- Products
- Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- Bulgaria
- Cyprus
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
AI Security Masters E7:
How CPR Broke ChatGPT's Isolation and What It Means for You
Blueprint Architecture for Securing
The AI Factory & AI Data Center
Call For Papers
Your Expertise. Our Stage
Good, Better, Best:
Prioritizing Defenses Against Credential Abuse
Ink Dragon: A Major Nation-State Campaign
Watch HereCheckMates Go:
CheckMates Fest
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Hybrid Mesh
- :
- Firewall and Security Management
- :
- Exclude Windows updates from Threat Emulation
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
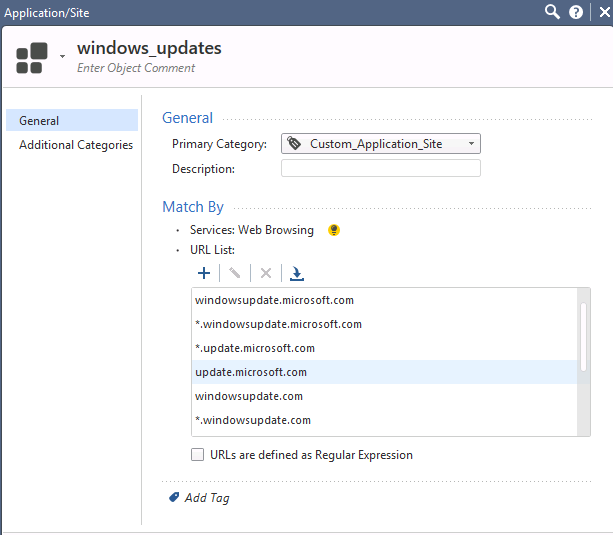
Exclude Windows updates from Threat Emulation
