Due to the market pressure, it is challenging to deliver high quality and secure embedded IoT assets. A secure product launch is highly dependent on factors such as the organization’s maturity, capital and product readiness. The IoT development process requires a multi-layered approach. During development, security is often not at the forefront of the process. Or there is not sufficient capital to develop “secure by design” IoT assets. A quick product launch often compromises on security, resulting in IoT assets with all kinds of security flaws.
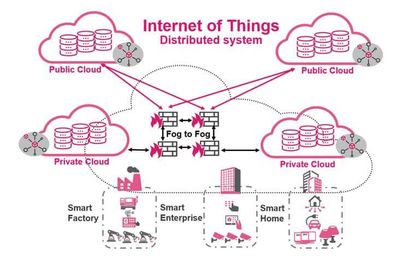
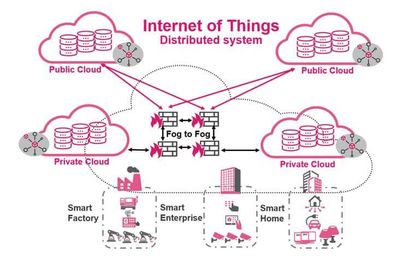
Figure 1: Overview of an IoT distributed system
What are the requirements when it comes to monolithic and distributed embedded IoT realms?
An embedded IoT system is a system that can have internet connectivity. Such systems are what we call “smart” assets, as they have network connectivity, whereas in the past, such assets were stand alone. Think of devices monitoring environmental factors.
An embedded IoT system will run software to execute all kinds of functions. This can either be performed in firmware or a dedicated OS.
What are the product challenges?
Challenges vary per product/practice and include those associated with:
- Hardware
- Software
- Deployment
- Maintenance
The world of embedded IoT systems can basically be divided into two groups. Each group offers unique pros and cons that should be assessed.
The embedded system types are:
- Monolithic – this is the classic “architecture” of client and server
- Distributed – represents a set of monolithic systems
Let’s take a deeper look at the monolithic IoT system itself.
The development of monolithic systems requires exact and accurate processes with subsequent workflows. What are the interfaces, which protocols are going to be used and which ports are open? Many monolithic smart assets are not “secure by design.” Many of those systems lack relevant security controls. Changes performed in the system (doesn’t matter how small they are) require compiling and extensive testing of the complete system, which is time consuming and expensive.
A distributed IoT system is a representation of several monolithic systems. Monolithic systems are used to build scalable distributed networks. By grouping such assets into a unique ecosystem, a distributed IoT system offers several advantages. Distributed systems are mostly managed via a common interface. This development approach is more secure and more sophisticated compared to the monolith system itself. It provides secure communication of the IoT asset with dedicated interfaces, ports, and protocols.
Secure development of an IoT asset is fundamental
Each use-case reflects unique requirements and needs. However, the following challenges generally pertain to all embedded IoT assets: power consumption ratio, security concerns, cost and size. Security, regulations, and standards are not on the agenda of IoT manufacturers. That needs to change, as the world is becoming more and more interconnected. And with that, the attack surface is expanding significantly. Luckily, we see more and more regulations and compliance standards on the horizon when it comes to IoT assets.
I love our ethos; prevention not detection. Detection, once malware is inside, is too late. While presenting the need for IoT security, I often use the IoT fish tank hack, as everyone (including the C-suite), has heard about that hack. The hack clearly shows how smart assets can be used as a steppingstone into a network (of the casino in this case). Hackers gained access to an unnamed U.S. casino by infiltrating the newly added thermostat in the fish tank. That fish tank had all kinds of sensors connected to a computer to regulate temperature, the saltiness of the water, food and cleanliness of the tank. I bet no one at that casino was expecting that the thermometer would be used to access and steal sensitive data.
It also clearly demonstrates that hackers are very creative and are always looking for new ways into the network. More information about the fish tank hack can be found here. Besides that, there is a lot of information available on the internet for criminals to use.
Imagine what information is available on Shodan, for instance. In case you’re unfamiliar, Shodan is a search engine for internet-connected assets. Search engines like Shodan are often used by hackers. The asset itself is presented to the hacker, with login credentials. There are even lists on the internet that describe vendor vulnerabilities that can be exploited and attackers are using this information to perform automated attacks on IoT assets. Think of password attacks, using insecure protocols and open ports to access sensitive data, basically exploiting known vulnerabilities. Other risks are that the IoT asset can get “bot” infected. Then, the bot on the compromised IoT asset communicates with a ‘command and control’ server to act as a zombie. This compromised IoT asset can be used to participate in DDoS attacks, and compromised assets can infect other assets with so called lateral movement techniques.
How to stay safe in the age of things
Secure architecture for all IoT assets is a must. Each organization should apply the highest level of security within products and services. IoT assets should be hardened and secured with security controls to prevent zero-day attacks. Each security challenge must be addressed with relevant security controls if we want to build secure smart industries, smart cities, smart offices and smart homes. For sustainable monolithic and distributed systems, in-depth planning with relevant life cycles and workflows are needed. The IoT solution should be secure, flexible, and compatible.
We at Check Point are here to help address IoT security challenges, offering a good security posture throughout the complete system, minimizing security concerns, and preventing critical breaches. Remember if it is smart, we can secure it! Start wearing your pink hat and secure your IoT assets!