- Products
- Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- Bulgaria
- Cyprus
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
AI Security Masters E7:
How CPR Broke ChatGPT's Isolation and What It Means for You
Blueprint Architecture for Securing
The AI Factory & AI Data Center
Call For Papers
Your Expertise. Our Stage
Good, Better, Best:
Prioritizing Defenses Against Credential Abuse
Ink Dragon: A Major Nation-State Campaign
Watch HereCheckMates Go:
CheckMates Fest
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Hybrid Mesh
- :
- Firewall and Security Management
- :
- Quick and Dirty Alert
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
This widget could not be displayed.
4 Replies
We are witnessing a surge in weaponized Microsoft documents containing a macro.
This campaign has very low detection by signature based solutions. It uses advanced social engineering techniques designed to make the user open the document and enable the macro. As you can see in the screen shots these are similar but more graphically adapt to the notorious locky campaign of 2016.
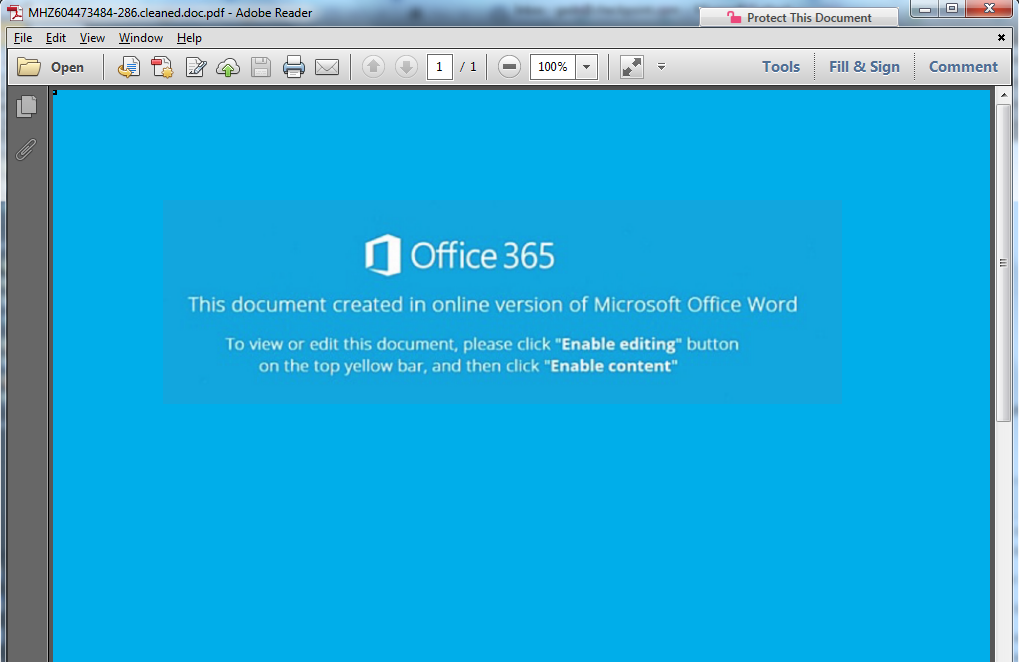
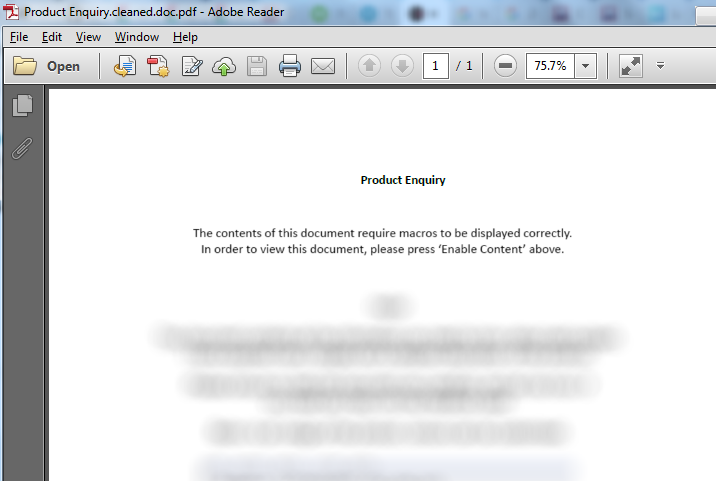
Screen shot of documents cleaned by Threat Extraction.
The last couple of days show a ten fold increase in the malicious files.
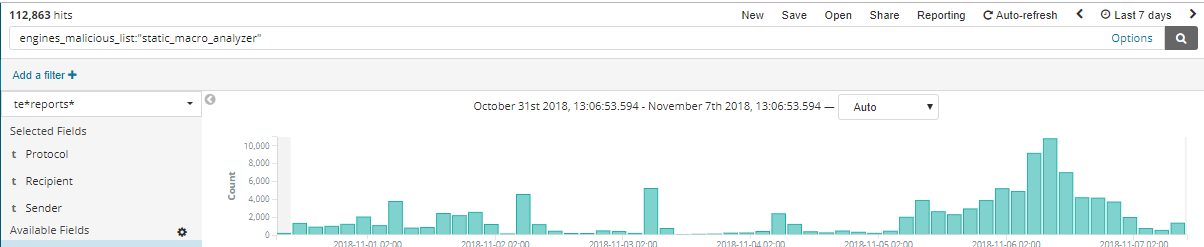
The surge as seen in numbers in the last week.