Hello Guys,
What approaches do you use to exclude multitude of .cab files which are part of Windows and Office updates from Threat Emulation without blocking all the .cab files in general?
I tried to add a global exception to threat prevention policy based on sites (*.windowsupdate.com and etc), but it seems to me it does not work.
I am very curious about best practises regarding this issue.
Thanks in advance.
14 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How exactly are you adding the exclusion?
Can you post a screenshot or two?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
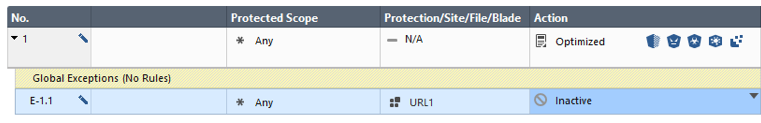
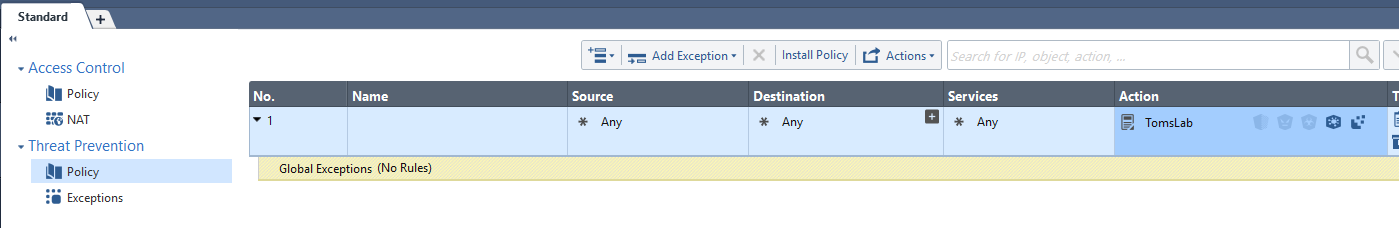
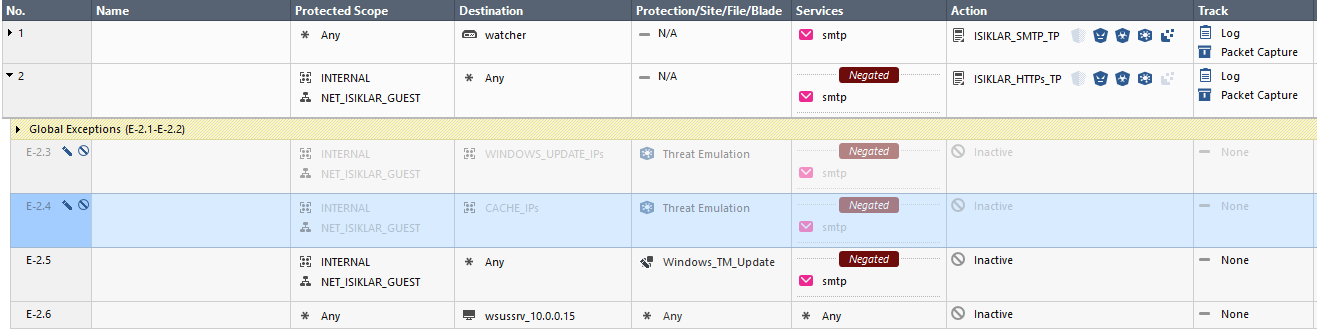
In Global Exceptions:

