- Products
Quantum
Secure the Network IoT Protect Maestro Management OpenTelemetry/Skyline Remote Access VPN SD-WAN Security Gateways SmartMove Smart-1 Cloud SMB Gateways (Spark) Threat PreventionCloudGuard CloudMates
Secure the Cloud CNAPP Cloud Network Security CloudGuard - WAF CloudMates General Talking Cloud Podcast - Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Quantum (Secure the Network)
- CloudGuard CloudMates
- Harmony (Secure Users and Access)
- Infinity Core Services (Collaborative Security Operations & Services)
- Developers
- Check Point Trivia
- CheckMates Toolbox
- General Topics
- Infinity Portal
- Products Announcements
- Threat Prevention Blog
- CheckMates for Startups
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
Mastering Compliance
Unveiling the power of Compliance Blade
SASE Masters:
Deploying Harmony SASE for a 6,000-Strong Workforce
in a Single Weekend
May the 4th (+4)
Navigating Paradigm Shifts in Cyber
CPX 2024 Content
is Here!
Harmony SaaS
The most advanced prevention
for SaaS-based threats
CheckMates Go:
CPX 2024 Recap
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- General Topics
- :
- NAT's issue
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
NAT's issue
Hi.
I'm configuring the NAT on CheckPoint 2200. But, it doesn't work. Please advise how can I do? Thanks.
18 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What exactly did you configure in an effort to make this work?
How did you test this to see that it worked (or didn't)?
What entries did you see in the logs when you tested this, if any?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I created the new host 192.168.1.20 and set static nat 2.2.2.10. After that, I ping to IP 2.2.2.10, but it's not forward to 192.168.1.20. I didn't see the log to 192.168.1.20. Is there any advise, I'll do it and update the result.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
add a proxy arp.
Regards, Maarten
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can you advise how to add a proxy arp on CheckPoint FW?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Demeon,
wonder about one thing, you may know that by heart but I just don't remember:
- once you've got "object-nat" based on single host, you obviously don't do the manual NATs and make them higher in sequencing, do you need a proxy-arp or not at all?
I was having one case with my old customer with R77.30 VSXs on 12xxx appliances in HA (ClusterXL not LSM) where they insisted that proxy-arp made on clish need to be in place, otherwise public IPs won't communicate with upstream router.
you agree or not - simple query though ![]()
Jerry
Jerry
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I believe that the proxy-arp is not required if Static Nat in object's properties is defined, at least in R77.30.
The problem that client of yours was experiencing without it is likely due to improperly configured routing on the upstream router.
I.e. public network may not have been forwarded to the Cluster XL's vIP and the network between Cluster XL and the upstream router or HSRP router pair may have been a subset of their public range, /28 or some such.
Possibly, vMAC was not enabled on cluster object.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
excellent point. thanks Vlad. I think it is spot on, the HSRP indeed turned out to be the case.
Cheers
Jerry
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Vlad, to make it even more complicated I will add a little bit of naughty stuff here:
- vMAC wasnt enabled indeed
- HSRP/VRRP was causing an issues
- Hosts on STATIC object IP were 2 SMS devices (Management HA)
- proxy arp was set but when removed there was no difference traffic flow wise, still Management HA couldn't communicate via VIP IP from ClusterXL hosts (core gw).
- when proxy arp was removed it still didn't work, only when IPS got into the Huawei crap (...) they've found mismatches on their config, fixed dynamic routing and all started to work as it should ![]()
now I'm facing similar story on R80.10 infra where Management HA cannot comm with CPUSE due to (potentially) upstream FW glitch as the proxy-arp in or not in place makes no difference. Static object NAT made on SMS boxes itself (by Dash).
still CPUSE cannot be reached by SMS's itself.
good thing is that it will get resovled soon when Compliance Team get on with it and sort their FW ruleset mess out.
best,
Jerry
Jerry
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can you elaborate on this please: "Static object NAT made on SMS boxes itself (by Dash)."
Unless I am misreading this, there are still gateways upstream of the SMS HA members and ultimately, those will be deciding what public IPs will be present to the outside world for SMS to CPUSE communication.
If you need the SMS HA members to have static IPs at all (i.e. they are managing gateways in other locations, such as branches, secondary data centers, etc..), then whatever the NAT configuration for these object is imposed on the gateways between SMS and the Internet should be the definitive authority, is it not?
