- Products
- Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- Bulgaria
- Cyprus
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
Stop Babysitting Rules.
Go Agentic
Step Into the Future of
AI-Powered Cyber Security
Bridge the CAASM Gap
with Exposure Management
AI Security Masters E8:
Claude Mythos: New Era in Cyber Security
Call For Papers
Your Expertise. Our Stage
CheckMates Go:
CheckMates Fest
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- General Topics
- :
- Check Point R80.20 Now GA
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Check Point R80.20 Now GA
R80.20, part of the Check Point Infinity architecture, delivers the most innovative and effective security that keeps our customers protected against large scale, fifth generation cyber threats.
The release contains innovations and significant improvements in:
- Gateway performance
- Advanced Threat Prevention
- Cloud Security
- Access policy
- Consolidated network and endpoint management capabilities
- And much more
This release is initially recommended for customers who are interested in implementing the new features. We will make it the default version (widely recommended) after significant adoption and make it available in the 'Showing Recommended Packages' section in the CPUSE tab in Gaia portal.
 Performance Enhancements More
Performance Enhancements More
Performance Enhancements
- HTTPS Inspection performance improvements
- Session rate improvements on high-end appliances (13000, 15000, 21000 & 23000 Security Gateway models).
- Acceleration remains active during policy installation, no impact on Security Gateway performance.
VSX Gateways
- Significant boost to Virtual Systems performance, utilizing up to 32 CoreXL FW instances for each Virtual System.
- Dynamic Dispatcher - Packets are processed by different FW worker (FWK) instances based on the current instance load.
- Changes in the number of FW worker instances (FWK) in a VSLS setup do not require downtime.
- SecureXL Penalty Box supports the contexts of each Virtual System, see sk74520.
 Significant Improvements & New Features More
Significant Improvements & New Features More
Advanced Threat Prevention
- Enhanced configuration and monitor abilities for Mail Transfer Agent (MTA) in SmartConsole for handling malicious mails.
- Configuration of ICAP Server with Threat Emulation and Anti-Virus Deep Scan in SmartConsole.
- Automatic download of IPS updates by the Security Gateway.
- SmartConsole support for multiple Threat Emulation Private Cloud Appliances.
- SmartConsole support for blocking archives containing prohibited file types.
- Threat Extraction
- Full ClusterXL HA synchronization, access to the original files is available after a failover.
- Support for external storage.
- Advanced Threat Prevention Indicators (IoC) API
- Management API support for Advanced Threat Prevention Indicators (IoC).
- Add, delete, and view indicators through the management API.
- Advanced Threat Prevention Layers
- Support layer sharing within Advanced Threat Prevention policy.
- Support setting different administrator permissions per Advanced Threat Prevention layer.
- MTA (Mail Transfer Agent)
- MTA monitoring, e-mails history views and statistics, current e-mails queue status and actions performed on e-mails in queue.
- MTA configuration enhancements
- Setting a domain object as next hop.
- Ability to create an access rule to allow SMTP traffic to a Security Gateway.
- Create a dedicated Advanced Threat Prevention rule for MTA.
- MTA enforcement enhancements
- Replacing malicious links in an email with a configurable template.
- Configurable format for textual attachments replacement.
- Ability to add a customized text to malicious e-mails' body or subject.
- Tagging malicious-mails using X-header
- Sending a copy of the malicious e-mail to a predefined recipients list
- Improvements in policy installation performance on R80.10 and above Security Gateways with IPS
- Performance impact of "Suspicious Mail Activity" protection in Anti-Bot was changed to "High" and is now off by default
CloudGuard IaaS Enhancements
- Automated Security Transit VPC in Amazon Web Services (AWS) - Automatically deploy and maintain secured scalable architecture in Amazon Web Services.
- Integration with Google Cloud Platform.
- Integration with Cisco ISE.
- Integration with Nuage Networks.
- Automatic license management with the CloudGuard IaaS Central Licensing utility.
- Monitoring capabilities integrated into SmartView.
- Data center objects can now be used in access policy rules installed on 41000, 44000, 61000 and 64000 Scalable Platforms.