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Philipp,
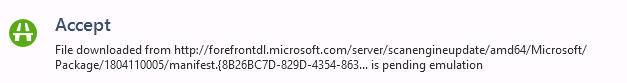
MS updates are usually excluded by our own whitelisting database.
Please check the according TE log and validate if you see "Trusted Source" in the details.
If so these files bypassed TE already without emulation.
Regards Thomas
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
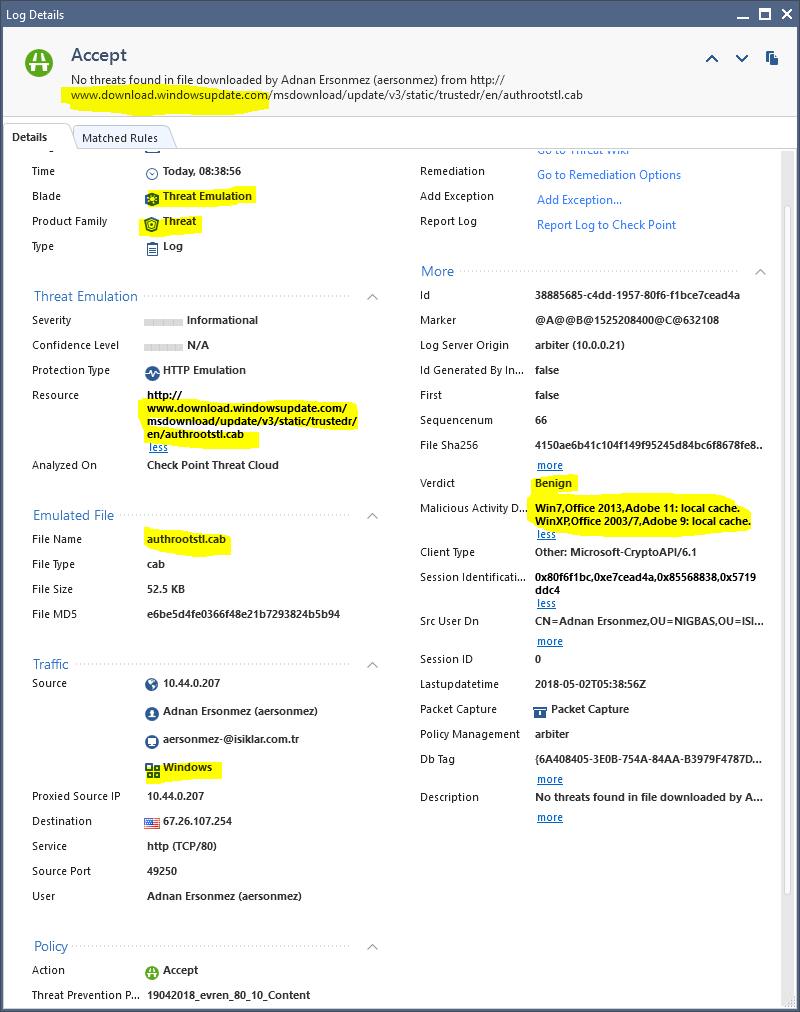
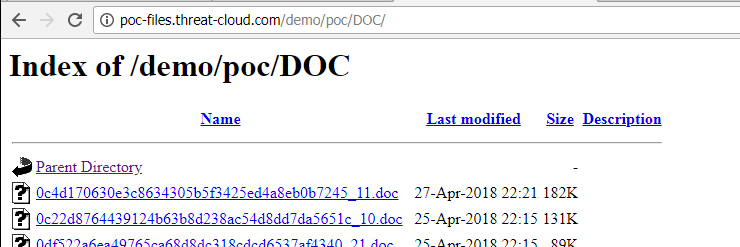
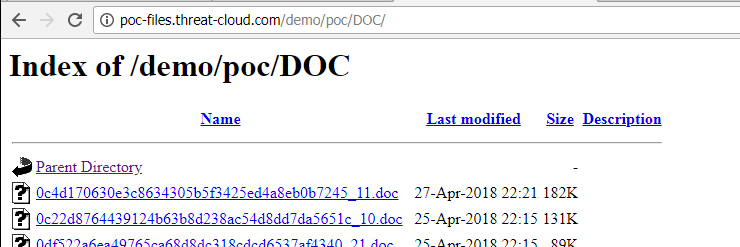
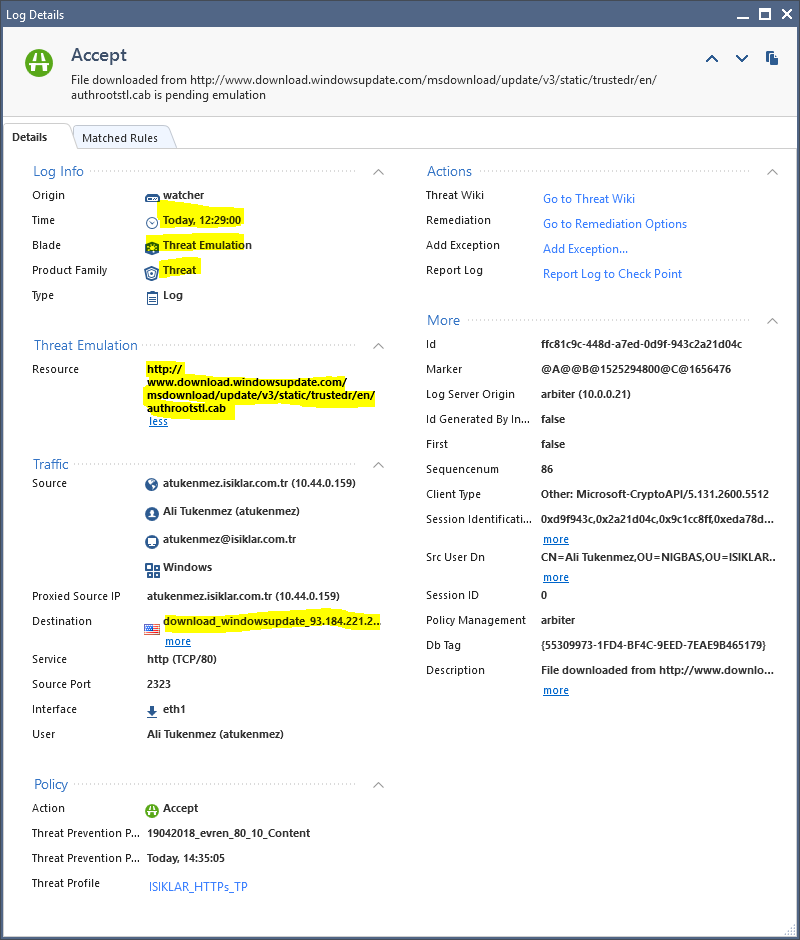
Unfortunatelly, there is no "Trusted Source" in Logs. And cab files from Microsoft updates continue to be checked:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can you check the log details ?
