- Products
- Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- AI Security
- Developers & More
- Check Point Trivia
- CheckMates Toolbox
- General Topics
- Products Announcements
- Threat Prevention Blog
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- Bulgaria
- Cyprus
- APAC
What's New in R82.10?
10 December @ 5pm CET / 11am ET
Improve Your Security Posture with
Threat Prevention and Policy Insights
Overlap in Security Validation
Help us to understand your needs better
CheckMates Go:
Maestro Madness
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Network & SASE
- :
- Threat Prevention
- :
- Re: Threat Prevention Policy - Protected Scope - N...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Threat Prevention Policy - Protected Scope - Not working?
Hello All,
We have an issue with some traffic triggering an IPS Block for some traffic.
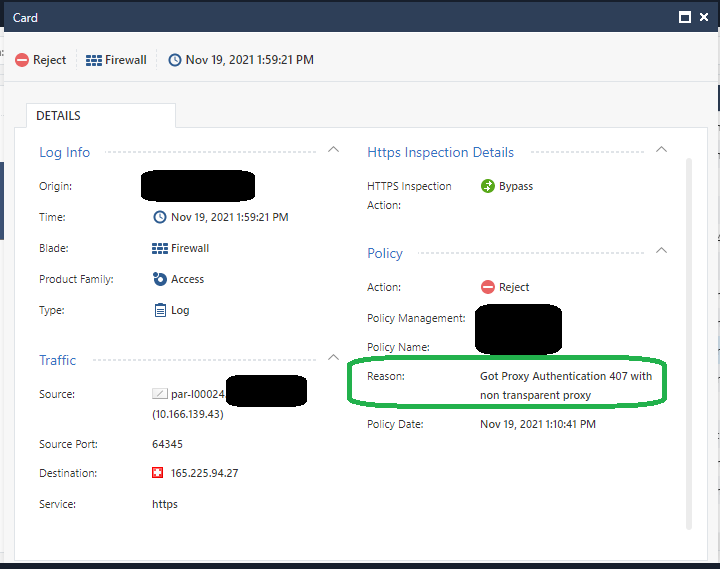
The FW Blade log:
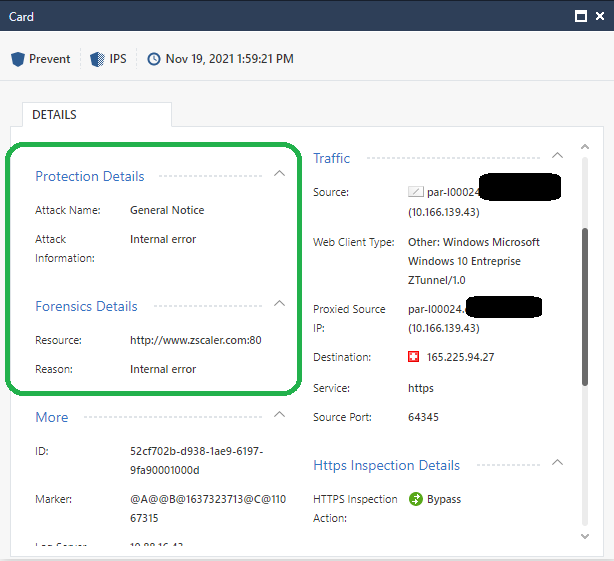
This is triggering a IPS Blade Log:
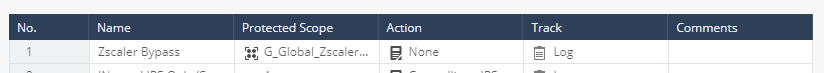
We tried to bypass the Zscaler traffic from the IPS. We do this generally as Zscaler should in theory already be doing security checks.
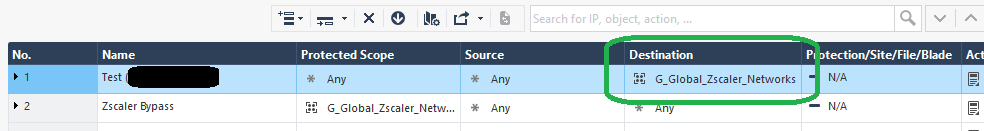
This did not have any effect. We were still getting the same log messages. As a test I implemented a Threat Protection rule which used "Destination" instead of "Protected Scope":
When we use this test rule, then the logs stop. Why understanding was (and other articles on the Community back this up) that "Protected Scope" is for matching "Source or Destination", but in this case it does not seem to work.
Is there any other difference between "Protected Scope" and using "Source" and "Destination", that we should be aware of that might explain this behaviour?
Many thanks,
Michael
11 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Protected scope refers to things behind the gateway, whether it is used as a source or destination.
Zscaler is clearly not in the protected scope in this case.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Phoneboy, with "things behind the gateway" you mean based on topology (defined in database), right?
