- Products
Quantum
Secure the Network IoT Protect Maestro Management OpenTelemetry/Skyline Remote Access VPN SD-WAN Security Gateways SmartMove Smart-1 Cloud SMB Gateways (Spark) Threat PreventionCloudGuard CloudMates
Secure the Cloud CNAPP Cloud Network Security CloudGuard - WAF CloudMates General Talking Cloud Podcast - Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Quantum (Secure the Network)
- CloudGuard CloudMates
- Harmony (Secure the Workspace)
- Infinity Core Services (Collaborative Security Operations & Services)
- Developers
- Check Point Trivia
- CheckMates Toolbox
- General Topics
- Infinity Portal
- Products Announcements
- Threat Prevention Blog
- CheckMates for Startups
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
Mastering Endpoint Security -
Best Practices for 2024
Customer Threat Prevention
& Vulnerability Management Survey
Hunting Malware Using Memory Forensics
CheckMates Toolbox Contest 2024
Make Your Submission for a Chance to WIN up to $300 Gift Card!
CPX 2024 Content
is Here!
CheckMates Go:
Identity Awareness Best Practices
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Harmony
- :
- Connect
- :
- Harmony Corporate Access: How does Protection Prof...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Harmony Corporate Access: How does Protection Profile work for internal applications?
Dear Check Mates,
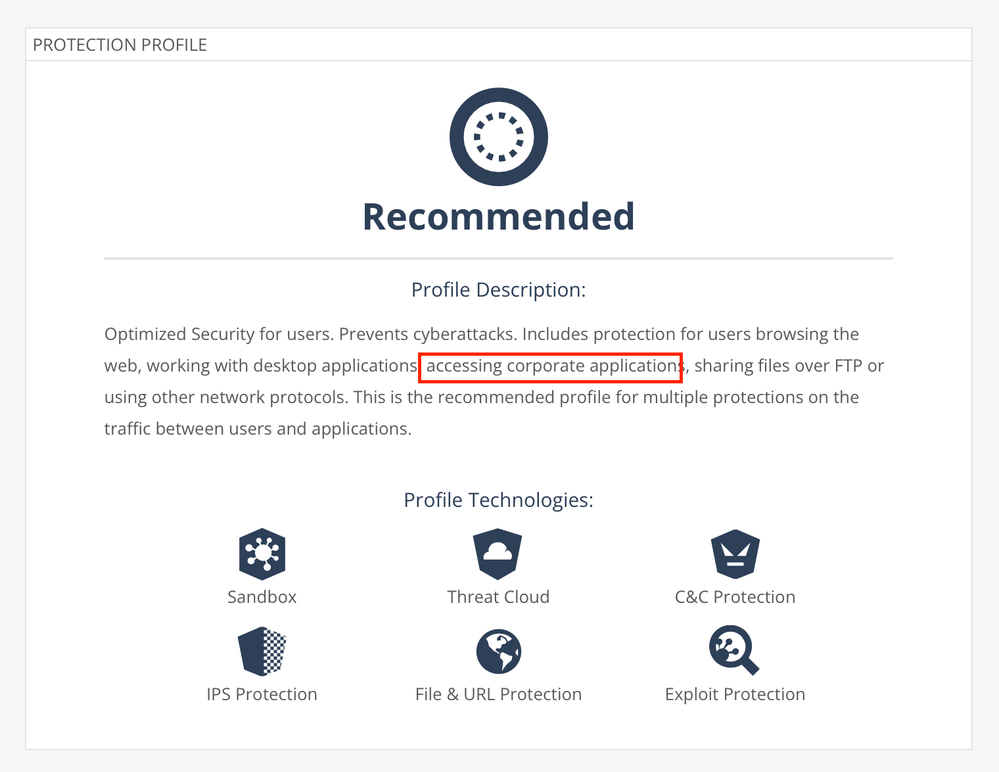
on harmony connect's threat prevention profile it says: "Includes protection for users browsing the web, working with desktop applications, accessing corporate applications, sharing files over FTP or using other network protocols."
1. Does this mean traffic to internal windows file servers is also verified?
2. What happens if a customers attempts to upload a malware to an internal file server? Is the connection terminated? Does the users receive some notification about this?
3. Is there any documentation concerning this feature? Unfortunately, the Admin Guide is very unspecific here.
Thank you all for your input
Tim
Labels
- Labels:
-
corporate access
8 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
For remote users / branches or both?
I see there's some risk of confusion here between Corporate Access & Internet Access license options and what each entails.
With that said some of the user centric use cases that immediately come to mind here are:
- SaaS applications accessed via the "Internet" (SWG for remote users)
- Split tunneling risk mitigation (for traditional VPN)
- Secure remote access (single agent)
- Secure remote access (clientless) - Application access is abstracted/proxied.
Recommend discussing further with your local SE to dive deeper.
CCSM R77/R80/ELITE
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Chris,
thanks for your quick reply.
I am referring to both (remote users and branches) accessing corporate applications. The profile description indicates that connections are sandboxed. Is this correct?
BR
Tim
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Typically, you would apply Threat Emulation (Sandboxing) to files from external sources correct.
CCSM R77/R80/ELITE
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I 'm not sure I understand this answer.
When we use Harmony Connect client (Secure Remote Access) for network access, does user traffic to internal resources go through the TP profile blades??
Same question for the clientless Application Access.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can we have someone from CP to reply on this one please?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Threat Emulation is about users downloading potential malicious content from external / untrusted sources. Typically this isn't something you would enforce for internal content.
CCSM R77/R80/ELITE
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I understand what you're saying here, but my question wasn't specifically about TE.
I am talking about all TP blades in general.
At the end of the day, we have remote users accessing internal resources through Harmony Connect which is CPs SASE solution.
So how are these resources protected during this access? Are there any TP blades applied to this traffic??
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
"The Threat Prevention profile is applicable to Internet Access (remote and branch users) and Network Access (remote and branch users)."
CCSM R77/R80/ELITE
Upcoming Events
Thu 01 Aug 2024 @ 10:00 AM (CEST)
CheckMates Live BeLux: What's new on Check Point CloudGuard!Thu 01 Aug 2024 @ 10:00 AM (CEST)
CheckMates Live BeLux: What's new on Check Point CloudGuard!About CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2024 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
About Us
UserCenter