I am sure that the majority of CheckMates users sometime already stumbled upon the article "HowTo Set Up Certificate Based VPNs with Check Point Appliances - R77 edition" written by @Danny . He is our instructor and CTO at ESC and has been working with Check Point Firewalls for almost two decades.
With the new R80.x release an update to his great VPN article was needed. Here we go:
Preface
Securing virtual private networks (VPNs) in enterprise Site-to-Site environments is an important task for keeping the trusted network and data protected. Also it's critical to avoid any loss of data sovereignty.
When it comes to VPN security many security experts first think of encryption algorithms, perfect forward secrecy (PFS), Diffie-Hellman groups... and a long pre-shared key (PSK).
What about VPN certificates?
Every security expert knows how much better certificates are for gaining high security levels. Therefore certificates are always best practice in enterprise grade security environments.
However, most VPN Site-to-Site setups are still based on simple, long lasting pre-shared keys. In many cases these keys were even forgotten by the administrators in charge of keeping the network secure because once configured for the VPN tunnel they are not needed anymore.
This is because it's much quicker and really easy to set up a VPN with a simple pre-shared key than having to deal with certificates and a certificate authority (CA).
But the comfort of choosing PSKs over certificates does not only minimize your security level it also makes you vulnerable to potential attacks and is not as safe as you might expect. Even if you pick a long PSK! This is because tools like 'ike-scan' (also comes preinstalled with Kali Linux), pks-crack etc. make it really easy to crack your PSK. It's just a matter of time. ℹ️
As a rule of thumb: VPN certificates significantly increase VPN security!
So let's get started!
When working with VPN tunnels between Check Point gateways there is absolutely no reason not to use VPN certificates.
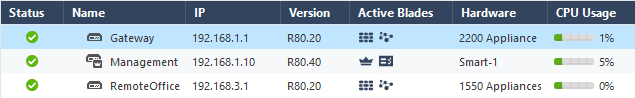
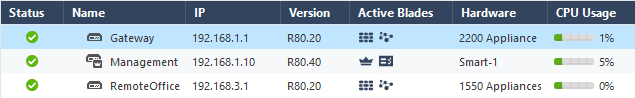
We used the following setup :
Gateway : Check Point Firewall & VPN
Management : Check Point SmartCenter (R80.40)
Remote Office : Check Point 1550 Appliance
(it is important to notice that the 1500 SMB appliances can only be centrally managed with R80.30 Jumbo Take_76 or R80.40 as mentioned in sk157412 and sk163296)
Centrally managed
Check Point is well-known for its superior security management solution to which all Check Point gateways are connected. This central management approach makes it remarkably easy to deploy security settings to all connected gateways with a single click on policy installation.
Check Point's security management is called SmartCenter Server (or Multi-Domain Security Management) and has a built-in internal certificate authority. This Internal CA enables the global use of certificates between all connected components and gateways right out-of-the-box.
Check Point automatically generates certificates whenever a new Check Point object is created, so you don't have to take care of certificate handling. Check Point does it all for you.
Establishing a certificate based VPN in centrally managed Check Point environments is as easy as 1-2-3.
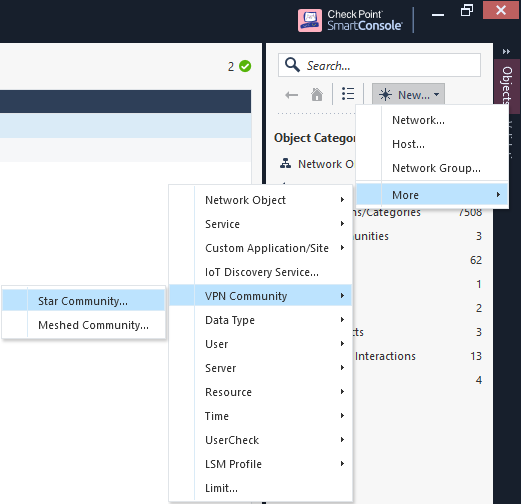
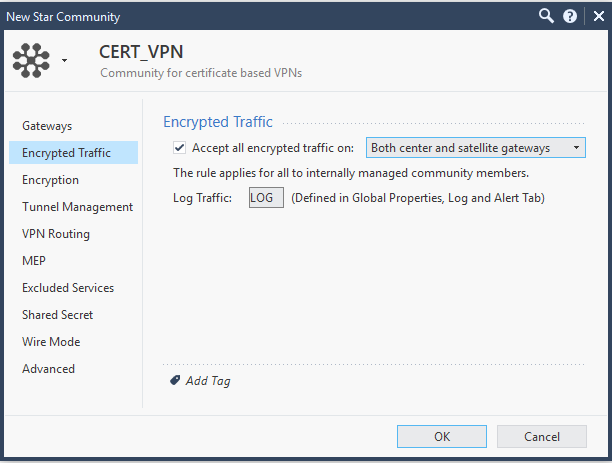
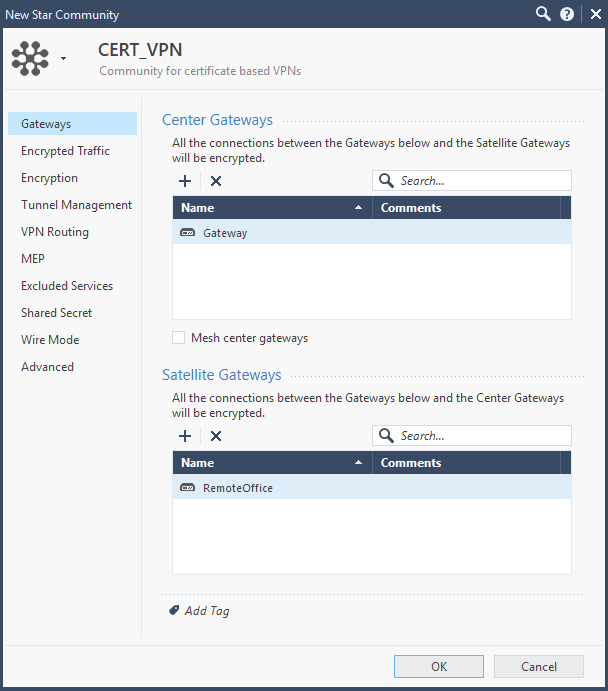
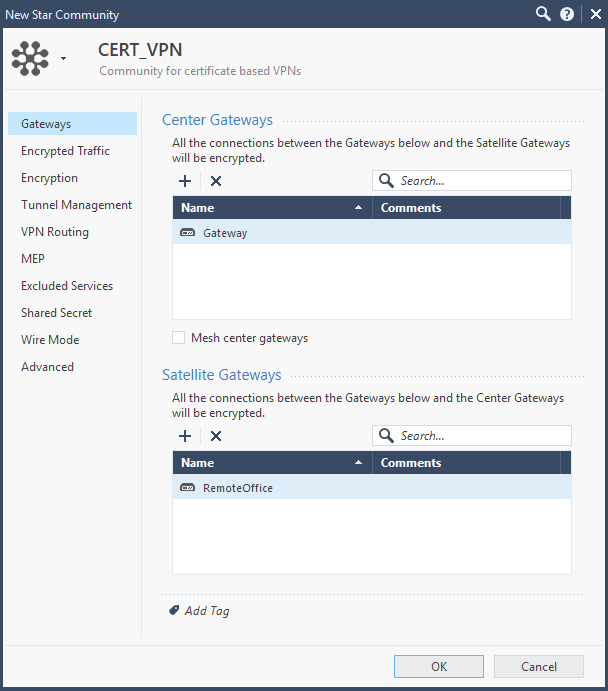
First, create a VPN community for certificate based VPNs (Mesh or Star topology)
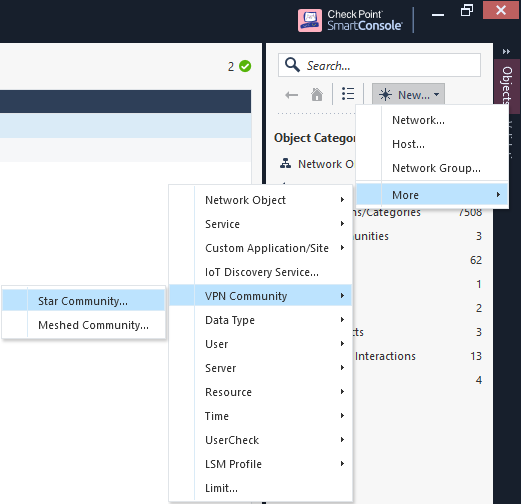
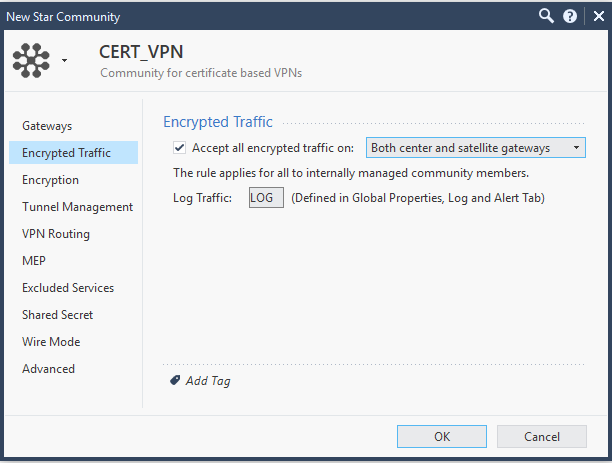
Now let's take a closer look at the settings of the created VPN community.
Check the "Accept all encrypted traffic on: " box and select the "Both center and satellite gateways" in the "Encrypted Traffic" tab.
Configure your preferred VPN encryption settings for Phase 1 (IKE) and Phase 2 (IPsec) and allow permanent tunnels if needed.

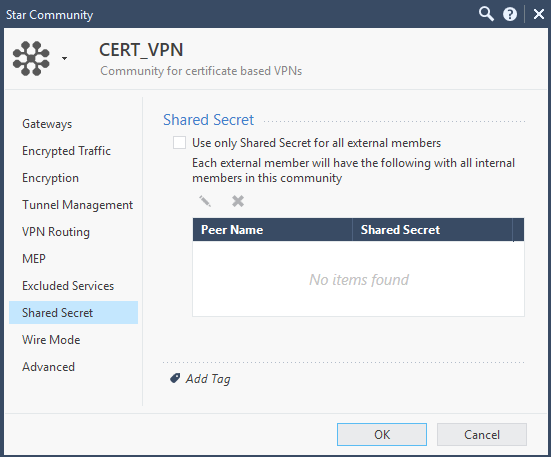
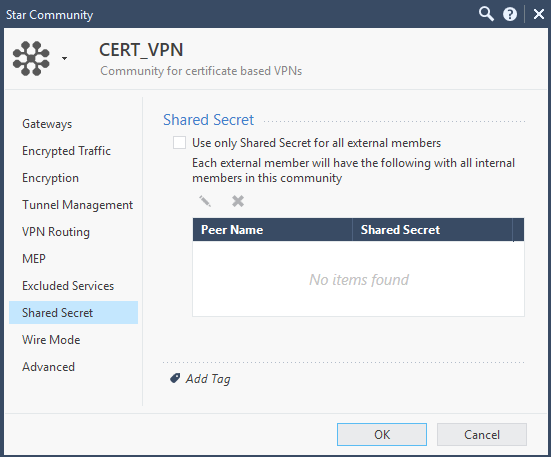
Leave the checkbox for pre-shared keys unchecked!
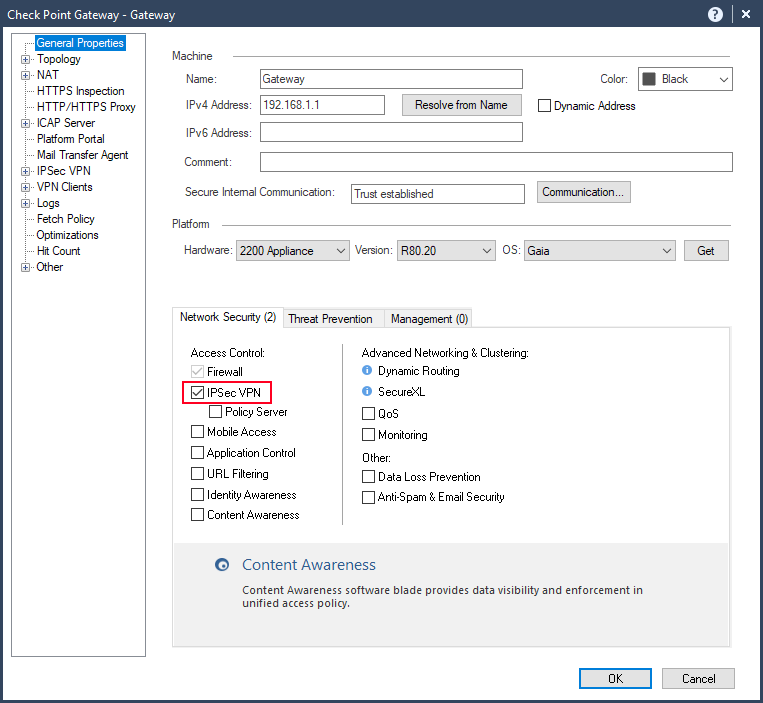
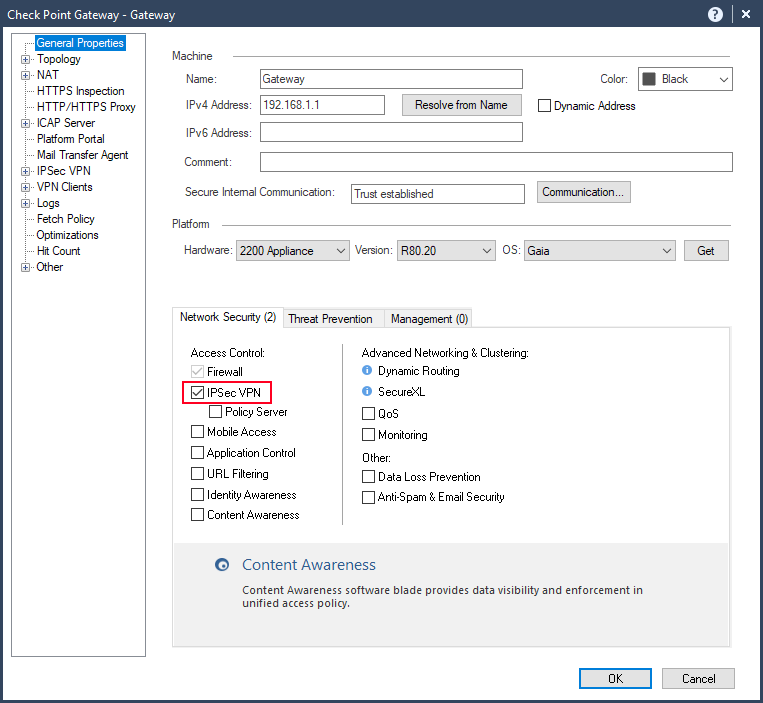
In the next step we want to activate and configure the needed IPSec VPN blade on the participating gateways. There are two possible options to do this. You can activate the blade in the “General Properties” tab on the gateway or during the installation when using the “Wizard Method”.
