- Products
- Learn
- Local User Groups
- Partners
- More
Step Into the Future of
AI-Powered Cyber Security
The State of Ransomware Q1 2026
Key Trends and Their Impact
AI Security Masters E8:
Claude Mythos: New Era in Cyber Security
Blueprint Architecture for Securing
The AI Factory & AI Data Center
Call For Papers
Your Expertise. Our Stage
CheckMates Go:
CheckMates Fest
| Overview |
|---|
From version R80.10 to version R81.10.
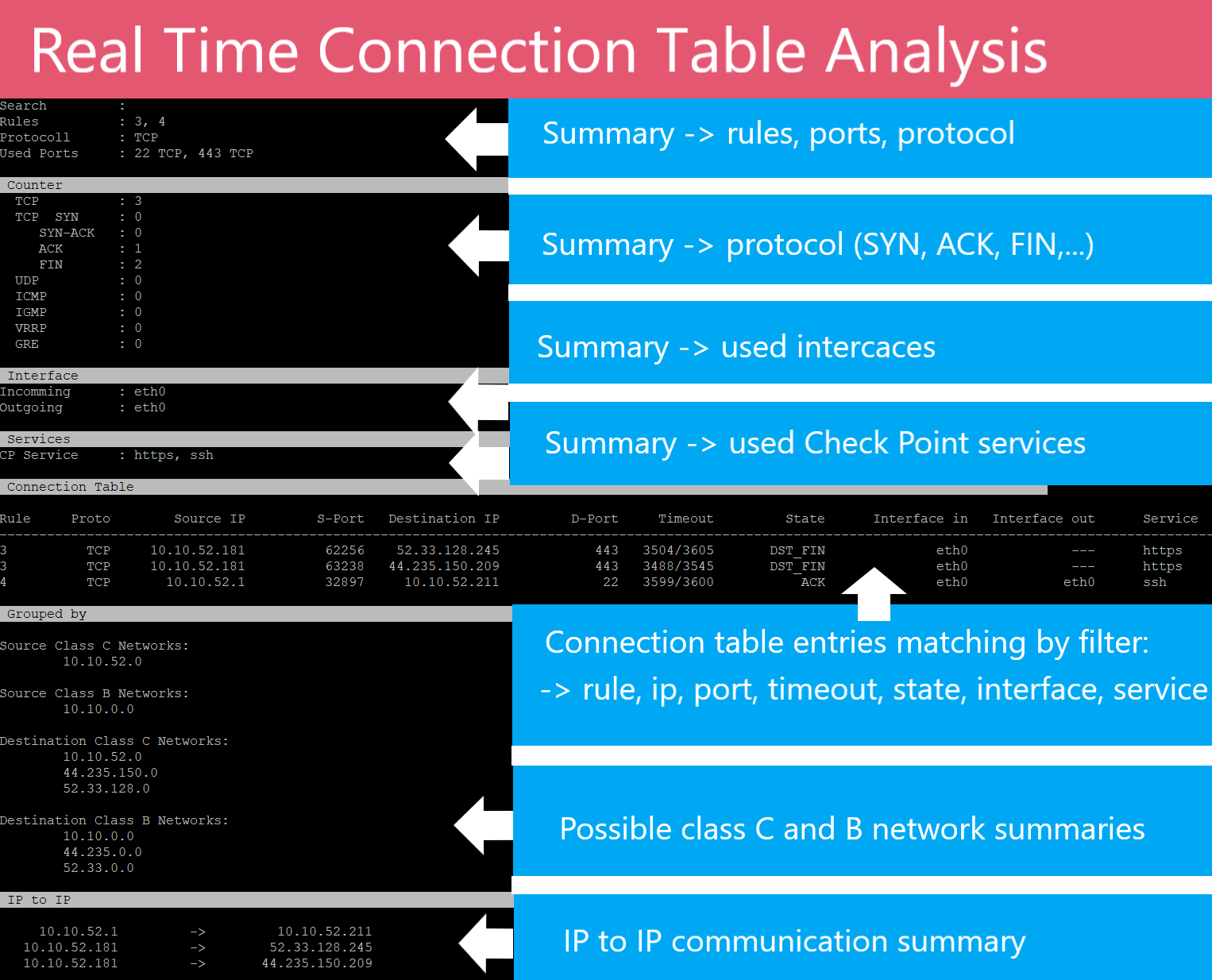
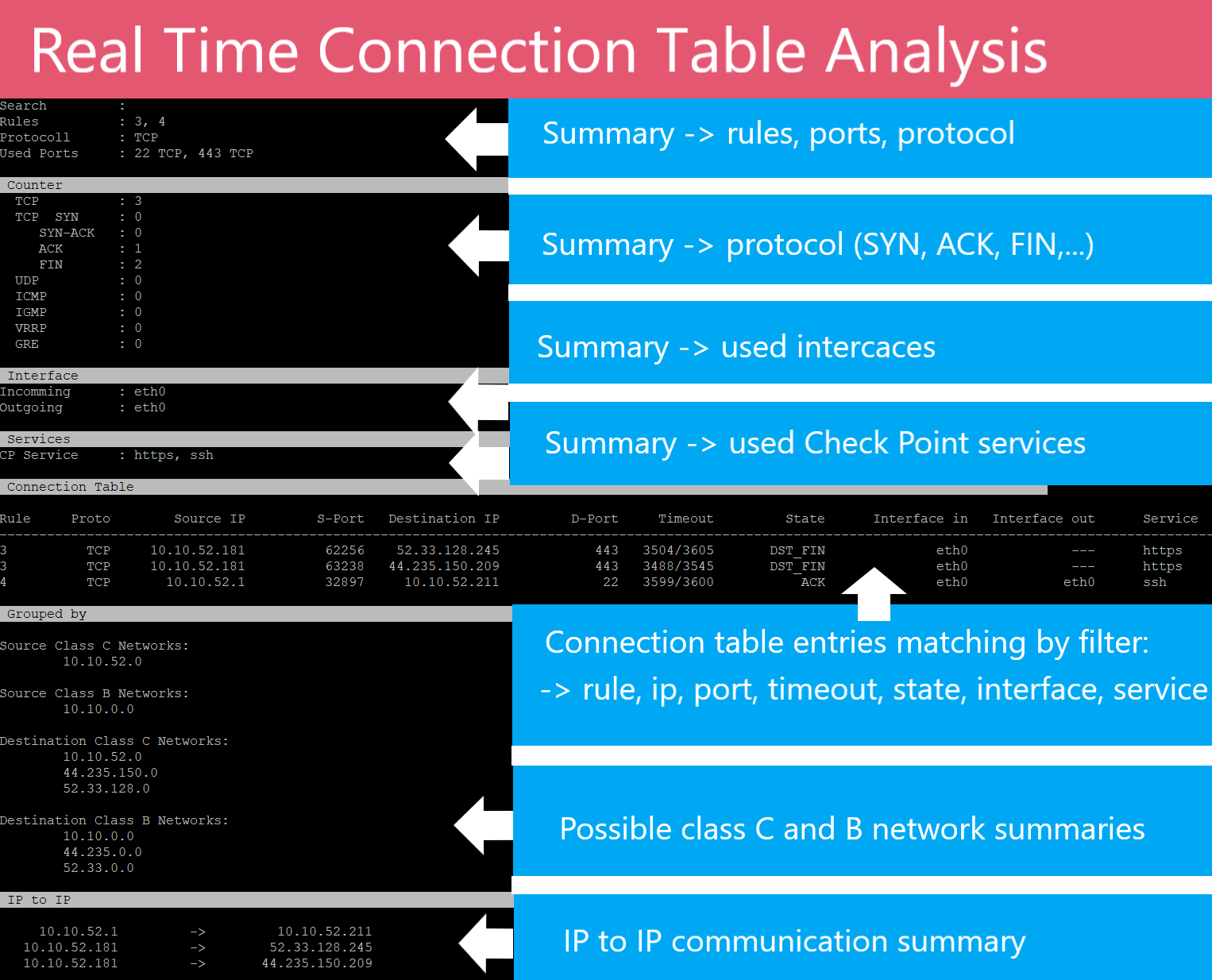
For many Check Point users the question arises again and again, which connections and services are used by a rule, a port, an destination IP or source IP in real time. For this purpose I have created a small tool, which all information about a rule can be read out in real time from the connection table.
