Dear all, I would like to request assistance with a project scenario, as described below:
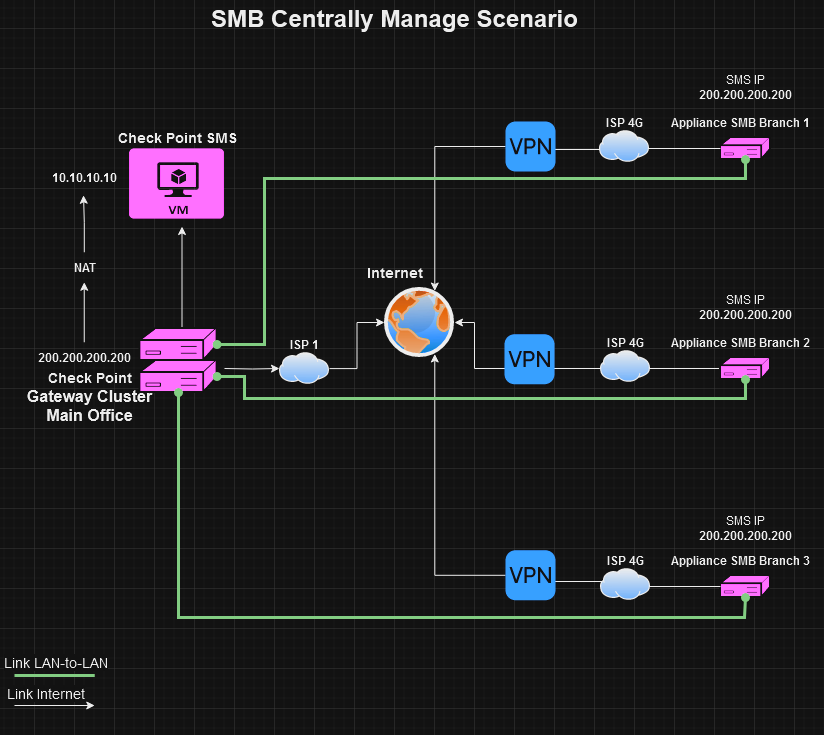
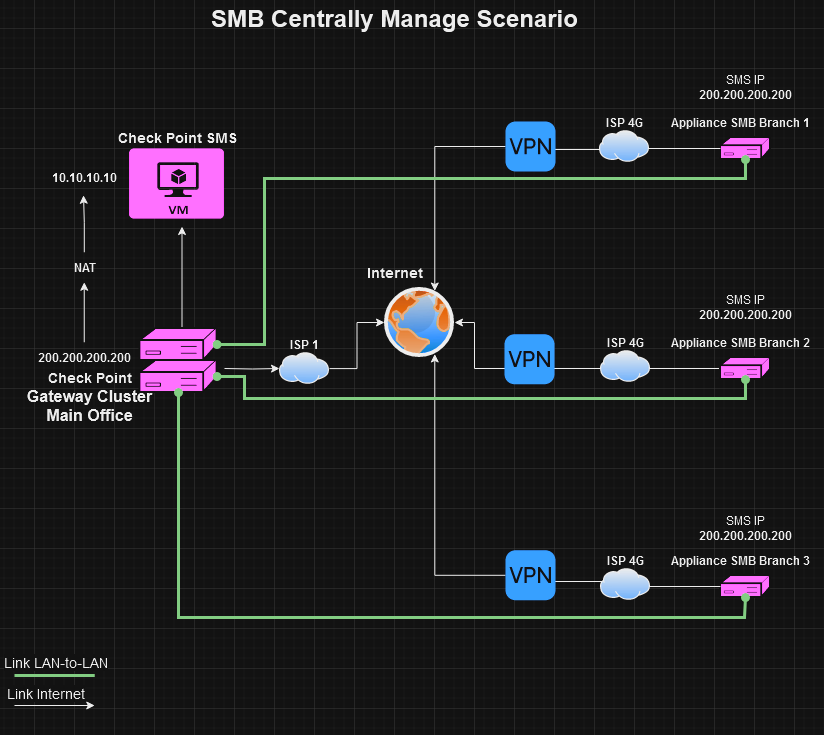
We have a client with a need to connect several remote branches to the company's main office with link redundancy. They already have a LAN-to-LAN structure in production, fiber links that extend from the main office to these branches, providing local and internet connectivity.
Additional internet links will be added to these branches, mostly 4G links (dynamic IP). SMB appliances (1500 Spark) will be installed, and the management of these appliances will be the same as the Main Office Cluster, as shown in the topology image. This means both the Main Office cluster and the branches will be in the same SMS.
To ensure that internal resources of the Main Office remain available to the branches in case the LAN-to-LAN link goes down, it is necessary to establish a VPN tunnel through the secondary link (4G).