So protected scope is only usable for things, which are reachable over an interface NOT defined as external from the affected gateway point of view, did I understand you right?
And when using source or destination field in TP policy instead of protected scope field, this limitation does not apply, right?
While this would be a good explanation for the effect Micheal showed us here, I'm really suprised it works this way.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Protected Scope contains objects that will be inspected when either connecting to or being connected from somewhere. This could contain Updateable Objects like O365 o.s.
CCSP - CCSE / CCTE / CTPS / CCME / CCSM Elite / SMB Specialist
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,
This would definitely explain the behavior. In the Threat Prevention Admin Guide I do not see this mentioned. The closest to a definition I can see is: "The list of network objects you want to protect." Is the protected Scope then only relevant to interface topologies that are marked as "internal"?
Many thanks,
Michael
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I find that this is explained very throughly in Threat Prevention R81.10 Administration Guide p.50ff Protected Scope ! Also see sk114806: ATRG: Threat Emulation (20) Performance considerations and Best practices and sk120933: How to configure the Protected Scope in Anti-Virus Settings for file downloads
CCSP - CCSE / CCTE / CTPS / CCME / CCSM Elite / SMB Specialist
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,
This definition is quite good, but does not explicitly clarify the comment as to whether the Protected Scope can cover objects that are external to the local security gateway. The comments you made about the use of updatable objects references which is part of the definition would indicate that the protects scope could include external resources, as it is highly unlikely that there are updateable objects for internal resources, unless is a customer created one. Everything I have seen referenced implies that external resources can be used as the protected scope. Hence my original question.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I read as follows:
Protected Scope objects can be
Network objects, such as Security Gateways, clusters, servers, networks, IP ranges, and so on. From R80.10, dynamic objects and domain objects are also supported in the Threat Prevention Policy.
Network object groups
Updatable objects (from R80.40)
IP address ranges
Roles
Zones
So naturally you can use external objects if needed, but in everyday life i would just include all internal networks to protect my clients and servers that will be inspected when either connecting to or being connected from somewhere. Also see the mentioned Performance considerations and Best practices !
CCSP - CCSE / CCTE / CTPS / CCME / CCSM Elite / SMB Specialist
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank, Günther, for the detailed explanation and I agree to that suggestion, but how does this explain the different behavior observed by Micheal when putting the network group object in Protected Scope field versus putting it in Destination field?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I would suggest to ask TAC about this different behavior !
CCSP - CCSE / CCTE / CTPS / CCME / CCSM Elite / SMB Specialist
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Similarly to Access Control, in the Threat Prevention policy the Protected Scope matching is performed pre-NAT. So for an outbound connection that is presumably Hide NATted, the original inside IP must be specified there for a proper match. For an inbound connection that is statically NATted, the outside Internet-routable IP address must be specified since that is the one present in the packet prior to any NAT operations. This applies equally regardless of whether source or destination (or both) are being NATted by the firewall.
Gaia 4.18 (R82) Immersion Tips, Tricks, & Best Practices Video Course
Now Available at https://shadowpeak.com/gaia4-18-immersion-course
Now Available at https://shadowpeak.com/gaia4-18-immersion-course
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Timothy,
Can You clarify:
"... For an inbound connection that is statically NATted, the outside Internet-routable IP address must be specified since that is the one present in the packet prior to any NAT operations. This applies equally regardless of whether source or destination (or both) are being NATted by the firewall."
If we have object with automatic static NAT do we have to create another object with public IP and use it in policy? Is it relevant for Protected Scope or Source or Destination in Threat Prevention?
Reagrds,
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 2 | |
| 1 | |
| 1 | |
| 1 | |
| 1 | |
| 1 |
Upcoming Events
Wed 03 Dec 2025 @ 10:00 AM (COT)
Última Sesión del Año – CheckMates LATAM: ERM & TEM con ExpertosThu 04 Dec 2025 @ 12:30 PM (SGT)
End-of-Year Event: Securing AI Transformation in a Hyperconnected World - APACThu 04 Dec 2025 @ 03:00 PM (CET)
End-of-Year Event: Securing AI Transformation in a Hyperconnected World - EMEAThu 04 Dec 2025 @ 02:00 PM (EST)
End-of-Year Event: Securing AI Transformation in a Hyperconnected World - AmericasWed 03 Dec 2025 @ 10:00 AM (COT)
Última Sesión del Año – CheckMates LATAM: ERM & TEM con ExpertosThu 04 Dec 2025 @ 12:30 PM (SGT)
End-of-Year Event: Securing AI Transformation in a Hyperconnected World - APACThu 04 Dec 2025 @ 03:00 PM (CET)
End-of-Year Event: Securing AI Transformation in a Hyperconnected World - EMEAThu 04 Dec 2025 @ 02:00 PM (EST)
End-of-Year Event: Securing AI Transformation in a Hyperconnected World - AmericasAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2025 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
About Us
UserCenter