SandBlast Threat Extraction cleans the macro from the document at zero time.
SandBlast prevents the download of the original file by three zero day engines: Macro Analyzer, CPU level detection on crash and the emulator by its malicious process activity.
I'll update when there is more data.
Thanks,
Gadi
Quick and Dirty Alert
Quick and Dirty Alert
We are witnessing a surge in weaponized Microsoft documents containing a macro.
This campaign has very low detection by signature based solutions. It uses advanced social engineering techniques designed to make the user open the document and enable the macro. As you can see in the screen shots these are similar but more graphically adapt to the notorious locky campaign of 2016.
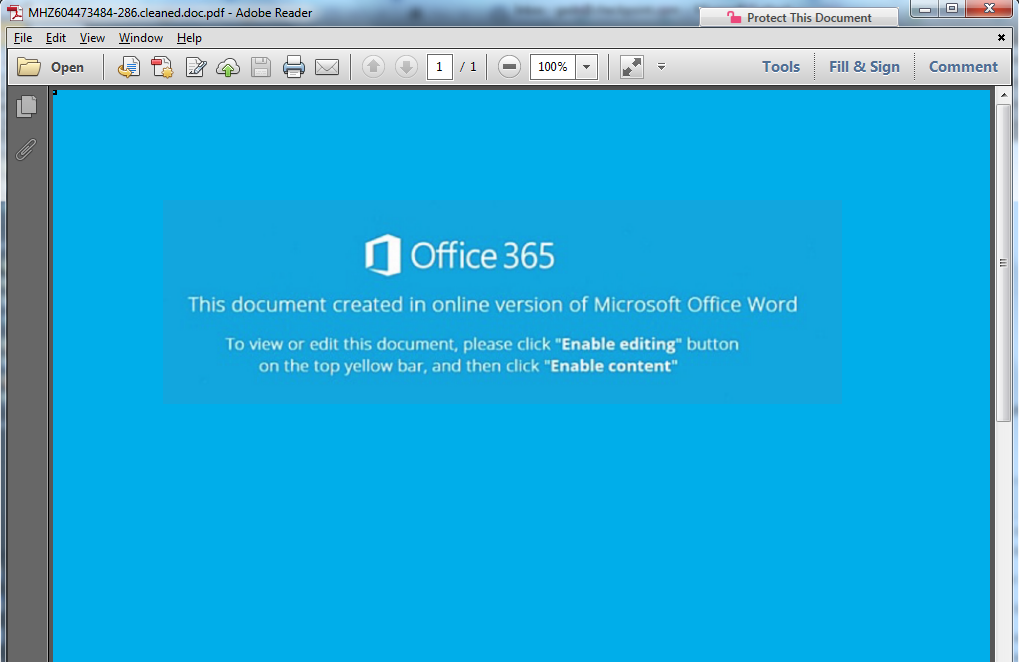
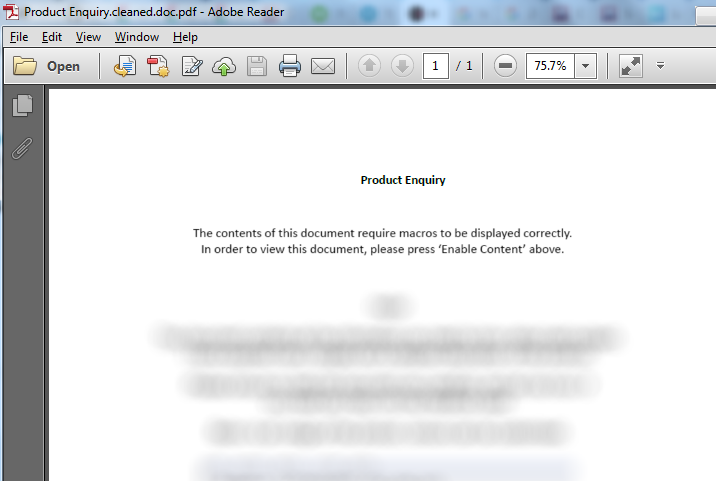
Screen shot of documents cleaned by Threat Extraction.
The last couple of days show a ten fold increase in the malicious files.
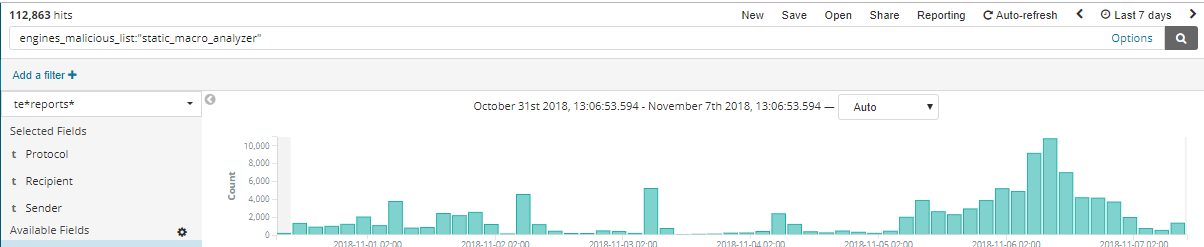
The surge as seen in numbers in the last week.