Access Policy
- Updatable Objects – a new type of network objects that represent an external service such as Office 365, Amazon Web Services, Azure GEO locations and more, and can be used in the Source and Destination columns of an Access Control policy. These objects are dynamically updated and kept up-to-date by the Security Gateway without the need to install a policy.
- Wildcard network object in Access Control that represents a series of IP addresses that are not sequential.
- Only for Multi-Domain Server: Support for scheduled policy installation with cross-Domain installation targets (Security Gateways or Policy Packages).
- Rule Base performance improvements, for enhanced Rule Base navigation and scrolling.
- Global VPN Communities (previously supported in R77.30).
- Support for using NAT64 and NAT46 objects in Access Control policy.
- Security Management Server can securely connect to Active Directory through a Security Gateway, if the Security Management Server has no connectivity to the Active Directory environment and the Security Gateway does.
Identity Awareness
- Identity Tags support the use of tags defined by an external source to enforce users, groups or machines in Access Roles matching.
- Improved SSO Transparent Kerberos Authentication for Identity Agent, LDAP groups are extracted from the Kerberos ticket.
- Two Factor Authentication for Browser-Based Authentication (support for RADIUS challenge/response in Captive Portal and RSA SecurID next Token/Next PIN mode).
- Identity Collector
- Support for Syslog Messages - ability to extract identities from syslog notifications.
- Support for NetIQ eDirectory LDAP Servers.
- Additional filter options - "Filter per Security Gateway" and "Filter by domain".
- Improvements and stability fixes related to Identity Collector and Web API.
- New configuration container for Terminal Servers Identity Agents.
- Active Directory cross-forest trust support for Terminal Servers Agent.
- Identity Agent automatic reconnection to prioritized PDP gateways.
- Security Management Server can securely connect to Active Directory via a Security Gateway if the Security Management Server has no connectivity to the Active Directory environment
HTTPS Inspection
- Hardware Security Module (HSM) support – outbound HTTPS Inspection stores the SSL keys and certificates on a third party dedicated appliance
- Additional ciphers supports for HTTPS Inspection (for more information, see sk104562)
Mirror and Decrypt
- Decryption and clone of HTTP and HTTPS traffic
- Forwarding traffic to a designated interface for mirroring purposes
Clustering
- New CCP Unicast - a new mode in which a cluster member sends the CCP packets to the unicast address of a peer member
- New Automatic CCP mode - CCP mode is adaptive to network changes, Unicast, Multicast or Broadcast modes are automatically applied according to network state
- Enhanced cluster monitoring capabilities
- Enhanced cluster statistics and debugging capabilities
- Enhanced Active/Backup Bond
- Support for more topologies for Synchronization Network over Bond interfaces
- Improved cluster synchronization and policy installation mechanism
- New grace mechanism for cluster failover for improved stability
- New cluster commands in Gaia Clish
- Improved clustering infrastructure for RouteD (Dynamic Routing) communication
Gaia OS
Upgraded Linux kernel (3.10) - applies to Security Management Server only
- New file system (xfs)
- More than 2TB support per a single storage device
- Enlarged systems storage (up to 48TB)
- I/O related performance improvements
- Support of new system tools for debugging, monitoring and configuring the system
iotop(provides I/O runtime statistics)lsusb(provides information about all devices connected to USB)lshw(provides detailed information about all hardware)lsscsi(provides information about storage)ps(new version, more counters)top(new version, more counters)iostat(new version, more counters)Advanced Routing:
- Allow AS-in-count
- IPv6 MD5 for BGP
- IPv4 and IPv6 OSPF multiple instances
- Bidirectional Forwarding Detection (BFD) for gateways and VSX, including IP Reachability detection and BFD Multihop
- OSPFv2 HMAC-SHA authentication (replaces OSPFv2 MD5 authentication)
ICAP Client
- Integrated ICAP Client functionality
 Security Management Enhancements More
Security Management Enhancements More
SmartConsole
- SmartConsole Accessibility features
- Keyboard navigation - ability to use the keyboard alone to navigate between the different SmartConsole fields
- Improved experience for the visually impaired, color invert for all SmartConsole windows
- Required fields are highlighted
- Multiple simultaneous sessions in SmartConsole. One administrator can publish or discard several SmartConsole private sessions, independently of the other sessions.