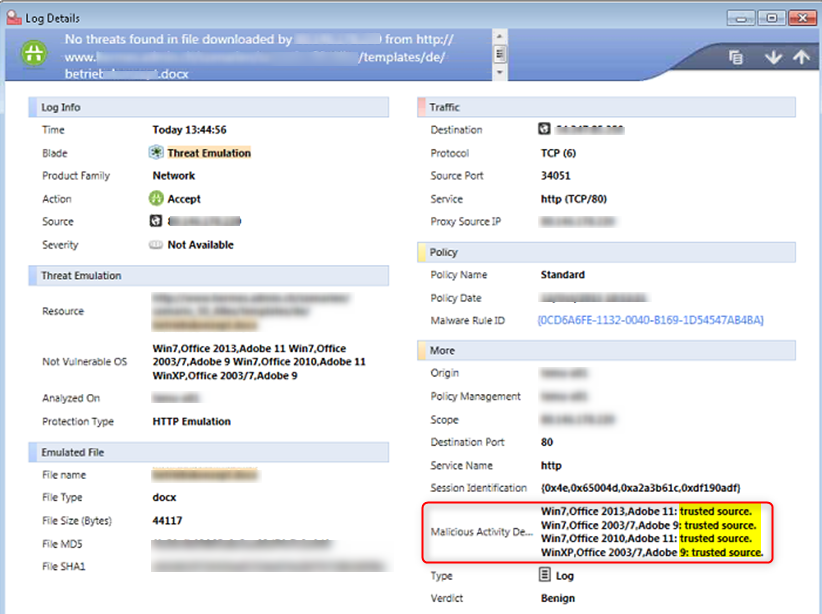
If it does not show "trusted source" or "local cache" here you need to open a ticket.
Then we will add the missing servers to our global whitelist which will be automatically updated in your environment.
Regards Thomas
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi there,
I was having the exact curiosity as Philipp Philippov thx for the explaination. Bu I have an additional question, concern: What about the logs those are created thousands maybe millions in a month? Do you have any advice to get rid of "trusted source" logs?
Also in my case my ISP cache system is in action and destination is NOT *.download.windowsupdate.com/*. So what we should do in this case? How are we supposed to get rid of thousands of MS update files to be scanned?

Thanks in advance...
Evren Buyer
Isiklar Holding A.S.
IT Manager
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Evren,
usually Threat Emulation log count is not a real problem in opposite to firewall logs that can be millions per day.
So I would not be concerned about the numbers of logs TE creates.
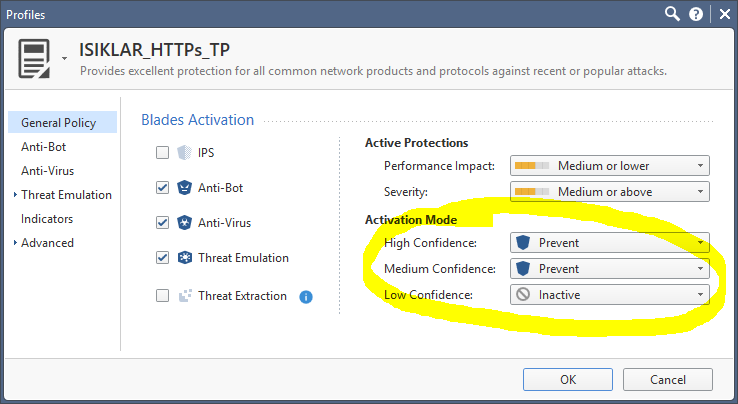
But anyway if you would like to disable benign file logging (which disables logging of ALL benign verdicts) you can do this in the advanced section of the TE settings in your relevant Threat Prevention profile:
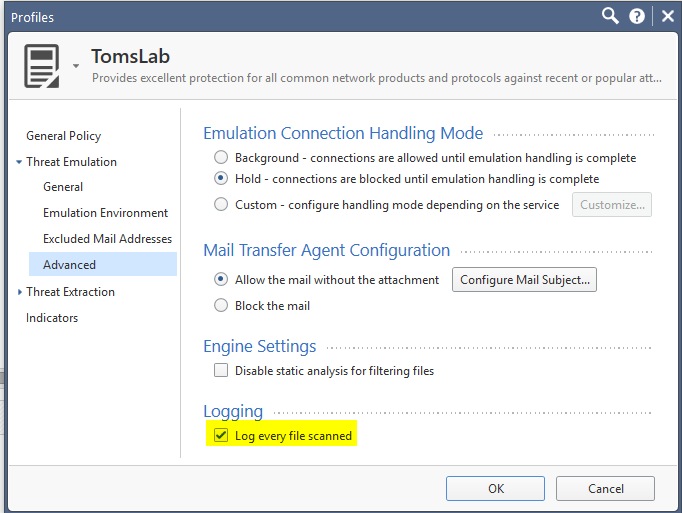
Global exclusions are set usually on destination URL not on IP.
