An important aspect in R80.10 security management and gateways is the clean-up rule at the end of every layer.
Ordered and Inline layers in R80.10 always end with a clean-up rule. This makes sure that there is always a match.
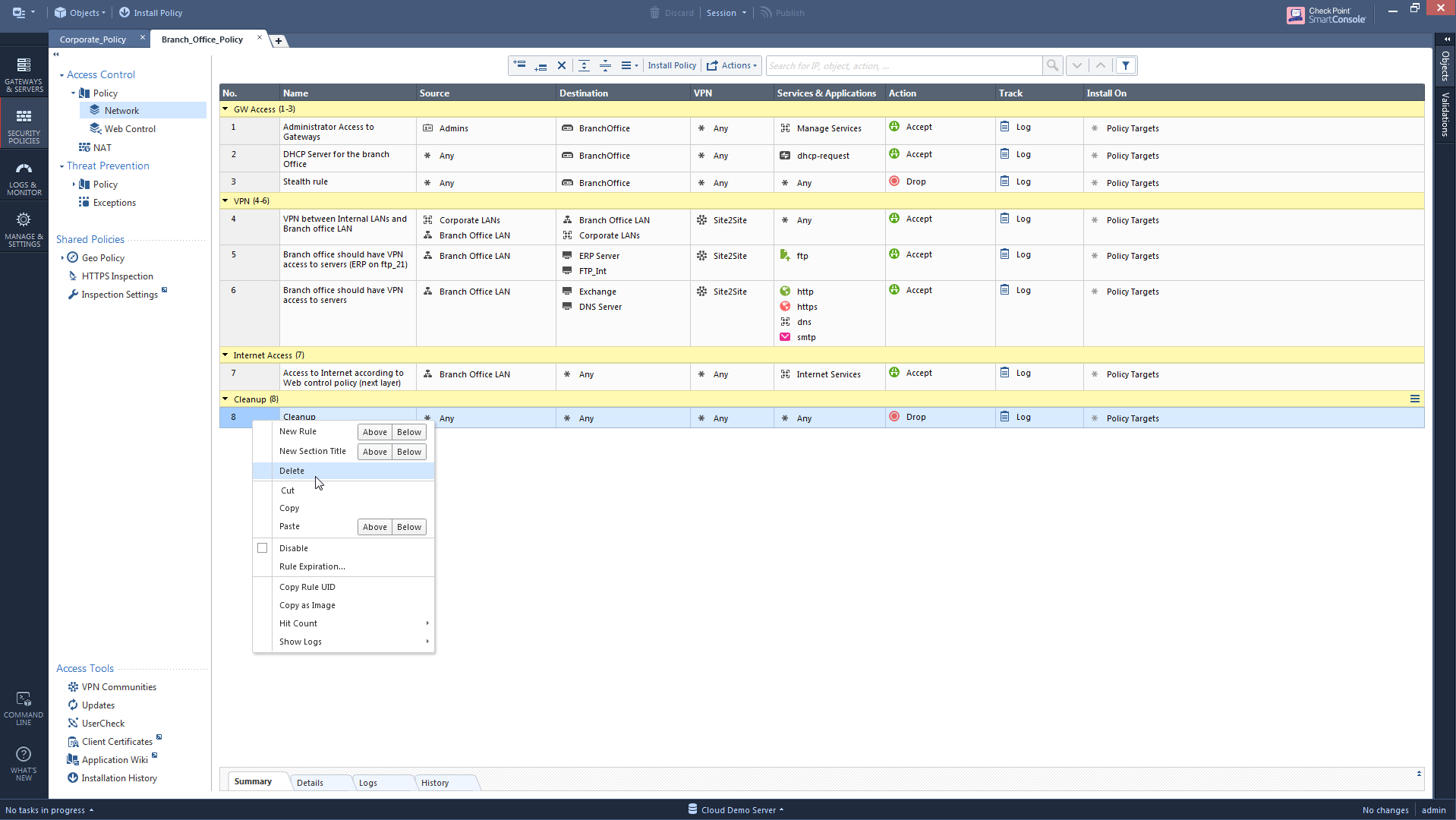
So even if a user tries to remove the last rule:
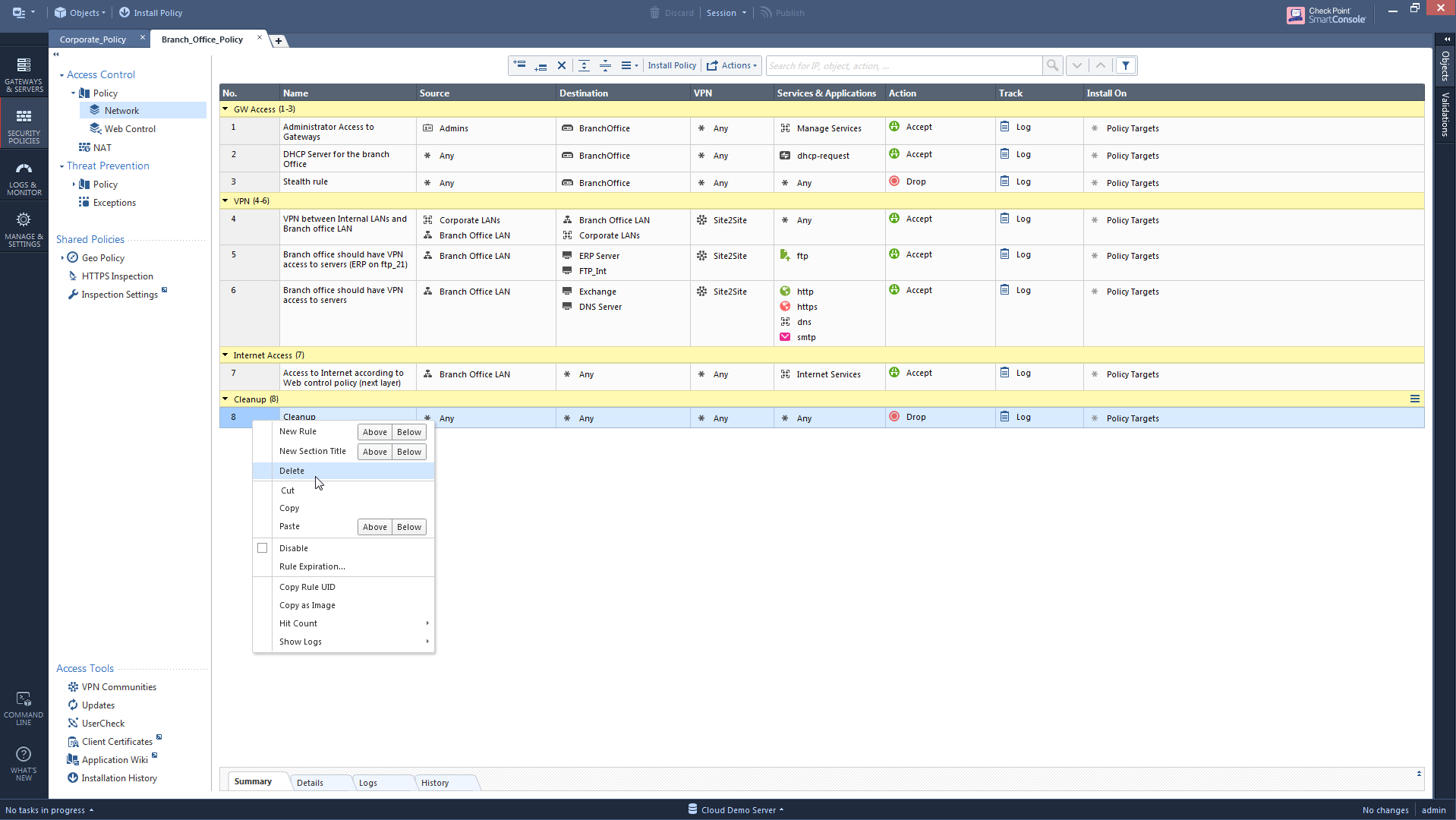
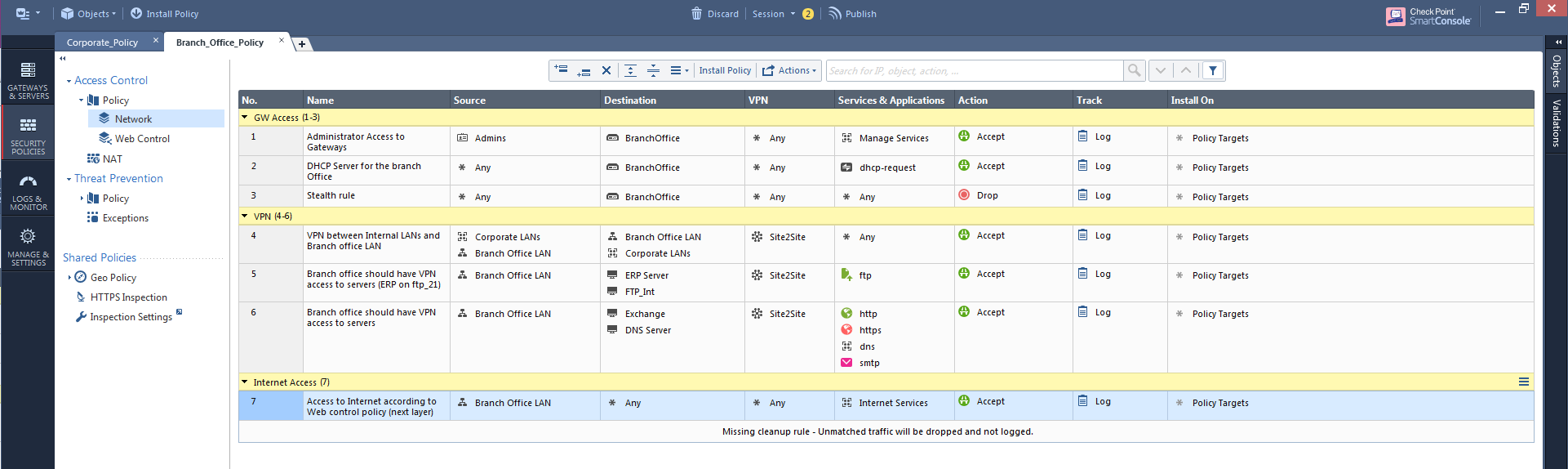
