Good day, CheckMates.
Does anyone here have experience with McAfee SIEM in consuming Check Point R80.30 Firewall logs over syslog? In this implementation, the event logs are sent to the SIEM via Check Point Log Exporter and not via OPSEC.
We followed this KB, https://kc.mcafee.com/corporate/index?page=content&id=KB91645&locale=en_US, particularly the 2nd workaround (i.e. Datasource Vendor = Generic and Datasource Model = Advanced Syslog Parser) and have had this configuration running for a while now.
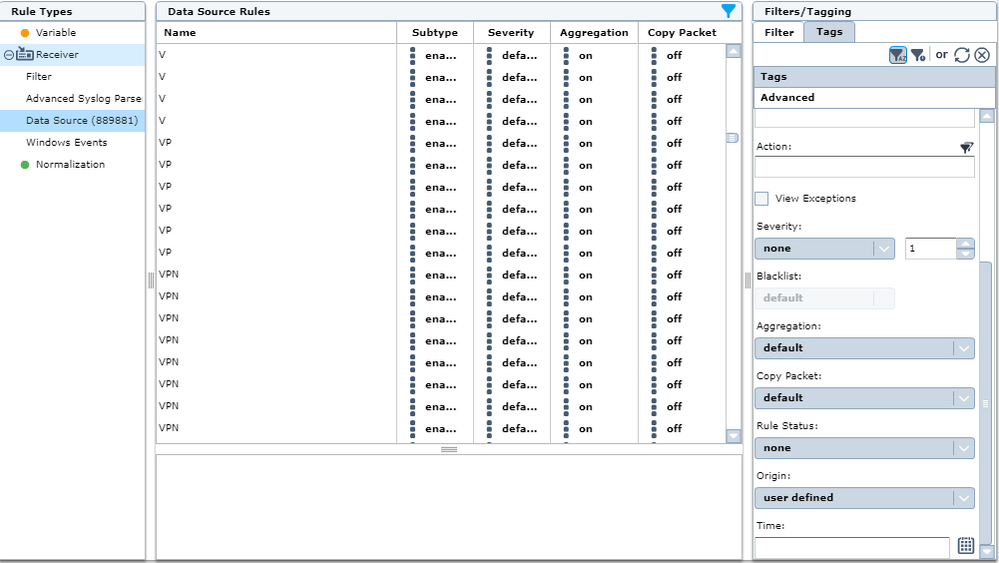
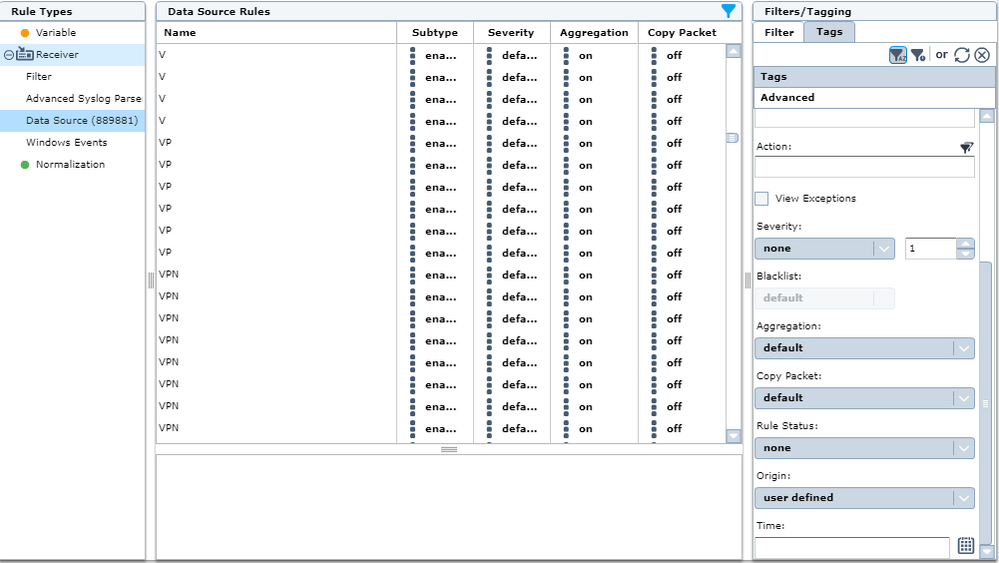
While events have been coming in regularly as expected, I just recently noticed that the number of auto-learned rules specific to Check Point have grown at an alarmingly huge rate--900K+ auto-learned rules as of this writing! This doesn't seem normal, especially since there's supposed to be a 25K limit of auto-learned rules per category. A number of these auto-learned rules are also duplicates and/or seem to be garbage. Refer to below policy screenshot from McAfee SIEM:
Based on what I've dug up so far, there are a number of Check Point events that seem to be causing this behaviour, particularly events where there are multiple values in the cu_dst, cu_proto, cu_service, cu_src fields. Below is a sample of such a packet (critical info changed):
<134>1 2021-01-30T06:36:45Z PROD-CPEVT01 CheckPoint 6645 - [flags:"16384"; ifdir:"inbound"; logid:"134217729"; loguid:"{0x5f6da62e,0x0,0xc69320a,0xa00001ad}"; origin:"10.x.x.5"; sequencenum:"1"; time:"1611988605"; version:"5"; action_repetitions:"9734 2"; cu_action:"drop reject"; cu_detected_by:"10.x.x.12"; cu_detection_time:"1611988605"; cu_dst:"10.x.1.11 10.x.1.12 10.x.1.12 10.x.15.59 10.x.250.5 10.x.52.50 10.x.52.52 10.x.52.53 10.x.52.58 10.x.52.9 10.x.104.14 10.x.202.50 10.x.212.50 10.x.212.51 10.x.213.51 117.x.232.240 117.x.237.29 150.x.20.12 161.x.226.18 161.x.226.26 161.x.226.28 192.x.27.100 192.x.27.101 192.x.81.16 192.x.88.104 192.x.89.16 192.x.16.1 192.x.16.10 192.x.16.103 192.x.16.104 192.x.16.105 192.x.16.108 192.x.16.109 192.x.16.11 192.x.16.110 192.x.16.113 192.x.16.114 192.x.16.117 192.x.16.120 192.x.16.122 192.x.16.123 192.x.16.124 192.x.16.125 192.x.16.127 192.x.16.129 192.x.16.131 192.x.16.132 192.x.16.133 192.x.16.136 192.x.16.137 192.x.16.139 192.x.16.140 192.x.16.141 192.x.16.142 192.x.16.143 