Classic Method
Activate the IPSec VPN blade in the "General Properties" tab.
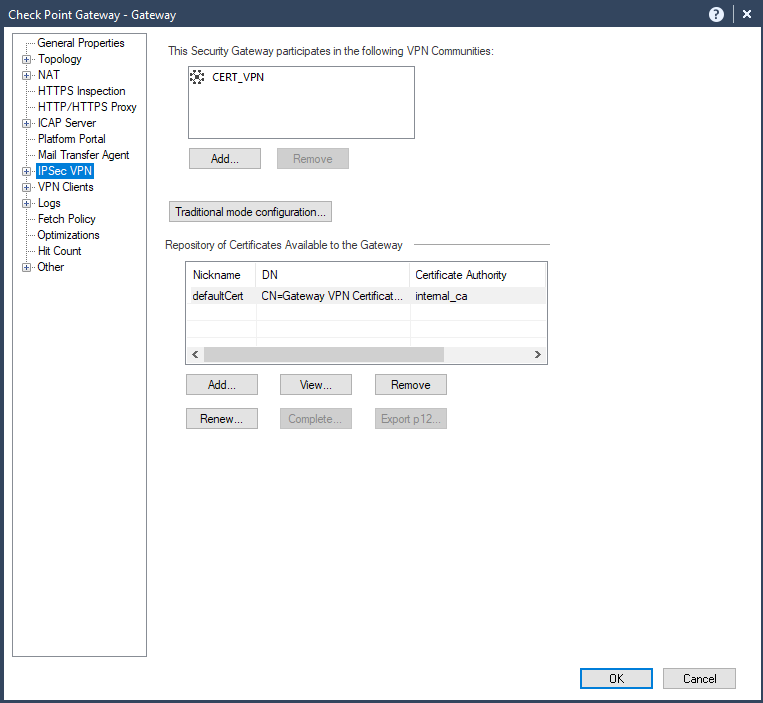
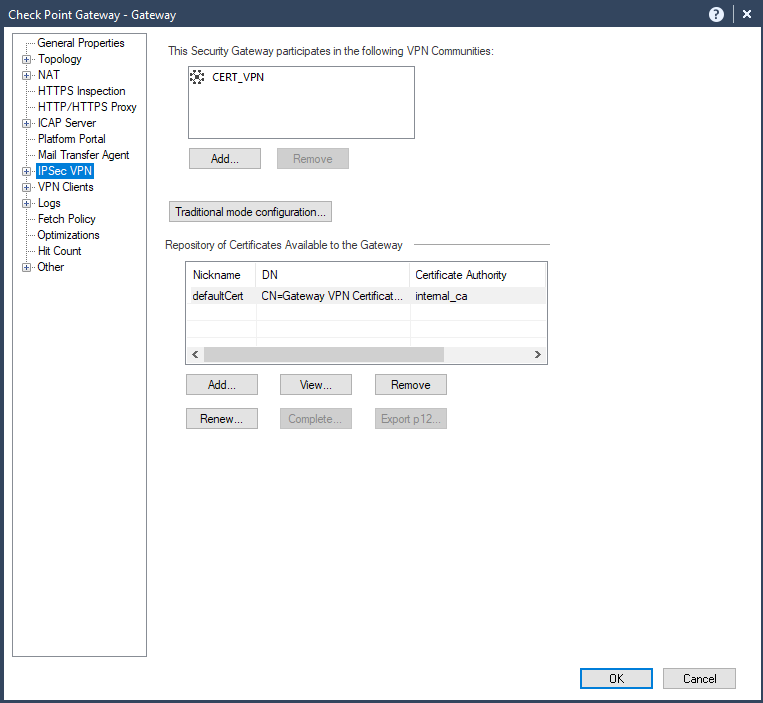
Choose your VPN community.
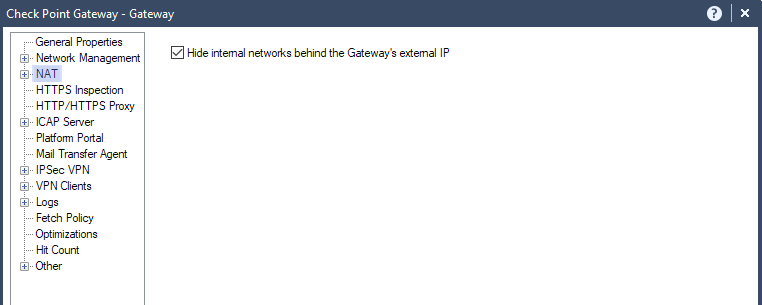
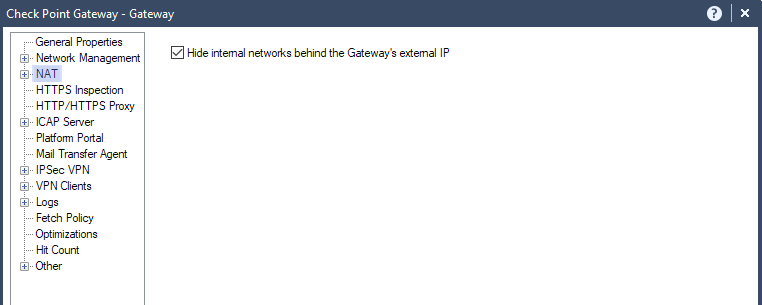
Activate NAT on the participant gateways.
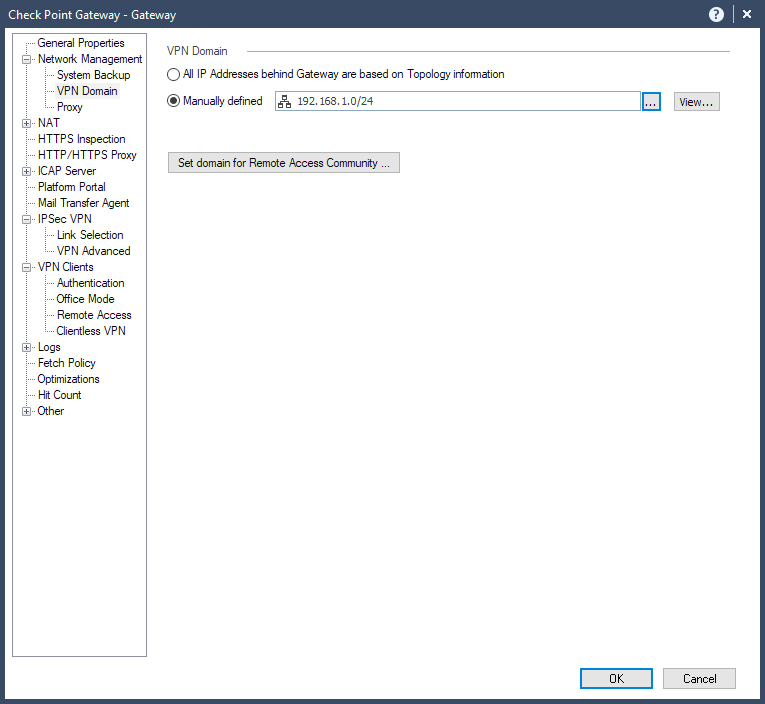
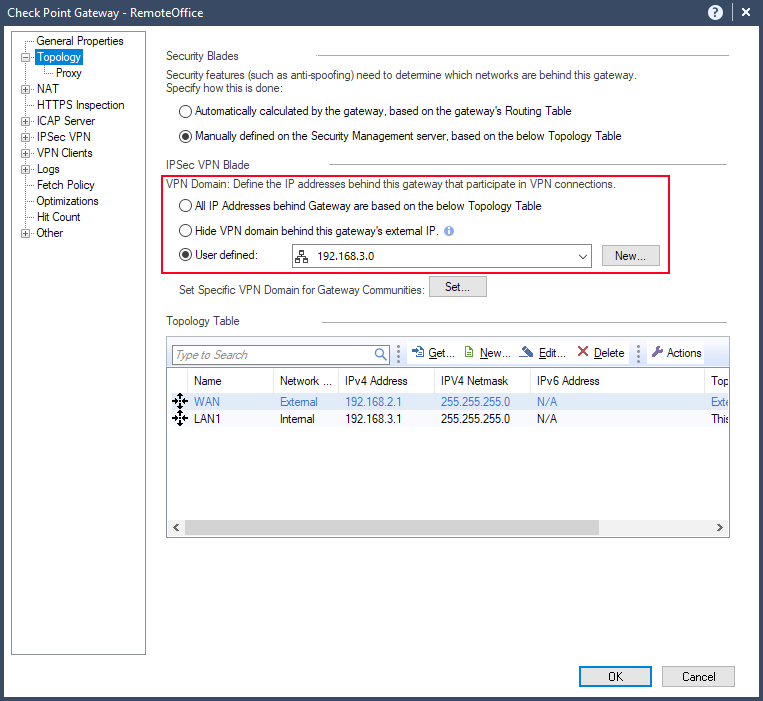
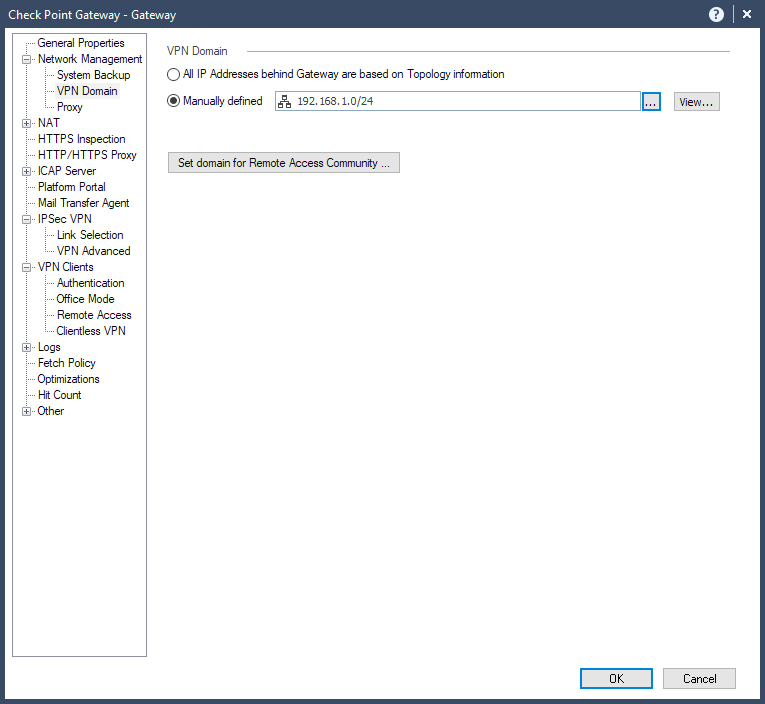
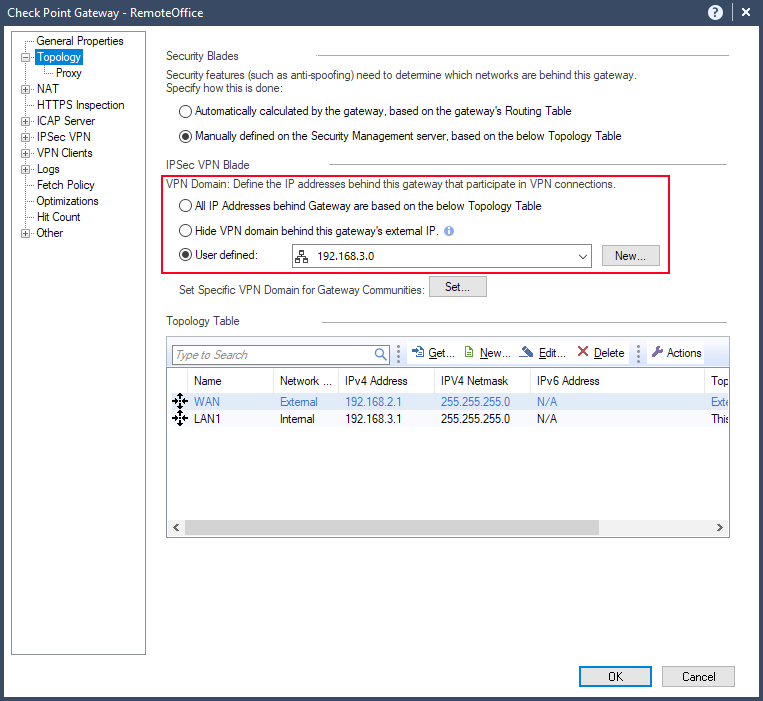
..and select the VPN encryption domain of the specific object.