This is good for optimizing the ruleset, as it provides a real-time view of the connection table with the corresponding info. This can be a good solution in more complex environments to see what this rule really do.
The following questions can be answered:
This tool will help you quickly answer these questions and many more.
| Tool |
|---|
When you execute this oneliner, a new cli command "econn" will be created.
After that, you only need to execute the following cli command in expert mode with the parameters.
The output of the tool always show:
Since version 3.0 VSX is supported:
On VSX systems, change to the corresponding virtual system with "vsenv" and execute "econn" on that VS system.
| Filter Syntax | Description |
| -a | Show the information about the complete connection table. |
| -r <rule number> | Show the information about a specific rule with the corresponding rule number. Inline rules for example 2.1 are not possible. You can only use the base rule in this case 2. |
| -p <port> | Show the information about a specific destination port with the corresponding port number. |
| -d <destination IP> | Show the information about a specific destination IP with the corresponding IP. |
| -s <source IP> | Show the information about a specific source IP with the corresponding IP. |
| -g <grep parameter> |
Search filter for the corresponding grep parameters in the raw data of "fw ctl conntab". |
| -e <grep parameter> |
Search filter for the corresponding grep parameters in the connection table output view. |
| Delete Connections |
Description |
| -x | Attention!!! This parameter deletes all connections from the connection table that match the filters. Grep parameters (-g) cannot be deleted in the combination with this option. This parameter is only available from R81 and higher. |
| Output extension | Description |
| -c | Shows the corresponding connection table entries. |
| -t | Tip! Display possible class C and B networks where the corresponding IP addresses from the connection table would match. This function is good to simplify rules. |
| -i | Displays only the summarized IP communication. Also used to simplify the set of rules. |
| -n |
No summary output. |
| File |
Description |
| -w <file name> | Write connection table to file. |
| -f <file name> |
Read connection table from file. Important! |
| Examples |
|---|
| Examples | Description |
| # econn -r 10 -c | Shows all basic informations (used Ports, counter TCP/UDP/ICMP...) to rule 10 and displays the appropriate connection table entries. |
| # econn -a | Gives an overview of all connectiontabel entries (used ports, used protocols and counter TCP/UDP/ICMP...). |
| # econn -p 443 -c | Displays all rules where port 443 is used and prints all connection table entries. |
| # econn -d 1.1.1.1 -c | Displays all rules where destination IP 1.1.1.1 is used and gives an overview of all connection table entries (used ports, used protocols and counter TCP/UDP/ICMP...) and prints all connection table entries. |
| # econn -s 1.1.1.1 -c | Displays all rules where source IP 1.1.1.1 is used and gives an overview of all connection table entries (used ports, used protocols and counter TCP/UDP/ICMP...) and prints all connection table entries. |
| # econn -s 1.1.1.0-1.1.1.255 |
Displays all rules where source IP range from 1.1.1.1 to 1.1.1.255 |
| # econn -r 10 -t -i | Shows all basic informations to rule 10 and summarizes all IP addresses to possible class C and B networks and output the IP communication summed by source IP's. |
| # econn -p 80 -t -i -c | Shows all possible informations to port 80 in the connection table: rules, connection summaries, used protocols and ports, grouped networks, IP communication |
| # econn -p 443 -g SYN -c |
Shows all possible informations to port 443 in the connection table with "TCP SYN" state |
| # econn -r 10 -p 53 -x | Attention!!! Delete all possible connections with port 53 in rule 10 in the connection table. |
| # econn -w test -p 433 |
Write the connection table to tar file where port 443 is used. |
| # econn -f test -c -e SYN |
Read the connection table from tar file and show the output with the filter view option for SYN. |
| # econn -n -p 443 -e SYN_SENT |
Don't show the connection summary + show connection table for port 443 and TCP state SYN. |
| Install Tool |
|---|
Use this auto installer script from "Spoiler" on the Firewall Gateway as CLI command in expert mode:
curl_cli -k http://www.ankenbrand24.de/inst_econn > /tmp/inst_econn && chmod 770 /tmp/inst_econn && /tmp/inst_econnOr "copy and past" the following script block from "Spoiler" to your Firewall Gateway (in expert mode):
cat <<EOT > /usr/bin/econn
#!/bin/bash
VERSION="4.0";
SHOW_CONN="0";
SHOW_GROUPED="0";
SHOW_IP="0";
DEL_CONN="0";
SUCHEN="";
FILTER_GREP="-v 'fgsdg'";
ENTRIE_GREP="-v 'hgdfk'";
FILE_Y="0";
FILE_FY="0";
SHOW_SUM="1";
echo "" > /tmp/econn_ip.txt
clear;
echo -e "\e[7m";printf '%.s ' {1..132}; echo;
echo " Real time connection table analysis by Heiko Ankenbrand 2021 (v\$VERSION) ";
printf '%.s ' {1..132};echo -e "\e[0m";
IsGATEWAY=`cpprod_util FwIsFirewallModule`;
if [ \$IsGATEWAY != "1" ] ;
then
echo ;
echo "This is not a gateway!";
echo ;
exit 1;
fi
while [[ \$# -gt 0 ]]
do
key1="\$1"
case \$key1 in
-h|--help.)
