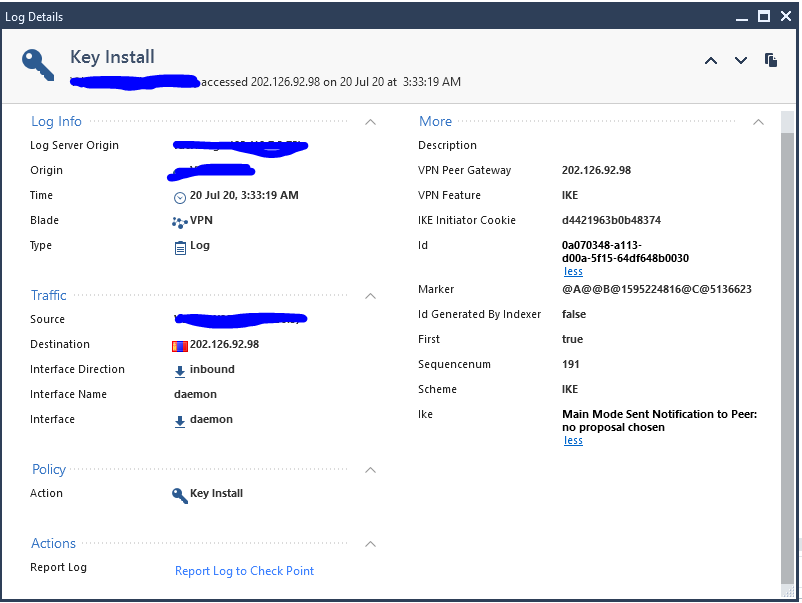
This has been brought up before at CheckMates, basically all UDP 500 traffic is allowed by the firewall and sent to the process vpnd on the gateway which is where all IKE negotiations occur. You'll see random Internet IPs trying to start IKE negotiations with a "Key Install" log but they won't get anywhere since they are not a defined peer.
IKEv1 Phase 1 does things in kind of a messed up order of operations by design which is not Check Point's fault. IKEv1 Phase 1 performs the following three tasks in this order:
- Agree on algorithms to form an SA
- Compute a secret key with Diffie-Hellman
- Authenticate the negotiating peers
The fact that lots of negotiation and a computationally expensive Diffie-Hellman calculation is performed before the peers even authenticate each other should raise alarm bells. Because the peer has not been authenticated yet, it always possible they are hostile and trying to crash us with malformed or otherwise corrupt negotiations. For that reason all IKE is handled in the vpnd process instead of the INSPECT/Firewall Worker which traditionally runs in the kernel. If the vpnd process happens to crash, its parent process fwd simply respawns it immediately, no harm no foul. However if IKE negotiations took place inside the kernel, a crash caused by the peer in there would cause the whole system to crash. With the advent of USFW, it will be interesting to see if functions like this that are done for stability reasons in separate processes will end up getting integrated into the INSPECT/fwk/Firewall Worker when USFW is enabled.
IKEv2 resolves this design issue by authenticating the peers first before allowing any other operations.
Gaia 4.18 (R82) Immersion Tips, Tricks, & Best Practices Video Course
Now Available at https://shadowpeak.com/gaia4-18-immersion-course