- Products
- Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- Bulgaria
- Cyprus
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
The State of Ransomware Q1 2026
Key Trends and Their Impact
Good, Better, Best:
Prioritizing Defenses Against Credential Abuse
AI Security Masters E7:
How CPR Broke ChatGPT's Isolation and What It Means for You
Blueprint Architecture for Securing
The AI Factory & AI Data Center
Call For Papers
Your Expertise. Our Stage
CheckMates Go:
CheckMates Fest
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Who rated this post
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thats valid question and as the guys said, its all about split tunnel. So, to put it in layman's terms, it works like this:
FULL TUNNEL - works in a way where say users connect via remote access VPN, their Internet traffic will go through the firewall as well. Now, while this does protect the user, most companies prefer not to do this, as it puts more load on the firewall and they dont wish to need to put more resources to make sure Internet browsing from user side is in check with what company's policy
SPLIT TUNNEL - works in a way where users connect to access ONLY corporate resources and their Internet traffic goes via their own ISP home provider (always preferred method, regardless what vendor you use)
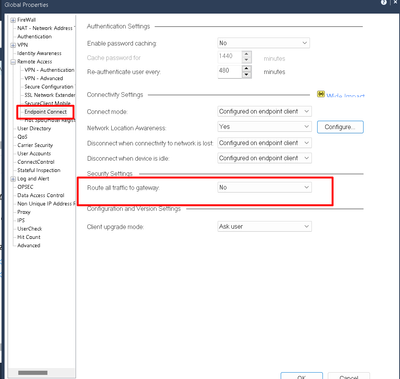
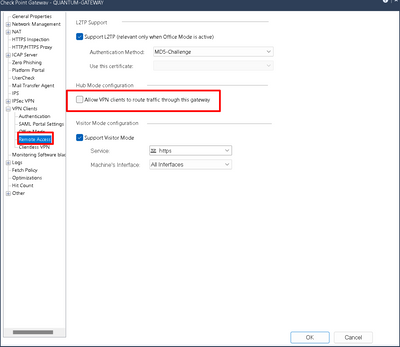
Now, as @_Val_ and @PhoneBoy mentioned, settings you need are below, I pointed them out and IF they are unchecked, it means it would be split tunnel.
If you select what I pasted, then it will do split tunnel and you wont have any issues. Let us know if you need more clarification.
Good reference article:
https://nordlayer.com/features/vpn-split-tunneling/
Cheers,
Andy
Best,
Andy
"Have a great day and if its not, change it"
Andy
"Have a great day and if its not, change it"
About CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2026 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
About Us
UserCenter