- Products
- Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- Bulgaria
- Cyprus
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
Step Into the Future of
AI-Powered Cyber Security
When the Agents Attack
A Live Look at Agentic Exposure Validation
Bridge the CAASM Gap
with Exposure Management
AI Security Masters E8:
Claude Mythos: New Era in Cyber Security
CheckMates Go:
CheckMates Fest
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- General Topics
- :
- SecureXL - Alternative method to identify rule cau...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jump to solution
SecureXL - Alternative method to identify rule causing templates to be disabled
Hello,
Is there are alternative way to identify exactly what is causing Accept Templates to be disabled. The output from the "fwaccel stat" has a output display issue and does not show me the information.
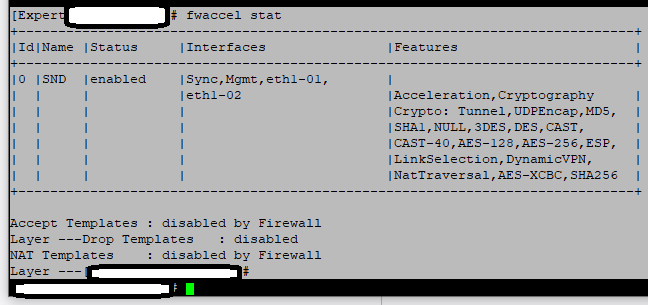
All I can see is "Layer ---", there is a missing carriage return and then "Drop Templates".
Many thanks,
Michael
2 Solutions
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Strange, it looks like fwaccel stat is not displaying its output correctly. Please provide the output of fwaccel templates -s and fwaccel templates -S, as I suspect Accept templating is actually working.
New Book: "Max Power 2026" Coming Soon
Check Point Firewall Performance Optimization
Check Point Firewall Performance Optimization
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ah here we go, your policy layer name must be longer than 32 characters. Shorten it and the fwaccel stat output will start working correctly:
New Book: "Max Power 2026" Coming Soon
Check Point Firewall Performance Optimization
Check Point Firewall Performance Optimization
10 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Which version do you use ? Afaik, this is the only way to display these layers. Even looks like an issue for TAC to me...
CCSP - CCSE / CCTE / CTPS / CCME / CCSM Elite / SMB Specialist
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
ZZZZZZZZ> cpinfo -y all
This is Check Point CPinfo Build 914000202 for GAIA
[IDA]
No hotfixes..
[MGMT]
HOTFIX_R80_30_JUMBO_HF_MAIN Take: 111
[CPFC]
HOTFIX_R80_30_JUMBO_HF_MAIN Take: 111
[FW1]
HOTFIX_R80_30_JUMBO_HF_MAIN Take: 111
FW1 build number:
This is Check Point's software version R80.30 - Build 078
kernel: R80.30 - Build 076
[SecurePlatform]
HOTFIX_R80_30_JUMBO_HF_MAIN Take: 111
[DIAG]
No hotfixes..
[PPACK]
HOTFIX_R80_30_JUMBO_HF_MAIN Take: 111
[CVPN]
No hotfixes..
[CPUpdates]
BUNDLE_CPINFO Take: 50
BUNDLE_INFRA_AUTOUPDATE Take: 19
BUNDLE_DEP_INSTALLER_AUTOUPDATE Take: 13
BUNDLE_R80_30_JUMBO_HF_MAIN_SC Take: 132
BUNDLE_R80_30_JUMBO_HF_MAIN Take: 111
[CPinfo]
No hotfixes..
[AutoUpdater]
No hotfixes..
[CPDepInst]
No hotfixes..
This is Check Point CPinfo Build 914000202 for GAIA
[IDA]
No hotfixes..
[MGMT]
HOTFIX_R80_30_JUMBO_HF_MAIN Take: 111
[CPFC]
HOTFIX_R80_30_JUMBO_HF_MAIN Take: 111
[FW1]
HOTFIX_R80_30_JUMBO_HF_MAIN Take: 111
FW1 build number:
This is Check Point's software version R80.30 - Build 078
kernel: R80.30 - Build 076
[SecurePlatform]
HOTFIX_R80_30_JUMBO_HF_MAIN Take: 111
[DIAG]
No hotfixes..