He will get this message that basically says there's an implicit cleanup rule on the gateway.
(you can actually follow-up on the best practice to keep an explicit cleanup rule by using the Compliance blade)
So what's new?
In our previous versions, the clean-up rule was a constant value:
- Any, any, drop at the end of the Firewall layer
- Any, any, accept at the end of the Applications layer
(either as an implicit rule or explicitly visible in SmartDashboard/SmartConsole)
With R80.10:
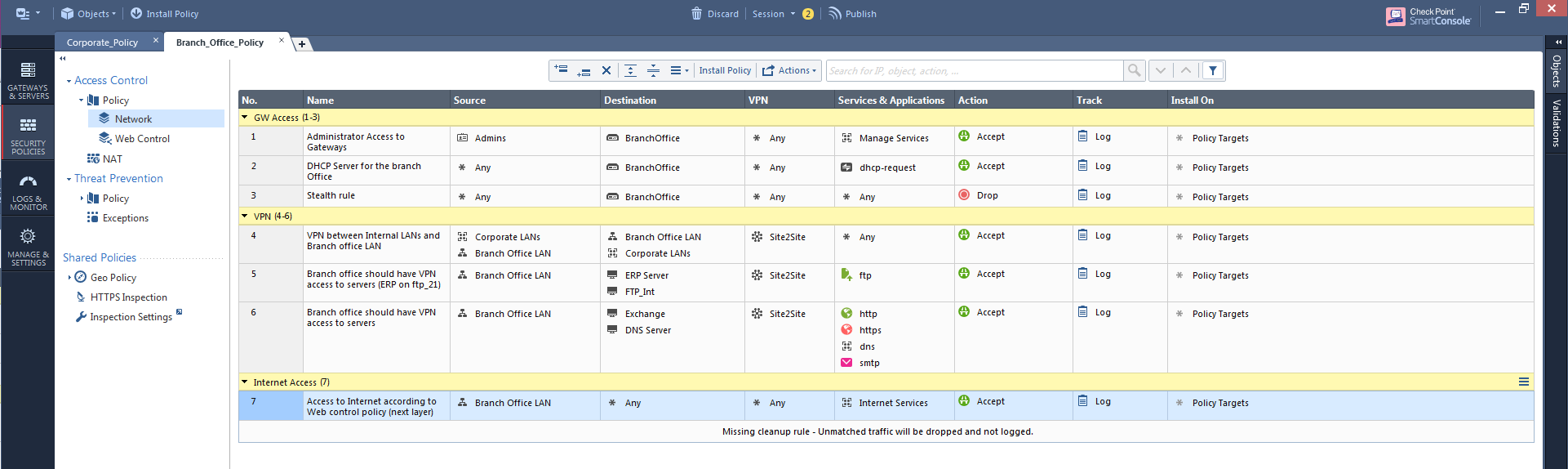
- You get better visualization of that behavior (as seen in the screenshot above)
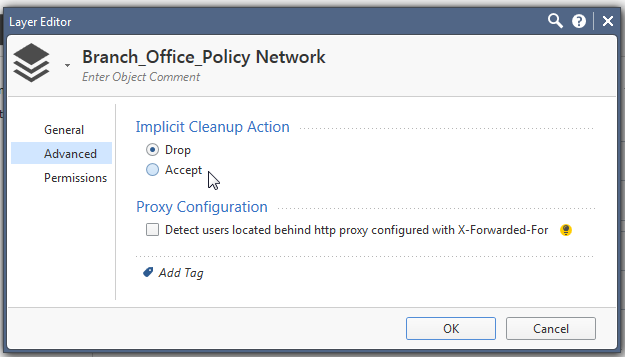
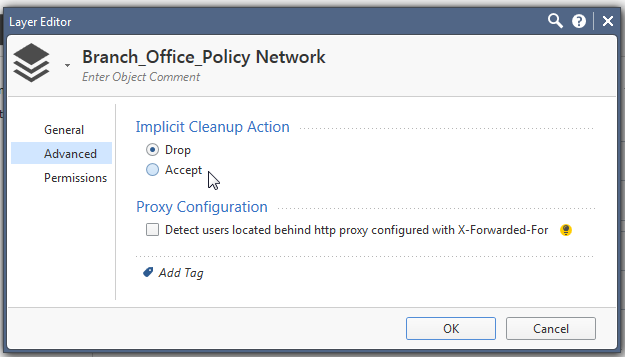
- You can configure the action: accept or drop.
You can control the action of that implicit cleanup rule by editing the layer. This will only matter if there's no explicitly defined cleanup rule at the end of the layer.
Let's see how this can look like in different usages of layers:
Inline Layers:
The fact that there is always a match in the inline layer, eliminates any impact of the inline layer's rules outside the inline layer.
