- Products
- Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- AI Security
- Developers & More
- Check Point Trivia
- CheckMates Toolbox
- General Topics
- Products Announcements
- Threat Prevention Blog
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- Bulgaria
- Cyprus
- APAC
MVP 2026: Submissions
Are Now Open!
What's New in R82.10?
Watch NowOverlap in Security Validation
Help us to understand your needs better
CheckMates Go:
Maestro Madness
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Network & SASE
- :
- Security Gateways
- :
- Re: Route Base VPN with Cisco
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jump to solution
Route Base VPN with Cisco
Hello everyone,
please tell me if i'm on the right way. I saw some videos and tutorials, but they all are for a clustered connection.
On our side with have CP R80.40, remote side has a Cisco Router. They want Route Based VPN. What I will do:
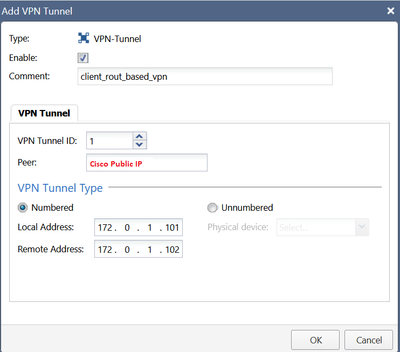
1. create VTI in GAIA:
2. create Interoperable Device with Cisco Public IP
3. Create VPN-Community with empty encryption Domain (a VPN-community likewise for policy/domain Based VPN)
4. add static Route: remote network behind VTI
5. something else?
Thank you in advance!
1 Solution
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Unfortunately we didn't manage to make work GRE over IPsec on the CP R80.40. We have temporarily installed another server until we upgrade CP to R81
15 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MAKE SURE remote address is one used as default gateway for static route to remote site.
Check out this post
Andy
Its cluster, but you get an idea, if you need help, we can do remote after hours
Best,
Andy
Andy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,
The "peer" parameter is NOT the public ip address of the peer. It is the name of the object you created on smartconsole for cisco device. So you should switch steps 1 and 2. Also the static routes should use as next hope the vti interface and not ip address as next hop. I have had some issues using IP address instead of interface.
One missing step (should be number 3 on your example) is get interfaces on your R80.40 gateway object on smartconsole, it is not possible to create a VTI interface manully, it must be fetched by a get interfaces, i would use get interfaces without topology option.
And of course you must have rules that allow the traffic. I think that is all.
Regards
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, very true about the peer, totally missed that part, it is indeed a NAME of interoperable object.
Andy
Best,
Andy
Andy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for suggestions. One more question: get Interface - with or without Topology?
If I choose with - it changes all interfaces... I'm getting more 100 changes in total.
If I choose without - it also changes all interfaces, I'm getting ~26 changes (because I have ~26 interfaces) even I don't see any in the SmartConsole. To be honest, I have no desire to change any productive interfaces... What to do?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I never do with topology, always without...if you do with topology option, it will reset everything to default.
Andy
Best,
Andy
Andy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,
I would use get interfaces without topology. I understand what you say, it happens to me every time i create a new route based vpn. I am not sure why those changes appear, but it always happened every time i created a new vti, and the configuration never changed, so you could safely publish. If you want to be sure, you can check your previous configuration with Policy Installation History feature, it will open a new smartconsole in read only mode with the policy you had before doing the fetch, and you will be able to compare the interfaces configuration.
Regards
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,
Is this a GRE tunnel? XD that would have been a good piece of information at the beginning jaja. GRE is supported starting in R81. From sk92845:
Generic Routing Encapsulation (GRE) Tunnels are not supported on Gaia OS running versions lower than R81.
Starting from R81, GRE Tunnels are supported.
Note: This is relevant to CloudGuard, as well as in physical appliances.
For R81 or newer versions:
https://support.checkpoint.com/results/sk/sk169794
Regards
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
hi RS_Daniel,
yes, I've just got new info this is GRE over IPsec.
Offtopic - do we always need GRE-Interface for GRE-Tunnel?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I found an article that CP supported GRE over IPsec even in 2011. I undersand, that it is different CP, but still... Can we configure GRE over IPsec?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Im prrtty sure its still supported, as per below.
Andy
https://support.checkpoint.com/results/sk/sk169794
Best,
Andy
Andy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello the_rock,
I'm sorry, but your link is about GRE Tunnel, which is not supported in R80.... It was already sent by RS_Daniel
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Right, but Im fairly sure its still supported.
Andy
Best,
Andy
Andy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Unfortunately we didn't manage to make work GRE over IPsec on the CP R80.40. We have temporarily installed another server until we upgrade CP to R81
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Faitr enough. You may as well go with R81.20, as its recommended and super stable.
Andy
Best,
Andy
Andy
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 19 | |
| 17 | |
| 14 | |
| 8 | |
| 7 | |
| 3 | |
| 3 | |
| 3 | |
| 3 | |
| 2 |
Upcoming Events
Tue 16 Dec 2025 @ 05:00 PM (CET)
Under the Hood: CloudGuard Network Security for Oracle Cloud - Config and Autoscaling!Thu 18 Dec 2025 @ 10:00 AM (CET)
Cloud Architect Series - Building a Hybrid Mesh Security Strategy across cloudsTue 16 Dec 2025 @ 05:00 PM (CET)
Under the Hood: CloudGuard Network Security for Oracle Cloud - Config and Autoscaling!Thu 18 Dec 2025 @ 10:00 AM (CET)
Cloud Architect Series - Building a Hybrid Mesh Security Strategy across cloudsAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2025 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
About Us
UserCenter