Gateway :
RemoteOffice :
(end of Classic Method)
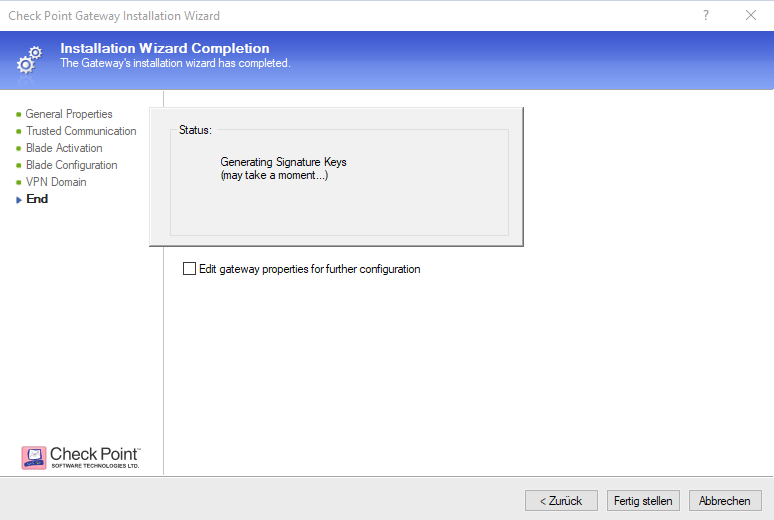
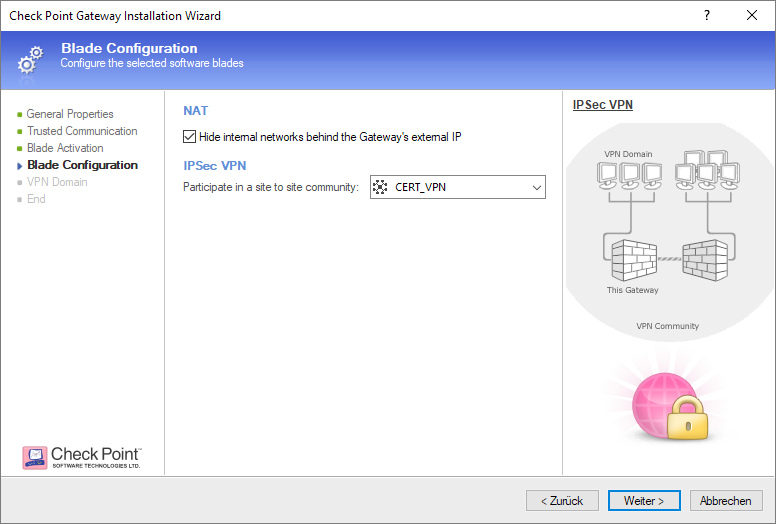
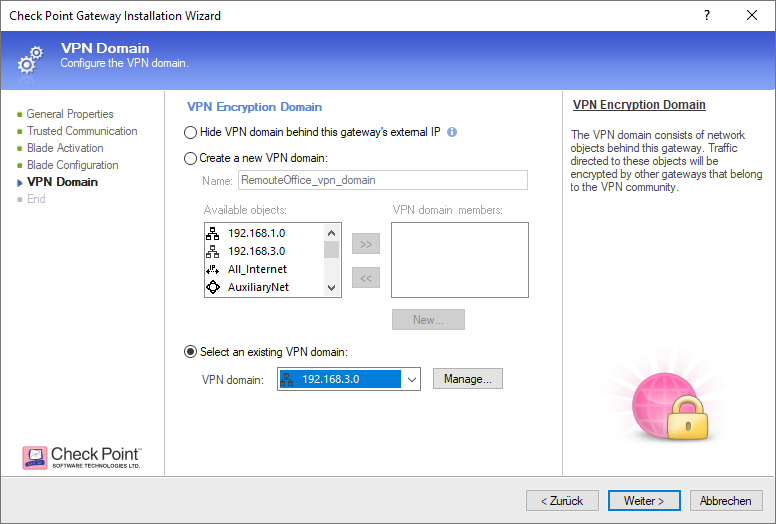
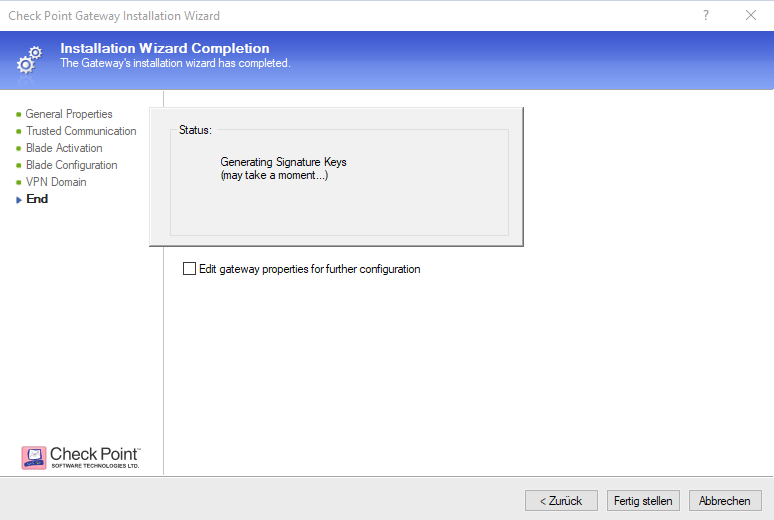
Wizard Method
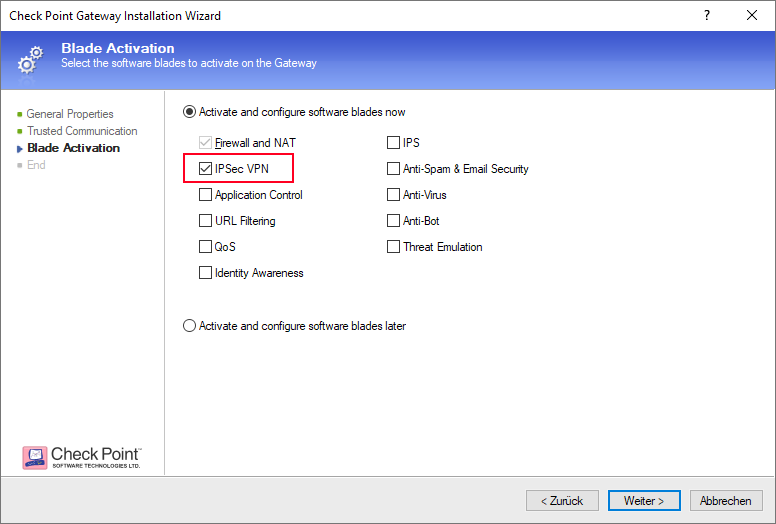
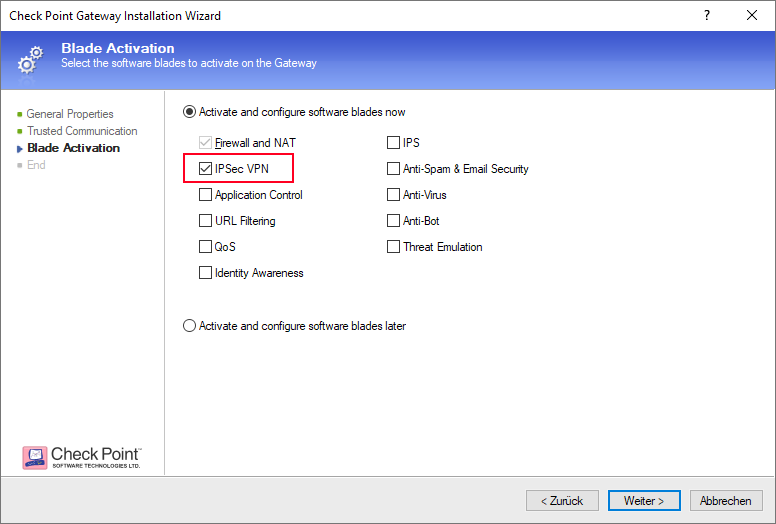
Activate IPSec VPN on your participant gateways.
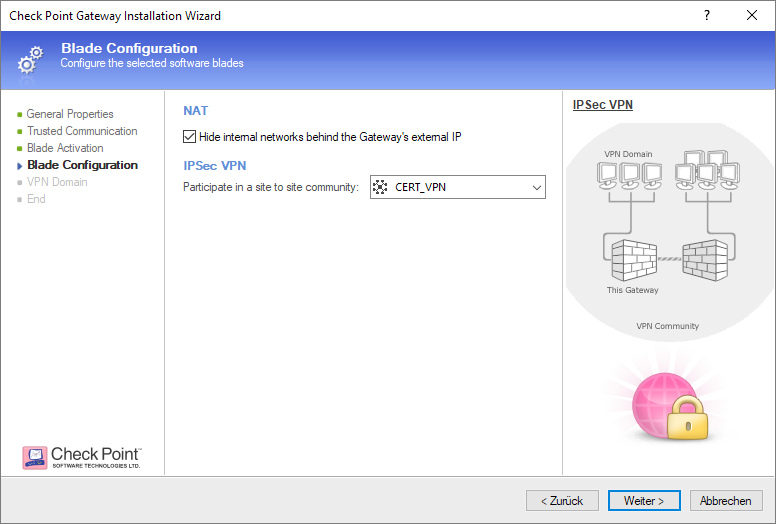
Choose your VPN community and activate NAT
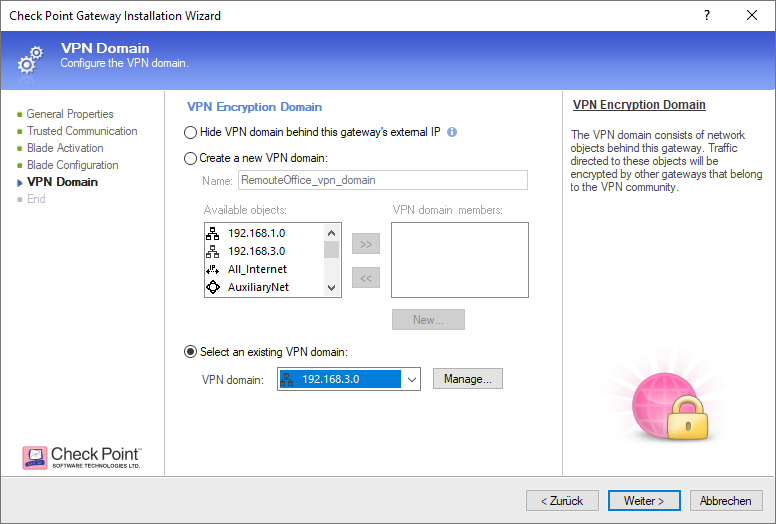
..and select the VPN encryption domain of the specific gateway.
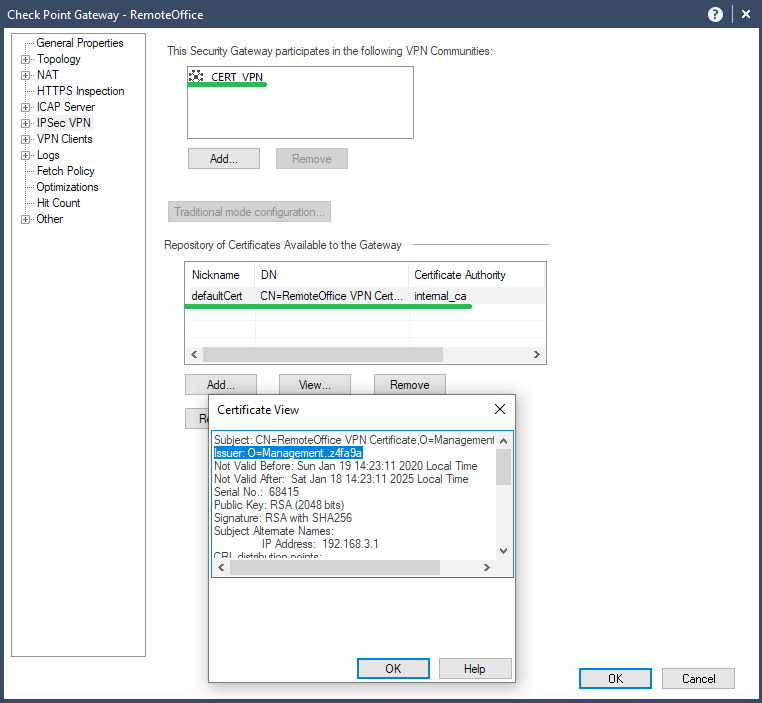
When everything is set verify your VPN certificate and IPSec VPN community.