shift;
echo;
echo -e "\e[6m";echo -n " Help overview";printf '%.s ' {1..118};echo -e "\e[0m";
echo
echo "Filter Syntax"
echo " -a Show the information about the complete connection table.";
echo " -r <rule number> Show the information about a specific rule with the corresponding rule number.";
echo " -p <port> Show the information about a specific destination port with the corresponding port number.";
echo " -d <destination IP> Show the information about a specific destination IP with the corresponding IP.";
echo " -d <dIP_start-dIP_end> Show the information about a specific destination IP range with the corresponding IP.";
echo " -s <source IP> Show the information about a specific source IP with the corresponding IP.";
echo " -g <grep parameter> Filters the search for the corresponding grep parameters.";
echo ;
echo "Output extension";
echo " -c Shows the corresponding connection table entries.";
echo " -e Is an option that sets a grep filter only on the output of the connection table view.";
echo " -t Display possible class C and B networks where the corresponding IP addresses from ";
echo " the connection table would match. This function is good to simplify rules.";
echo " -i Displays only the summarized IP communication. Also used to simplify the set of rules.";
echo " -n No summary output";
echo ;
echo "Delete connection";
echo " -x Attention!!! This parameter deletes all connections from the connection table that match the "
echo " filters. Grep parameters (-g) cannot be deleted in the combination with this option.";
echo "File";
echo " -w <file name> Write connection table to file.";
echo " -f <file name> Read connection table from file.";
echo " Important!";
echo " Search filters only work when writing the file -w not with the option -f.";
echo -e "\e[6m";echo -n " Examples";printf '%.s ' {1..123};echo -e "\e[0m";
echo "# econn -r 10 -c Shows all basic informations (used Ports, counter TCP/UDP/ICMP...) to rule 10 and displays";
echo " the appropriate connection table entries.";
echo "# econn -a Gives an overview of all connectiontabel entries (used ports, used protocols and counter";
echo " TCP/UDP/ICMP...)";
echo "# econn -p 443 -c Displays all rules where port 443 is used and prints all connection table entries.";
echo "# econn -d 1.1.1.1 -c Displays all rules where destination IP 1.1.1.1 is used and gives an overview of all ";
echo " connection table entries (used ports, used protocols and counter TCP/UDP/ICMP...) and";
echo " prints all connection table entries.";
echo "# econn -s 1.1.1.1 -c Displays all rules where source IP 1.1.1.1 is used and gives an overview of all connection";
echo " table entries (used ports, used protocols and counter TCP/UDP/ICMP...) and prints all";
echo " connection table entries.";
echo "# econn -s 1.1.1.0-1.1.1.255 Displays all rules where source IP range from 1.1.1.1 to 1.1.1.255.";
echo "# econn -r 10 -t -i Shows all basic informations to rule 10 and summarizes all IP addresses to possible";
echo " class C and B networks and output the IP communication summed by source IP's.";
echo "# econn -p 80 -t -i -c Shows all possible informations to port 80 in the connection table: rules, connection ";
echo " summaries, used protocols and ports, grouped networks, IP communication.";
echo "# econn -p 443 -g SYN -c Shows all possible informations to port 443 in the connection table with 'TCP SYN' state";
echo "# econn -r 10 -p 53 -x Attention!!! Delete all possible connections with port 53 in rule 10 in the connection table.";
echo "# econn -w test -p 433 Write the connection table to tar file where port 443 is used.";
echo "# econn -f test Read the connection table from tar file and show the output.";
echo "# econn -f test -c -e SYN Read the connection table from tar file and show the output with the filter view option for SYN.";
echo "# econn -n -p 443 -e SYN_SENT Don't show the connection summary + show connection table for port 443 and TCP state SYN.";
echo;
exit 1;
;;
-x|-del)
shift;
SHOW_CONN="1";
DEL_CONN="1";
;;
-n)
shift;
SHOW_SUM="0";
SHOW_CONN="1";
;;
-s|--sip)
key="\$2";
FILTER="\$FILTER -sip=\$key";
SUCHEN="\$SUCHEN Source IP=\$key ";
shift;
shift;
;;
-d|--dip)
key="\$2";
FILTER="\$FILTER -dip=\$key";
SUCHEN="\${SUCHEN}Destination IP=\$key ";
shift;
shift;
;;
-p|--port)
key="\$2";
FILTER="\$FILTER -dport=\$key";
SUCHEN="\${SUCHEN}DPort=\$key ";
shift;
shift;
;;
-a|--all)
key="\$2";
FILTER="";
SUCHEN="Complete connection table!";
shift;
;;
-r|--role)
key="\$2";
FILTER="\$FILTER -rule=\$key";
SUCHEN="\${SUCHEN}Rule=\$key ";
shift;
shift;
;;
-g|--grep)
key="\$2";
FILTER_GREP="\$key";
SUCHEN="\${SUCHEN}GREP='\$key' ";
shift;
shift;
;;
-e)
ENTRIE_GREP="\$2";
SHOW_CONN="1";
if [ "x\$ENTRIE_GREP" = "x" ]
then
echo "Parameter -e not correct set!";
ENTRIE_GREP="-v dsfgdsj";
fi
shift;
shift;
;;
-t|-tip)
shift;
SHOW_GROUPED="1";
;;
-i|-ip)
shift;
SHOW_IP="1";
;;
-c|-conn)
SHOW_CONN="1";
shift;
;;
