- Products
Quantum
Secure the Network IoT Protect Maestro Management OpenTelemetry/Skyline Remote Access VPN SD-WAN Security Gateways SmartMove Smart-1 Cloud SMB Gateways (Spark) Threat PreventionCloudGuard CloudMates
Secure the Cloud CNAPP Cloud Network Security CloudGuard - WAF CloudMates General Talking Cloud Podcast - Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Quantum (Secure the Network)
- CloudGuard CloudMates
- Harmony (Secure the Workspace)
- Infinity Core Services (Collaborative Security Operations & Services)
- Developers
- Check Point Trivia
- CheckMates Toolbox
- General Topics
- Infinity Portal
- Products Announcements
- Threat Prevention Blog
- CheckMates for Startups
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
Mastering Endpoint Security -
Best Practices for 2024
Check Point Named Leader
In Mobile Threat Defense
Regulatory Compliance Update
For Non-US DoC Versions
Customer Threat Prevention
& Vulnerability Management Survey
CheckMates Toolbox Contest 2024
Make Your Submission for a Chance to WIN up to $300 Gift Card!
CheckMates Go:
What's New in Quantum Spark
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Quantum
- :
- SMB Gateways (Spark)
- :
- Incorrect categorization of url filtering when use...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
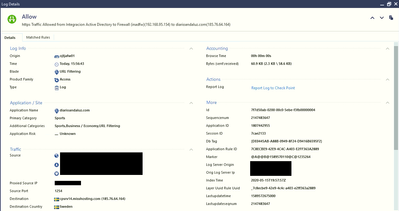
Incorrect categorization of url filtering when use Google Crhome
Hello and good morning
I have some problems with smb 1490
I don't know if anyone had the same problem or if it's a limitation of SMB 1400
When clients use the google chrome web browser for some web pages, checkpoint cant categorized correctly by checkpoint
Yes I have a rule that blocks all traffic that cannot be classified, but the problem is the incorrect categorization.
note : this happen in all SMB appliances(1400).
On the other hand, when the client uses firefox explorer in the same pages, these are correctly categorized after this if the client uses the google chrome explorer, again it is already correctly categorized by checkpoint.
to take into account that
1.- I don't have https inspection (resources problems) activated.
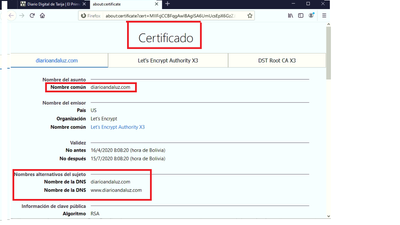
But I understand that it complies with Categorize HTTPS Websites via Certificate Checking.
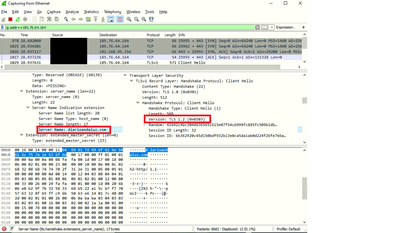
2.- the session is performed by the TLS1.2v on the clients.
3.- The SNI and the CN have the same name as the domain of the web page
4.- Google chrome and firefox are updated (also try old versions with the same result).
5.- The smb is centrally administered
6.- the management and the smb is update.
SMB 1400 R77.20.87 (990173004). Management R80.30 JH take 191
7.- Trusted Ca and blacklist is update .
Please if someone has any clue or knows what could be happening? or if a limitation of smb
Thanks for the help.
13 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
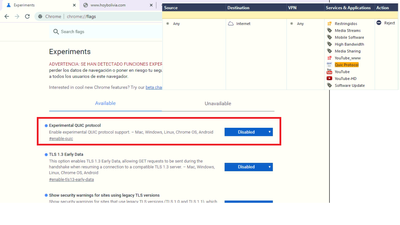
Are you blocking QUIC?
Just to note: we do not look at SNI at all on that SMB code release.
That capability was only added to R80.20.05, which is not available for the 1490 (but is on the newer 1500 series).
However, when I went to that site, the CN of the certificate looks correct, so we should see it.
Just to note: we do not look at SNI at all on that SMB code release.
That capability was only added to R80.20.05, which is not available for the 1490 (but is on the newer 1500 series).
However, when I went to that site, the CN of the certificate looks correct, so we should see it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello and ty for the help PhoneBoy
Are you blocking QUIC?
Yes te quic protocol is blooqued by the firewall and i try to block in the client too , but with the the same results .
