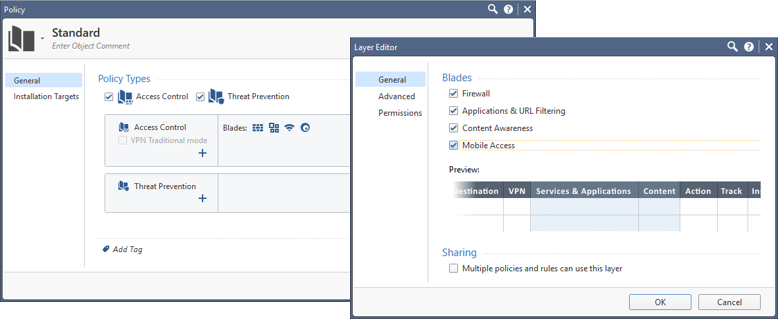
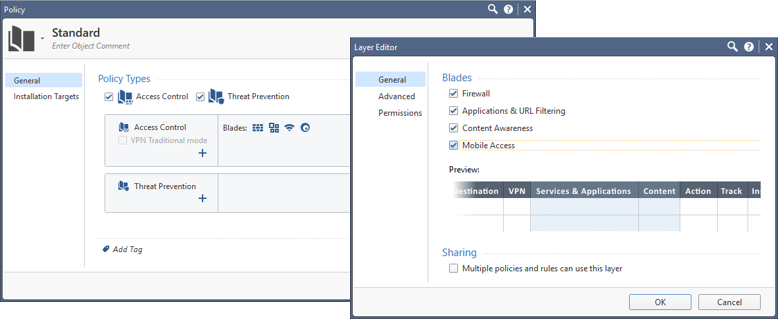
In R77 access control is applied in an ordered fashion, for instance firewall rules are checked before application control rules. There was duplication in the firewall and application object definitions and in the policies. In R80.10 this is simplified by defining which security features you want the policy layer to inspect in the unified policy. Service objects, application objects and logging are all in sync with the policy definition.
Service Objects and Protocol Signatures
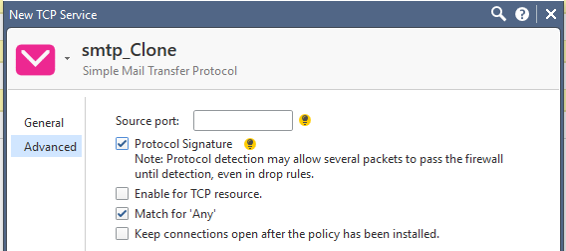
In R77 with separate policies for firewall and Application Control & URL Filtering there are Services Objects for the firewall policy and Network Service applications for the Application Control policy. In R80.10 this duplication is eliminated and the number of protocol handlers available in the advanced settings for the firewall service objects is reduced from over 200 to less than 20. In its place the default is to match by port in the service object and as an option to clone the service object and enable match by protocol signature. This enhances policy matching and changes the number of packets needed to define the session depending upon whether firewall does a port-based match or application control does the match. When application control does the match more packets are needed to make a decision about the session.
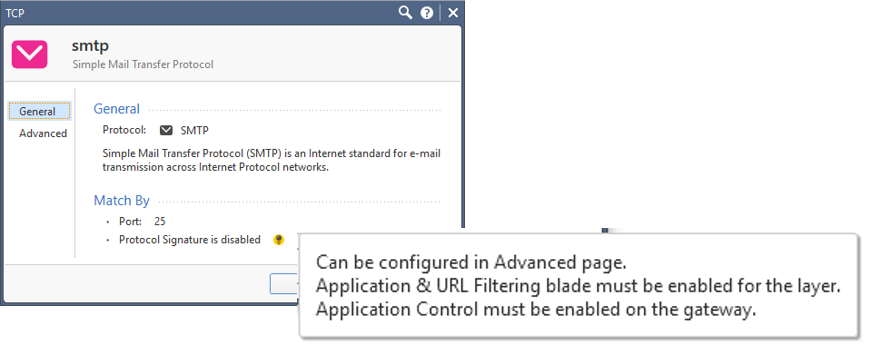
Consider the default R80.10 SMTP service object (shown below) which matches TCP connections where the destination port is 25. When using this object in a policy, there is no need to do transaction level analysis to identify the connection as SMTP protocol traffic. The SYN packets in the three-way TCP handshake can simply be dropped or accepted if the destination port is 25. Once the match is made the SMTP protocol handler continues to inspect the session for security issues.