192.x.16.144 192.x.16.145 192.x.16.146 192.x.16.151 192.x.16.152 192.x.16.153 192.x.16.154 192.x.16.156 192.x.16.158 192.x.16.159 192.x.16.16 192.x.16.160 192.x.16.162 192.x.16.163 192.x.16.164 192.x.16.167 192.x.16.170 192.x.16.171 192.x.16.172 192.x.16.177 192.x.16.18 192.x.16.180 192.x.16.183 192.x.16.184 192.x.16.186 192.x.16.189 192.x.16.190 192.x.16.191 192.x.16.192 192.x.16.194 192.x.16.195 192.x.16.196 192.x.16.197 192.x.16.199 192.x.16.20 192.x.16.201 192.x.16.202 192.x.16.203 192.x.16.206 192.x.16.207 192.x.16.210 192.x.16.211 192.x.16.212 192.x.16.213 192.x.16.214 192.x.16.217 192.x.16.219 192.x.16.22 192.x.16.220 192.x.16.222 192.x.16.224 192.x.16.225 192.x.16.227 192.x.16.228 192.x.16.229 192.x.16.23 192.x.16.231 192.x.16.234 192.x.16.235 192.x.16.238 192.x.16.24 192.x.16.25 192.x.16.252 192.x.16.254 192.x.16.3 192.x.16.30 192.x.16.32 192.x.16.34 192.x.16.35 192.x.16.36 192.x.16.41 192.x.16.42 192.x.16.43 192.x.16.44 192.x.16.45 192.x.16.46 192.x.16.47 192.x.16.53 192.x.16.54 192.x.16.55 192.x.16.56 192.x.16.59 192.x.16.6 192.x.16.60 192.x.16.61 192.x.16.63 192.x.16.65 192.x.16.66 192.x.16.7 192.x.16.72 192.x.16.73 192.x.16.75 192.x.16.77 192.x.16.81 192.x.16.83 192.x.16.85 192.x.16.87 192.x.16.89 192.x.16.9 192.x.16.90 192.x.16.92 192.x.16.93 192.x.16.95 192.x.16.97 192.x.16.98 192.x.16.99 192.x.17.1 192.x.17.100 192.x.17.101 192.x.17.107 192.x.17.109 192.x.17.11 192.x.17.113 192.x.17.114 192.x.17.115 192.x.17.118 192.x.17.119 192.x.17.12 192.x.17.121 192.x.17.123 192.x.17.129 192.x.17.13 192.x.17.130 192.x.17.133 192.x.17.135 192.x.17.137 192.x.17.139 192.x.17.140 192.x.17.147 192.x.17.150 192.x.17.152 192.x.17.157 192.x.17.158 192.x.17.159 192.x.17.16 192.x.17.160 192.x.17.163 192.x.17.164 192.x.17.17 192.x.17.170 192.x.17.179 192.x.17.18 192.x.17.180 192.x.17.181 192.x.17.185 192.x.17.186 192.x.17.187 192.x.17.189 192.x.17.190 192.x.17.192 192.x.17.193 192.x.17.194 192.x.17.195 192.x.17.196 192.x.17.197 192.x.17.198 192.x.17.200 192.x.17.202 192.x.17.204 192.x.17.205 192.x.17.206 192.x.17.207 192.x.17.208 192.x.17.21 192.x.17.210 192.x.17.211 192.x.17.212 192.x.17.213 192.x.17.214 192.x.17.216 192.x.17.218 192.x.17.219 192.x.17.22 192.x.17.222 192.x.17.223 192.x.17.229 192.x.17.231 192.x.17.232 192.x.17.237 192.x.17.243 192.x.17.246 192.x.17.247 192.x.17.252 192.x.17.253 192.x.17.254 192.x.17.255 192.x.17.29 192.x.17.3 