Hi,
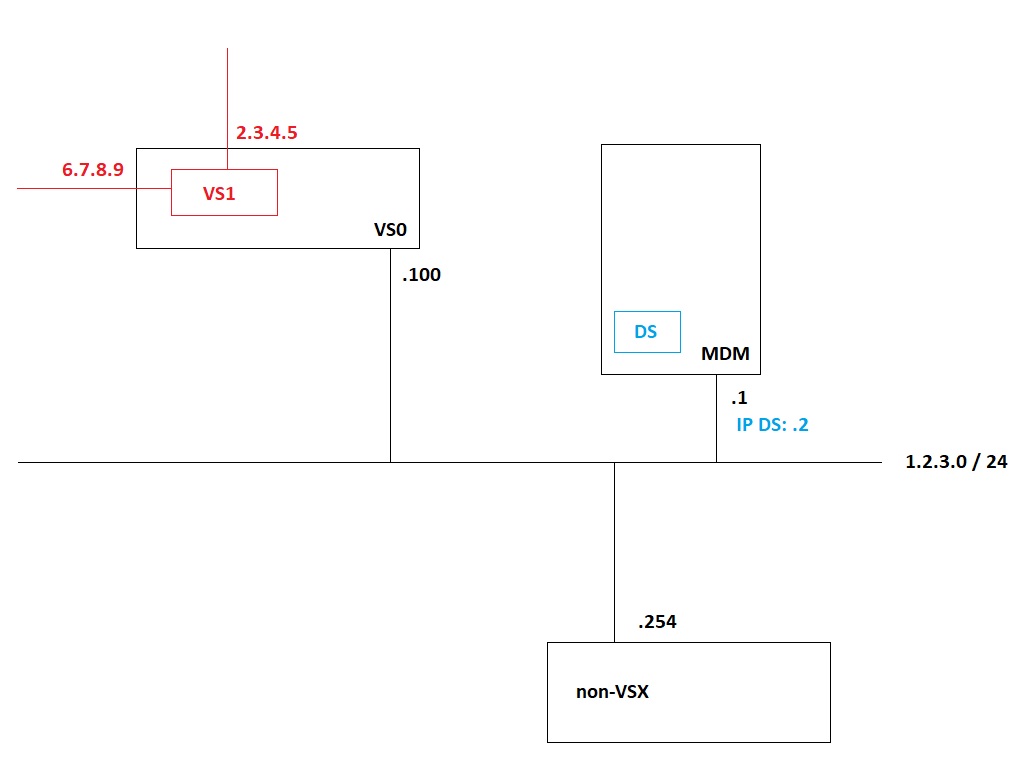
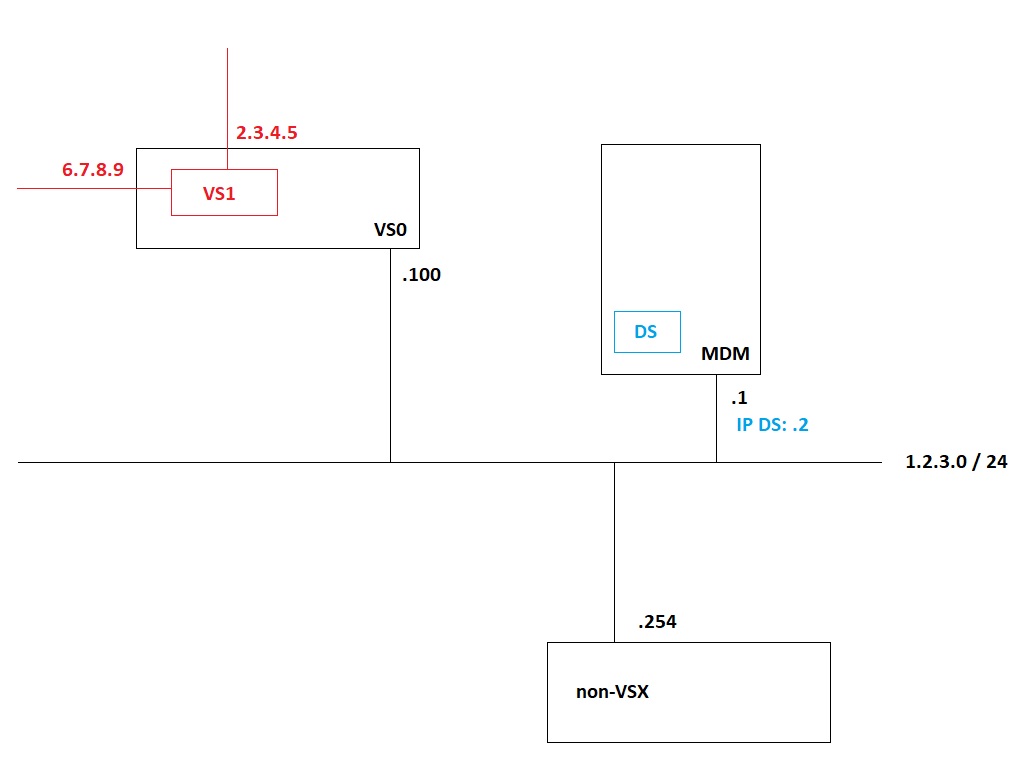
The Multi Domain Servers and the VSX clusters (VS0) are located in a firewall management network.
This firewall management network is protected by a non-VSX cluster. This cluster is the default gateway of the Multi Domain servers.
There is not route from the Domain Servers to the virtual systems. Not even physically.
So every time a Domain Server tries to contact a virtual system on the VSX clusters, it is send via the default gateway and is dropped by this non-VSX cluster securing the firewall management network.
So the traffic is not dropped by a virtual system (VS0 or any other virtual system) but by a completely other non-VSX cluster. So internal logic is not relevant here.
All is working and Monitor is showing all VS's OK within the Domain Servers. Policy installs, logging, it all works. So there is no need for the Domain Server to contact the VS's this way.
I have added a simple network drawing.
The MDM servers and VSX clusters (VS0) are located in network 1.2.3.0 / 24. The Multi Domain server is 1.2.3.1 and the Domain Server managing VS1 is 1.2.3.2.
The default gateway for the VSX clusters and Multi Domain servers is 1.2.3.254. The non-VSX cluster.
VS1 is created in a VSX cluster with IP-addresses 2.3.4.5 and 6.7.8.9. Let's say 2.3.4.5 is the main address.
In the non-VSX cluster 1.2.3.254 we can see packets being dropped from 1.2.3.2 to 2.3.4.5 for Check Point services.
Regards,
Martijn