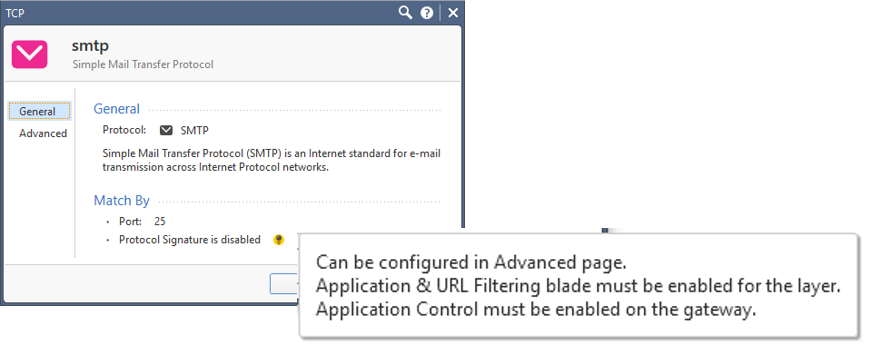
When the SMTP service object is cloned (shown below) and protocol signature is enabled, Application Control must be enabled on the gateway and in the policy layer. As noted earlier and in the UI, protocol detection may allow several packets to pass to accurately identify the protocol.
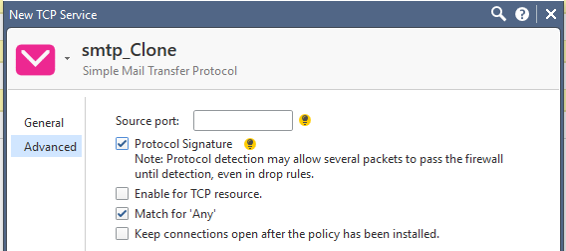
Consider an example SMTP session and some example C2S requests and S2C responses. A few packets will be needed to correctly identify the protocol.

R80.10 Applications and Recommended Services
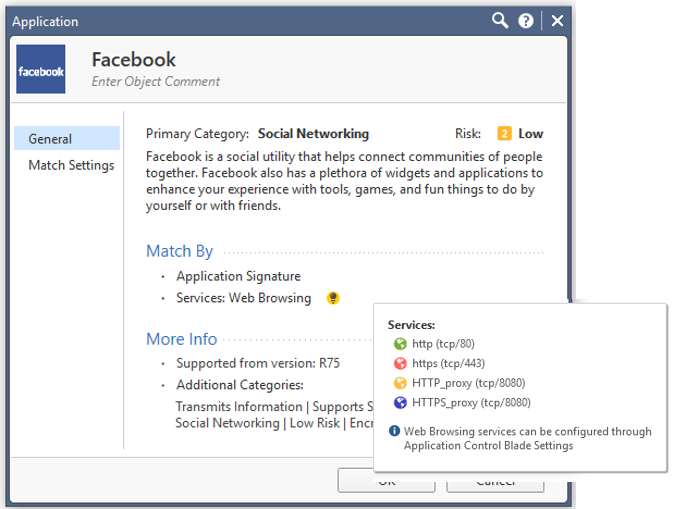
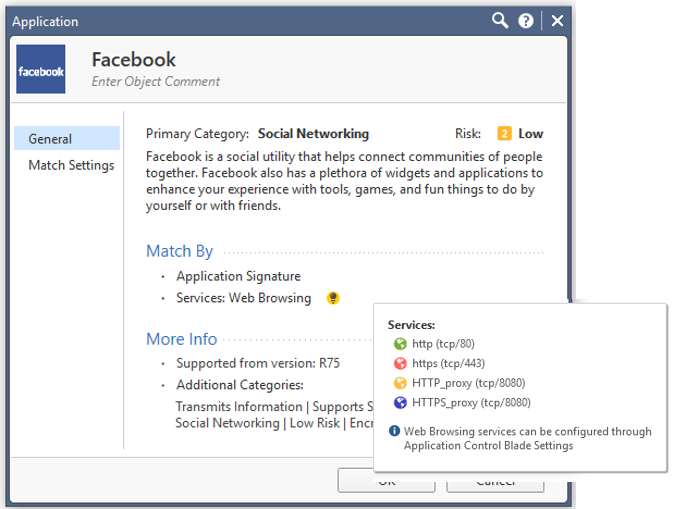
We have seen how R80.10 Service objects and application signatures are combined. Likewise, R80.10 applications now include recommended services such as HTTP and HTTPS in the application definition simplifying the unified policy configuration. For instance the R80.10 Facebook application definition (shown below) includes the Web services where it is common to see Facebook traffic; HTTP/S over port 80/443 and HTTP/S proxy connections over port 8080. In the UI you can see the services included in the application definition.
