- Products
- Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- Bulgaria
- Cyprus
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
Access Control and Threat Prevention Best Practices
5 November @ 5pm CET / 11am ET
Firewall Uptime, Reimagined
How AIOps Simplifies Operations and Prevents Outages
Overlap in Security Validation
Help us to understand your needs better
CheckMates Go:
Spark Management Portal and More!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Product Announcements
- :
- EA program for the new Mobile Access portal
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
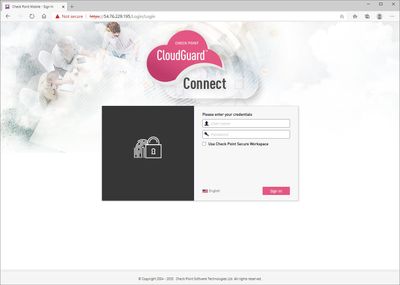
EA program for the new Mobile Access portal
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
2020-04-29
01:36 AM
The below has been released as part of R81.
If you wish to leverage the features of the new Mobile Access portal, you will need to upgrade to R81.
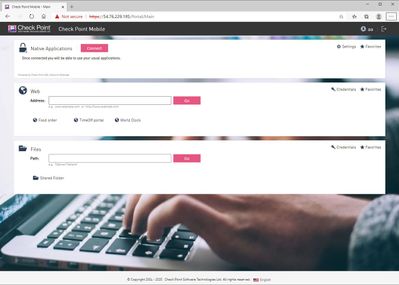
Key features of the new portal:
- Redesigned scan results
- Discontinued SNX connection pop-ups
- User friendly language selector
- Removed need for extra clicks during sign-out
- Added ability to launch all applications in separate tabs
- Settings / favorites are implemented as pop-up windows
- Non-configured items are not shown
- Full support of mainstream browsers on all major platforms
Portal customization
The new MAB portal has simplified customization capabilities. Since it has completely new page markup there is no need to follow the complicated instructions and change PHP files. Customer specifies its brand identity and we will provide a customization package tailored to its needs. Or the new style can be easily applied by the person with minimal knowledge in HTML and CSS.
We kindly invite you to try the new portal. It is available as early take of R81 or hotfix on top of R80.30 Jumbo take 196 and R80.40 Jumbo take 48 security gateways. Hotfixes can be installed on standalone gateways, clusters HA/LS and VSX.
Please contact me (@MaksimBahunou) or @AndreiR to get the latest hotfixes.
Enjoy and please provide your feedback to us.
32 Comments
About CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2025 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
About Us
UserCenter