Logging and Monitoring
- Log Exporter - an easy and secure method to export Check Point logs over Syslog to any SIEM vendor using standard protocols and formats
- Ability to export logs directly from a Security Gateway (previously supported in R77.30)
- Unified logs for Security Gateway, SandBlast Agent and SandBlast Mobile for simplified log investigation
- Enhanced SmartView in browser:
- Log viewer with log card, column profile and statistics
- Export logs with custom or all fields
- Automatic-refresh for views
- Relative time frame support
- Improved log viewer with cards, profiles, statistics and filters
- I18N support for 6 languages (English, French, Spanish, Japanese, Chinese, Russian)
- Accessibility support - keyboard navigation and high contrast theme
SmartProvisioning
- Integration with SmartProvisioning (previously supported in R77.30)
- Support for the 1400 series appliances
- Administrators can now use SmartProvisioning in parallel with SmartConsole
Mobile Access
- Support for reCaptcha, keep abusive automated software activities from interfering with regular portal operations
- Support for One Time Password (OTP) without any hardware tokens
Endpoint Security Management Server
Endpoint Security Server is now part of the main train.
- Support for SandBlast Agent, Anti-Exploit and Behavioral Guard policies
- SandBlast Agent push operation to move/restore files from quarantine
- Directory Scanner initial scan and full rescan takes significantly less time
- Stability and performance enhancements for Automatic Synchronization (High Availability)
Endpoint Security Management features that are included in R77.30.03:
- Management of new Software Blades:
- SandBlast Agent Anti-Bot
- SandBlast Agent Threat Emulation and Anti-Exploit
- SandBlast Agent Forensics and Anti-Ransomware
- Capsule Docs
- New features in existing Software Blades:
- Full Disk Encryption
- Offline Mode
- Self Help Portal
- XTS-AES Encryption
- New options for the Trusted Platform Module (TPM)
- New options for managing Pre-Boot Users
- Media Encryption & Port Protection
- New options to configure encrypted container
- Optical Media Scan
- Anti-Malware:
- Web Protection
- Advanced Disinfection
Compliance
- User can create custom best practices based on scripts
- Support for 35 regulations including General Data Protection Regulation (GDPR)
Download and release information here: Check Point R80.20
131 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Check Point configurations are indeed copied when you upgrade using CPUSE, but custom files that are added by the user are not copied to the new partition with the upgrade. Of course we recommend to test the GW after the upgrade to make sure that all is working as expected.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
For example, what would these custom files be ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In general, anytime you make a configuration change, particularly via expert mode/Unix shell, you should document it for future you. ![]()
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
I have upgraded sms via cpuse to version 80.20 M2, but when I am going to upgrade the log server the following message appearsWhat is happening?
Other question, the version 80.20 M2 is 80.20 GA?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
GA is release of management and gateways, R80.20m2 is just release of management with new features..
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
R80.20.M2 was released after R80.20 GA and contains additional features and functionality.
That said, it looks like you are attempting to upgrade from R80.20 GA to R80.20.M2.
This upgrade path requires additional steps, as described here: Security Management upgrade from/to Management Feature Release
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Indeed R80.20.M2 is a Management Feature Release. It is built on top of R80.20 GA, but adds more Management features. The Mx release train is described in this SK: sk123473
The Management Feature Releases give you access to the latest Management features, but many customers will prefer to go with the official main-train GA. It is important for us to be transparent and clear about our versions, so I would like to reach out directly to understand if there is something that we still need to improve.
** Regarding the installation verification error, it should be possible to upgrade a standard Log Server. Some other configurations (such as Multi Domain Log Server) are not yet supported via an easy CPUSE upgrade (like Dameon mentioned). It's important to note that we are already working on removing these limitations and future releases should support all upgrade paths transparently.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I found the following things missing in R80.20:
- Interface can no longer be set with a /32 subnet mask. (This worked in R80.10)
- Along with this the OVH failover IP setup is not supported. See also: Configuring IP aliasing
- IPv6 routes of /3 are not supported (most notably used for 2000::/3 as alternative for a default gateway) (this worked in R80.10) iIp route add 2000::/3 .... still works in bash)
- IPv6 routes can no longer use logical interfaces. (This worked in R80.10)
It would be nice if R&D can see why these issues are no longer working with R80.20 and fix them.