-w)
FILE_W="\$2";
FILE_W="\${FILE_W}.tgz";
FILE_Y="1";
shift;
shift;
;;
-f)
FILE_F="\$2";
FILE_F="\${FILE_F}.tgz";
FILE_FY="1";
shift;
shift;
;;
*)
POSITIONAL+=("\$1") # save it in an array for later
shift # past argument
;;
esac
done
if [ \$FILE_FY == "1" ] ;
then
if test -f "\$FILE_F";
then
echo -e "\e[6m";echo -n " Read connection table from tar archive";printf '%.s ' {1..93};echo -e "\e[0m";
echo "Read file : \$FILE_F";
tar xzfP \$FILE_F;
FILTER="";
SUCHEN="";
if [ ! -f /tmp/econn_ports ]; then
echo;
echo "File /tmp/econn_ports not found in tar!";
echo;
exit 1;
fi
if [ ! -f /tmp/econn_ip.txt ]; then
echo;
echo "File /tmp/econn_ip.txt not found in tar!";
echo;
exit 1;
fi
if [ ! -f /tmp/econn_if ]; then
echo;
echo "File /tmp/econn_if not found in tar!";
echo;
exit 1;
fi
echo -n "CT entries : ";
more /tmp/econn_ip.txt | wc -l;
else
echo;
echo "File \$FILE_F not exist";
echo;
exit 1;
fi
else
fw ctl conntab \$FILTER 2>&1 |grep \$FILTER_GREP | grep -v "Got NULL" |grep -v "gen_services_array Failed" | egrep -v '^\s*$|^#' > /tmp/econn_ip.txt;
fw ctl iflist > /tmp/econn_if;
if test -f "\$FWDIR/state/__tmp/FW1/local.set"; then
more \$FWDIR/state/__tmp/FW1/local.set | grep srv_name | awk '{split(\$0,a,","); print a[1] " " a[3];}' | sed -e 's/: (\"//g' > /tmp/econn_ports;
fi
fi
if [ \$FILE_Y == "1" ] ;
then
echo -e "\e[6m";echo -n " Write connection table to tar archive";printf '%.s ' {1..94};echo -e "\e[0m";
echo -n "Search filter : \$SUCHEN";
tar -czf \$FILE_W -P /tmp/econn_ip.txt /tmp/econn_if /tmp/econn_ports;
echo;
echo -n "Connection table entries : ";
more /tmp/econn_ip.txt | wc -l;
echo "Written in file : \$FILE_W";
echo ;
exit 1;
fi
if [ \$SHOW_SUM == "1" ] ;
then
echo -e "\e[6m";echo -n " Connection Summary";printf '%.s ' {1..113};echo -e "\e[0m";
echo -n "Search : \$SUCHEN";
vsx_system=\`fw vsx stat 2>&1 | grep -c "VSX is not supported"\`
echo ;
if [ \$vsx_system == "0" ]
then
echo -n "VSX VS : ";
vsx_vsenv1=\`vsx get | awk '{split(\$0,a,"("); sub(/ID /, "", a[2]); sub(/)./, "", a[2]); print a[2]; }'\`
echo "\$vsx_vsenv1"
fi
echo -n "Rules : ";
more /tmp/econn_ip.txt | awk '{print \$6 " "\$2 \$3 \$4 " "\$5 " "\$8}' | sed -e 's/src=//g' | sed -e 's/\],dest=\[/ /g' | sed -e 's/\],/ /g' | sed -e 's/)\;//g' | sed -e 's/\[//g' | sed -e 's/rule\=/ /g' | sed -e 's/\,/ /g' | sed -e 's/state\=/ /g' | sed -e 's/Ifn[c,s]in\=[0-9]*//g' | sed -e 's/Ifn[c,s]out\=[0-9]*//g' | egrep -v '^\s*$|^#' | awk '{printf "%s, \n", \$1}' 2>&1 | grep -v -E '^[1-9][0-9][0-9][0-9][0-9][0-9]' |grep -v '0,' | sort -n | uniq | tr -d '\n' | sed -e 's/0000002f/GRE/g' | sed -e 's/00000070/VRRP/g' | sed 's/\(.*\),/\1\t/' | sed -e 's/^, //g'
echo ;
echo -n "Protocoll : ";
more /tmp/econn_ip.txt | awk '{print \$6 " "\$2 \$3 \$4 " "\$5 " "\$8}' | sed -e 's/src=//g' | sed -e 's/\],dest=\[/ /g' | sed -e 's/\],/ /g' | sed -e 's/)\;//g' | sed -e 's/\[//g' | sed -e 's/rule\=/ /g' | sed -e 's/\,/ /g' | sed -e 's/state\=/ /g' | sed -e 's/Ifn[c,s]in\=[0-9]*//g' | sed -e 's/Ifn[c,s]out\=[0-9]*//g' | egrep -v '^\s*$|^#' | awk '{printf "%s, \n", \$6}' 2>&1 | sort -n | uniq | tr -d '\n' | sed -e 's/0000002f/GRE/g' | sed -e 's/00000070/VRRP/g' | sed 's/\(.*\),/\1\t/' | sed -e 's/^, //g'
echo;
echo -n "Used Ports : ";
more /tmp/econn_ip.txt | awk '{print \$6 " "\$2 \$3 \$4 " "\$5 " "\$8}' | sed -e 's/src=//g' | sed -e 's/\],dest=\[/ /g' | sed -e 's/\],/ /g' | sed -e 's/)\;//g' | sed -e 's/\[//g' | sed -e 's/rule\=/ /g' | sed -e 's/\,/ /g' | sed -e 's/state\=/ /g' | sed -e 's/Ifn[c,s]in\=[0-9]*//g' | sed -e 's/Ifn[c,s]out\=[0-9]*//g' | egrep -v '^\s*$|^#' | awk '{printf "%s %s, \n", \$5, \$6}' 2>&1 | sort -n | uniq | tr -d '\n' | sed -e 's/0000002f/GRE/g' | sed -e 's/00000070/VRRP/g' | sed 's/\(.*\),/\1\t/' | sed -e 's/^ , //g' | sed -e 's/0 ICMP, //g' | sed -e 's/0 IGMP, //g' | sed -e 's/0 VRRP, //g'
echo -e "\n\e[6m";echo -n " Counter";printf '%.s ' {1..124};echo -e "\e[0m";
echo -n ' TCP : ';more /tmp/econn_ip.txt | grep 'TCP' |wc -l;
echo -n ' TCP SYN : ';more /tmp/econn_ip.txt | grep 'SYN_SENT' |wc -l;
echo -n ' SYN-ACK : ';more /tmp/econn_ip.txt | grep 'SYN_ACK' |wc -l;
echo -n ' ACK : ';more /tmp/econn_ip.txt | grep 'ESTAB' |wc -l;
echo -n ' FIN : ';more /tmp/econn_ip.txt | grep 'FIN' |wc -l;
echo -n ' UDP : ';more /tmp/econn_ip.txt | grep 'UDP' |wc -l
echo -n ' ICMP : ';more /tmp/econn_ip.txt | grep 'ICMP' |wc -l;
echo -n ' IGMP : ';more /tmp/econn_ip.txt | grep 'IGMP' |wc -l;
echo -n ' VRRP : ';more /tmp/econn_ip.txt | grep '00000070)' |wc -l;
echo -n ' GRE : ';more /tmp/econn_ip.txt | grep '0000002f)' |wc -l;
echo -e "\e[6m";echo -n " Interface";printf '%.s ' {1..122};echo -e "\e[0m";
echo -n "Incomming : ";
more /tmp/econn_ip.txt | awk '{split(\$0,a,";"); print a[2];}' | awk '{split(\$0,b,",") ;print b[4];}' |grep in | sort |uniq > /tmp/econn_in
more /tmp/econn_ip.txt | awk '{split(\$0,a,";"); print a[2];}' | awk '{split(\$0,b,",") ;print b[5];}' |grep in | sort |uniq >> /tmp/econn_in