SandBlast Threat Extraction cleans the macro from the document at zero time.
SandBlast prevents the download of the original file by three zero day engines: Macro Analyzer, CPU level detection on crash and the emulator by its malicious process activity.
I'll update when there is more data.
Thanks,
Gadi
We are witnessing a surge in weaponized Microsoft documents containing a macro.
This campaign has very low detection by signature based solutions. It uses advanced social engineering techniques designed to make the user open the document and enable the macro. As you can see in the screen shots these are similar but more graphically adapt to the notorious locky campaign of 2016.
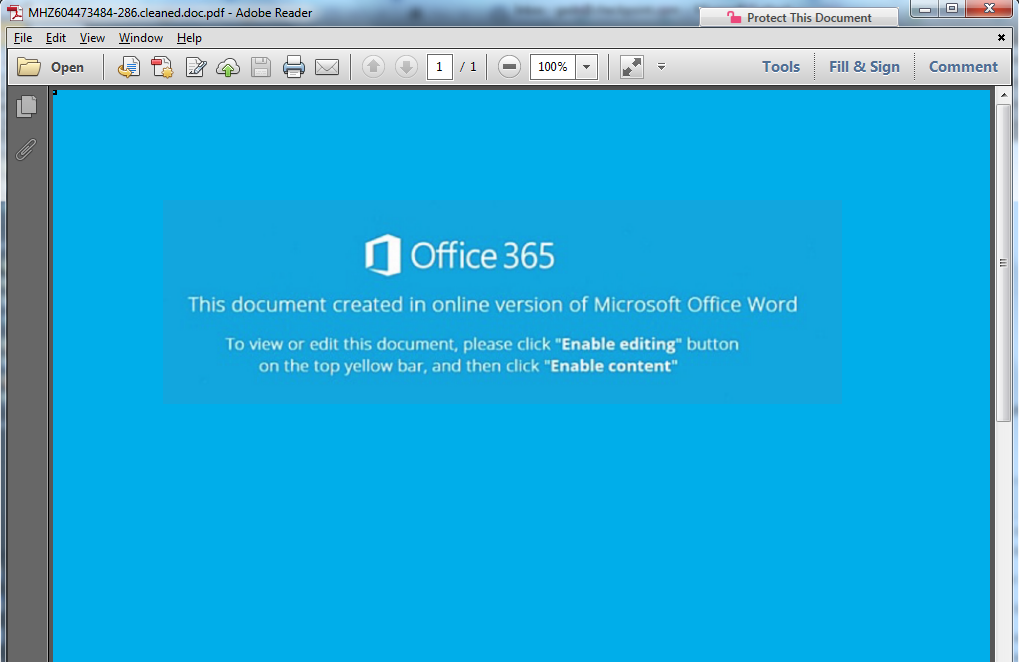
Screen shot of documents cleaned by Threat Extraction.
The last couple of days show a ten fold increase in the malicious files.
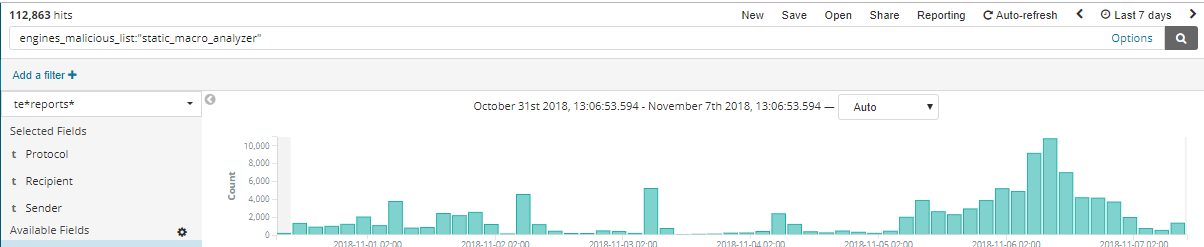
The surge as seen in numbers in the last week.
SandBlast Threat Extraction cleans the macro from the document at zero time.
SandBlast prevents the download of the original file by three zero day engines: Macro Analyzer, CPU level detection on crash and the emulator by its malicious process activity.
I'll update when there is more data.
Thanks,
Gadi
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Vladimir,
Yes, TE is able to catch it and prevent it.
I'll upload a report
Hi Vladimir,
Yes, TE is able to catch it and prevent it.
I'll upload a report
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sample this morning came with two word documents. AV Blade caught the emails. Does Emotet usually send two attachments?
Sample this morning came with two word documents. AV Blade caught the emails. Does Emotet usually send two attachments?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Not that I am aware of, please do share
Not that I am aware of, please do share