192.x.17.30 192.x.17.36 192.x.17.38 192.x.17.42 192.x.17.46 192.x.17.47 192.x.17.50 192.x.17.52 192.x.17.55 192.x.17.59 192.x.17.64 192.x.17.65 192.x.17.67 192.x.17.7 192.x.17.71 192.x.17.73 192.x.17.75 192.x.17.79 192.x.17.83 192.x.17.88 192.x.17.9 192.x.17.90 192.x.17.91 192.x.17.92 192.x.17.93 192.x.17.94 192.x.17.95 192.x.17.96 192.x.17.98 192.x.17.99 192.x.23.0 192.x.23.100 192.x.23.101 192.x.23.102 192.x.23.103 192.x.23.105 192.x.23.106 192.x.23.107 192.x.23.108 192.x.23.109 192.x.23.110 192.x.23.113 192.x.23.114 192.x.23.115 192.x.23.116 192.x.23.117 192.x.23.118 192.x.23.119 192.x.23.12 192.x.23.120 192.x.23.122 192.x.23.124 192.x.23.125 192.x.23.127 192.x.23.129 192.x.23.13 192.x.23.134 192.x.23.137 192.x.23.138 192.x.23.139 192.x.23.140 192.x.23.144 192.x.23.146 192.x.23.147 192.x.23.148 192.x.23.150 192.x.23.152 192.x.23.153 192.x.23.154 192.x.23.156 192.x.23.158 192.x.23.159 192.x.23.16 192.x.23.160 192.x.23.161 192.x.23.162 192.x.23.163 192.x.23.165 192.x.23.166 192.x.23.167 192.x.23.169 192.x.23.170 192.x.23.174 192.x.23.177 192.x.23.178 192.x.23.179 192.x.23.18 192.x.23.180 192.x.23.181 192.x.23.182 192.x.23.185 192.x.23.187 192.x.23.195 192.x.23.196 192.x.23.200 192.x.23.202 192.x.23.205 192.x.23.211 192.x.23.212 192.x.23.214 192.x.23.216 192.x.23.22 192.x.23.220 192.x.23.224 192.x.23.225 192.x.23.227 192.x.23.228 192.x.23.230 192.x.23.231 192.x.23.232 192.x.23.234 192.x.23.236 192.x.23.24 192.x.23.240 192.x.23.241 192.x.23.242 192.x.23.244 192.x.23.247 192.x.23.248 192.x.23.249 192.x.23.25 192.x.23.250 192.x.23.252 192.x.23.254 192.x.23.255 192.x.23.27 192.x.23.29 192.x.23.3 192.x.23.30 192.x.23.31 192.x.23.32 192.x.23.33 192.x.23.34 192.x.23.36 192.x.23.39 192.x.23.4 192.x.23.42 192.x.23.5 192.x.23.53 192.x.23.54 192.x.23.57 192.x.23.58 192.x.23.60 192.x.23.61 192.x.23.62 192.x.23.64 192.x.23.66 192.x.23.68 192.x.23.73 192.x.23.74 192.x.23.75 192.x.23.78 192.x.23.80 192.x.23.81 192.x.23.82 192.x.23.84 192.x.23.85 192.x.23.89 192.x.23.90 192.x.23.91 192.x.23.92 192.x.23.93 192.x.23.94 192.x.23.96 192.x.23.97 192.x.23.98 192.x.232.240 35.x.60.223 35.x.235.110 40.x.108.123 52.x.64.147 52.x.226.0"; cu_last_update_time:"1611988605"; cu_log_count:"1062230038"; cu_proto:"6 6 6 6 17 17 1 6 6 17 6 6 17 6 6 17 6 17 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 17 17 6 6 17 6 6 6 6 6 6 17 6 17 17 6 17 