Hi everyone,
R77.30
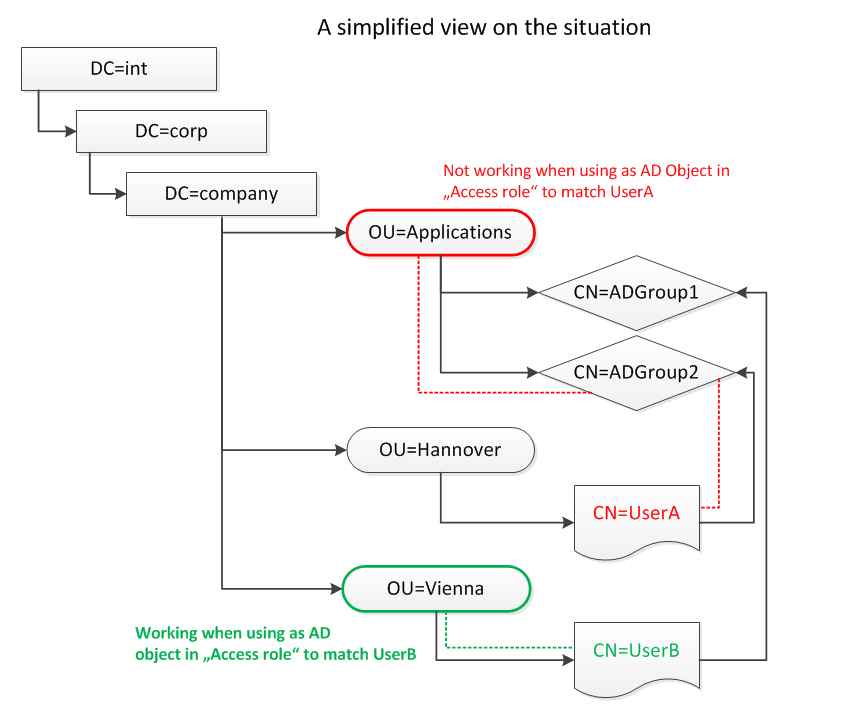
I just noticed an unfortunate behaviour of the Identity Awareness (IA) in regards to handling OUs inside "Access Role"-objects. Maybe you know if this is known not to work, or you even have a workaround/fix for this.
One of our customers has a working Access Role listing a OU called "OU=LocationA" comprising of other OUs and inside those are users (DN):
OU=LocationA,DC=blablub,DC=corp,DC=int
Example user entries inside the used OU or sub-OUs (DN):
CN=UserA,OU=CB,OU=LocationA,DC=blablub,DC=corp,DC=int
CN=UserB,OU=Extern,OU=CB,OU=LocationA,DC=blablub,DC=corp,DC=int
etc.
They also have a not working Access Role using one OU with AD-groups only inside called "OU=JIRA" (DN):
OU=JIRA,OU=Applications,OU=Global-Groups,DC=blablub,DC=corp,DC=int
Example AD-groups entries inside the used OU (DN):
CN=JIRA_PX,OU=JIRA,OU=Applications,OU=Global-Groups,DC=blablub,DC=corp,DC=int
CN=JIRA_QA,OU=JIRA,OU=Applications,OU=Global-Groups,DC=blablub,DC=corp,DC=int
etc.
not working means: The "Access Role" does not match connections of users that are members of the according AD-group.
working means: The "Access Role" does match connections of users that are members of the according OU or sub-OUs.
These are the only two occasions we used OUs. Normally AD-groups are the standard entry for "Access Roles". And in this case we really need the not working OU to work.
I can browse those AD branches inside the SmartDashboard "Objects list" under (Users and Administrators) ok. Users are being listed for the AD-groups and OUs when double clicking.
I'm not too deep into AD, but I believe IA has an issue with nested AD-groups inside an OU when a OU is used as entry in an Access Role.
Does anyone have any experience with this situation? Your thoughts are highly appreciated.
best regards
Carsten