- Products
- Learn
- Local User Groups
- Partners
- More
Step Into the Future of
AI-Powered Cyber Security
When the Agents Attack
A Live Look at Agentic Exposure Validation
Bridge the CAASM Gap
with Exposure Management
AI Security Masters E8:
Claude Mythos: New Era in Cyber Security
CheckMates Go:
CheckMates Fest
🎓 Simulates common hping use cases
🤠 Utilizes using bash + /dev/tcp + nping + nc
👉 Requires R82.10+
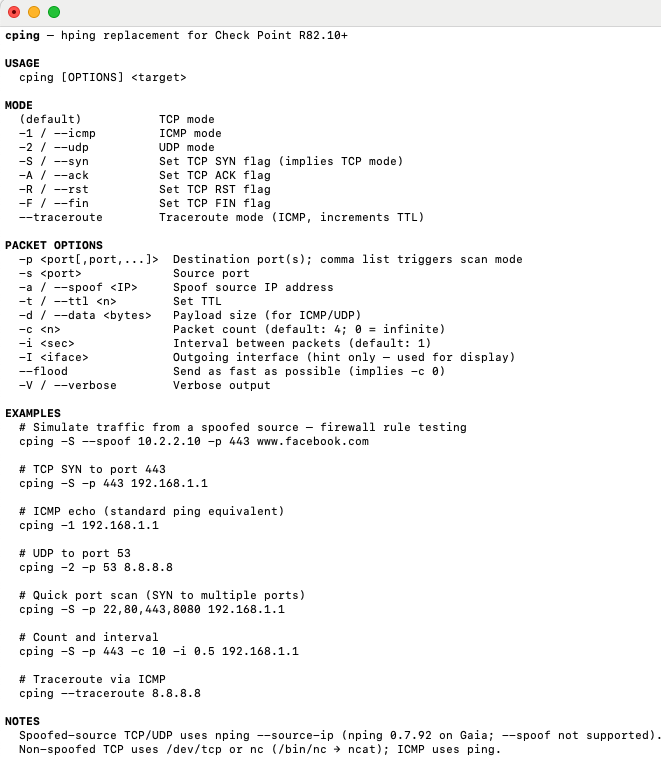
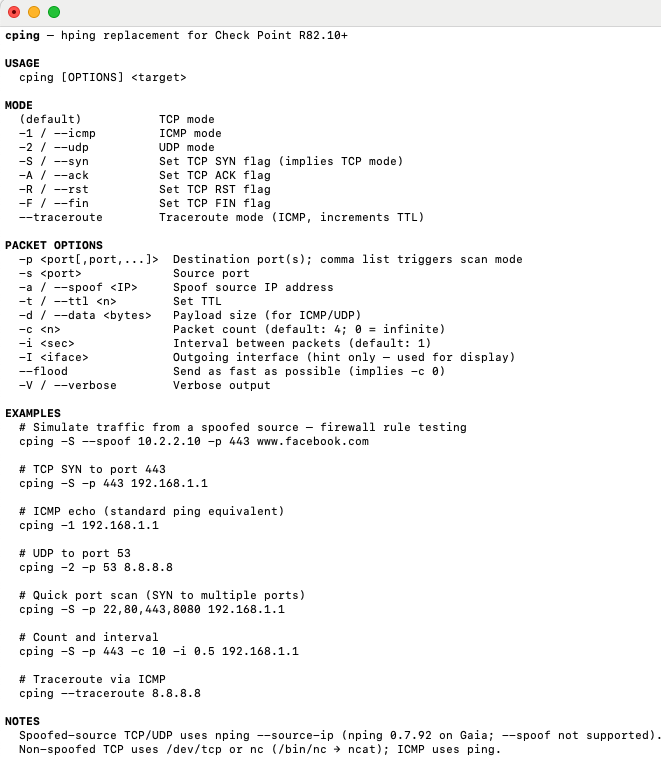
cping - hping replacement for Check Point R82.10+
curl_cli $(awk '/proxy:ip/{p=$2}/proxy:port/{print "--proxy "p":"$2}' /config/active) --cacert $CPDIR/conf/ca-bundle.crt https://dannyjung.de/cping|zcat>/usr/bin/cping&&chmod +x /usr/bin/cping
🎓 Simulates common hping use cases
🤠 Utilizes using bash + /dev/tcp + nping + nc
👉 Requires R82.10+
cping - hping replacement for Check Point R82.10+
curl_cli $(awk '/proxy:ip/{p=$2}/proxy:port/{print "--proxy "p":"$2}' /config/active) --cacert $CPDIR/conf/ca-bundle.crt https://dannyjung.de/cping|zcat>/usr/bin/cping&&chmod +x /usr/bin/cping
About CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