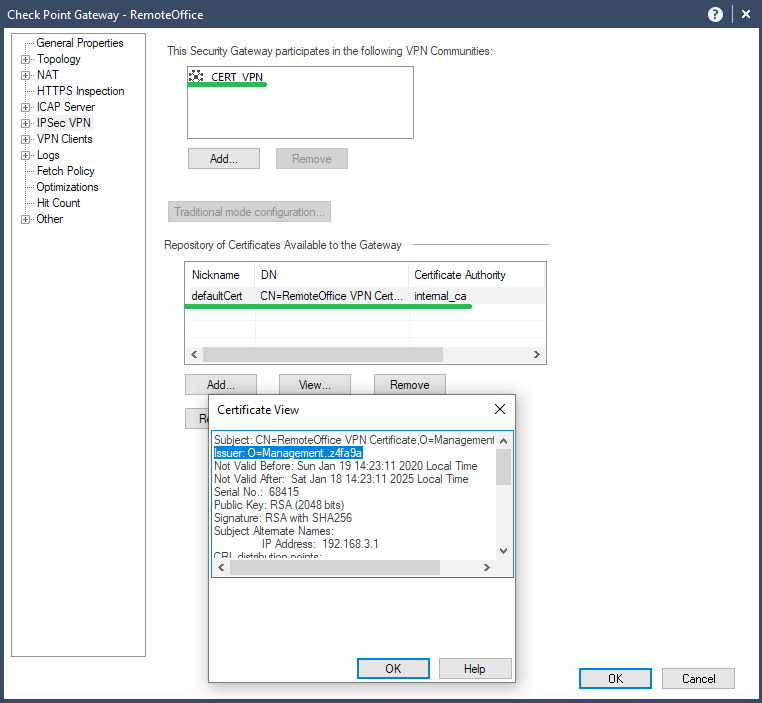
After you have configured the VPN topology for your VPN gateways you should add them to your VPN community (if not already done).
Finally, install the security policy.

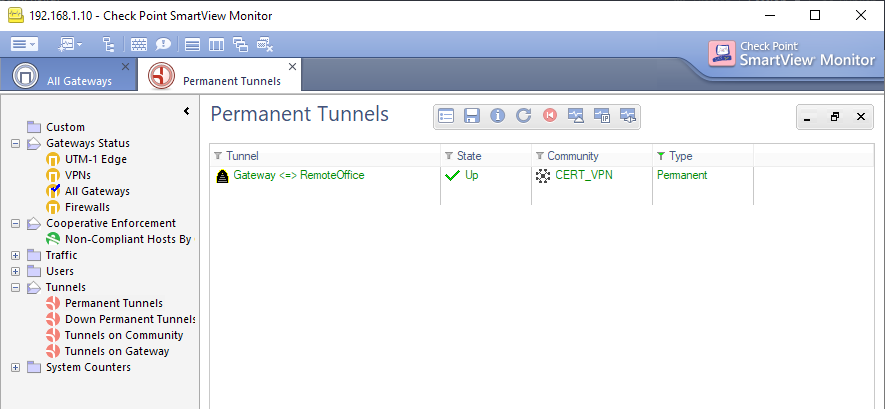
The certificate based VPN tunnel is now up and working!
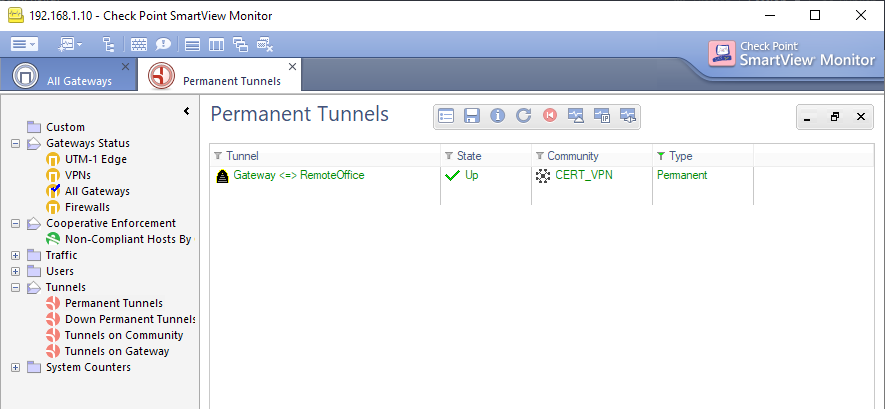
Should the connection to the SMB appliance (in our case the "RemoteOffice") get lost after the policy installation check the "Connection Persist" option and activate "Keep all connections".

Locally managed
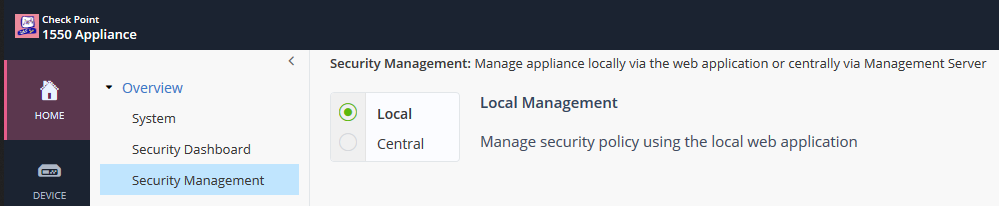
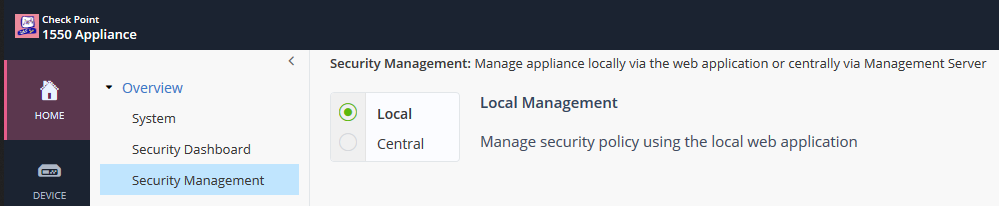
Check Point's 700 appliances are locally managed. So can be 1100 / 1400 / 1500 appliances.
These SMB appliances have their own local CA!
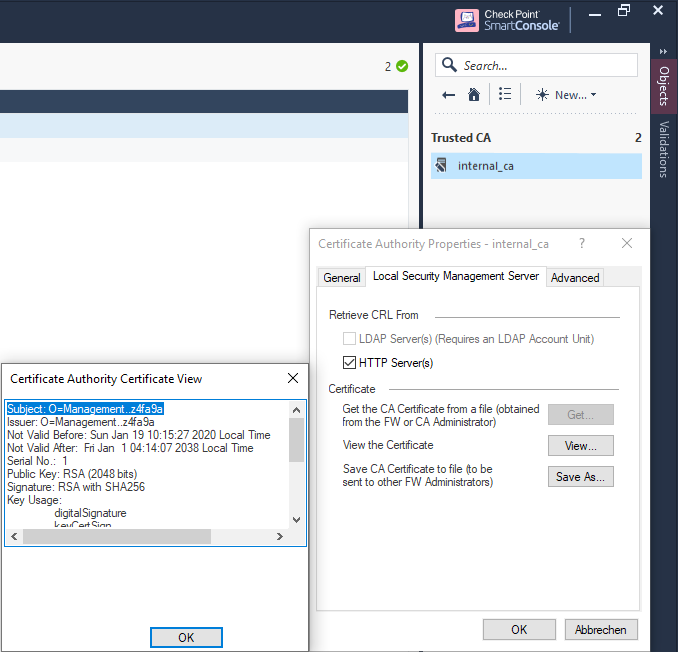
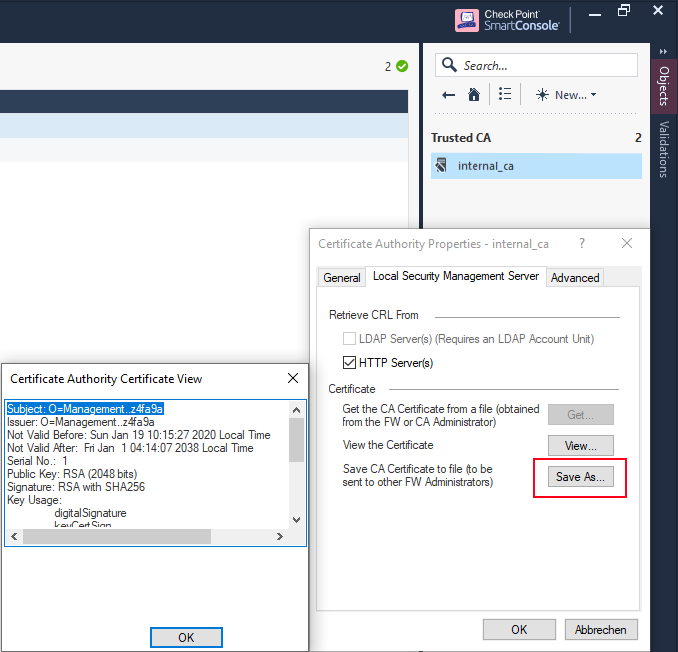
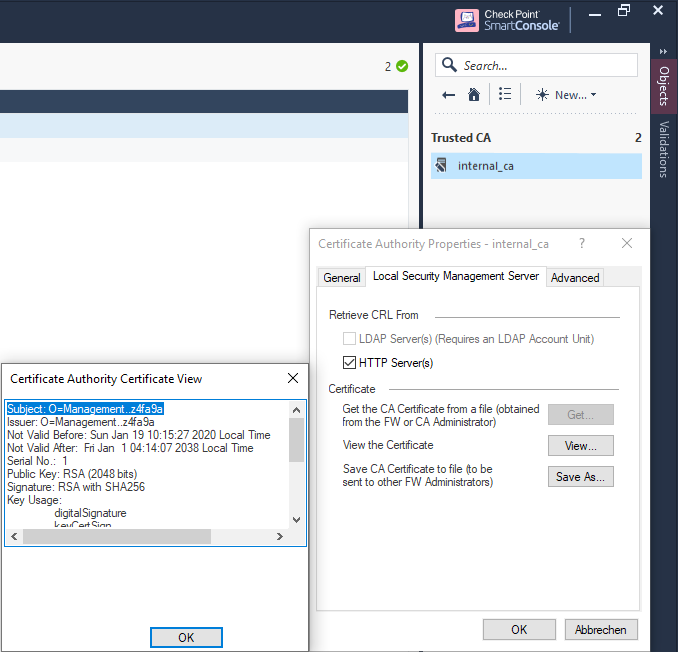
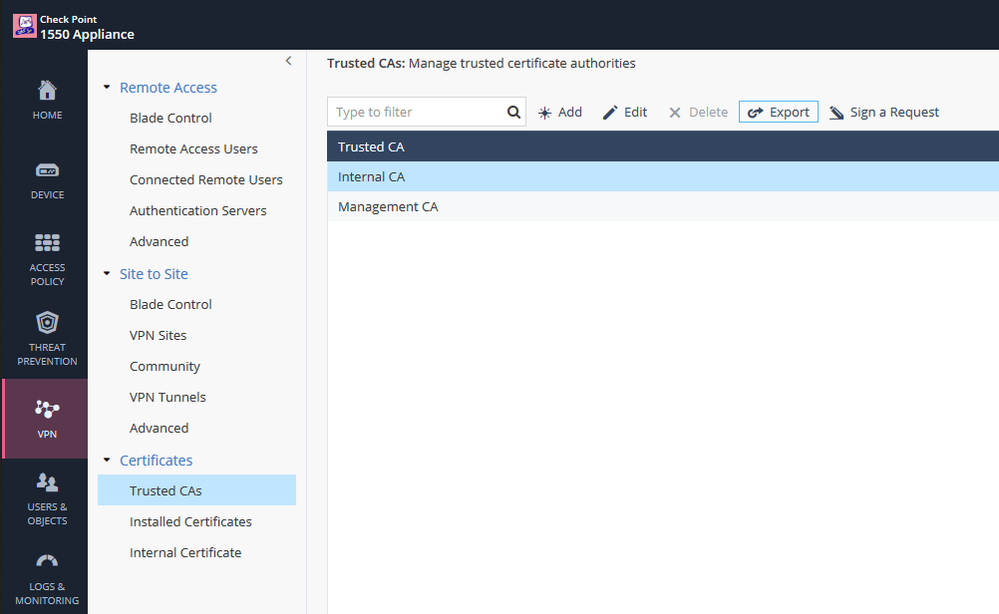
First, let's export our Internal CA to the 1100 / 1400 / 1500 appliance at our remote office.
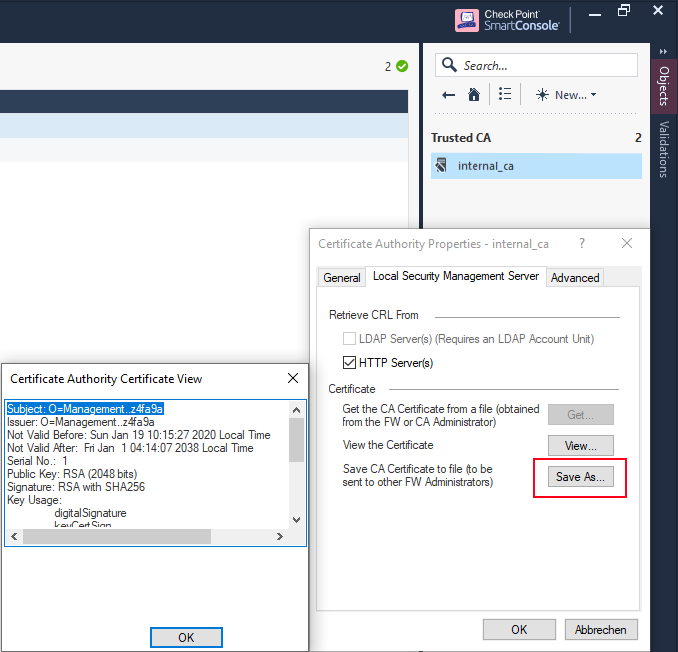
In SmartDashboard just navigate to Manage > Servers and OPSEC Applications... > internal_ca > Edit... > Local Security Management Server > Save As... and export the certificate.
