- Products
- Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- Bulgaria
- Cyprus
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
Step Into the Future of
AI-Powered Cyber Security
The State of Ransomware Q1 2026
Key Trends and Their Impact
AI Security Masters E8:
Claude Mythos: New Era in Cyber Security
Blueprint Architecture for Securing
The AI Factory & AI Data Center
Call For Papers
Your Expertise. Our Stage
CheckMates Go:
CheckMates Fest
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Hybrid Mesh
- :
- Firewall and Security Management
- :
- Re: Zero Phishing and IOS 18.4: Captive Portal Pro...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jump to solution
Zero Phishing and IOS 18.4: Captive Portal Problem
Hi,
if you have R82 and Zero Phishing active on a gateway (I know, not the most common setup), you may run into a problem I just had.
An iPhone or an iPad updated to IOS 18.4 will no longer be able to connect to a WIFI that is secured by a firewall described above.
The culprit in this case: Zero Phishing:
curl http://captive.apple.com/`
[HTML>[HEAD>[TITLE>Success[/TITLE>[/HEAD><BODY><script nonce="***">var zphInj="***"[/script>[script nonce="***" src='http://zero-phishing.iaas.checkpoint.com/zph/token_generator.php?api_key={***}' crossorigin>[/script>[script nonce="***" src='https://zerophishing.iaas.checkpoint.com/3/zp.js?api_key={***}' defer crossorigin>[/script>Success[/BODY>[/HTML>
(info: replaced all "<" by "[" to be able to post)
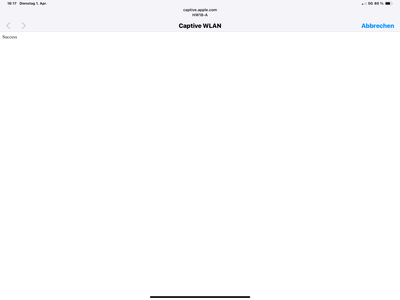
Prior to IOS 18.4, my iPhone had no problem with that reply, but with IOS 18.4 it hangs with this screen:
It no longer recognizes the "SUCCESS" due to the SCRIPT-Tag from Zero Phishing.
I don't need a solution, disabling the blade was a quick fix. I know how to create exceptions.
But I guess this will hit several people who don't know what hit them. As the update on IOS triggers this, I looked in Apple's direction first (and not completely wrong to do so). I opened an SR to give CP a heads up as I will not be the last one to stumble over this.
JHF was 12 in my case.
Yours, Martin
I don't know where I'm going, but I'm on my way
1 Solution
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
See the solution on how to create an exception: https://community.checkpoint.com/t5/Firewall-and-Security-Management/Zero-Phishing-and-IOS-18-4-Capt...
I don't know where I'm going, but I'm on my way
20 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Appreciate you sharing this tidbit in case others run into it.
Hopefully it will be addressed in a future JHF.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am quite optimistic on that. This will cause a lot of SR cases. Advised my contacts in the support team on the incoming wave. I‘m glad I ran into this one early, so it may do some good.
I don't know where I'm going, but I'm on my way
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The workaround is to add an exception to the threat prevention policy.
1. Under "Custom Applications/Categories" -> Application/Site -> Create an object for example: AppleCaptive
2. Add "captive.apple.com" to the Application object "AppleCaptive".
3. Create an exception
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
As I wrote, I know how to create an exception. This post was meant as something Google finds when you're looking for the problem. This has the potential to keep less experienced admins to scratch their heads 😁.
I don't know where I'm going, but I'm on my way
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We've faced the same issue. The workaround helped a lot. Thank you!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for this post, I had the exact same issue and it is now fixed!
I was not able to see anything relevant in the logs, which made the troubleshooting quite difficult.
Luckily, I came across your post — otherwise I would probably still be looking in the wrong direction.
How we could see these errors in logs
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We just started to see this issue yesterday (2/23). We are R82 JHF 73. I added the captive.apple.portal per example and did not help. If user chooses to "Use without Internet" client will join the SSID and have Internet access. Client will NOT see the captive.apple.portal again unless they "forget" the SSID and try to rejoin. I presume eventually client will see again if device is not online after some time. No issues with Android or Windows. Does not matter what SSID / auth method is used the Apple device tries to join (although I believe MAC Auth devices are not reporting this issue). I spent 6 hours with Cisco TAC who say its a DNS resolution timing issue that causes the Apple devices to believe they are on a Captive Portal SSID. We use Cloudflare as external DNS -- we tried using Google's 8.8.8.8 and it did not help. I did a curl from GW and it returns 200 code. No blocks in Log. How can I tell if its Phishing blade?
[Expert@GW-2:0]# curl_cli -v http://captive.apple.com
* Rebuilt URL to: http://captive.apple.com/
* Trying 17.253.3.137...