Neither R80.10 nor R80.20 can actually use a default gateway to a host outside a directly attached network. The command is accepted but it fails to work.
<< We make miracles happen while you wait. The impossible jobs take just a wee bit longer. >>
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This works for me with DHCP - I receive a DHCP IP on a /32 subnet, addresses the interface OK and I get a default route, with another route added out of that interface to the upstream gateway.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Update regarding upgrade of Security Management Servers from R80.20.M1 to R80.20:
We are gradually enabling customers to upgrade their R80.20.M1 Security Management Servers to R80.20 without the requirement to contact Check Point Support.
Some customers will be able to upgrade their R80.20.M1 environments to R80.20, either with CPUSE or with Advanced Upgrade, while other customers will still face the message that requires them to open a ticket to Check Point Support.
Customers who currently face the message that requires them to open a ticket to Check Point Support, are advised to either wait for the gradual rollout to complete, or manually retrieve the updated upgrade package.
sk137677 contains the updated instructions for upgrading Security Management Servers from R80.20.M1 to R80.20.
Notes:
- Currently, Multi-Domain customers with version R80.20.M1 are advised to upgrade with the assistance of Check Point Support.
- The instructions for upgrading Security Gateways of all versions, or Security Management of versions prior to R80.20.M1 (such as: R80.10, R80, and R77.30) are not affected by this change.
Once the gradual rollout completes, we will once again update this thread.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I was just testing this in my lab:
- Changes in the number of FW worker instances (FWK) in a VSLS setup do not require downtime.
It seemed to work great - I didn't lose a ping, and it seemed to make the changes on the Standby member, then fail over and make the change on the Active member instead of blowing up both members at the same time as in the past. This is fantastic news!
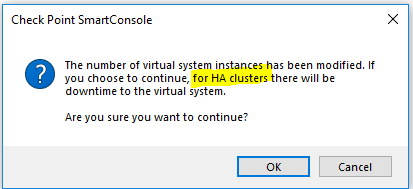
I did notice, however, that SmartConsole still warns about this creating downtime. It appears the wording has changed stating it only applies to HA clusters (even though my setup is VSLS):
Thanks for including this in R80.20 - it is hugely valuable.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It's referring to a VSX HA cluster (entire chassis failover), not VSLS (HA for a given VS).
- « Previous
- Next »
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 8 | |
| 4 | |
| 4 | |
| 4 | |
| 2 | |
| 2 | |
| 2 | |
| 2 | |
| 2 | |
| 1 |
Upcoming Events
Tue 02 Jun 2026 @ 10:00 AM (AEST)
The Cloud Architect Series: Check Point WAF. The next generation of AI-Powered Protection - APACTue 02 Jun 2026 @ 06:00 PM (IDT)
Under the Hood | Check Point SASE: Identity Integration & Access Policy Design Best PracticesThu 04 Jun 2026 @ 02:00 PM (CEST)
Deep Dive Webinar: New CloudGuard GWLB Deployment Without NAT Gateways - EuropeTue 02 Jun 2026 @ 10:00 AM (AEST)
The Cloud Architect Series: Check Point WAF. The next generation of AI-Powered Protection - APACTue 02 Jun 2026 @ 06:00 PM (IDT)
Under the Hood | Check Point SASE: Identity Integration & Access Policy Design Best PracticesThu 04 Jun 2026 @ 02:00 PM (CEST)
Deep Dive Webinar: New CloudGuard GWLB Deployment Without NAT Gateways - EuropeThu 04 Jun 2026 @ 07:00 PM (IDT)
Deep Dive Webinar: New CloudGuard GWLB Deployment Without NAT Gateways - AmericaThu 04 Jun 2026 @ 10:00 AM (PDT)
AI Security Masters E9: READY OR NOT: Securing the AI Enterprise 1/5 - AI Agent SecurityAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2026 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
About Us
UserCenter