Verify that the locally managed SMB appliance has Site-to-Site VPN enabled.

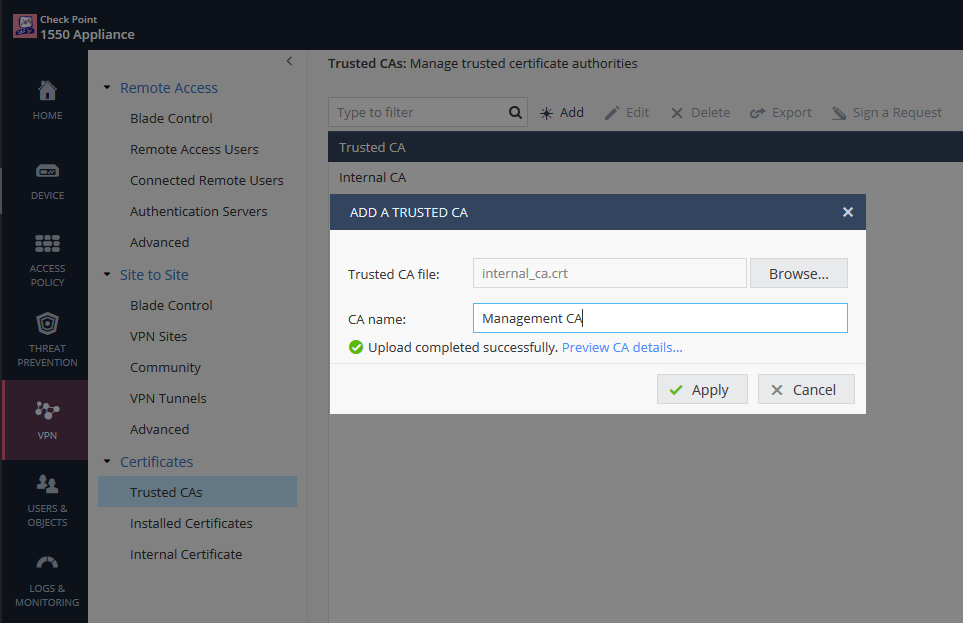
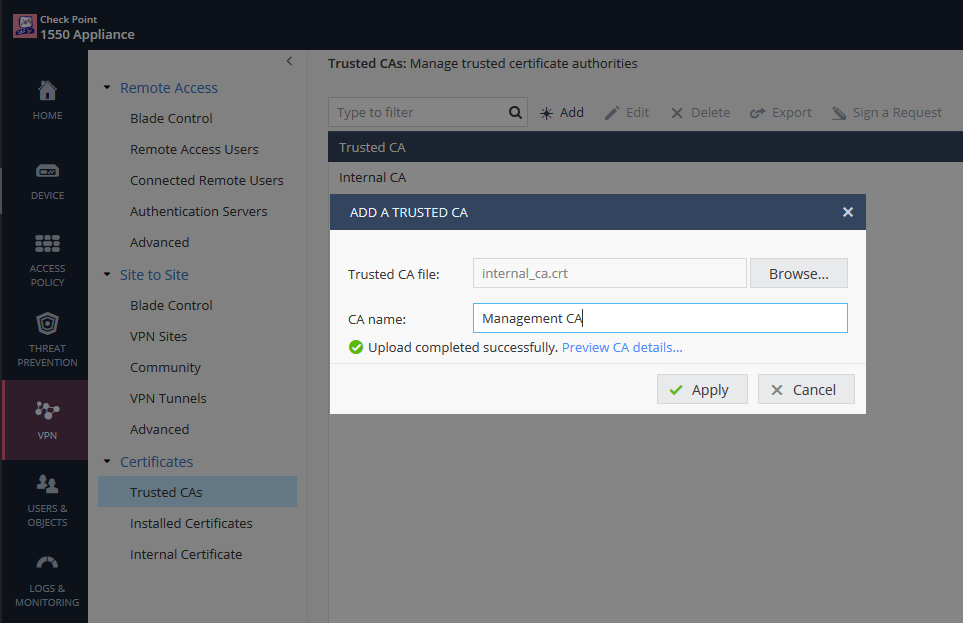
Import the internal_ca.crt file to your locally managed SMB appliance.
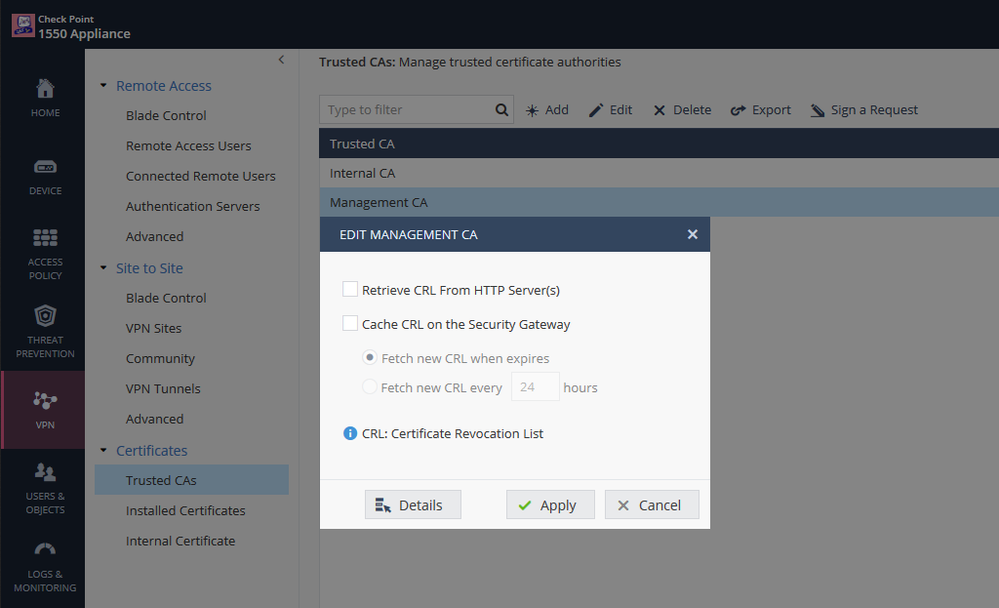
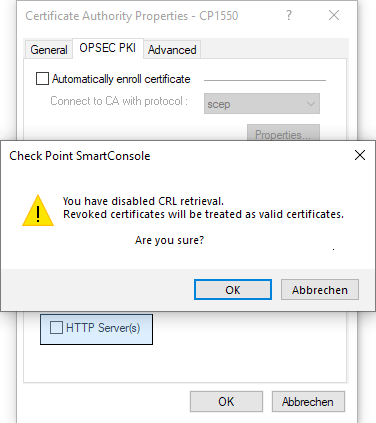
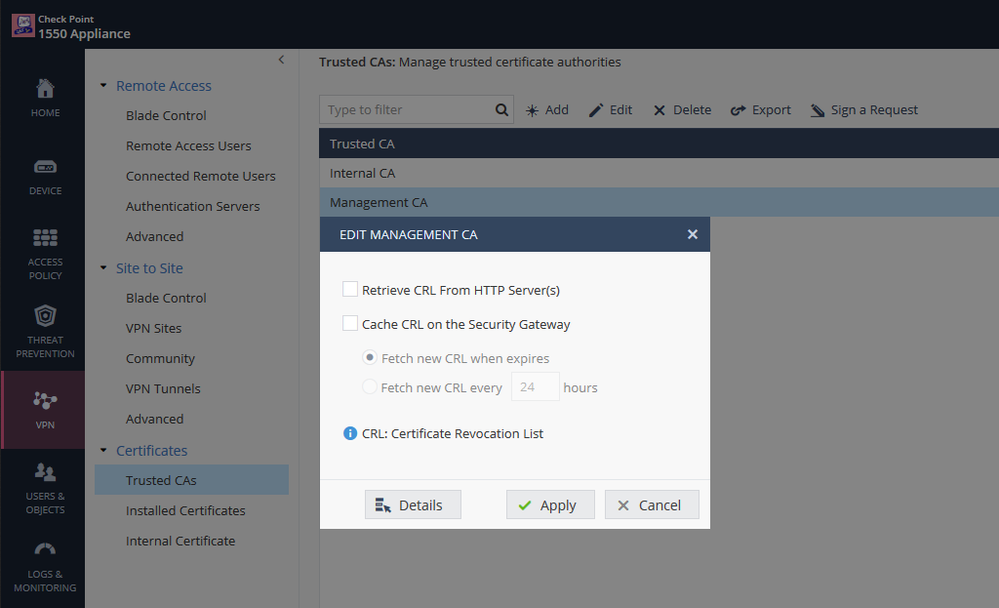
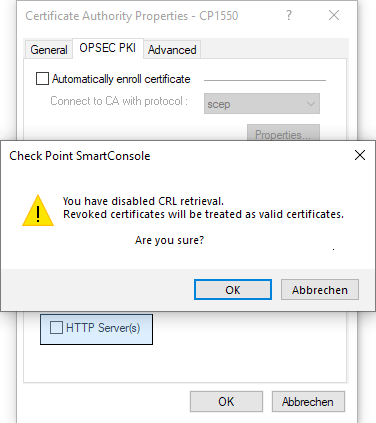
You may want to disable CRL checking if your Management as primary CRL Distribution Point can't be reached or isn't resolvable.
Easy, isn't it? Now we want to export the SMB appliance's certificate to our Management or (if you prefer) issue a certificate request to be signed by our management's Internal CA.
Option A - Export the SMB appliance's certificate
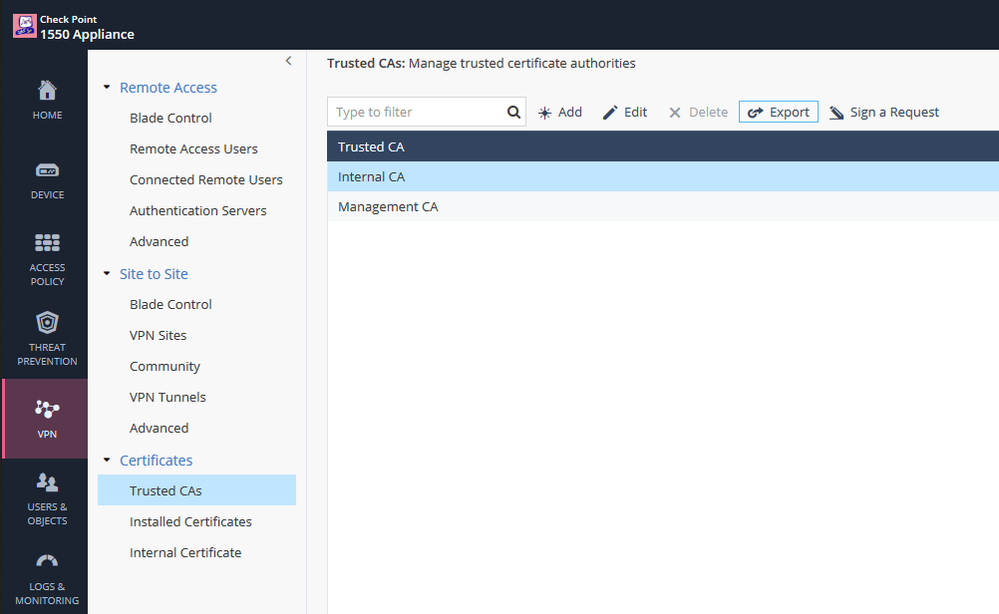
Highlight the Internal CA of our SMB appliance (NOT the one we just imported), then click "Export" and save the file.
Go to VPN >Certificates > Internal Certificates and copy the Certificate CN of the Internal VPN Certificate.

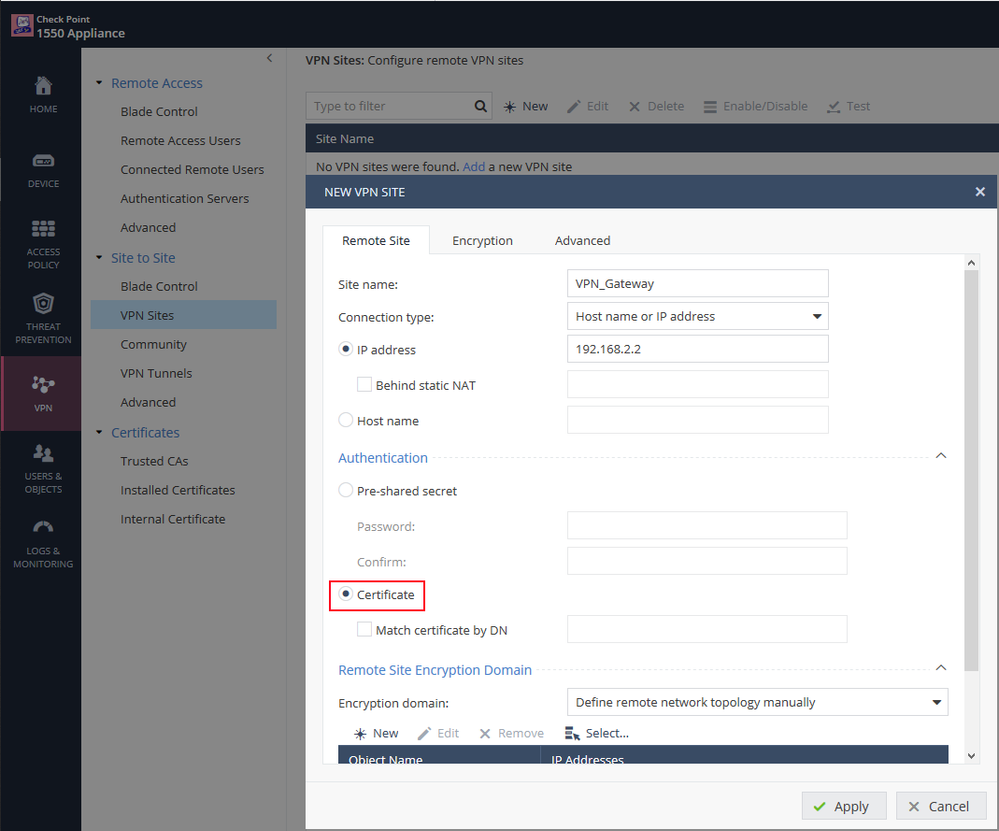
Create a VPN site for the certificate based VPN tunnel to our VPN Gateway and configure the site to use Certificate as authentification.