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6 17 6 17 6 6 6 6 6 6 6 6 6 6 6 6 6 6 6"; cu_rule_category:"Denial Of Service"; cu_rule_id:"{EF274D01-EBFC-9f88-AC63-841056002777}"; cu_service:"1024 1026 1080 110 111 123 1311 135 137 143 1433 1434 1521 16010 161 179 19 1911 2000 20000 2082 21 22 2222 23 2323 2428 25 3052 3128 3306 33389 3389 3390 40000 443 4431 4443 445 44818 4567 47545 47808 4786 49152 49366 49502 502 5060 5061 50995 51005 5246 52869 53 53213 53480 5353 554 5555 587 5900 5901 5902 5904 5984 5985 60000 623 6443 68 7001 7011 7547 7680 80 8000 8001 8002 8003 8004 8005 8008 8072 8080 8081 8081 8082 8085 8088 8089 81 8165 8181 82 8443 8686 8888 9166 9200 9443 9600 990"; cu_src:"10.49.65.80 10.x.10.30 10.x.16.145 10.x.16.147 10.x.16.183 10.x.20.195 10.x.20.41 10.x.201.168 10.x.201.237 10.x.202.124 10.x.202.128 10.x.202.131 10.x.202.144 10.x.202.162 10.x.202.175 10.x.202.18 10.x.202.193 10.x.202.204 10.x.202.208 10.x.202.25 10.x.203.228 10.x.203.238 10.x.204.112 10.x.204.133 10.x.204.140 10.x.204.152 10.x.204.228 10.x.204.64 10.x.204.81 10.x.x.12 10.x.x.28 10.x.x.40 10.x.x.48 10.x.x.52 10.x.16.147 10.x.11.13 10.x.8.190 10.x.8.81 10.x.8.82 122.228.19.80 134.209.35.77 144.217.34.148 162.x.125.17 162.x.125.27 162.x.125.31 162.x.125.66 162.x.125.73 162.x.125.76 167.x.133.16 167.x.133.18 167.x.133.31 167.x.133.64 172.x.207.40 192.x.131.32 192.x.16.131 192.x.17.4 192.x.17.68 192.x.23.227 192.x.23.228 192.x.23.3 192.x.23.35 192.x.23.36 192.x.23.67 192.x.23.99 192.x.25.132 192.x.25.196 192.35.x.184 216.x.206.113 218.x.235.5 69.x.59.30 71.x.135.131 71.x.199.23 74.x.14.24 74.x.14.30 74.x.14.31 74.x.14.64 74.x.14.74 80.x.126.199 80.x.77.33 83.x.20.31 83.x.20.35 89.x.160.178 92.x.160.21 92.x.161.21 92.x.161.37"; destination_repetitions:"14 12 12 1 7 7 10 8 8 4 44 8 6 8 8 139 28 11 3 1 2 23 14 18 32 2 3 8 1 4 4 1 3 3 2 4 1 3 2 5 2 6 2 3 3 11 18 2 6 2 4 4 3 2 2 3 5 1 1 7 3 2 4 3 3 3 2 5 5 20 1 2 2 3 3 2 3 1 2 3 5 3 1 3 3 10 8 1 3 1 2 2 2 3 1 1 3 4 1 3 2 3 4 2 4 2 1 112 6 4 3 1 2 3 3 3 3 5 9 11 3 4 7 9 7 2 1 5 2 2 5 4 3 2 3 3 1 3 3 3 2 3 3 1 1 4 5 3 6 5 5 3 3 3 3 3 3 3 3 7 4 2 16 3 1 3 3 2 4 4 3 3 3 2 4 3 2 3 2 17 2 1 3 3 3 3 2 2 3 1 3 13 12 3 3 3 2 4 2 2 2 4 6 2 1 3 4 7 2 1 5 1 3 2 2 2 5 6 1 3 4 3 3 4 3 2 3 1 2 3 4 4 4 4 4 3 2 1 2 2 1 5 9 4 19 2 1 2 3 2 4 3 2 1 2 21 11 4 2 3 2 2 1 4 6 3 1 3 1 2 4 8 12 9 3 3 5 2 2 5 3 2 1 3 3 4 2 1 4 5 4 7 3 4 3 2 1 