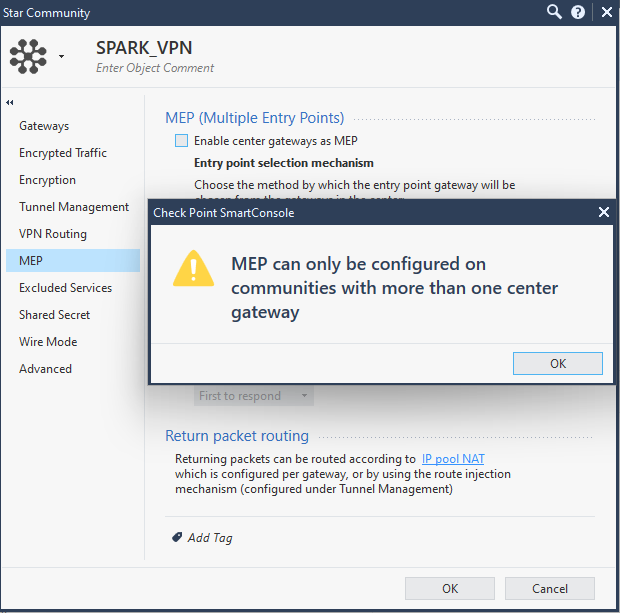
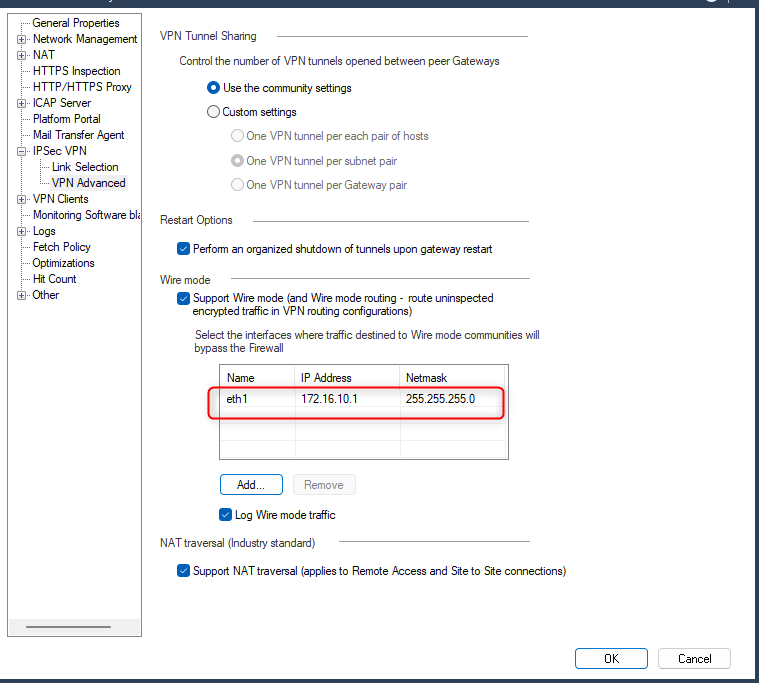
However, here is the challenge: if we have the Main Office cluster and the Spark from a branch in the same SMS, when we create the Star Community and add the participating gateways, any traffic coming from Spark is expected by the Cluster to be within the Community.
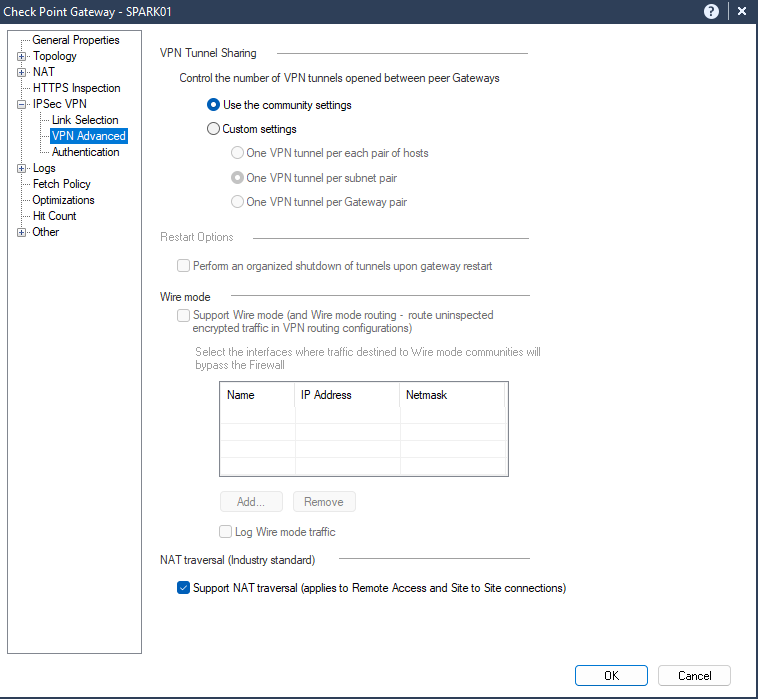
How could I separate this traffic both in Spark and the Cluster? In a way that, while the primary link (LAN-to-LAN) is up, all traffic goes through it, outside the VPN tunnel. When this traffic reaches the Cluster outside the tunnel, it should be accepted and routed normally. And when the primary link (LAN-to-LAN) goes down, the VPN tunnel with the secondary link (4G dynamic IP) should be established and continue to provide connectivity to the internal resources of the Main Office.
We tried to establish the VPN tunnel through the LAN-to-LAN link, believing that when this link became unavailable, the secondary link would establish the tunnel normally. However, the tunnel is not established by the secondary link; according to logs and debugs, apparently, phase 1 is completed, but for some reason, phase 2 never starts.
I have attached the topology image of the project described above. If the tests are successful, approximately 400 Spark appliances will be installed as part of this topology.
I appreciate you for helping me overcome this challenge.
Thank you in advance for your attention.
Topology: