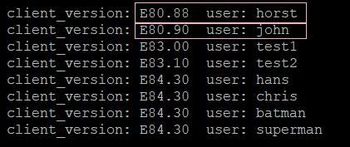
On August 2019 we released version E81.20 addressing usage limitation of older versions of Check Point’s Endpoint, VPN and SandBlast agent (sk158912). These older, out of support versions – Endpoint/VPN E80.81 to E81.10 (Windows only) and SandBlast agent E80.61 to E81.10 (Windows only) – WILL CEASE TO OPERATE on January 1st 2021.
Unfortunately, we see that some customers haven’t updated these old versions. Their update will become more difficult to facilitate after January 1st.
Therefore, we urge to all customers reminding them that users of versions E81.10 and before are required to update their versions by January 1st 2021 in order to make sure their systems remain operational.
We offer our customers two options to address this request. Upgrade to a newer version (Recommended) or apply a simple fix to the old version. Look into sk171213 for the details.
Either way, customers should make sure to carry upgrades to supported versions (E83 or later versions) at a later time to ensure they receive the best security.
Our TAC services are available to support any customer needs regarding this request. More information can be found on this web page.
Please find some FAQ below:
FAQs
- Q: Why are we approaching all customers now?
On August 2019 we released version E81.20 addressing usage limitation of older versions of Check Point’s Endpoint, VPN and SandBlast agent (sk158912). These older, out of support versions will cease to operate on January 1st 2021. We are approaching all customers as we saw that many of them haven’t updated these old versions, and their update will become more difficult to facilitate after January 1st. So, we need to make sure they do so this week – before January 1st – to ensure a smooth and easy to facilitate transition to newer versions.
- Q: What is the technical problem?
The issue happens due to the internal certificate used by VPN/Endpoint services. One of the certificates expires on January 1st 2021, therefore all services that use this certificate will stop working on January 1st 2021. The fix is within the driver library: epklib. The library fixes an issue with regards to the certificate’s expiration validation (current date and not the signing date).
- Q: Which versions are affected, and which are not?
A: For the full list of affected clients, please refer to sk171213.
- Q: Is this a security update? Is there a vulnerability in the software?
A: No. This is a functional update to ensure VPN and blade connectivity and functionality. There are no known security vulnerabilities.
- Q: Is this a pressing matter?
A: Yes! Customers need to act before Jan-1st 2021. After this date they may experience client malfunctions For Stand Alone VPN with Firewall – the Firewall and the VPN may stop working. For Endpoint client - Firewall, Forensics, Threat Emulation, Anti-Bot and in some cases also the VPN may stop working.
- Q: Are customers notified?
Impacted versions are already out-of-support. See Check Point Support Life Cycle Policy.
- Q: What is the suggested course of action?
Please follow sk171213 for the full details on all the actions.
- A. Upgrade to a newer version (E81.20 or later versions). We recommend using version E84.0 Download link, or
- B. Apply a quick and temporary fix that takes a minute to install (Download from sk171213).
Either way, you should make sure to carry upgrades to supported versions (E83 or later versions) at a later time to ensure you receive the best security.
- Q: Who should I approach for additional information?
The Check Point TAC should be consulted.
- Q: What indications customers will encounter facing this problem?
- Inability to connect using remote access VPN. Error message while connecting "Connectivity with the Check Point Endpoint Security service is lost".
- “Blade not running” indicated in Endpoint/VPN client Display Overview.