Regards Thomas
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Thomas,
I understand your approach to my question, but in my case; I have limited internet bandwith (my country conditions) and lots of internal requests behind it. My question also contains another approach which is to exclude both global known file download scanning processes and logs. So according to your approach, yes I will be able to disable benign file logging, but not the whole job. That's why I asked how to "globally exlude" known/trusted URLs or destinations from the TE scans and also exclude the logs.
Thanks for your time and interest.
Evren Buyer
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
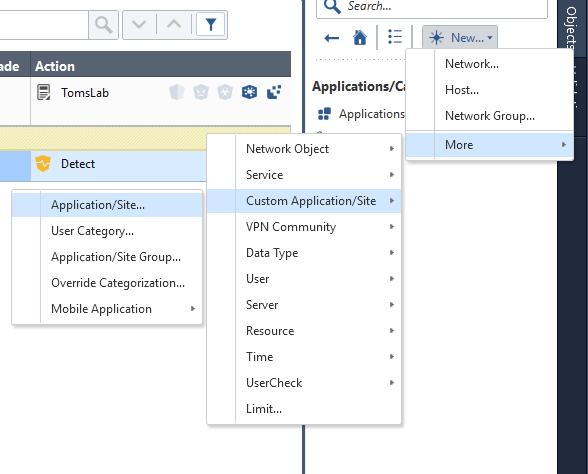
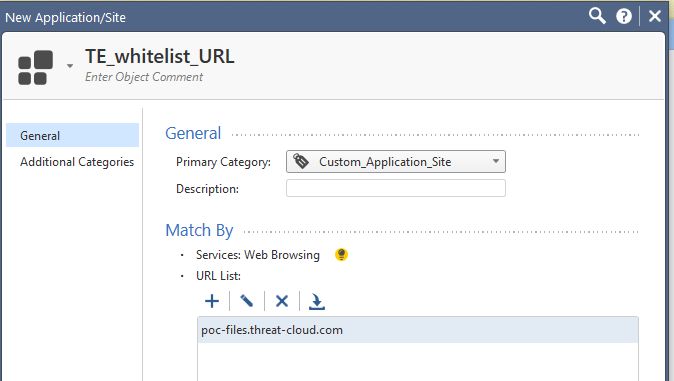
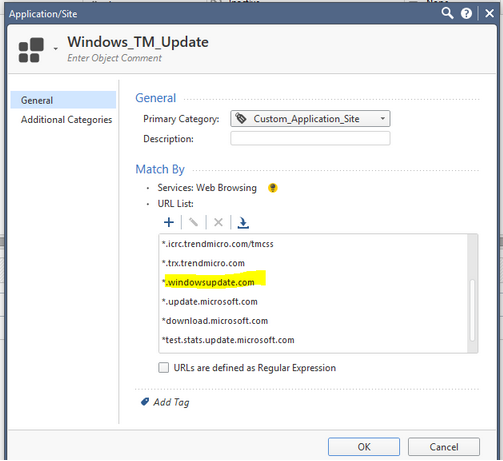
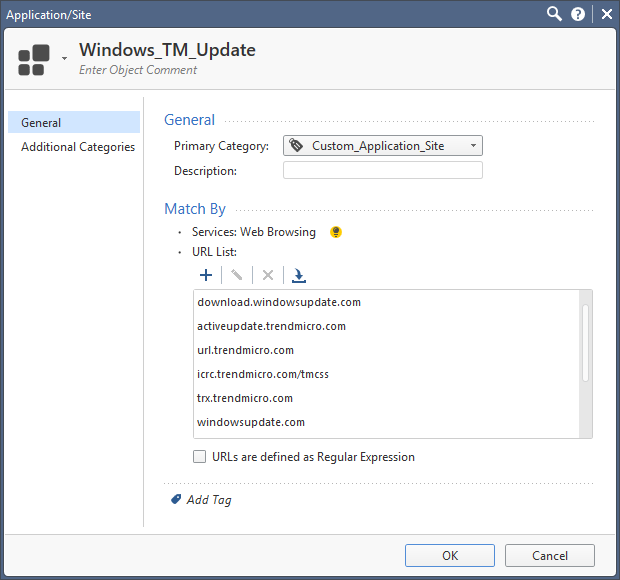
You can create groups of URLs that are Excluded from Threat Prevention.