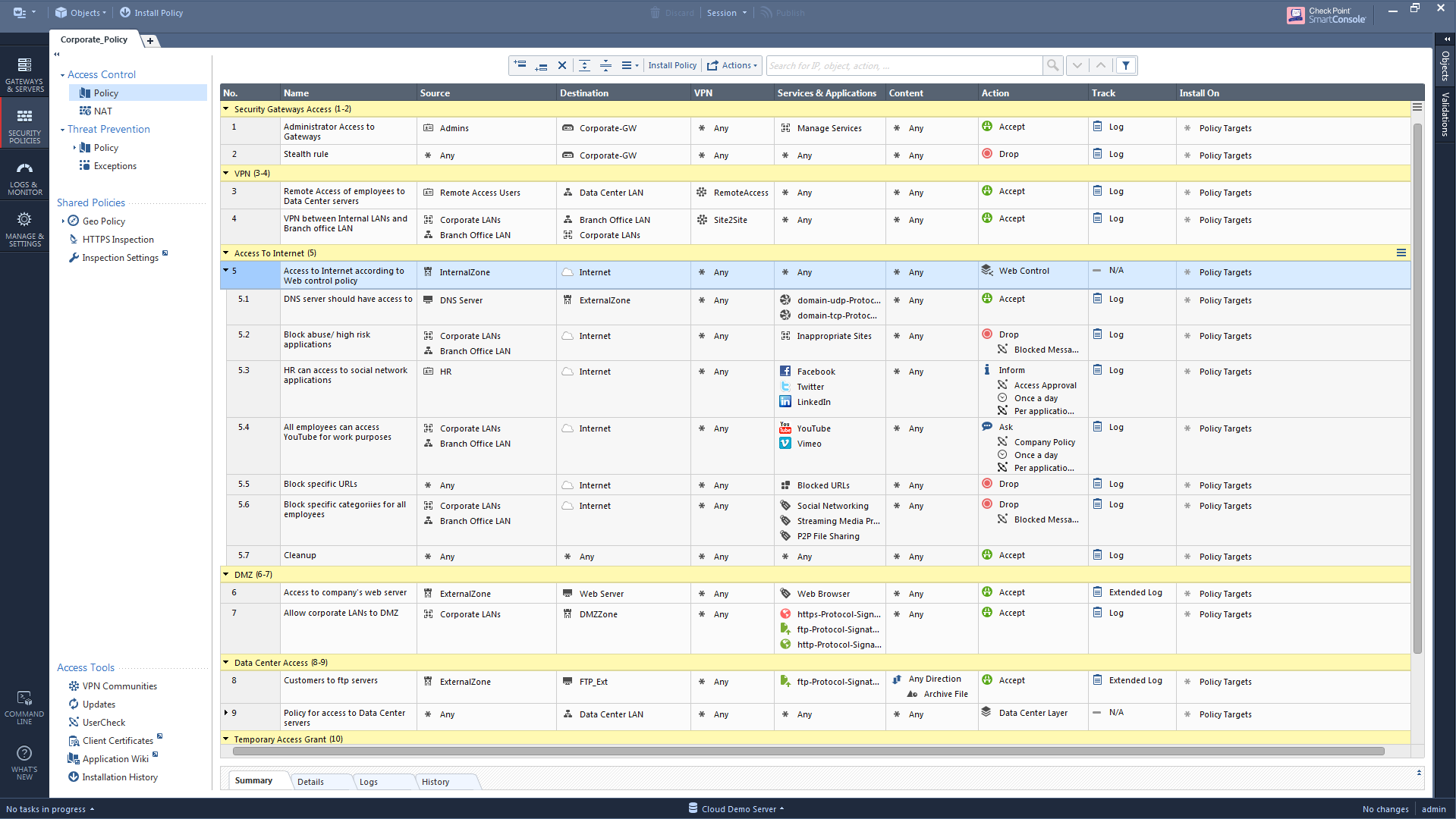
In this example, rule 5 has an inline layer.