more /tmp/econn_ip.txt | awk '{split(\$0,a,";"); print a[2];}' | awk '{split(\$0,b,",") ;print b[6];}' |grep in | sort |uniq >> /tmp/econn_in
more /tmp/econn_in | sort |uniq| awk '{split(\$1,c,"=") ;system("cat /tmp/econn_if |grep ^"c[2] ); }' | awk '{split(\$0,d,":") ;print "," d[2] ;}' |sort | uniq| tr -d '\n' | sed -e 's/^, //g'
echo
echo -n "Outgoing : ";
more /tmp/econn_ip.txt | awk '{split(\$0,a,";"); print a[2];}' | awk '{split(\$0,b,",") ;print b[4];}' |grep out | sort |uniq > /tmp/econn_out
more /tmp/econn_ip.txt | awk '{split(\$0,a,";"); print a[2];}' | awk '{split(\$0,b,",") ;print b[5];}' |grep out | sort |uniq >> /tmp/econn_out
more /tmp/econn_ip.txt | awk '{split(\$0,a,";"); print a[2];}' | awk '{split(\$0,b,",") ;print b[6];}' |grep out | sort |uniq >> /tmp/econn_out
more /tmp/econn_out | sort |uniq| awk '{split(\$1,c,"=") ;system("cat /tmp/econn_if |grep ^"c[2] ); }' | awk '{split(\$0,d,":") ;print "," d[2] ;}' |sort |uniq | tr -d '\n' | sed -e 's/^, //g'
echo
echo -e "\e[6m";echo -n " Services";printf '%.s ' {1..123};echo -e "\e[0m";
echo -n "CP Service : ";
more /tmp/econn_ip.txt | awk '{split(\$0,a,";"); print a[2];}' | awk '{split(\$0,b,",") ; print b[3];}' |grep service |grep -v "(" | sort |uniq > /tmp/econn_service_used
more /tmp/econn_ip.txt | awk '{split(\$0,a,";"); print a[2];}' | awk '{split(\$0,b,",") ; print b[4];}' |grep service |grep -v "(" | sort |uniq >> /tmp/econn_service_used
more /tmp/econn_service_used | sort |uniq| awk '{split(\$1,c,"=") ;system("cat /tmp/econn_ports |grep ^"c[2] ); }' | awk '{split(\$0,b," ") ; print ", " b[2];}' | tr -d '\n' | sed -e 's/^, //g' > /tmp/econn_service_used_all
more /tmp/econn_ip.txt | awk '{split(\$0,a,";"); print a[2];}' | awk '{split(\$0,b,",") ; print b[3];}' |grep service |grep "(" |sort |uniq | awk '{split(\$1,s2,"("); sub(/)/, "[[:blank:]]",s2[2]); service_id="^"s2[2]; system("cat /tmp/econn_ports |egrep "service_id)}' |awk '{split(\$0,b," ") ; print ", " b[2];}' | tr -d '\n' >> /tmp/econn_service_used_all
more /tmp/econn_ip.txt | awk '{split(\$0,a,";"); print a[2];}' | awk '{split(\$0,b,",") ; print b[4];}' |grep service |grep "(" |sort |uniq | awk '{split(\$1,s2,"("); sub(/)/, "[[:blank:]]",s2[2]); service_id="^"s2[2]; system("cat /tmp/econn_ports |egrep "service_id)}' |awk '{split(\$0,b," ") ; print ", " b[2];}' | tr -d '\n' >> /tmp/econn_service_used_all
more /tmp/econn_service_used_all | sed -e 's/, FW1_omi-sic(40)//g' | sed -e 's/^, //g'
echo
fi
if [ \$SHOW_CONN == "1" ] ;
then
echo -e "\e[6m";echo -n " Connection Table";printf '%.s ' {1..115};echo -e "\e[0m";
echo -e "\nRule Proto Source IP S-Port Destination IP D-Port Timeout State Interface in Interface out Service";
printf '%.s-' {1..160};
echo;
more /tmp/econn_ip.txt | egrep -v '^\s*$|^#'| awk -f /opt/etool/script/econn_awk1 -v vsx_system="\$vsx_system" | sort -n | sed 's/^[1-9][0-9][0-9][0-9][0-9][0-9]/-imp->/g' | grep \$ENTRIE_GREP;
fi
if [ \$SHOW_GROUPED == "1" ] ;
then
echo -e "\e[6m";echo -n " Grouped by";printf '%.s ' {1..121};echo -e "\e[0m";
# printf '%.s-' {1..50};echo -e "\nGrouped by ";printf '%.s-' {1..50};
echo -e "\nSource Class C Networks:";
more /tmp/econn_ip.txt | awk '{print \$6 " "\$2 \$3 \$4 " "\$5 " "\$8}' | sed -e 's/src=//g' | sed -e 's/\],dest=\[/ /g' | sed -e 's/\],/ /g' | sed -e 's/)\;//g' | sed -e 's/\[//g' | sed -e 's/rule\=/ /g' | sed -e 's/\,/ /g' | sed -e 's/state\=/ /g' | sed -e 's/Ifn[c,s]in\=[0-9]*//g' | sed -e 's/Ifn[c,s]out\=[0-9]*//g' | egrep -v '^\s*$|^#'| awk '{split(\$2,a,"."); printf "\t%s.%s.%s.0\n", a[1],a[2],a[3]}' 2>&1 | sort -n | uniq | sed -e 's/\.\.\.0//g' | sed -e 's/\.\.0\.0//g'
echo -e "\nSource Class B Networks:";
more /tmp/econn_ip.txt | awk '{print \$6 " "\$2 \$3 \$4 " "\$5 " "\$8}' | sed -e 's/src=//g' | sed -e 's/\],dest=\[/ /g' | sed -e 's/\],/ /g' | sed -e 's/)\;//g' | sed -e 's/\[//g' | sed -e 's/rule\=/ /g' | sed -e 's/\,/ /g' | sed -e 's/state\=/ /g' | sed -e 's/Ifn[c,s]in\=[0-9]*//g' | sed -e 's/Ifn[c,s]out\=[0-9]*//g' | egrep -v '^\s*$|^#'| awk '{split(\$2,a,"."); printf "\t%s.%s.0.0\n", a[1],a[2],a[3]}' 2>&1 | sort -n | uniq | sed -e 's/\.\.\.0//g' | sed -e 's/\.\.0\.0//g'
echo -e "\nDestination Class C Networks:";
more /tmp/econn_ip.txt | awk '{print \$6 " "\$2 \$3 \$4 " "\$5 " "\$8}' | sed -e 's/src=//g' | sed -e 's/\],dest=\[/ /g' | sed -e 's/\],/ /g' | sed -e 's/)\;//g' | sed -e 's/\[//g' | sed -e 's/rule\=/ /g' | sed -e 's/\,/ /g' | sed -e 's/state\=/ /g' | sed -e 's/Ifn[c,s]in\=[0-9]*//g' | sed -e 's/Ifn[c,s]out\=[0-9]*//g' | egrep -v '^\s*$|^#'| awk '{split(\$4,a,"."); printf "\t%s.%s.%s.0\n", a[1],a[2],a[3]}' 2>&1 | sort -n | uniq | sed -e 's/\.\.\.0//g' | sed -e 's/\.\.0\.0//g'
echo -e "\nDestination Class B Networks:";