Create an Application with the necessary URLs/hosts then add it as an exception.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Dameon,
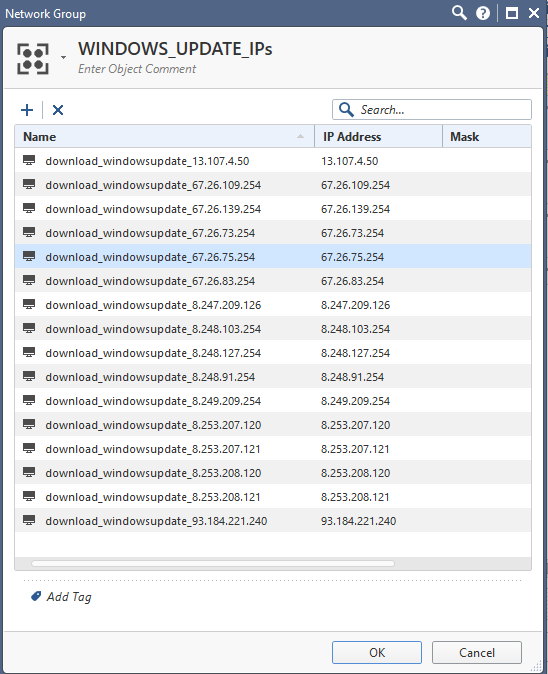
I did already, even in many ways with no luck...! Cause Threat Prevention Global Exceptions -some how?- won't work with Threat Prevention. You may see my objects, rules and logs below:
Log destination IP not in my list cause I wasn't able to add it before the log created. If I continue like that, I'll add whole Microsoft IP network as objects in my policy ! ![]()
Please check the latest image below. That's the problem in TE...!!!
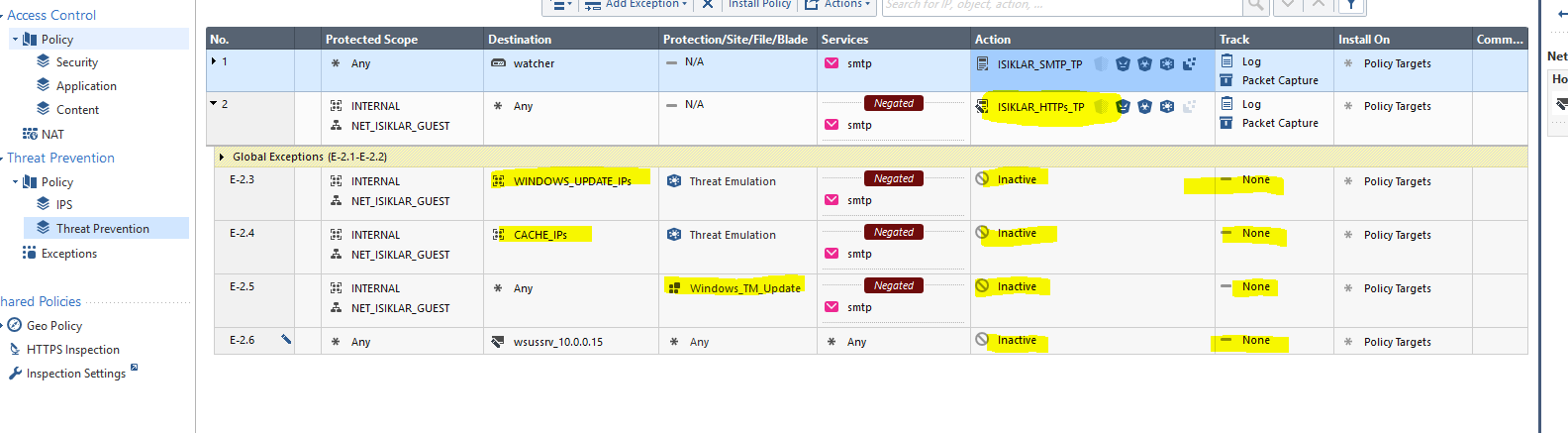
This rule didn't work, cause the destination Microsft IP wasn't recognized by me yet !