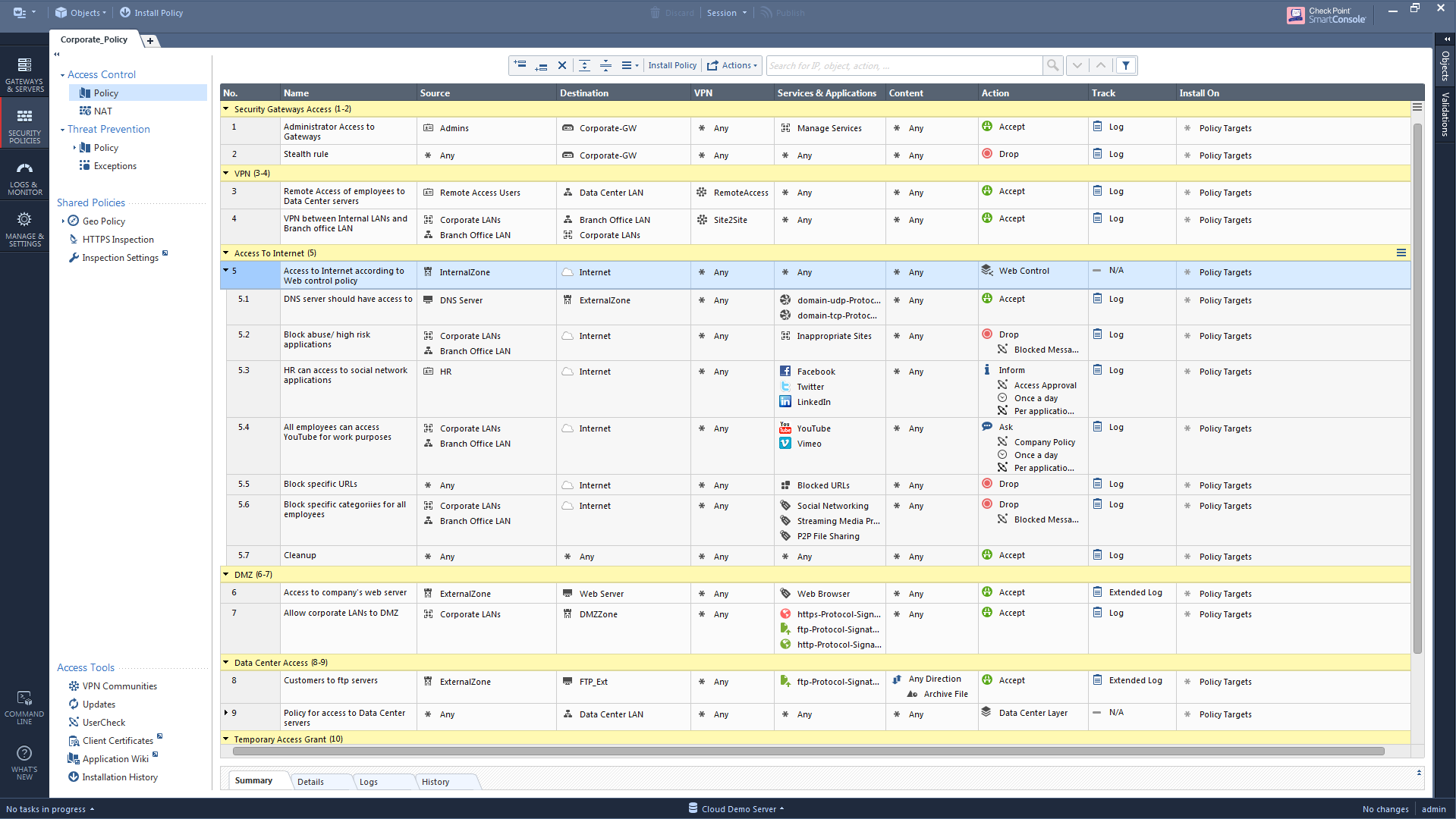
- When changing the inline layer's rules, we can't change the enforcement for rules 1-4, because they will always be matched before rules 5-12.
- When changing the inline layer's rules, we can't change the enforcement for rules 6-11, because matching on rule 5 always ends with matching any of the rules 5.1-5.7. There will always be a match, because the cleanup is always present.
Ordered Layers:
Some ordered layers can work in whitelist mode, while others can work in blacklist mode. For example, you can work with an ordered layer of "blocked unaccepted traffic" which accepts only on the last rule.
Or you can work with an ordered layer of "accepted specific web applications" which blocks the rest of the web applications.
Either way, it is OK to put an "any, any, accept" rule as the clean-up rule for an ordered layer while still ensuring unexpected traffic will be dropped, by providing an additional ordered layer with an "any, any" drop" rule.
Read more about using layers here: Layers in R80
Note: Multi-domain layers work differently here.
A local policy can have global rules and a "Domain layer" between them. When the gateway evaluates the rules in the local policy, if there was no match for the global rules at the top of the rulebase, it starts to evaluate the rules from the domain layer. If there was still no match for those rules, the global rules that were created below the domain layer are evaluated. So there is no cleanup rule before or after the domain layer.
Read more about Domain Layers here: https://community.checkpoint.com/thread/1102