"fw ctl zdebug" is a powertool that is not exhausted from being used with "fw ctl zdebug drop". There is not much to be found in Check Point KB or in the documentation. "fw ctl zdebug" is an R&D tool for testing software in development. Therefore, the insert should be used with care. It starts a debugging in the background until it is aborted with CTRL+C. On productive systems it can have a high performance impact. Furthermore, the debug buffer is not the largest.
What happens when you execute! It is a macro that executes the following commands:
fw ctl debug -buf 1024
fw ctl debug [The option behind "fw ctl zdebug"]
fw ctl kdebug -f
[Wait until CTRL+C is pressed]
fw ctl debug 0
Node:
A current list with kernel debug flags can be found here.
Kernel Debug Flags R80.10
Kernel Debug Flags R77
Here are some good examples for debugging:
fw ctl zdebug + packet
fw ctl zdebug + packet | grep -B 1 TCP |grep -B 1 "(SYN)" <<< change SYN-ACK,ACK,FIN,... and/or UDP,TCP...
fw ctl zdebug + all |grep -A 1 "Monitor" | grep "1.1.1.1" <<< change IP address
fw ctl zdebug + all |grep -A 2 "Monitor"
fw ctl zdebug + sync
fw ctl zdebug + conn |grep "After VM:" |grep "(SYN)"
fw ctl zdebug + xlate
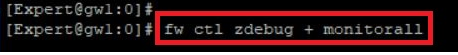
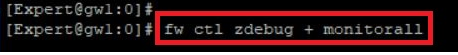
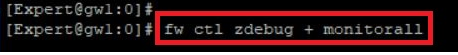
fw ctl zdebug + monitorall <<< use with host IP "| grep 1.1.1.1" or network range "| grep 1.1."
fw ctl zdebug + monitor <<< use with host IP "| grep 1.1.1.1" or network range "| grep 1.1."
fw ctl zdebug + filter conn | grep -A 8 "rule 1" <<< change rule number - show connetions to rule xyz
fw ctl zdebug + filter monitor | grep -A 8 "rule 2" <<< change rule number - show connetions to rule xyz
Attention, if you turn on debugging, this will affect the performance of the firewall.
Regards,
Heiko
➜ CCSM Elite, CCME, CCTE ➜ www.checkpoint.tips