more /tmp/econn_ip.txt | awk '{print \$6 " "\$2 \$3 \$4 " "\$5 " "\$8}' | sed -e 's/src=//g' | sed -e 's/\],dest=\[/ /g' | sed -e 's/\],/ /g' | sed -e 's/)\;//g' | sed -e 's/\[//g' | sed -e 's/rule\=/ /g' | sed -e 's/\,/ /g' | sed -e 's/state\=/ /g' | sed -e 's/Ifn[c,s]in\=[0-9]*//g' | sed -e 's/Ifn[c,s]out\=[0-9]*//g' | egrep -v '^\s*$|^#'| awk '{split(\$4,a,"."); printf "\t%s.%s.0.0\n", a[1],a[2],a[3]}' 2>&1 | sort -n | uniq | sed -e 's/\.\.\.0//g' | sed -e 's/\.\.0\.0//g'
fi
if [ \$SHOW_IP == "1" ] ;
then
echo -e "\e[6m";echo -n " IP to IP";printf '%.s ' {1..124};echo -e "\e[0m\n";
more /tmp/econn_ip.txt | awk '{print \$6 " "\$2 \$3 \$4 " "\$5 " "\$8}' | sed -e 's/src=//g' | sed -e 's/\],dest=\[/ /g' | sed -e 's/\],/ /g' | sed -e 's/)\;//g' | sed -e 's/\[//g' | sed -e 's/rule\=/ /g' | sed -e 's/\,/ /g' | sed -e 's/state\=/ /g' | sed -e 's/Ifn[c,s]in\=[0-9]*//g' | sed -e 's/Ifn[c,s]out\=[0-9]*//g' | egrep -v '^\s*$|^#' | awk '{printf "%15s -> \t%15s \n", \$2,\$4}' 2>&1 | sort -n | uniq
fi
if [ \$DEL_CONN == "1" ] ;
then
OS=`cat /etc/cp-release | cut -c 17- | sed 's/^ *//g' | sed 's/\s*\$//g' | cut -c -3 | grep -c '^R8[1-9]'`
if [[ \$OS == "1" ]] ;
then
if [[ \$FILTER_GREP == *"fgsdg"* ]] ;
then
echo -e "\e[6m";echo -n " Delete Connections";printf '%.s ' {1..114};echo -e "\e[0m\n";
echo
echo ">>>> ATTENTION <<<<"
echo
echo "This will clear all the connections matching the filter in the connection table!!!"
echo -n "Are you sure (yes/no)? [n] "
read DEL_CONN_1
if [[ \$DEL_CONN_1 == "yes" ]] || [[ \$DEL_CONN_1 == "y" ]] ;
then
echo;
echo -n "Are you really sure you want to do this (yes/no)? [n] "
FILTER="-x\$FILTER";
if [ -f /var/log/econn_delete_connections.txt ];
then
rm /var/log/econn_delete_connections.txt 2>&1> /dev/null;
fi
echo;
echo;
echo "###########################################################################################################";
echo "There is currently a bug in R81 and R80.10. This means"
echo "that deleting does not work correctly, because the filters"
echo "do not match. Therefore I have disabled the function."
echo;
echo "fw ctl contab \$FILTER";
echo
echo "More read here:"
echo "https://community.checkpoint.com/t5/General-Topics/fw-ctl-contab-x-issue-in-R81-10/m-p/128288#M23421"
echo;
echo "###########################################################################################################";
echo;
exit 1;
fw ctl conntab \$FILTER: > /var/log/econn_delete_connections.txt;
echo
more /var/log/econn_delete_connections.txt | grep "Nothing done." | sed -e 's/Are you sure (yes\/no)? \[n\] //g'
echo
echo "All deleted connections respectively the result are listed in the following file:"
echo "/var/log/econn_delete_connections.txt";
else
echo
echo "Nothing done.";
fi
else
echo
echo "You have set grep filter. This does not work with deleting the connections!";
echo
echo "Nothing done.";
fi
else
echo "-x is only posible in R81 and above!"
fi
fi
echo;
EOT
[ -d "/opt/etool" ] || mkdir /opt/etool;
[ -d "/opt/etool/script" ] || mkdir /opt/etool/script;
cat <<EOT > /opt/etool/script/econn_awk1
{
where=match(\$4, "TCP");
if (where !=0) { rule=\$6 ; state=\$8; service=\$9 ; timer =\$5 ; proto="TCP"; dst=\$3; src=\$2; if_in=\$10;if_out=\$11; where=match(\$13, "out"); if (where !=0) {if_out=\$13 } } ;
where=match(\$4, "UDP");
if (where !=0) { rule=\$6 ; state="state=---"; service=\$7 ; timer =\$5 ; proto="UDP"; dst=\$3; src=\$2; if_in=\$8;if_out=\$9; where=match(\$11, "out"); if (where !=0) {if_out=\$11 } } ;
where=match(\$4, "0000002f");
if (where !=0) { rule=\$6 ; state="state=---"; service=\$7 ; timer =\$5 ; proto="GRE"; dst=\$3; src=\$2; if_in=\$8;if_out=\$9} ;
where=match(\$4, "00000070");
if (where !=0) { rule=\$6 ; state="state=---"; service=\$7 ; timer =\$5 ; proto="VRRP"; dst=\$3; src=\$2; if_in=\$8;if_out=\$9} ;
where=match(\$4, "ICMP");
if (where !=0) { rule=\$6 ; state="state=---"; service=\$7 ; timer =\$5 ; proto="ICMP"; dst=\$3; src=\$2; if_in=\$8;if_out=\$9; where=match(\$11, "out"); if (where !=0) {if_out=\$11 } };
where=match(\$4, "IGMP");
if (where !=0) { rule=\$6 ; state="state=---"; service=\$7 ; timer =\$5 ; proto="IGMP"; dst=\$3; src=\$2; if_in=\$8;if_out=\$9; where=match(\$11, "out"); if (where !=0) {if_out=\$11 } };
split(service,s,"=");
service=s[2];
sub(/,/, "", service);
where=match(\$service, ")");
if (where !=0) {split(service,s1,"("); service=s1[2];sub(/)/, "", service);}
split(state,h,"=");
state=h[2];
split(rule,h,"=");
rule=h[2];
where=match(\$9, "in");
if (where !=0) { if_in=\$9};
where=match(\$10, "in");
if (where !=0) { if_in=\$10};
where=match(\$11, "in");
if (where !=0) { if_in=\$11};
where=match(\$9, "out");
if (where !=0) { if_out=\$9};
where=match(\$10, "out");
if (where !=0) { if_out=\$10};
where=match(\$11, "out");
if (where !=0) { if_out=\$11};
where=match(\$12, "out");
if (where !=0) { if_out=\$12};
where=match(\$13, "out");
if (where !=0) { if_out=\$13};
split(if_in,h,"=");
if_in=h[2];
split(if_out,h,"=");
if_out=h[2];
split(src,h,"=");
split(h[2],h1,",");
src_ip=h1[1];
src_p=h1[2] ;
split(dst,h,"=");
split(h[2],h1,",");
dst_ip=h1[1];
dst_p=h1[2];
