Hi mcatanzaro,
This is what worked for me:
- Configure the active gateway to be a CA
- Sign the CSR
- Deploy signed certificate to end host
- Export signed certificate in .p12 format
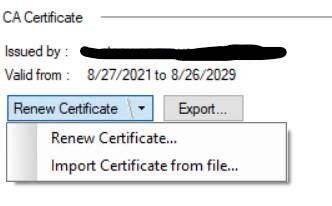
Import .p12 certificate in SmartDashboard -> HTTPS Inspection -> CA Certificate
More detailed:
# Create CA directories and files. With Trail and Error and looking at the openssl.cnf file, these are the directories/files needed
mkdir ca_certificate
cd ca_certificate
mkdir demoCA
cd demoCA
mkdir {certs,crl,newcerts,private,crl,conf}
touch {index.txt,serial}
# Serial numbers are in hex and here we are starting with 1
echo "01" > serial
# Create private key for CA
cpopenssl genrsa -aes256 -out private/cakey.pem 4096
# Copy CheckPoint openssl configuration file to local configuration directory
cp $CPDIR/conf/openssl.cnf conf/
# Modify openssl.cnf
- In the [ req_distinguished_name ] section, change the default values to your appropriate environment
- In the [ usr_cert ] section, change the value for basicConstraint from FALSE to TRUE
# Create a certificate for this local CA
cpopenssl req -new -x509 -days 3650 -key private/cakey.pem -out cacert.pem -config config/openssl.cnf
# Generate a CSR on active gateway
cpopenssl req -new -newkey rsa:4096 -sha256 -out gw.csr -keyout gw.key -config <user generated config file including CN name and other data>
# Sign the CSR
cpopenssl ca -startdate 210910000000Z -enddate 290909000000Z -in gw.csr -out gw.crt -config conf/openssl.cnf
# Deploy certificate to end host
# Export the signed certificate in .p12 format
cpopenssl pkcs12 -export -out gw.p12 -in gw.crt -inkey gw.key
# Import the .p12 certificate from the SmartDashboard -> HTTPS Inspection -> CA certificate
# Push the policy
I submitted the above steps to the TAC. I probably won't here back until Monday, but it seems to work so far. Still testing...