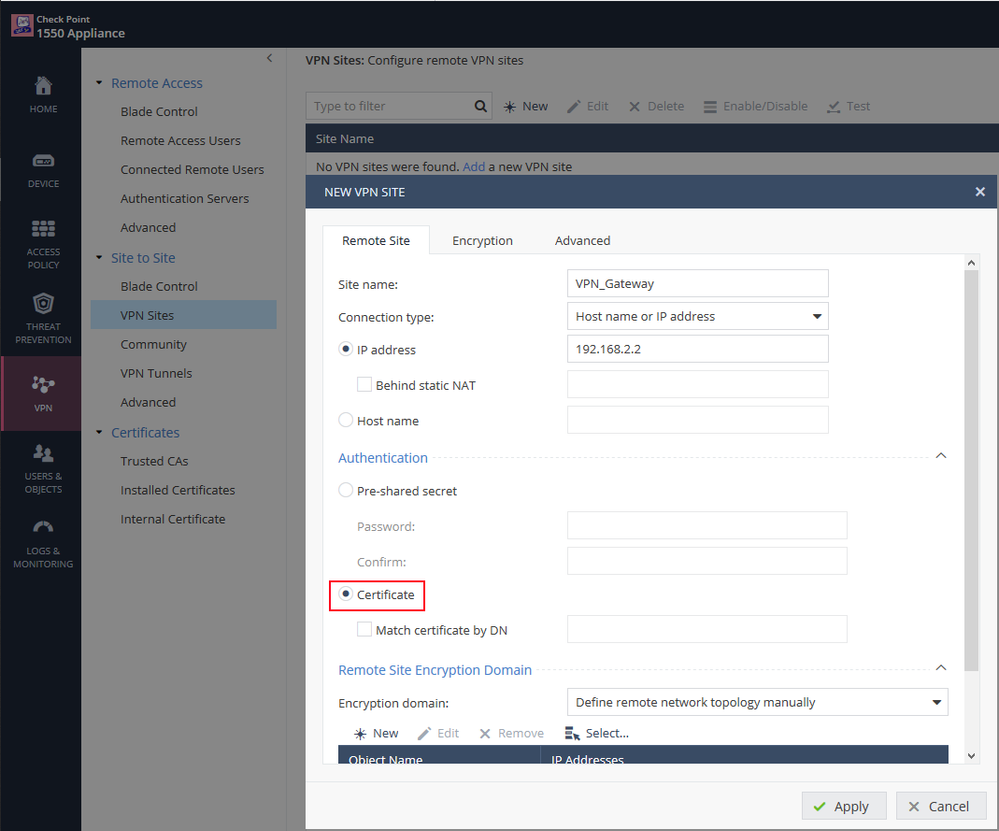
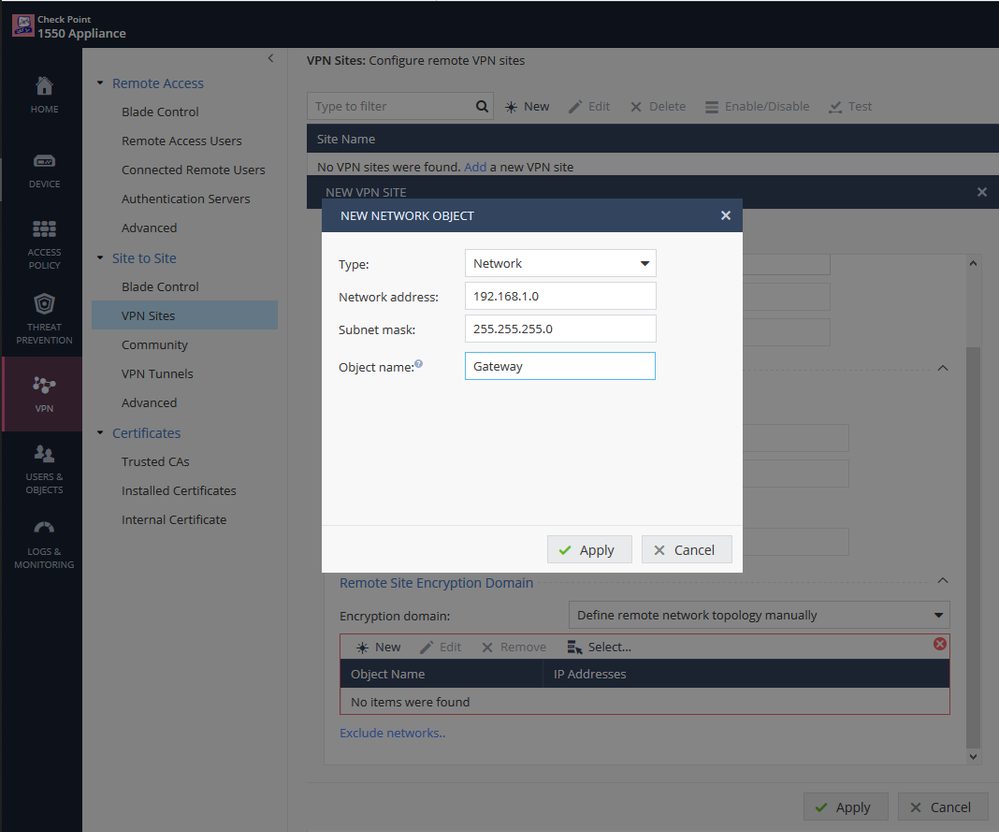
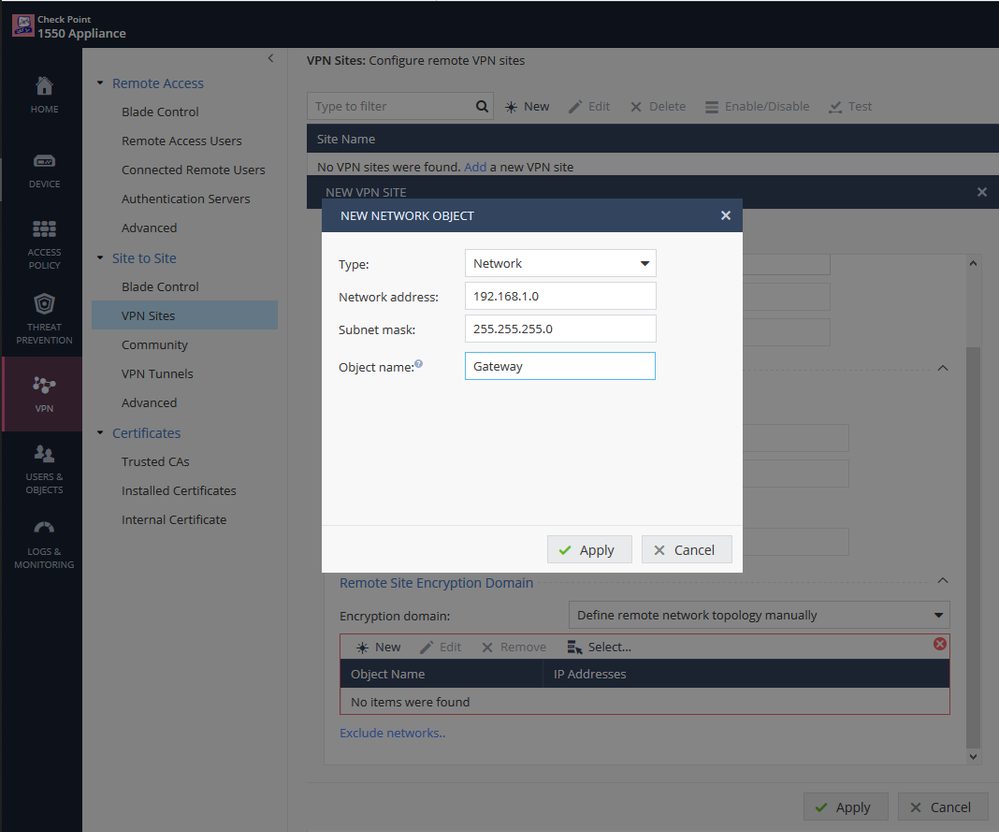
Don't forget to select the Remote Site Encryption Domain.
In the tab Advanced > Certificate Matching set the "Remote Site Certificate should be issued by" to our Management trusted CA's name and enable permanent tunnels if needed.
We are now finalizing our VPN setup in SmartDashboard on our Management.
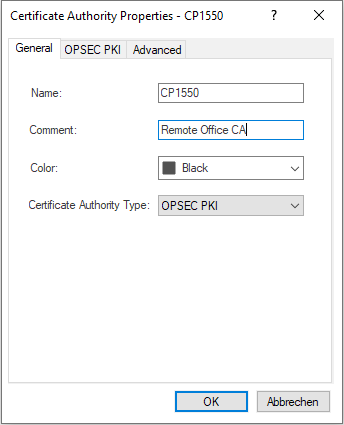
Navigate to Manage > Servers and OPSEC Applications.. > New > CA > Trusted select OPSEC PKI and open the tab OPSEC PKI to import our saved SMB Internal CA file.
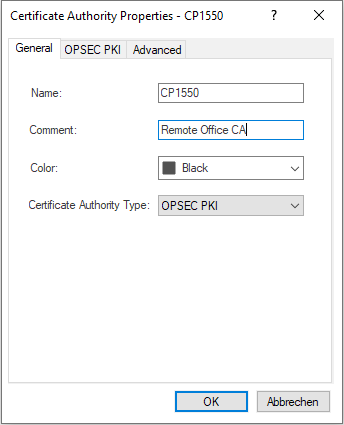

Again, you may want to disable CRL Checking if required.
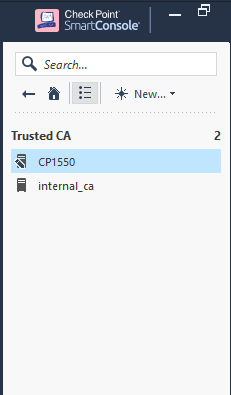
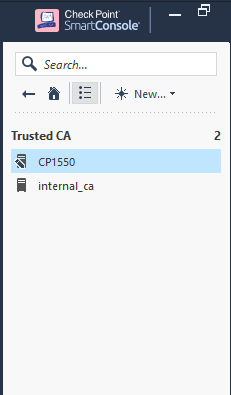
You'll then find our imported SMB certificate 'CP1550' next to our internal_ca within the Trusted CA list of our Management.