For CPUSE specifically, you should be able to use the proxy settings in the Gaia to circumvent whatever impediments the NAT currently causing.
Cheers,
Vladimir
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It's a function of this:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks, I got that as it was quite frustrating so far. Now all clear.
EOT
Cheers
Jerry
Jerry
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
1. You have two public IP ranges on the outside of your firewall (reason?). You have to verify that routing between them and the Internet is working (from the router, ping Internet hosts using source IP of 2.2.2.14).
2. Properly define topology of the 2200 gateway (i.e. eth0 as External Interface, eth1 as Internal with defined network)
3. Verify that hosts on the Internet are reachable from 2200 (i.e. ping www.yahoo.com from expert mode)
4. Configure host object with IP address of 192.168.1.20 and its NAT properties as Static with IP of 2.2.2.10 (this is only necessary if you are trying to reach the 192.168.1.20 from the Internet. If all you are trying to achieve is outbound access, configure NAT properties as "Hide" behind gateway).
5. If you are using Static NAT, verify that the packets from upstream router hitting External interface of 2200 (Enable ICMP in Global Properties, traceroute from the router to the 2.2.2.10, check the CP logs for ICMP packets).
6. Verify that the gateway on 192.168.1.20 is defined as 192.168.1.1
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for your information. I'll check some thing and update the result.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Just looking at the drawing, you need to add proxy arp, unless your using automatic NAT
add arp proxy ipv4-address 2.2.2.10 macaddress xx:xx:xx:xx:xx:xx real-ipv4-address 2.2.2.9
Where macaddress is the address of the interface with 2.2.2.9
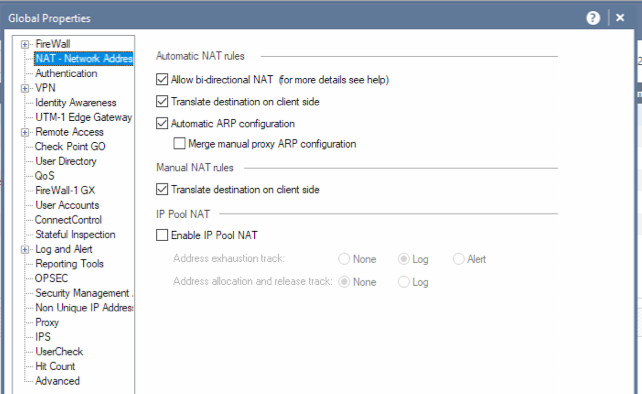
In the global properties of the management server check the NAT page for these settings:
After adding a proxy do not forget to push the policy otherwise it will still not work.
To check if the proxy arp is working use: fw ctl arp
Regards, Maarten
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for your advise. Let me check on it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Here is also related sk30197-Configuring Proxy ARP for Manual NAT where are all steps described well.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Tuan,
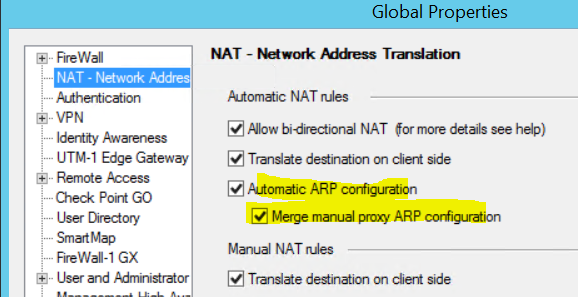
As described by the other users:
- add proxy arp
- enable manual proxy arp configuration
Here you can find a flowchart of how nat (source NAT and destination NAT) is implemented:
R80.x Security Gateway Architecture (Logical Packet Flow)
Regards,
➜ CCSM Elite, CCME, CCTE
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
proxy arp from clish (for simplicity)
clish> add arp proxy ipv4-address "public desirable IP" interface ethx real-ipv4-address "interface-physical-ip"
hope it helps
Jerry
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 20 | |
| 18 | |
| 12 | |
| 11 | |
| 6 | |
| 5 | |
| 5 | |
| 4 | |
| 4 | |
| 4 |
Upcoming Events
Thu 02 May 2024 @ 04:00 PM (CEST)
CheckMates Live DACH - Keine Kompromisse - Sicheres SD-WANThu 02 May 2024 @ 05:00 PM (CEST)
SASE Masters: Deploying Harmony SASE for a 6,000-Strong Workforce in a Single WeekendAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2024 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
Facts at a Glance
User Center