sub(/TCP_ESTABLISHED/, "ESTABLISHED", state);
sub(/,/, "", state);
sub(/,/, "", rule);
sub(/,/, "", timer);
sub(/,/, "", service);
sub(/\[/, "", src_ip);
sub(/\[/, "", dst_ip);
sub(/\]/, "", src_p);
sub(/\]/, "", dst_p);
sub(/,/, "", if_in);
sub(/,/, "", if_out);
read_file_into_array("/tmp/econn_if", File);
where=match(\$service, ")");
if (where ==0) {
read_file_into_array1("/tmp/econn_ports", File1);
service_last=File1[service];
}
else {
service_last=service;
}
if_out_last=File[if_out];
if (length(if_out_last) <= 0) {if_out_last="---";}
if_in_last=File[if_in];
if (length(if_in_last) <= 0) {if_in_last="---";}
if (length(service_last) <= 0) {service_last="---";}
if (proto == "icmp") { dst_p="---"; src_p="---"; }
printf "%.6s \t%6s \t%15s \t%6s \t%15s \t%6s \t%10s \t%11s \t%10s \t%10s \t%.15s \n", rule, proto, src_ip, src_p, dst_ip, dst_p, timer, state , if_in_last, if_out_last, service_last ;
service="";
rule="";
timer="";
state="";
proto="" ;
dst="" ;
src="";
if_in="";
if_out="";
}
function read_file_into_array(file, array ,status, record, count ) {
count = 0;
while (1) {
status = getline record < file
if (status == -1) {
print "Failed to read file " file;
exit 1;
}
if (status == 0) break;
split(record,r,":");
sub(/ /, "", r[1]);
array[r[1]] = r[2];
}
close(file);
return count
}
function read_file_into_array1(file, array ,status, record, count ) {
count = 0;
while (1) {
status = getline record < file
if (status == -1) {
print "Failed to read file " file;
exit 1;
}
if (status == 0) break;
split(record,r," ");
sub(/ /, "", r[1]);
array[r[1]] = r[2];
}
close(file);
return count
}
EOT
chmod 770 /usr/bin/econn
chmod 770 /opt/etool/script/econn_awk1
| Version |
|---|
0.1 08-08-2021 - oneliner to show all connection table entries
(ONELINER - Formatted Connection Table)
0.9 08-12-2021 - Bugs fixed
1.0 08-26-2021 - Version v1.0 - This version only shows info about certain rules
(Easy Tool - Real time rule analysis v1.0)
2.0 08-25-2021 - New version for filtering by rule, port, dst IP and src IP
2.1 08-26-2021 - Bugs fixed
2.2 08-27-2021 - Add -g grep parameter
2.3 08-28-2021 - Add -x delete parameter
(This parameter is only available from R81 and higher.)
2.4 08-28-2021 - There is currently a bug in R81 and R81.10 with "fw ctl conntab -x -rule=3"
Therefore I have disabled this function -x.
('fw ctl contab -x' issue in R81.10)
2.5 09-01-2021 - Bugs fixed (conn issue)
2.6 09-08-2021 - Incoming and outgoing interface added
2.7 09-09-2021 - Check Point service names added
2.8b 09-09-2021 - Bugs fixed
( --> more \$FWDIR/state/__tmp/FW1/ )
2.9 09-10-2021 - Now with extended connection table view:
incoming interface, outgoing interface, Check Point service name
2.9i 09-10-2021 - Bugs fixed
(ICMP issues, interface issue, Check Point service issue)
3.0 09-11-2021 - VSX support
3.1 09-11-2021 - Bugs fixed
(option -g issue, VSX "fw ctl conntab" issue)
3.2 09-12-2021 - Bugs fixed
( option -r /-s /-d /-p /-g issue)
3.3 09-13-2021 - Design modification
4.0 09-15-2021 - File read and write, added -n no summary output
4.0f 09-16-2021 - Performance optimization of the script for large connection tables.
4.0g 09-23-2021 - Add -h option
4.0h 14-11-2021 - Performance optimization for VSX environments
5.0a 01-28-2026 - now for R82 and R82.10
| New version and demo video |
|---|
Use version 6.0 or higher:
ECONN - Easy Connection Table Tool 6.x
Here is a demo video for version 6.0:
| Overview |
|---|
From version R80.10 to version R81.10.
For many Check Point users the question arises again and again, which connections and services are used by a rule, a port, an destination IP or source IP in real time. For this purpose I have created a small tool, which all information about a rule can be read out in real time from the connection table.
This is good for optimizing the ruleset, as it provides a real-time view of the connection table with
...;
Hi @HeikoAnkenbrand
The script simplifies the search in the connection table.
Great idea and thanks for your great contributions.
Small note:
Unfortunately, the use of multiple filters -p 53 -d 8.8.8.8 does not work.
Hi
@HeikoAnkenbrand
The script simplifies the search in the connection table.
Great idea and thanks for your great contributions.
Small note:
Unfortunately, the use of multiple filters -p 53 -d 8.8.8.8 does not work.
Hi @Reimar_W,
I reworked this in the script and it now works with multiple filter parameters.
Thanks
Heiko
It's really cool how you can browse with this tool in the connection tabel.
This allows you to get information quickly and easily.
Great job
@HeikoAnkenbrand
It's really cool how you can browse with this tool in the connection tabel.
This allows you to get information quickly and easily.
Great job
@HeikoAnkenbrand
Hi @HeikoAnkenbrand,
nice solution.
What is the state "conn" in the output?
Hi @HeikoAnkenbrand,
nice solution.
What is the state "conn" in the output?
Hi @Power_Support
Bug is fixed in version 2.5!