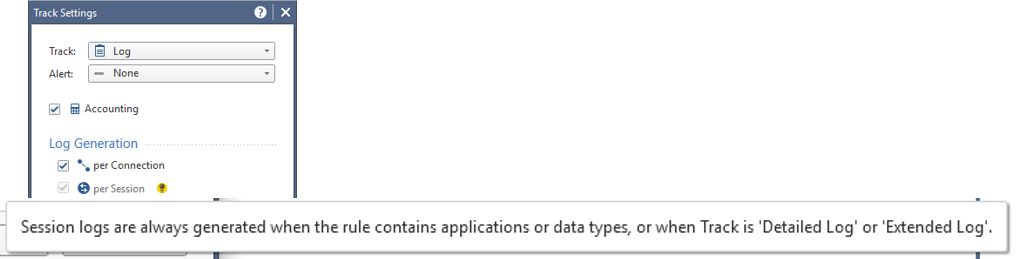
Log Options Match Policy Definition
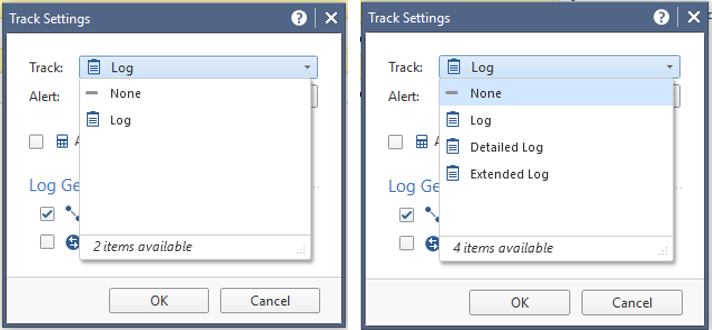
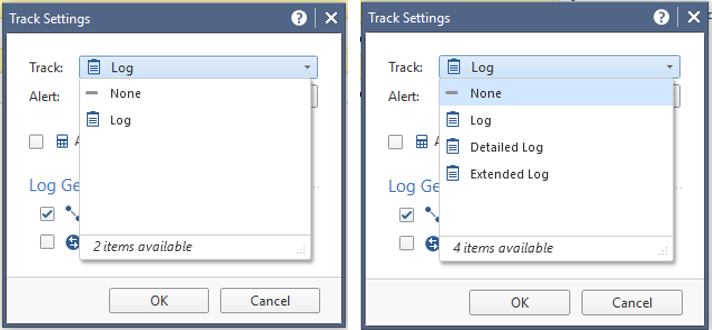
Logging options match the policy. When only firewall is enabled on the policy the default Track option is Log. At a minimum, this is the Source, Destination, Source Port, and Destination Port (see the left graphic below). When Application Control or Content Awareness is enabled then the Detailed or Extended logging options are available (see the right graphic below). The Detailed option logs the application and the Extended option logs the full list of URLs and Files.
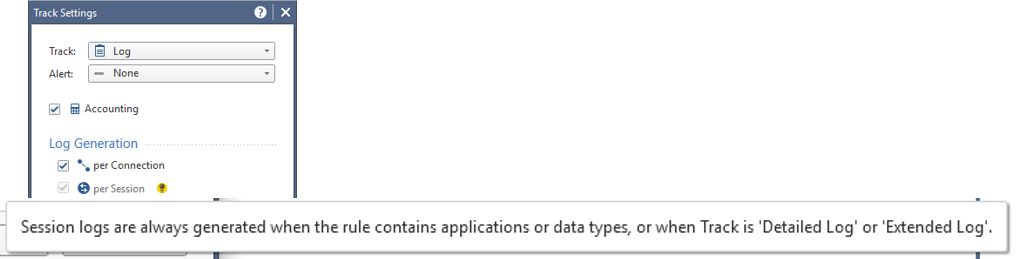
When an application object is added to the rule, then by default session logging is also enabled. A session is a user's activity at a specified site or with a specified application. The session starts when a user connects to an application or to a site. The Security Gateway includes all the activity that the user does in the session in one session log. Select this to generate one log for all the connections in the same session. This is the default for rules in a Layer with Applications and URL Filtering or Content Awareness enabled.Connection unification for the logs in the session is set in the Advenced Application Control Blade settings and has a default value of 180 minutes. These are basic Application Control logs in the R80.10 Unified Policy.