(end of Option A)
Option B - Issue a certificate request
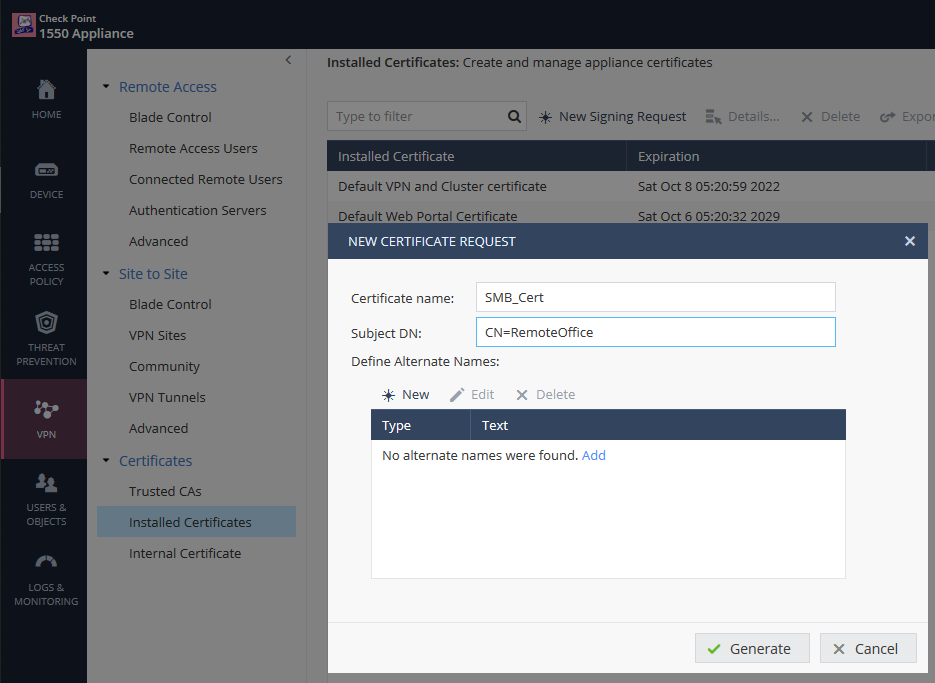
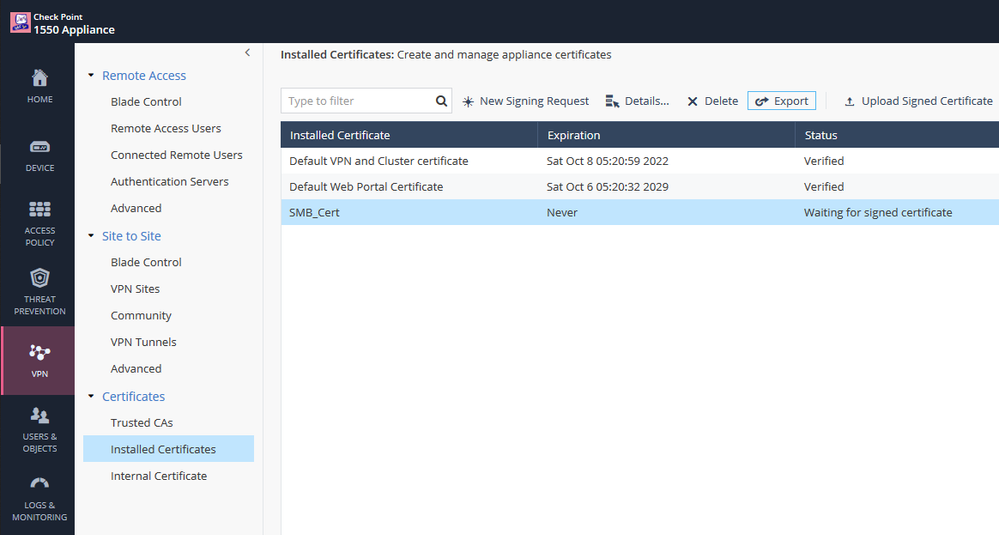
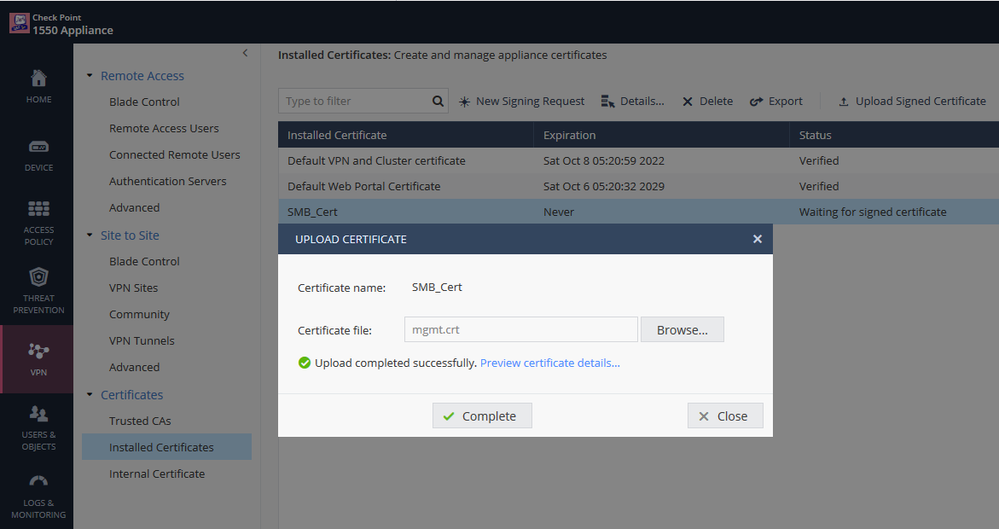
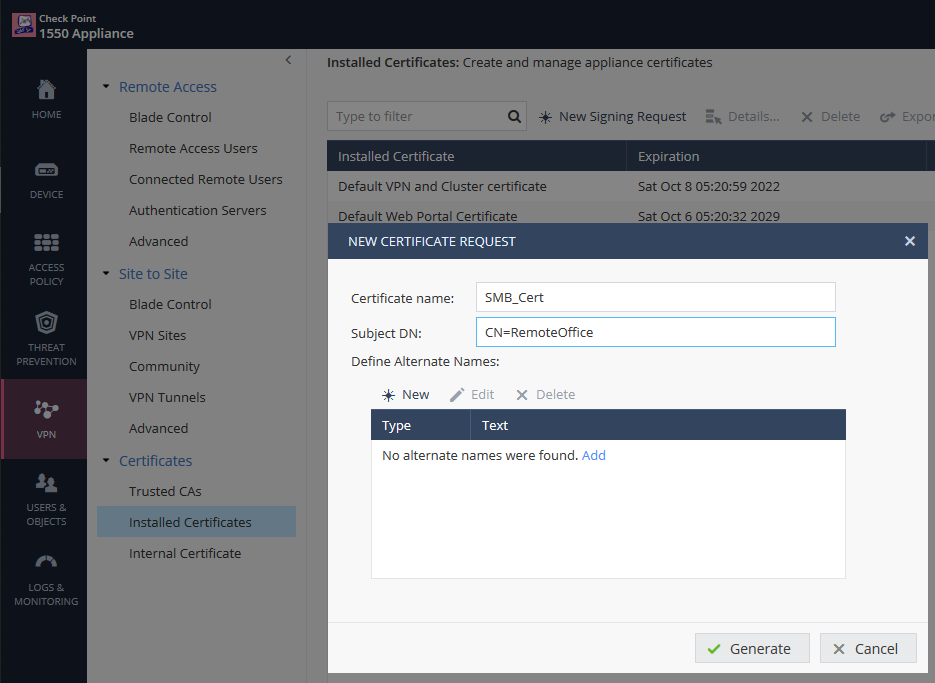
Go to VPN > Certificates > Installed Certificates and click New Signing Request to generate a new certificate.
Enter a Certificate name and Subject DN.
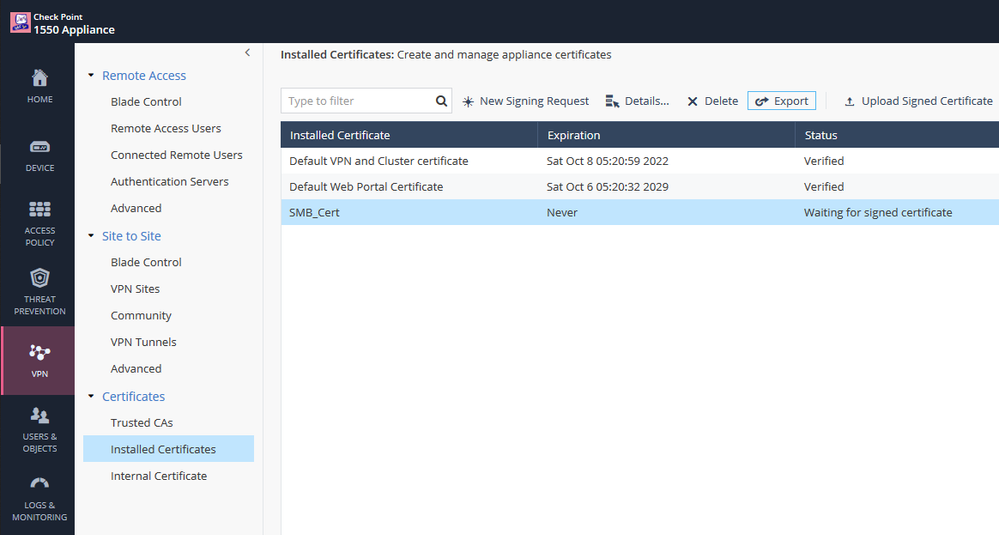
Export the signing request to a file.
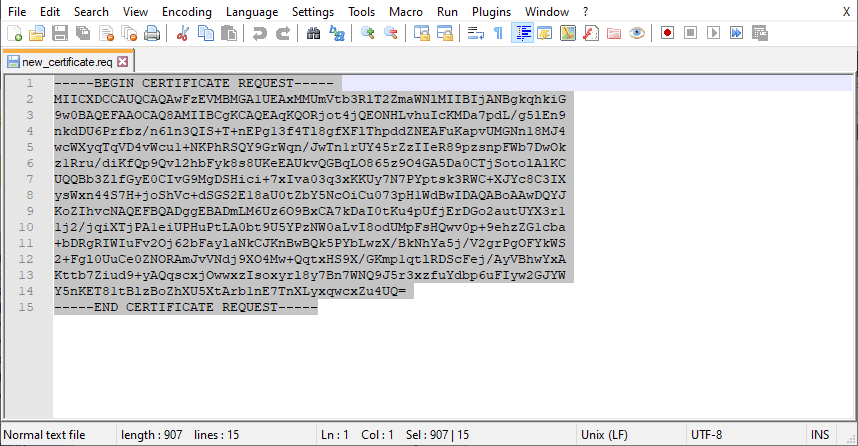
Copy the content of the exported file.
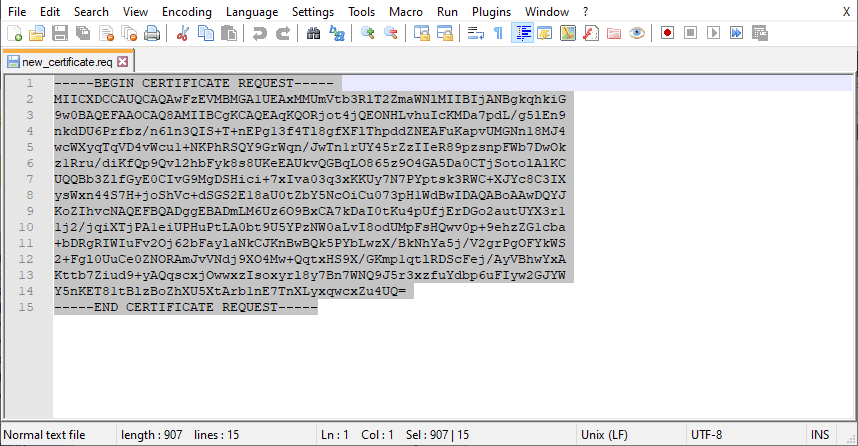
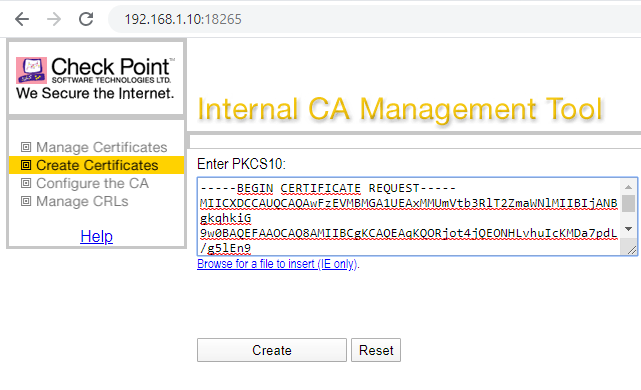
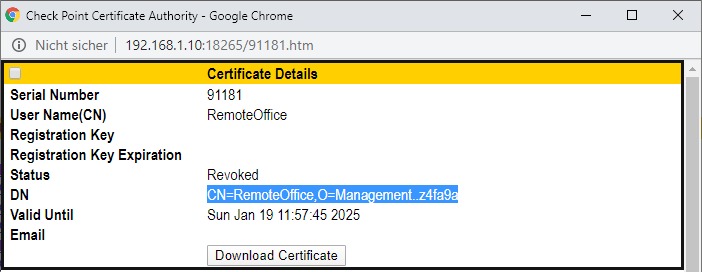
On the Management start the ICA Management Tool (sk39915), go to Create Certificates and paste the certificate request into the PKCS#10 text box.
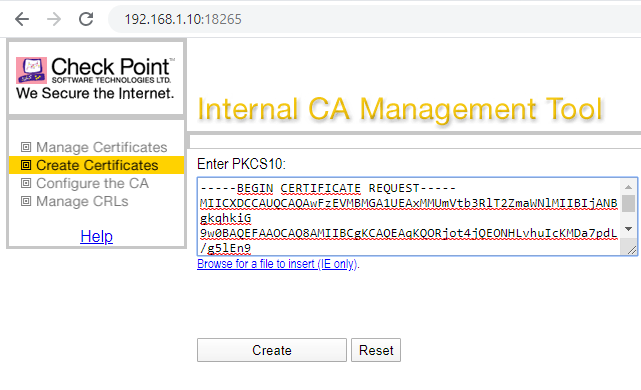
Create the signed certificate.
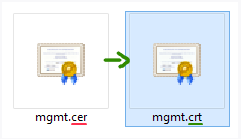
If required change the file name extension of the created certificate to .crt .