Great tool @HeikoAnkenbrand . How about VSX, known problems ?
Great tool @HeikoAnkenbrand . How about VSX, known problems ?
;Hi @Wolfgang,
The script is very complex and I try to integrate VSX. However, one or two functions are not yet VSX compatible.
Please give me another week or two 😉
Hi Heiko,
You could add a small option for the top rules using cpstat blades and take the 5 rules and show them .
Cheers
Hi @Wolfgang,
After a weekend with a lot of programming work I made the script VSX compatible.
You only need to run the command in a VS instance:
# vsenv xy
# econn ...
Now the VS instance should be displayed as shown in the picture:
work like a charm with VSX. Saved me a lot of time at the moment investigating a problem with some connections.
👍👍
work like a charm with VSX. Saved me a lot of time at the moment investigating a problem with some connections.
👍 👍
;From version 2.9 with extended connection table view:
+ Incoming interface
+ Outgoing interface
+ Check Point service name
got a few errors (r80.20 hf take188) Yes, I know it's "old". 🙂
using -t -i -c
awk: fatal: can't open source file `/opt/etool/script/econn_awk1' for reading (No such file or directory)
also
Incomming : sh: -c: line 0: syntax error near unexpected token `('
sh: -c: line 0: `cat /tmp/econn_if |grep ^domain-udp(122)'
got a few errors (r80.20 hf take188) Yes, I know it's "old". 🙂
using -t -i -c
awk: fatal: can't open source file `/opt/etool/script/econn_awk1' for reading (No such file or directory)
also
Incomming : sh: -c: line 0: syntax error near unexpected token `('
sh: -c: line 0: `cat /tmp/econn_if |grep ^domain-udp(122)'
Hello @HeikoAnkenbrand
In case of inline rules the -r flag doesn't seem to work. For a example for a rule 2.1,2.2 etc.
| -r <rule number> | Show the information about a specific rule with the corresponding rule number. |
BR,
Kostas
Hello @HeikoAnkenbrand
In case of inline rules the -r flag doesn't seem to work. For a example for a rule 2.1,2.2 etc.
| -r <rule number> | Show the information about a specific rule with the corresponding rule number. |
BR,
Kostas
;Hi @KostasGR,
I use the command "fw ctl conntab" to display the connection tab. Unfortunately this does not support inline rules. Therefore, you can only use the basic inline layer rule. Unfortunately, this cannot be changed technically.
Here is an example from my lab environment:
fw ctl conntab -r 3
Output tool
Hi @KostasGR,
I use the command "fw ctl conntab" to display the connection tab. Unfortunately this does not support inline rules. Therefore, you can only use the basic inline layer rule. Unfortunately, this cannot be changed technically.
Here is an example from my lab environment:
fw ctl conntab -r 3
Output tool
;
would like to try this, but I get:
/bin/econn: line 10: [[: $#: syntax error: operand expected (error token is "$#")
fw ver
This is Check Point's software version R80.40 - Build 124
uname -a
Linux hostname 3.10.0-957.21.3cpx86_64 #1 SMP Sun Apr 18 18:41:00 IDT 2021 x86_64 x86_64 x86_64 GNU/Linux
Regards,
Henrik
would like to try this, but I get:
/bin/econn: line 10: [[: $#: syntax error: operand expected (error token is "$#")
fw ver
This is Check Point's software version R80.40 - Build 124
uname -a
Linux hostname 3.10.0-957.21.3cpx86_64 #1 SMP Sun Apr 18 18:41:00 IDT 2021 x86_64 x86_64 x86_64 GNU/Linux
Regards,
Henrik
;Great job.
Version 4.0 is now available with many new features:
- VSX Support
- Write connection table to file
- Read connection table from file
- No summary output (option -n)
- Search filter for the corresponding grep parameters in the connection table view output.
Version 4.0 is now available with many new features:
- VSX Support
- Write connection table to file
- Read connection table from file
- No summary output (option -n)
- Search filter for the corresponding grep parameters in the connection table view output.
Hello @HeikoAnkenbrand,
first of all a big thank you for another great tool here for the CheckMates community.
The script runs on all our gateways. It is a bit slow with more than 100K connection table entries.
But otherwise a great solution.
Hello @HeikoAnkenbrand,
first of all a big thank you for another great tool here for the CheckMates community.
The script runs on all our gateways. It is a bit slow with more than 100K connection table entries.
But otherwise a great solution.
In the last few days I have spent a lot of time optimizing the code. Now even larger connection tabs should be output in a reasonable time.
From version 4.0e I will optimize the script code a bit more.
In the latest version 4.0g the script is performance optimized. Therefore, connection tabs larger than 100K can be displayed quickly.
Hi Heiko, Just tried pasting in the script and got this:
Real time connection table analysis by Heiko Ankenbrand 2021 (v4.0)
/usr/bin/econn: line 308: syntax error near unexpected token `\$2,a,"."'
/usr/bin/econn: line 308: ` more /tmp/econn_ip.txt | awk '{print \$6 " "\$2 \$3 \$4 " "\$5 " "\$8}' | sed -e 's/src=//g' | sed -e 's/\],dest=\[/ /g' | sed -e 's/\],/ /g' | sed -e 's/\;//g' | sed -e 's/\[//g' | sed -e 's/rule\=/ /g' | sed -e 's/\,/ /g' | sed -e 's/state\=/ /g' | sed -e 's/Ifn[c,s]in\=[0-9]*//g' | sed -e 's/Ifn[c,s]out\=[0-9]*//g' | egrep -v '^\s*$|^#'| awk '{split(\$2,a,".")'; printf "\t%s.%s.%s.0\n", a[1],a[2],a[3]}' 2>&1 | sort -n | uniq | sed -e 's/\.\.\.0//g' | sed -e 's/\.\.0\.0//g''
Hi Heiko, Just tried pasting in the script and got this:
Real time connection table analysis by Heiko Ankenbrand 2021 (v4.0)
/usr/bin/econn: line 308: syntax error near unexpected token `\$2,a,"."'
/usr/bin/econn: line 308: ` more /tmp/econn_ip.txt | awk '{print \$6 " "\$2 \$3 \$4 " "\$5 " "\$8}' | sed -e 's/src=//g' | sed -e 's/\],dest=\[/ /g' | sed -e 's/\],/ /g' | sed -e 's/\;//g' | sed -e 's/\[//g' | sed -e 's/rule\=/ /g' | sed -e 's/\,/ /g' | sed -e 's/state\=/ /g' | sed -
Hello @HeikoAnkenbrand,
Nice tool.
I sometimes get a grep bug in the ports section!
Hello @HeikoAnkenbrand,
Nice tool.
I sometimes get a grep bug in the ports section!
About CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