1 2 2 4 4 2 2 6 2 4 4 4 2 1 2 1 3 4 5 3 3 2 12 2 4 2 1 1 2 2 1 3 3 7 2 2 4 1 26 33 5 4 3 3 6 4 3 1 4 2 1 5 9 2 1 3 3 2 3 1 2 4 3 5 1 4 5 3 3 3 1 3 4 27 4 4 4 5 7 22 6 15 5 5 2 5 2 2 11 3 5 4 5 27 4 4 3 1 4 2 1 5 3 2 8 5 2 5 4 2 3 2 59 3 3 2 6 5"; domain:"SMC User"; event_name:"High rate of blocked connections"; event_start_time:"1601021446"; is_correlated:"1"; is_last:"0"; log_id:"2000"; max_num_count_detected:"243302"; num_of_updates:"179779"; origin_repetitions:"9736"; origin_sic_name:"CN=PROD-CPGW01,O=PROD-CPMGT01.domain.com.qfo6o5"; product:"VPN-1 & FireWall-1"; service_repetitions:"1 1 3 3 6 11 19 2 16 48 2 30 5 1 3 65 4 2 1 2 4 3 1 33 7 191 36 36 1 2 1 1 1 21 2 1 5721 1 2 111 4 4 100 1 1 2 5 2 1 1 4 1 1 125 1 8 24 1 4 4 10 3 1 2 3 1 2 1 4 2 1 1 15 16 2 5 810 24 10 8 2 1 5 3 23 43 3 1 2 1 2 3 56 32 10 1 5 2 3 1 1 1 1 1"; source_repetitions:"8 39 2 8 9 2 39 7 8 8 7 8 8 7 6 6 7 7 6 7 8 8 6 7 7 7 8 5 6 8 7 8 7 8 10 11 3 30 19 2 2 1 2 2 1 1 1 1 2 1 1 1 1 32 3 2 5 5 9 1 6 11 2 10 3 4 1 1 3 4 1 2 3 1 2 2 1 2 2 12 8 43 1 1 1"; time_interval:"60"; ]
I have escalated this to McAfee SIEM Support and this is what they came back with:
"Once parsed the Field Assignment defines how we produce the Rule message. What happens is we will parse a signature id and a signature name.
The signature id is looked up in the datasource rules, if there is an existing one then we use the rule message for the existing datasource rule. If there is no datasource rule then one is created using the rule message from the log.
Looking at the parsing for this, we are expecting to find a "rule name" field but because we do not, we then put together "product+protocol+action" to create a dynamic rule message. I think due to the length of the events we are truncating and at some point we parsed just "V" as in the first letter of the product as the rule message - from then onwards everything that looks vaguely similar gets the same poor rule message."
I already have an open Service Request with McAfee to investigate this further, but I am also curious as to why Check Point is sending such events in the first place.
Does anybody have a clue as to what is going here exactly and whether this is a legitimate event, or whether there is something we need to change in the Firewall and/or Log Exporter to prevent this from happening?
Thanks and looking forward to your feedback!