- Products
- Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- Bulgaria
- Cyprus
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
Call For Papers
Your Expertise, Our Stage
Ink Dragon: A Major Nation-State Campaign
March 11th @ 5pm CET / 12pm EDT
AI Security Masters E4:
Introducing Cyata - Securing the Agenic AI Era
The Great Exposure Reset
AI Security Masters E3:
AI-Generated Malware
CheckMates Go:
CheckMates Fest
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Hybrid Mesh
- :
- Firewall and Security Management
- :
- VPN authentication question
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
VPN authentication question
Hey guys,
I really hope someone can shed light on this, as I sadly never gotten confirmation via case we had with TAC. So, apologies in advance if this sounds like a stupid inquiry, but here it goes...
Say you have company of 200 people and 20 people are IT and they require using MFA. Now, when I worked with TAC for another customer, we had a case for about 20 days and final suggestion was to have people who need to use Radius set up individual local VPN users and then set them up as Radius auth in user properties. Ok, great, that does work, as it was easy to do and they all get mfa prompts on their phones and all is dandy, but what would happen if there is a company of say 2000 employees and 400 of them have to use Radius mfa...who would have time to create 400 individual users via smart dashboard. Its not really a scalable solution in my view...
Now, if I look at ldap group object, you cant assign auth method there, so my question is this...is there ANY way possible to give certain auth method to a group that contains say 20 users from AD? From all I looked at and what TAC checked, we never found a way.
I even reviewed carefully the document attached, but sadly, did not help. The reason why I posted this in the first place is because there is another customer who wants to use Radius soon, but they want to do it gradually...they dont want to move everyone at once. Also, even from vpn_auth screenshot I attached, I dont see option there either to assign specific users to desired auth method. Yes, there is option for common lookup type, but that does absolutely nothing.
If anyone had any suggestions, I would so greatly appreciate it.
Thanks as always!
Best,
Andy
Andy
12 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I've not tested your scenario recently but I get where you're coming from.
SAML is the future... but saying that one option might be to have the Radius server itself impose such logic I would think.
The challenge there comes with how the MFA prompt is displayed or details parsed via a common field.
CCSM R77/R80/ELITE
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yea, thats the issue...I cant tell the customer to create say 100 local vpn users just for this purpose, its not really optimal.
Best,
Andy
Andy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What I can imagine is that all IT admins will need to be part of specific LDAP group which will then be used as Huntgroup on Radius server to authenticate towards specific IPs.
Kind regards,
Jozko Mrkvicka
Jozko Mrkvicka
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We even had TAC review this last time I worked with customer and we did that exact scenario, but it did not help, we simply had to end up creating local VPN users to fix the problem, which in my view, is not a good solution at all. Yes, it works, but too much manual work.
Best,
Andy
Andy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Doesn't the user select which option to authenticate with?
If am not mistaken, isn't it like a drop down menu on the client with say "general staff login" and "IT MFA login" ?
You'd like to automatize that user process lets say?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Juan_ ...I will explain again, its literally same example I gave in description. Say, for arguments sake, you have company with 5000 employees and CEO requires 10% of them to use MFA (so 500 people). Well, there is no option anywhere within dashboard at all to indicate if you create LDAP group to represent those 500 people to have them authenticate with say Radius, so they can get prompt for mfa on their phones or whatever mfa app they use. It really defeats the purpose if you have to create 500 local vpn users in dashboard and give them same usernames that would represent their AD credentials and then indicate radius auth.
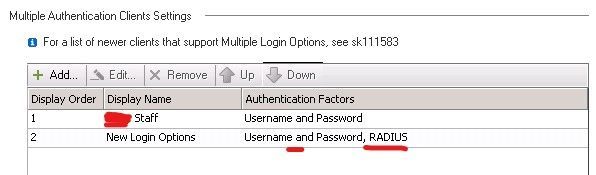
So, if you look at vpn_auth screenshot I attached, yes, you can define multiple auth methods on gateway itself, BUT, issue is, once you edit specific auth method, it does NOT let you select specific group in there for that auth type, just whole account unit.
Makes sense?
Best,
Andy
Andy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I (think) I know what you mean, the gateway itself can't decide what's the designated login option based on group, for example.
It could decide based on username if you created the user indvidually as you explained
But:
- Wouldn't that be a function best served by the radius as Jozko suggested?
- If you create a new login option with "AD + Radius" and deploy a custom client for IT stuff to use that option, wouldn't that work as well?
I understand this second option is probably not as good as what you are asking but..
Sorry if im not fully understanding 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Right, I would have thought something like this was gonna do the trick:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
O that, right...Im pretty sure we tried that too and it did not do anything. See, the whole problem really, at least in my view it, that you can NOT sadly indicate right auth method for ldap group you create in dashboard that represents group of users in AD. If that was possible, I think that would make this so much easier.
Best,
Andy
Andy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What in case you will create dedicated Domain with the Account Unit dedicated only for IT admins using MFA which will ONLY be used for ONLY one gateway inside that new domain ? The best would be to use VS, to save some money. You will need one new domain, and one gateway (or cluster).
Kind regards,
Jozko Mrkvicka
Jozko Mrkvicka
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Here is an official TAC response on it:
After consulting with escalations, assigning specific users to desired authentication method in Check Point Multiple Login Options is not a supported feature yet, and there is already an existing RFE submitted for that. However, you can configure only RADIUS authentication, and have the RADIUS server determine who gets MFA or who does not, meaning configure the MFA on the RADIUS server/Using DUO or some other MFA services on the account itself instead of having the gateway to do the MFA.
Best,
Andy
Andy
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 40 | |
| 24 | |
| 14 | |
| 11 | |
| 8 | |
| 8 | |
| 7 | |
| 7 | |
| 6 | |
| 6 |
Upcoming Events
Tue 03 Mar 2026 @ 04:00 PM (CET)
Maestro Masters EMEA: Introduction to Maestro Hyperscale FirewallsTue 03 Mar 2026 @ 03:00 PM (EST)
Maestro Masters Americas: Introduction to Maestro Hyperscale FirewallsTue 03 Mar 2026 @ 04:00 PM (CET)
Maestro Masters EMEA: Introduction to Maestro Hyperscale FirewallsTue 03 Mar 2026 @ 03:00 PM (EST)
Maestro Masters Americas: Introduction to Maestro Hyperscale FirewallsFri 06 Mar 2026 @ 08:00 AM (COT)
Check Point R82 Hands‑On Bootcamp – Comunidad DOJO PanamáAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2026 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
About Us
UserCenter