* TCP_NODELAY set
* Connected to captive.apple.com (17.253.3.137) port 80 (#0)
[ HTTP/1.1 200 OK
[ Content-Length: 69
[ Cache-Control: max-age=31536000
[ Last-Modified: Mon, 23 Feb 2026 06:31:50 GMT
[ Content-Type: text/html
[ Date: Mon, 23 Feb 2026 06:31:50 GMT
[ Age: 57238
[ Via: http/1.1 usnyc3-edge-fx-014.ts.apple.com (acdn/293.16398), http/1.1 usnyc3-edge-fx-014.ts.apple.com (acdn/293.16398)
[ X-Cache: miss, hit-fresh
[ CDNUUID: bf9030cb-3676-4078-921f-1c634444da6a-11805875095
[ Access-Control-Allow-Origin: *
[ Connection: keep-alive
[
[HTML>[HEAD>[TITLE>Success[/TITLE>[/HEAD>[BODY>Success[/BODY>[/HTML>
* Connection #0 to host captive.apple.com left intact
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You have to do the curl from a system behind the firewall. If it is the same output, it is not the problem I described in my post. If there is some weird output like in my original post, it's that blade.
This cannot be tested from the firewall itself...
I don't know where I'm going, but I'm on my way
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks. Ran curl in powershell on my Win 11 laptop and got 200 code. But laptop is wired connected....
RawContent : HTTP/1.1 200 OK
Age: 9810
X-Cache: miss, hit-fresh
CDNUUID: 5c47da3d-1ac8-4a88-bcc0-04d362c6711b-15226575337
Access-Control-Allow-Origin: *
Connection: keep-alive
Content-Length: 999
Cache-Cont...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The 200 is not important, but the "[HTML>[HEAD>[TITLE>Success[/TITLE>[/HEAD>[BODY>Success[/BODY>[/HTML>" is....
To determine if the blade is intervening, a wired PC is OK.
I don't know where I'm going, but I'm on my way
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks. Tried it in Wi-Fi and got the same result. But not sure what I should be looking for here:
Content : <HTML><HEAD><TITLE>Success</TITLE></HEAD><BODY><script nonce="3D67A23820B">var zphInj="eyJkc3RfaXAi
OiIxNy4yNTMuOTcuMjAyIiwiZHN0X3BvcnQiOiI4MCIsImVuY29kZWRfaHR0cF9ob3N0IjoiWTJGd2RHbDJaUzVoY0hCc1....
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
....I don't see anything in curl response that shows Phishing
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This comes from the Anti-Phishing blade:
<script nonce="3D67A23820B">var zphInj="eyJkc3RfaXAi
OiIxNy4yNTMuOTcuMjAyIiwiZHN0X3BvcnQiOiI4MCIsImVuY29kZWRfaHR0cF9ob3N0IjoiWTJGd2RHbDJaUzVoY0hCc
I don't know where I'm going, but I'm on my way
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
There is something intervening in your access to the captive portal and it looks like the Anti-Phishing blade.
I don't know where I'm going, but I'm on my way
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This part is added by the blade:
<script nonce="3D67A23820B">var zphInj="eyJkc3RfaXAi
OiIxNy4yNTMuOTcuMjAyIiwiZHN0X3BvcnQiOiI4MCIsImVuY29kZWRfaHR0cF9ob3N0IjoiWTJGd2RHbDJaUzVoY0hCc
I don't know where I'm going, but I'm on my way
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Phishing does not have a "dedictated" blade to turn off to test. GW is set to Use Automatic Settings. Autonomous Policy is set to Perimeter (recommended). Blocked and Detected phishing attempts show 0. Maybe change to Internal Network Profile which seems to disable Zero Phishing. No way to "bypass" Phishing for the portal?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
See the solution on how to create an exception: https://community.checkpoint.com/t5/Firewall-and-Security-Management/Zero-Phishing-and-IOS-18-4-Capt...
I don't know where I'm going, but I'm on my way
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks. I added the Exception to Threat Prevention policy and it works. I am still going to enter a CP ticket to see if it can be addressed w/o need for Exception rule. We just applied JHF 73 to our R82 last week and this had never been an issue before. Androids use a URL to probe for captive portal which does not seem to be impacted by Phishing blade. I ran the curl against connectivitycheck.gstatic.com/generate_204 and no phishing code present.
Thanks for the assist.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi, Did you manage to get anywhere with Check Point for an offical fix for this?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I advise CP through a ticket of this effect.
But I didn't ask for a fix since I would not rate it a bug. It is a change in IOS that triggered the problem.
Sorry!
I don't know where I'm going, but I'm on my way
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 24 | |
| 14 | |
| 10 | |
| 10 | |
| 8 | |
| 6 | |
| 5 | |
| 4 | |
| 4 | |
| 4 |
Upcoming Events
Tue 19 May 2026 @ 06:00 PM (IDT)
AI Security Masters E8 - Claude Mythos: New Era in Cyber SecurityWed 20 May 2026 @ 11:00 AM (CEST)
The New DDoS Reality: Autonomy, Scale, and the Future of DefenceTue 19 May 2026 @ 06:00 PM (IDT)
AI Security Masters E8 - Claude Mythos: New Era in Cyber SecurityWed 20 May 2026 @ 11:00 AM (CEST)
The New DDoS Reality: Autonomy, Scale, and the Future of DefenceFri 29 May 2026 @ 09:00 AM (EDT)
Caracas: Executive Breakfast: Innovación en Ciberseguridad – IA y Threat IntelligenceAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2026 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
About Us
UserCenter