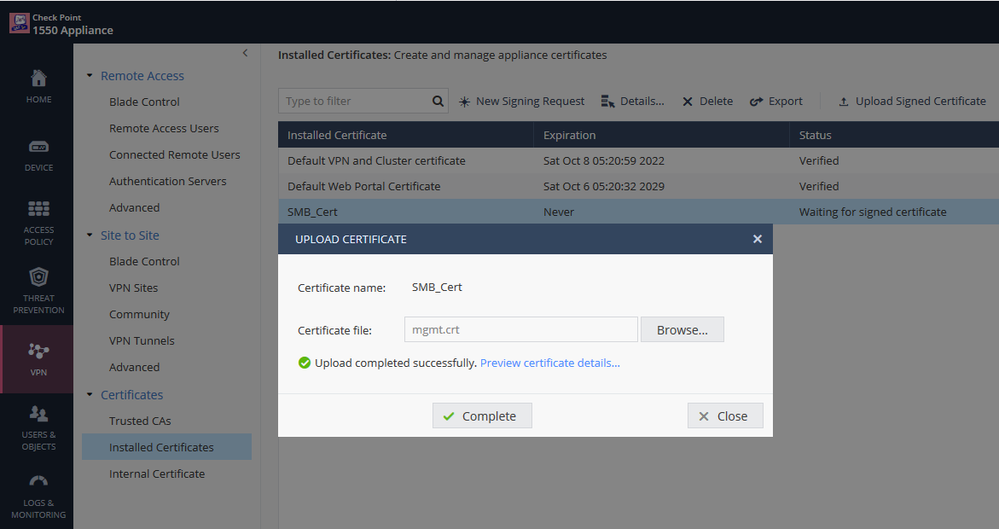
On the SMB appliance click 'Upload Signed Certificate', select the certificate and click 'Complete'.
(end of Option B)
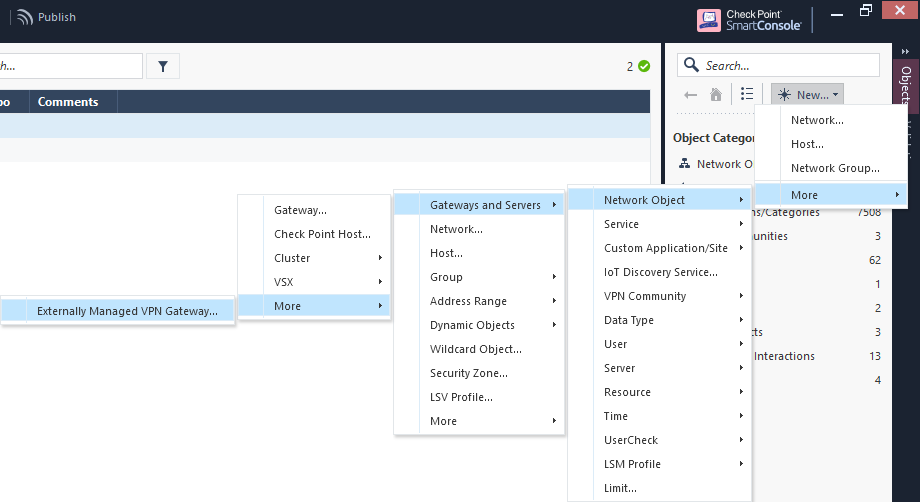
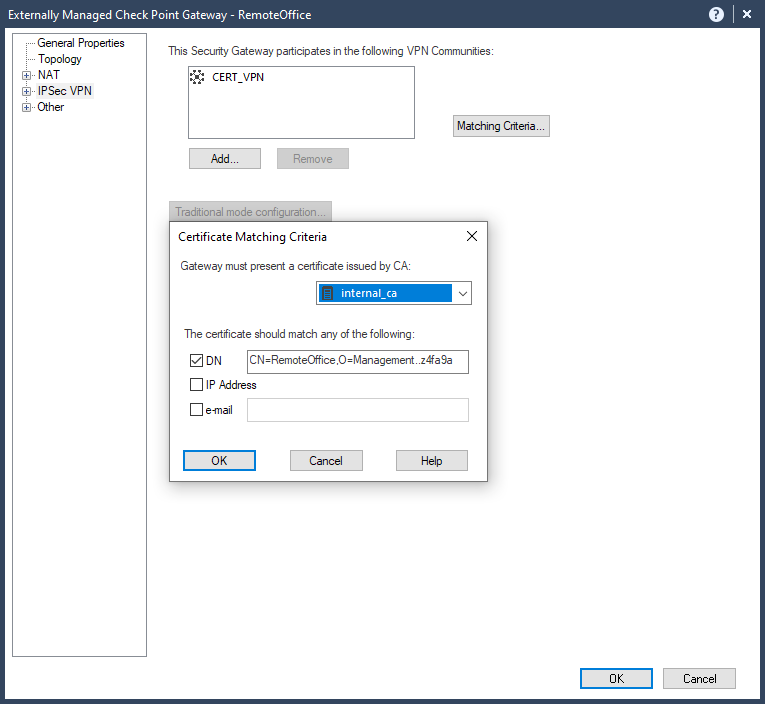
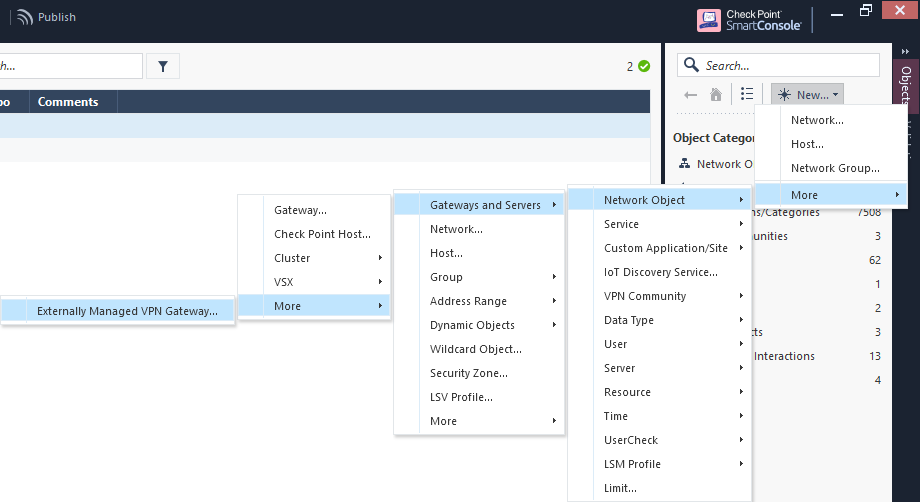
Now simply create an Externally Managed Check Point Gateway for our SMB appliance and you are all set up and done.
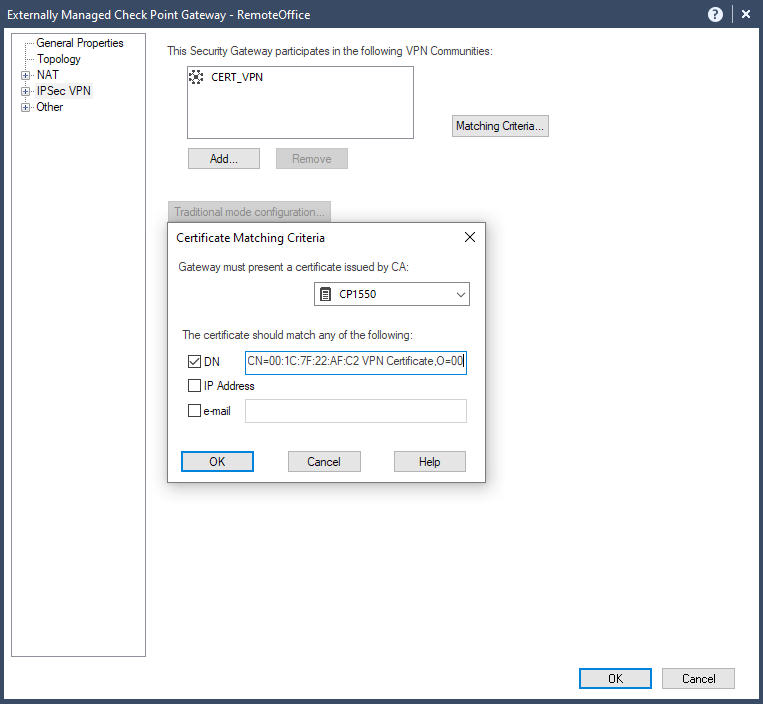
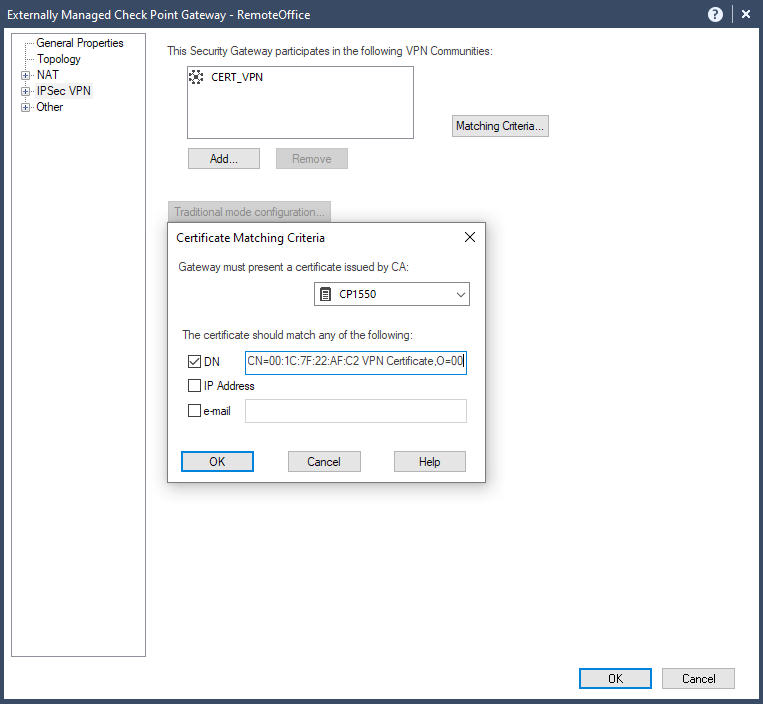
When configurating the Matching Criteria for our SMB appliance, check the DN box and paste the subject of our SMB appliance Default Certificate if you took Option A.
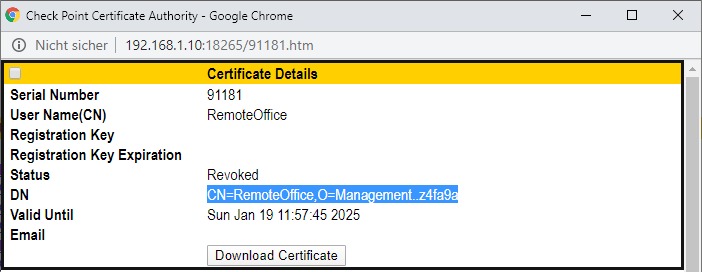
In case of Option B first copy the DN of the created certificate from within ICA Management Tool.
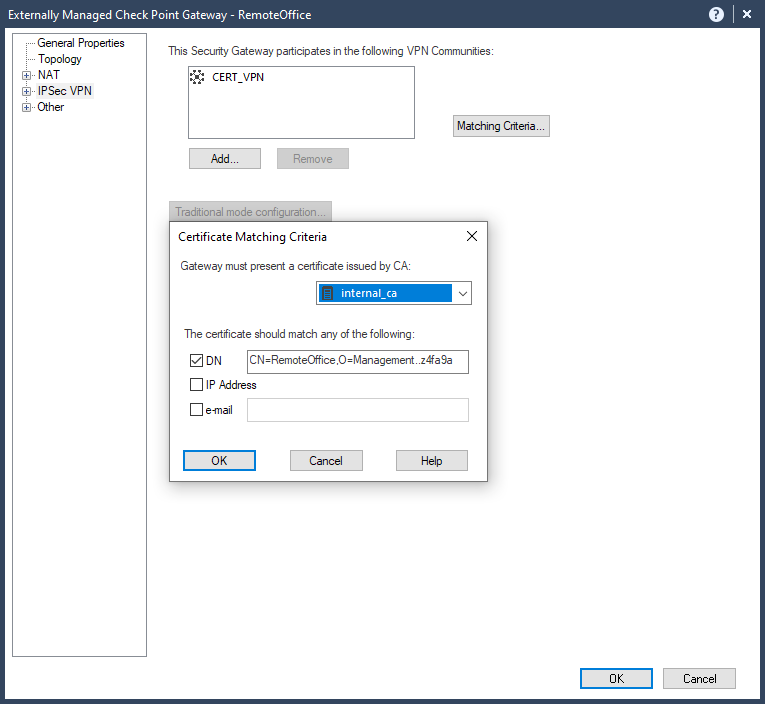
Then paste it into the DN field of the VPN certificate as issued by our internal_ca.
Install the security policy.

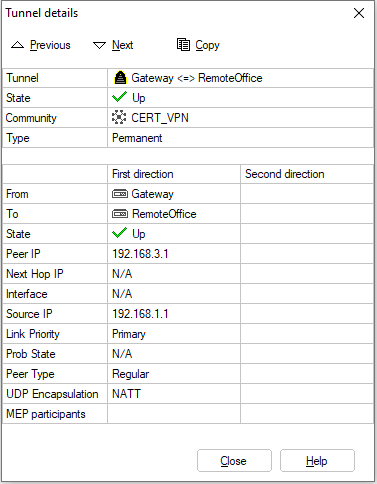
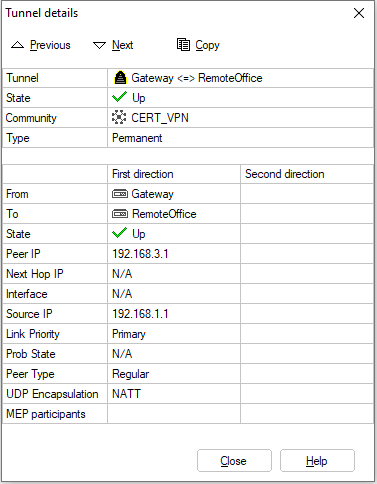
And check out the working VPN tunnel.
Special thanks to @Ziegelsambach , @Joshua and @jannag !
Thank you.