My Company has a number of Small Business customers who are relying on basic internet connections from Comcast, Fios, Charter, etc... for their primary internet. Most of these Customers already have a primary Internet Gateway/Router that they purchased or rent. My company provides Managed Security Services and these Customers are interested in Firewall solutions but aren't willing to change their existing setups. They want something dropped inline that doesn't change their setup.
We're wondering if there is an Architecture with Layer 2 Transparent bridging on some ports that will work in this setup. This would require a device to Bridge Traffic to the Gateway (pass the DHCP request) then have some capability to also communicate outbound for updates/management with only one DHCP lease. One port would need to be Layer 3 to get a routable IP and point to a Gateway for internet updates.
Use Case would be:
INTERNET-->CHECKPOINT FW-->INTERNET ROUTER --> LAN
Does anyone know if this is possible with any Checkpoint UTM devices?
Based on this article: Bridge Mode it sounds like this could be possible, but I'm not clear.
The article section that is interesting:
Routing and Bridges
Security Gateways with a bridge interface can support Layer 3 routing over non-bridged interfaces. If you configure a bridge interface with an IP address for one Security Gateway (not a cluster), the bridge functions as a regular Layer 3 interface. It participates in IP routing decisions on the gateway and supports Layer 3 routing.
- Cluster deployments do not support this configuration.
- You cannot configure the bridge to be the route gateway.
- One Security Gateway can support multiple bridge interfaces, but only one bridge can have an IP address.
- The Security Gateway cannot filter or transmit packets on a bridge interface that it inspected before (double-inspection).
Management over Bridge
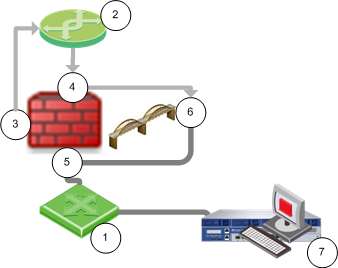
The following diagram shows a sample topology:
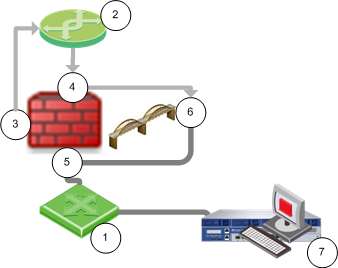
Item | Description |
1 | Switch |
2 | Router |

| Security Gateway Firewall bridging Layer-2 traffic |
3 | Management interface (inspects first packet) |
4 | eth1 (inspects first packet again) |
5 | eth2 |
6 | Bridge interface - Management traffic drops |
7 | Security Management Server |
When a Layer-3 management interface sends traffic through the firewall, the traffic is dropped because it cannot inspect the same packet again.
- The first packet is inspected and then goes from the management interface to the router.
- The router sends the packet to the bridge interface, and the firewall inspects the first packet again. The firewall concludes that this packet is a retransmission and then drops it.
Use the procedure for the applicable Security Gateway version.