For the AV/ABOT blades, the "Last Update" does not mean what you think it means when compared to something like the IPS blade. Check Point seems to be a bit cagey about what is going on with AV/ABOT updates and there is little documentation, but allow me to explain my understanding of this which granted may not be 100%:
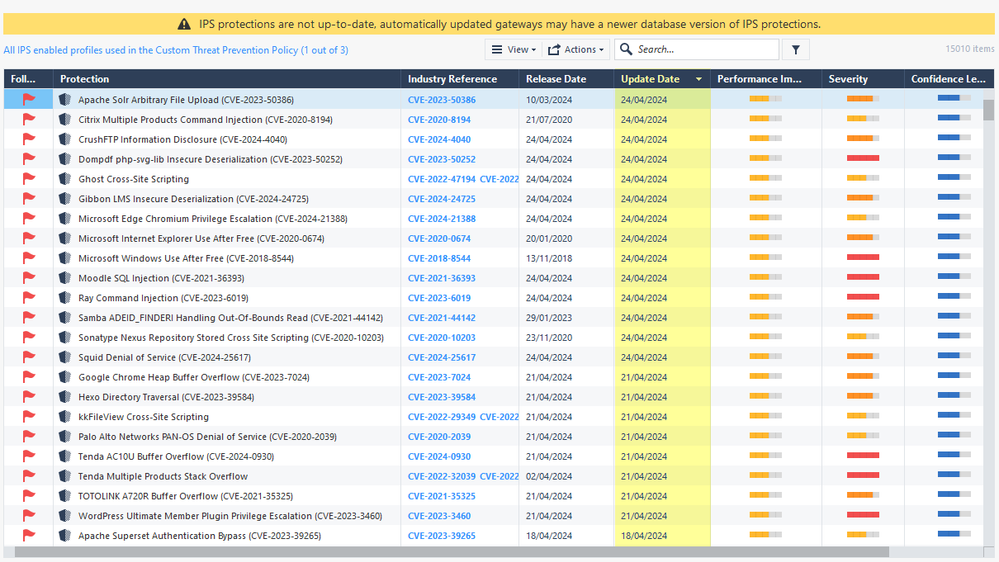
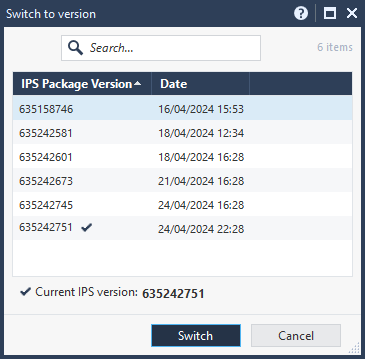
The IPS feature exclusively uses a traditional set of patterns/signatures that are downloaded in their entirety as one big database file, and once the database is downloaded and slipstreamed into the existing Threat Prevention policy on the gateway, the IPS blade operates 100% autonomously with no live interaction with the ThreatCloud needed for enforcement. However Anti-Virus and Anti-Bot use a combination of memory-based caches and constant interactions with the Check Point ThreatCloud via the rad process to help keep the caches populated.
Normally Check Point gateways will interact with the Check Point ThreatCloud servers with no consideration given to which countries those servers are actually located in. But interestingly it is possible to configure the gateway to only obtain ThreatCloud updates from Check Point servers located in certain countries and avoid undesirable countries; here are some interesting examples: sk168057: Restricting Threat Prevention Gateways to China (Geo-Restriction) & sk97877: Restricting Gateways to Send Files for Emulation only in a Specific Country (Threat Emulati...
