- Products
- Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- Bulgaria
- Cyprus
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
AI Security Masters E7:
How CPR Broke ChatGPT's Isolation and What It Means for You
Call For Papers
Your Expertise. Our Stage
Good, Better, Best:
Prioritizing Defenses Against Credential Abuse
Ink Dragon: A Major Nation-State Campaign
Watch HereCheckMates Go:
CheckMates Fest
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Hybrid Mesh
- :
- Firewall and Security Management
- :
- Re: After a while VPN is going down
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
After a while VPN is going down
Hi Mates,
We have recently established an S2S VPN connection between Checkpoint and Barracuda FW. They are able to communicate effectively over this VPN. However, when a remote desktop connection is initiated between the two sites, after 10-15 minutes, the S2S VPN is automatically reset, and the tunnel is established again. As a result, the RDP connection is lost. Upon examining the logs, I discovered that when the connection is lost, the other site sends a "delete SA" message, which causes the tunnel to reset. What might be causing the tunnel to reset and how we can fixthis issue?
Thanks
20 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How's is the encryption domain currently configured?
Refer also:
sk142355 - keep_IKE_SAs
sk108600 - Scenario 4
CCSM R77/R80/ELITE
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
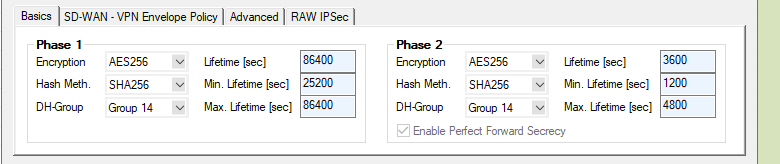
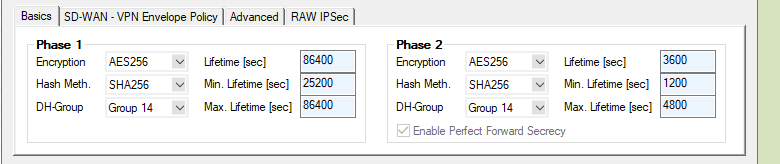
IKEv1
Phase 1
AES-256
SHA-256
Group 14
Renegotiate : 86400 sec
Phase 2
AES-256
SHA-256
Renegotiate : 3600 sec
Group 14
Perfect Forward Secrecy is enabled
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
log says after a while, when the tunnel went down --> Informational Exchange Received Delete IPSEC-SA from Peer: 3.party external IP.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Your IKE Phase 1 and Phase 2 timers do not match on both sides. The tunnel will start even though they don't match and you will see behavior like this. Unfortunately Check Point chose to express the Phase 1 timer in minutes and the Phase 2 timers in seconds, while most other vendors express both values in seconds so double-check that they really match on both sides.
New Book: "Max Power 2026" Coming Soon
Check Point Firewall Performance Optimization
Check Point Firewall Performance Optimization
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Second that.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Actually Phase 1 and Phase 2 timers match. But it is interesting, on barracude site there is max and min life time options. Normal lifetime options already match. But min/max lifetime is different. You can see in the attachment.
And also one point, After I reset the vpn, before tunnel goes up, fw received a message from other site, that "Quick Mode received Notification Peer: Invalid payload type" and " Payload malformed". But then vpn goes up, while vpn up in 30 min tunnel is resetted automatically.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Make sure option for "keep ike SAs" in global properties is checked as @Chris_Atkinson mentioned. I cant open the attachment from your last response, but not 100% certain what those timers options would equate to on CP side.
Best,
Andy
"Have a great day and if its not, change it"
Andy
"Have a great day and if its not, change it"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Keep ike SA is already checked in global properties. Following picture is from other site. Barracuda.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I cant find any timer settings on VPN community except under advanced tab in community itself (Im sure thats been like that for the last 25 years with CP vpn), but I did find below. Not sure this would help you, but I agree with @Timothy_Hall
Andy
Best,
Andy
"Have a great day and if its not, change it"
Andy
"Have a great day and if its not, change it"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Set Min, Max, and Lifetime to the same value on the Barracuda matching the Check Point timers. Anything that brings down the tunnel early (idle time, data lifesize) in an interoperable scenario will hang the tunnel and produce the behavior you are experiencing.
New Book: "Max Power 2026" Coming Soon
Check Point Firewall Performance Optimization
Check Point Firewall Performance Optimization
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,
I am having a problem with an S2S VPN with a third party, where every 4 to 5 hours, the tunnel goes down.
I have several other tunnels with other clients that are working fine.
Could this be a problem with the remote peer at the PUBLIC IP level?
Is there a command that can help me validate the negotiation, perhaps with tcpdump or cppcap?
Thank you.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Any relevant logs you can send?
Best,
Andy
"Have a great day and if its not, change it"
Andy
"Have a great day and if its not, change it"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
So does not like something with phase 2...just wondering, how is tunnel management configured? per subnet. gw, host?
Best,
Andy
"Have a great day and if its not, change it"
Andy
"Have a great day and if its not, change it"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Per Subnet ....
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Route based, domain based? Permanent tunnel?
Best,
Andy
"Have a great day and if its not, change it"
Andy
"Have a great day and if its not, change it"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It is domain-based.
The resources behind the remote pair are IPs with /32, but on my side, I have /24.
Is it necessary to set it per host?
The permanent tunnel is enabled.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
From my experience, when you have comination of hosts and subnets, per gateway is the right option.
Best,
Andy
"Have a great day and if its not, change it"
Andy
"Have a great day and if its not, change it"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sorry, my mistake.
Permanent tunneling is disabled.
But I don't think that's the problem because most of my other VPNs work fine.
So in scenarios where HOST vs SUBNET are combined, is it better to set “per GW”?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Might be worth enabling permanet tunnel option and yes, per gw should be set in your case. What is the other side?
Best,
Andy
"Have a great day and if its not, change it"
Andy
"Have a great day and if its not, change it"
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 64 | |
| 23 | |
| 13 | |
| 12 | |
| 11 | |
| 9 | |
| 8 | |
| 7 | |
| 7 | |
| 7 |
Upcoming Events
Tue 21 Apr 2026 @ 05:00 PM (IDT)
AI Security Masters E7: How CPR Broke ChatGPT's Isolation and What It Means for YouTue 28 Apr 2026 @ 06:00 PM (IDT)
Under the Hood: Securing your GenAI-enabled Web Applications with Check Point WAFTue 21 Apr 2026 @ 05:00 PM (IDT)
AI Security Masters E7: How CPR Broke ChatGPT's Isolation and What It Means for YouTue 28 Apr 2026 @ 06:00 PM (IDT)
Under the Hood: Securing your GenAI-enabled Web Applications with Check Point WAFTue 12 May 2026 @ 10:00 AM (CEST)
The Cloud Architects Series: Check Point Cloud Firewall delivered as a serviceThu 30 Apr 2026 @ 03:00 PM (PDT)
Hillsboro, OR: Securing The AI Transformation and Exposure ManagementAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2026 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
About Us
UserCenter