- CheckMates
- :
- Products
- :
- CloudMates Products
- :
- Cloud Network Security
- :
- Discussion
- :
- IPsec Redundancy to the Same Endpoint
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Are you a member of CheckMates?
×- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
IPsec Redundancy to the Same Endpoint
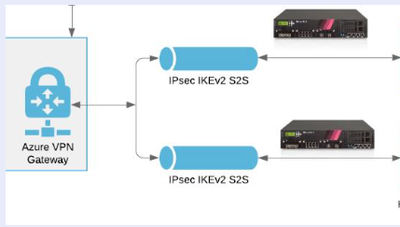
The following shows what we need to establish: The Azure VPN gateway is on the UK South domain.
What has been identified is that traffic loss is seen when the specific link to Azure domain is in maintenance, traffic is lost fro approx 20 mins.
What the requirement is that the secon IPSec is established as a standby.
It is assumed that multiple access links for the Azure are available and that may be set up as the standby (cold)
The two CP gateways are a HA pair.
Currently the BGP is showing only as being available and active from the Active :
169.254.22.69 65xxx 17 16 Established 1 21 4d7h
We know that in HA redundancy that the BGP re-forms on the HA partner when there is a failure.
When we need to do is enable the platform to have two possible IPsec to the remote Azure VPN gateway , having the same Target remote AS number.
So in essence a Primary and a secondary : now not having experimented and not having any lab facility the behaviour and the configuration is unknown, this is where I post this article/ info request.
Also in the event of the switch between Active Ip sec and the Secondary Ipsec ( when the AZ provider does the maintenance ) one would assume that the traffic will be interrupted due to the re-formation of the BGP on the secondary IPsec.
There is no requirement for any load sharing : One Ipsec is up or the other.
Expressing here the design requirements that have been presented for any valid input or design ideas or even sample configurations that may have been developed or deployed in the past.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Where are you intending to initiate the second tunnel from?
The same active device or the other (standby) device?
Note in an HA configuration, only one of the gateways should initiate an IPsec tunnel.