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
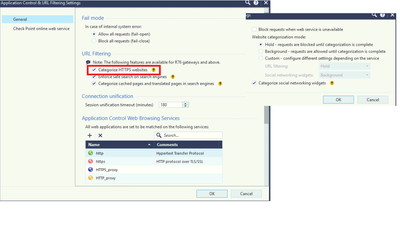
Try to set in SmartConsole, Manage & Settings -> Blades -> APPCL & URLF -> CheckPoint online web service -> Web categorization mode to "Hold" and see if that makes any difference in observed behavior.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
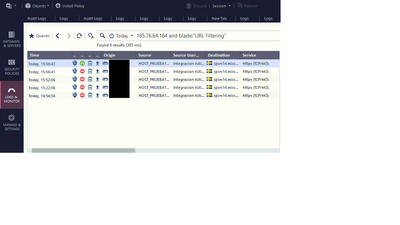
mm yes right now the mode of web categorization is in hold , but the problem persist , ty for the help HristoGrigorov(you can see it in the 4° photo).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
URL categorization is made in CheckPoint Cloud not on device itself. I think if for some reason it fails to do that it will threat it as uncategorized.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, but when the client uses firefox as a browser, it seems that checkpoint can correctly categorize it.
so it is a bit strange that with firefox checkpoint can categorize it.
so it is a bit strange that with firefox checkpoint can categorize it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Agree. It is worth involving TAC here.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
yes the tac is involved , but at the moment couldn't be determine what it could be, so I open this case in the community to find out if anyone may have had the same problem.
Any help is appreciated
Any help is appreciated
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May be sniff the traffic between Firefox and SMB and then between Chrome and SMB and compare it. Pay special attention to HTTP headers and what browser sends as requested URL.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Any progress with this? We are seeing the same thing
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We're running into the same thing with several sites (running on 15400 appliances R80.40) which started up a few days ago, we do block uncategorized sites. I haven't had time to sift through the logs on all the sites but several of them appear to be hosted on AWS. Even www.amazon.com shopping site which we permit gets blocked when it reaches the uncategorized AWS hosts.
Wonder if AWS added a new IP subnet that Checkpoint hasn't categorized yet?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello @charcris
Since when you're experiencing the issue?
Have you been able to access any of those websites before?
Have you tried to access the website via IP like this: https://185.76.64.164:443
Also can you tried to disable enforce safe search > install policy > clear cookies/cache on browser or open a private tab and share the results.
Hablo español cualquier cosa amigo!
Thanks!
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
After a lot of days of researchs I found a solution for this without enable HTTPS Inspection.
- On Network Layer - create a Drop rule for UDP 443 QUIC
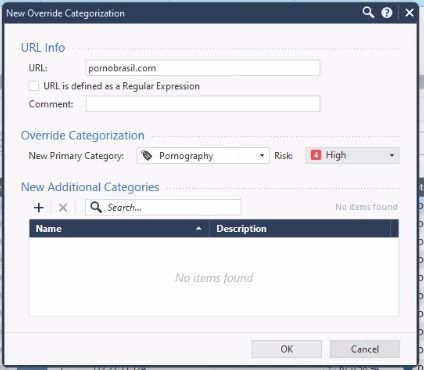
- On App control & URL Filtering layer - create a DROP rule for desired categories like Pornografy, Sex, Nudity ...
- And the final key for firewall Drop correctly the sites on this categories for Google Chrome create a object New Override Categorization - and set a Risk High or Critical, after that the firewall will Drop with more criteria and priority all sites classified on this categories that you create a New Override Categorization object. Set one site just to save the object, but important thing here will be the risk
From the Objects tab of SmartConsole, select New > More > Custom Application/Site > Override Categorization
Before applied this configuration a lot of porn sites oppening just on the Google Chrome, and on this customer don't was possible enable HTTPS Inspection, with this configurations was possible drop everything just with URL Filtering.
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 3 | |
| 3 | |
| 2 | |
| 2 | |
| 2 | |
| 1 | |
| 1 | |
| 1 | |
| 1 | |
| 1 |
Upcoming Events
Thu 25 Jul 2024 @ 11:00 AM (EDT)
CP Tips and Tricks 2024 #12: Dynamic Access Policies using Data Center ObjectsThu 01 Aug 2024 @ 10:00 AM (CEST)
CheckMates Live BeLux: What's new on Check Point CloudGuard!Tue 06 Aug 2024 @ 05:00 PM (CEST)
Americas CheckMates Live - Infinity XDR/XPR Q2 Product UpdatesThu 25 Jul 2024 @ 11:00 AM (EDT)
CP Tips and Tricks 2024 #12: Dynamic Access Policies using Data Center ObjectsThu 01 Aug 2024 @ 10:00 AM (CEST)
CheckMates Live BeLux: What's new on Check Point CloudGuard!Tue 06 Aug 2024 @ 05:00 PM (CEST)
Americas CheckMates Live - Infinity XDR/XPR Q2 Product UpdatesAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2024 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
About Us
UserCenter