\:\" \ ;echo " "'
Thanks for this command. I added this into a script file and changed the following:
ifconfig -a $1
So it's also possible to only get the Output on a specified interface, for example "scriptname eth1"
--------------------------------------------------------------------------------------------------
more $FWDIR/state/local/FW1/local.set | grep -A 30 \(%
Added \( before %, because there were strange outputs on the Sync and Mgmt Interfaces
Here is the one liner again to insert int
...;Is there a best practice/admin guide around anti-spoofing?
It has been a thorn in my side ever since taking on the firewalls a few years ago. Invariably, it would start blocking traffic and we'd just have to turn it off. And that doesn't thrill me any.
I'd like to get it fixed and fixed correctly in the coming year.
Is there a best practice/admin guide around anti-spoofing?
It has been a thorn in my side ever since taking on the firewalls a few years ago. Invariably, it would start blocking traffic and we'd just have to turn it off. And that doesn't thrill me any.
I'd like to get it fixed and fixed correctly in the coming year.
;About CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