This rule NEVER WORKED...!!! And I don't know why...?

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Evren,
your exception rules E-2.3 and E-2.4 are only valid for R80.xx gateways because only these GWs understand the exception by blade. Is this the case ?
I validated exceptions in my lab some minutes ago:
1) Configuration before exception
a.) TP Policy
b.) Malware download
c.) Log
2) Configuration with Exception by hostname
a.) TP Policy
When using non-Regex schema please be sure to only use hostnames/FQDNs here !
If you want to use exclusions based on URLs you need to specify them as RegEx and enable the Regex checkbox in the dialog above.
b.) Malware download again
I cleared the cache before with "# tecli c c"
c.) Log
No log was issued. No emulation done.
d.) DLPU debug
With enabling DLPU debug by "# fw_debug dlpu on TDERROR_ALL_ALL=5" you can see in $FWDIR/log/dlpu.elg that the streaming engine does not pickup the file for TE anymore.
(Note: Enabling this debug on a production GW might cause high load due to extensive logging. Be also sure to disable again by running "# fw debug dlpu off TDERROR_ALL_ALL=0"
after troubleshooting is done)
Regards Thomas
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Thomas,
First of all, I thank you for your time and great interest to my situation.
Q1) your exception rules E-2.3 and E-2.4 are only valid for R80.xx gateways because only these GWs understand the exception by blade. Is this the case ?
A1) I have distributed setup and both my GW and Management are 80.10 (take 91 installed)

MY RULE BASE:
MY CUSTOM APPLICATION SITE OBJECT
before you warn me:
after I fixed the RegExs and installed the policy at 03.05.2018 11:45 AM (GMT+3):
And the exception did not work, log created again:

Also I had enabled the log and I can provide hole file if required.
6947][3 May 12:29:00][DLPU_MNGR] dlpu_mngr_http_conn_free: [150EC] freeing at Date: May 3, 2018
12:29:00
[6947][3 May 12:29:00][DLPU_MNGR] dlpu_mngr_http_session_free: freeing.. sid=6029318
[6947][3 May 12:29:00][DLPU_MNGR] dlpu_mngr_av_free_file_data: freeing AV file data for file authrootstl.cab
[6947][3 May 12:29:00][DLPU_MNGR] dlpu_mngr_av_free_file_data: file_data->current_file_path/opt/CPsuite-R80/fw1/tmp/dlp/{5D13B48D-C98A-2153-2700-5854E04ADBCF}
[6947][3 May 12:29:00][DLPU_COMM] dlpu_comm_read_handler: Done processing, 0 bytes left on buffer
[6947][3 May 12:29:00][DLPU_COMM] dlpu_comm_read_handler: Buffer position at 0
[6947][3 May 12:29:00][TED_CLIENT] [TED_CLIENT (TD::All)] ted_client_get_umsess_data: About to set_umsess_data for file /opt/CPsuite-R80/fw1/tmp/te/dlpu_tmp_files_0-1/{BEACFC1A-F07A-F349-8127-57588740B994}
[6947][3 May 12:29:00][TE_IS_TRACE] [TE_IS_TRACE (TD::All)] te_is::SocketApiClient::SendObject: sending data:
(
:connection (
:src_ip (10.44.0.159)
:src_port (2323)
:dst_ip (93.184.221.240)
:dst_port (80)
:protocol (6)
)
:meta_data (
:file_orig_name (authrootstl.cab)
:file_path ("/opt/CPsuite-R80/fw1/tmp/te/dlpu_tmp_files_0-1/{BEACFC1A-F07A-F349-8127-57588740B994}")
:file_type (cab)
:file_len (53747)
:protocol (http)
:rule_id (6)
:free_text (dlpu_te)
:should_track (1)
:malware_rule_id ("{D9126BC2-EB6D-4478-B5E8-0062F2597393}")
:scope_ip (10.44.0.159)
:conn_id (86252)
:session_id (6029318)
:instance_id (1)
:investigation_path (PATH_TE)
:cdir (2)
)
:http_data (
:url ("http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab")
)
:smtp_data (
:to ()
:from ()
:subject ()
:body_path ()
)
Continues...
