Hi All,
This is my first post so forgive me if I am in the wrong area.
I help support a small data center that has a small Check Point environment. We have 2 Smart-1 225s configured as HA managers. They managed two 12600 Secure Gateways that are configured as a VSX cluster. The environment is on R77.30 Take 351 and we would like to upgrade it to R80.40. My understanding is that the 12600s only support R80.40. Yes, this upgrade is long overdue. This will be an in place upgrade on the existing appliances.
I would like to approach the upgrade in two phases. The first phase being to upgrade the managers to R80.40 and leave the VSX cluster/Gateways on R77.30. I would like to run in this configuration for a period of time to ensure that the managers are stable.
The second phase would be to upgrade the VSX Cluster/Gateways at a later time.
I was looking over the R80.40 Installation and Upgrade Guide and have some questions I would like to bounce off the community for guidance and opinion. The revision of the guide is dated January 2022. Some of these questions may have straightforward answers, others may be more complex.
At any rate in no particular order.
The guide mentions additional steps and considerations for dedicated End Point Servers, Smart Event Servers, Dedicated Logs servers and so forth. I am pretty confident I do not have any dedicated servers. Is there any configuration I can check to be sure of this?
In addition to performing snapshots and backups on each Check Point appliance, should I also perform a migrate export? I suspect I should and if so, do I only need to do this on the Active Smart-1 225 manager or from both managers?
On page 167 of the Upgrade and Installation Guide there is a recommendation of making an explicit firewall rule for Smart Console if that traffic goes through an R77 gateway. I am pretty confident I do not need to do this since my workstation running Smart Console does not traverse a network path that goes through a VS or Gateway. Just looking for more insight to this action from the Guide.
On page 168, the procedure for HA Manager environment states to upgrade the primary active manager and then doing a clean install on the secondary manager and the to connect the secondary manager to the primary manager. This particular procedure really gives me concern. Wouldn't I just use CPUSE to upgrade the primary manager first then do the same for the secondar standby manager? I am especially interested in feedback to this question.
On page 176, there are mobile access prerequisites listed. I am curious if these apply to the manager or gateways or both. We do use the SSL extender in our environment with 2FA via SMS. I confess I am not overly familiar with how this was set up, but I do know it involves using an SMSPhones file in the $CVPNDIR/conf directory on the VS in our VSX cluster that we use for VPN access into the data center. I believe there was also some modifications made using the DB Editor as well to create linkage between Active Directory to the SMSPhones file. I am curious if the SMSPhones file along with the DB changes that were made will be overwritten during the upgrade and what steps I should take to protect the configuration changes that were made to make our VPN 2FA functionality work.
On page 176 there is also mention of Mobile Endpoint Compliance Security updates. Do these apply to me or how can I tell if this applies to me and what actions do I possibly need to take?
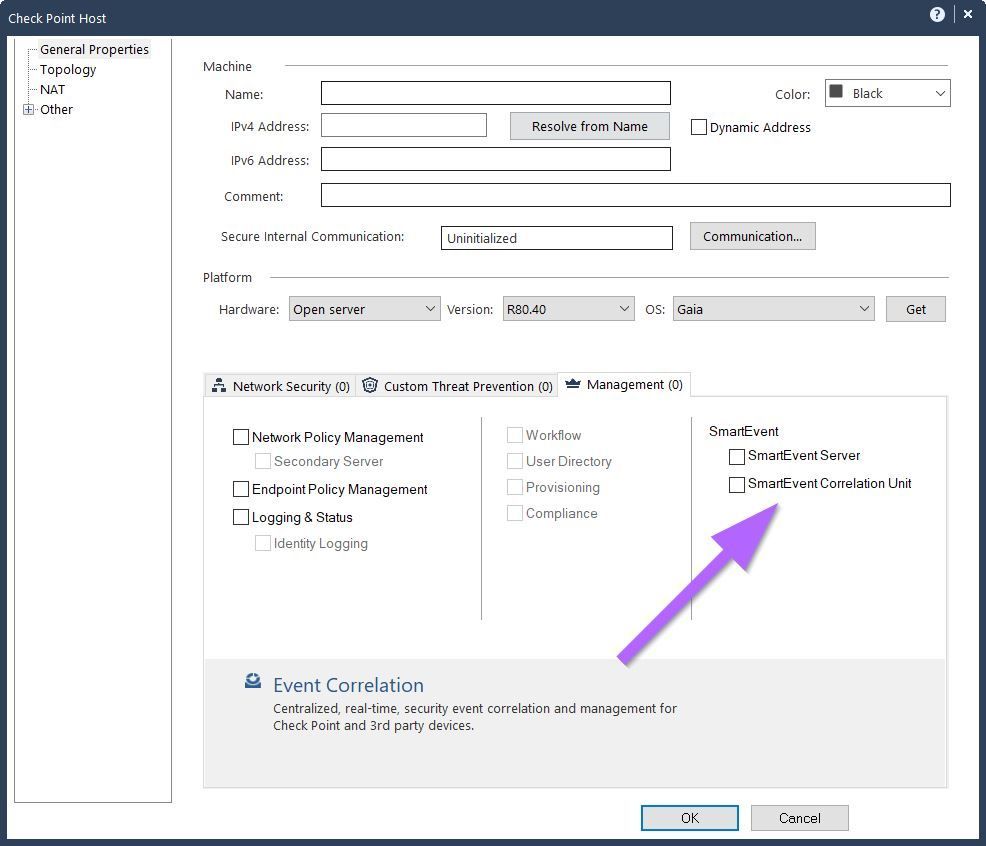
On page 191 there is mention of a Smart Correlation Blade? I do not think I have one of these but how do I verify to be sure?
When I ran the Pre Upgrade Verification Tool on the active manager, the report produced a warning regarding DHCP Legacy vs New handling and referenced sk104114 . After doing some research it appears that DHCP is handled differently by default if the gateways are running R77 vs R80. R77 uses Legacy handling and R80 uses New handling. Thee aforementioned sk details how to configure gateways on R77 to use New DHCP handling. I have identified a custom made Service Object in my Policy we made that includes legacy DHCP services. The aforementioned sk is fairly complex and I am curious as to what I should or should not do for the time being if I continue to run the VSX cluster on R77 and the managers on R80.40.
After both managers are upgraded to R80.40, what steps beyond what is described in the guide should I take to confirm that I can push, and mange polices on the R77.30 VSX Cluster members?
Lastly, if things go poorly when upgrading the managers from R77.30 to R80.40 and I need to fall back on one or both managers, how do I do this? Is reverting back to the snapshot I make prior to the upgrade all I need to do or is there more involved. The Installation and Upgrade guide does not actually have a process for fallback even though it does mention making snapshots and backups. Also, the sk articles that are referenced at least to me do not also give a clear fallback procedure.
I appreciate any feedback that anyone has on the questions. Also, if there is any other advice or thoughts on performing this upgrade, I would appreciate it.
Thank you.