[PPACK]
HOTFIX_R80_30_JUMBO_HF_MAIN Take: 111
[CVPN]
No hotfixes..
[CPUpdates]
BUNDLE_CPINFO Take: 50
BUNDLE_INFRA_AUTOUPDATE Take: 19
BUNDLE_DEP_INSTALLER_AUTOUPDATE Take: 13
BUNDLE_R80_30_JUMBO_HF_MAIN_SC Take: 132
BUNDLE_R80_30_JUMBO_HF_MAIN Take: 111
[CPinfo]
No hotfixes..
[AutoUpdater]
No hotfixes..
[CPDepInst]
No hotfixes..
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
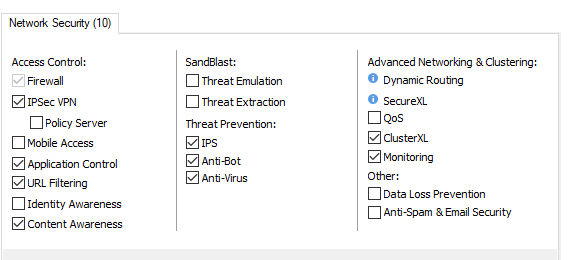
Is the firewall being managed by MDSM/Provider-1, and if so are there global rules being inserted at the top of the policy? Also please provide the output of enabled_blades.
New Book: "Max Power 2026" Coming Soon
Check Point Firewall Performance Optimization
Check Point Firewall Performance Optimization
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,
The cluster is not managed as part of a MDM environment, so there are not global rules. the following blades are activated:
Regards,
Michael
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try temporarily disabling Anti-bot, reinstall policy, then check Accept templating status again.
New Book: "Max Power 2026" Coming Soon
Check Point Firewall Performance Optimization
Check Point Firewall Performance Optimization
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello Unfortunately no difference after disabling Anti-Bot blade.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Are you using any of those in the policy: dhcp-request' / 'dhcp-reply' / 'dhcpv6-request' / 'dhcpv6-reply' / 'dhcpv6-relay?
If yes, look here: https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solut...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Strange, it looks like fwaccel stat is not displaying its output correctly. Please provide the output of fwaccel templates -s and fwaccel templates -S, as I suspect Accept templating is actually working.
New Book: "Max Power 2026" Coming Soon
Check Point Firewall Performance Optimization
Check Point Firewall Performance Optimization
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks, this solved the display issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ah here we go, your policy layer name must be longer than 32 characters. Shorten it and the fwaccel stat output will start working correctly:
New Book: "Max Power 2026" Coming Soon
Check Point Firewall Performance Optimization
Check Point Firewall Performance Optimization
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 9 | |
| 8 | |
| 8 | |
| 6 | |
| 6 | |
| 6 | |
| 5 | |
| 3 | |
| 3 | |
| 3 |
Upcoming Events
Wed 10 Jun 2026 @ 01:00 PM (EDT)
Deep Dive: When the Agents Attack: A Live Look at Agentic Exposure ValidationThu 11 Jun 2026 @ 11:00 AM (EDT)
Tips and Tricks 2026 #8: Say Yes to AI Without Saying Yes to RiskFri 12 Jun 2026 @ 10:00 AM (CEST)
CheckMates Live Netherlands - Sessie 47: Continuous Threat Exposure ManagementTue 16 Jun 2026 @ 05:00 PM (CEST)
Under the Hood: Check Point SASE | Internet Access Optimization & Performance TuningWed 10 Jun 2026 @ 01:00 PM (EDT)
Deep Dive: When the Agents Attack: A Live Look at Agentic Exposure ValidationThu 11 Jun 2026 @ 11:00 AM (EDT)
Tips and Tricks 2026 #8: Say Yes to AI Without Saying Yes to RiskFri 12 Jun 2026 @ 10:00 AM (CEST)
CheckMates Live Netherlands - Sessie 47: Continuous Threat Exposure ManagementTue 16 Jun 2026 @ 05:00 PM (CEST)
Under the Hood: Check Point SASE | Internet Access Optimization & Performance TuningThu 18 Jun 2026 @ 10:00 AM (CEST)
The Cloud Architects Series: Check Point WAF - The Next Generation of AI powered protectionAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2026 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
About Us
UserCenter