6947][3 May 12:29:00][TE_IS_TRACE] [TE_IS_TRACE (TD::All)] te_is::SocketApiClient::OnListenerCallback: got data:
(
:event_id ("{82CB902E-2A21-D04C-9C1C-C8FFEDA78D44}")
:action (accept)
:confidence (none)
:done (1)
:file_path ("/opt/CPsuite-R80/fw1/tmp/te/dlpu_tmp_files_0-1/{BEACFC1A-F07A-F349-8127-57588740B994}")
:md5_string (b41d1f286e73f8a1a9b8da8131bcc814)
:investigation_path (PATH_TE)
:additional_data ()
:body_path ()
)
[6947][3 May 12:29:00][TED_CLIENT] [TED_CLIENT (TD::All)] TedClientListener::OnListenerCallback: got response:
(
:event_id ("{82CB902E-2A21-D04C-9C1C-C8FFEDA78D44}")
:action (accept)
:confidence (none)
:done (1)
:file_path ("/opt/CPsuite-R80/fw1/tmp/te/dlpu_tmp_files_0-1/{BEACFC1A-F07A-F349-8127-57588740B994}")
:md5_string (b41d1f286e73f8a1a9b8da8131bcc814)
:investigation_path (PATH_TE)
:additional_data ()
:body_path ()
)
[6947][3 May 12:29:00][TED_CLIENT] [TED_CLIENT (TD::All)] TedClientListener::OnListenerCallback: sending results to kernel
(
:event_id ("{82CB902E-2A21-D04C-9C1C-C8FFEDA78D44}")
:action (accept)
:confidence (none)
:done (1)
:file_path ("/opt/CPsuite-R80/fw1/tmp/te/dlpu_tmp_files_0-1/{BEACFC1A-F07A-F349-8127-57588740B994}")
:md5_string (b41d1f286e73f8a1a9b8da8131bcc814)
:investigation_path (PATH_TE)
:additional_data ()
:body_path ()
)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Evren,
DLPU still picks up the file from www.download.windowsupdate.com
But as far as your screenshot goes this host is not whitelisted.
Please switch to RegEx by enabling "URLs are defined as Regular Expressions" option in the whitelist settings.
Then change your host exclusion to:
e.g. for windowsupdate.com enter:
.*.windowsupdate.com
You might find this tool useful to check if your RegEx is correct:
Online regex tester and debugger: PHP, PCRE, Python, Golang and JavaScript
Regards Thomas
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Evren,
Give this a try using regex in your custom Application/Site object. Just validated in my lab and it stopped all the win updates logging when set up as a Global Exception.
(^|.*\.)windowsupdate\.com
Reference:
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 66 | |
| 19 | |
| 13 | |
| 12 | |
| 11 | |
| 10 | |
| 7 | |
| 7 | |
| 7 | |
| 7 |
Upcoming Events
Tue 28 Apr 2026 @ 06:00 PM (IDT)
Under the Hood: Securing your GenAI-enabled Web Applications with Check Point WAFThu 30 Apr 2026 @ 03:00 PM (PDT)
Hillsboro, OR: Securing The AI Transformation and Exposure ManagementTue 28 Apr 2026 @ 06:00 PM (IDT)
Under the Hood: Securing your GenAI-enabled Web Applications with Check Point WAFThu 30 Apr 2026 @ 03:00 PM (PDT)
Hillsboro, OR: Securing The AI Transformation and Exposure ManagementAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2026 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
About Us
UserCenter