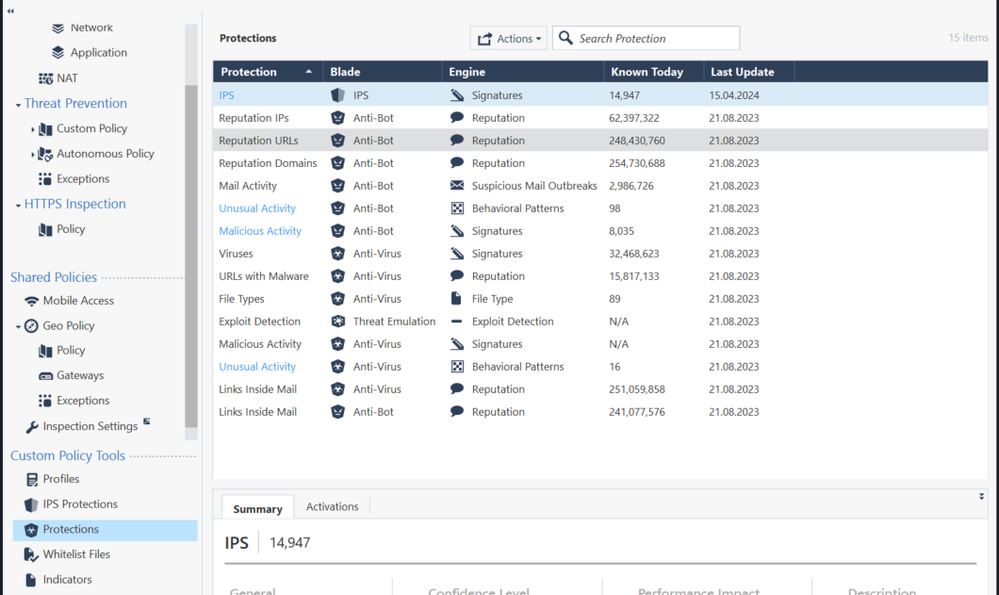
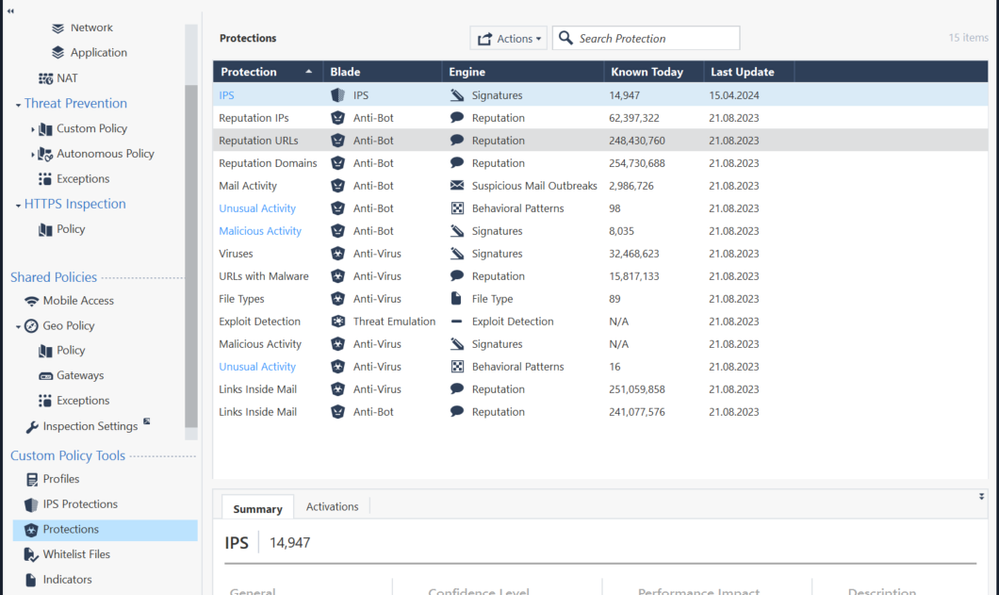
There really isn’t a big "database download" for all AV/ABOT-based protections like there is for IPS, but AV/ABOT do have a big signature database they download for a portion of their inspection duties, I believe this is the "Update Number" shown in cpview on the Software-blades...Overview screen and the Gateways & Servers tab of SmartConsole, but NOT on the "Protections" screen shown in your last post. While not clearly documented, the actual scanning engines employed by AV/ABOT can also be modified or enhanced by Check Point via these updates "on the fly" in response to new threats.
All of this will be covered in the upcoming Check Point Threat Prevention Specialist (CTPS) course that should be available worldwide from ATCs in Q3 2024.
New Book: "Max Power 2026" Coming Soon
Check Point Firewall Performance Optimization