- Products
Quantum
Secure the Network IoT Protect Maestro Management OpenTelemetry/Skyline Remote Access VPN SD-WAN Security Gateways SmartMove Smart-1 Cloud SMB Gateways (Spark) Threat PreventionCloudGuard CloudMates
Secure the Cloud CNAPP Cloud Network Security CloudGuard - WAF CloudMates General Talking Cloud Podcast - Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Quantum (Secure the Network)
- CloudGuard CloudMates
- Harmony (Secure Users and Access)
- Infinity Core Services (Collaborative Security Operations & Services)
- Developers
- Check Point Trivia
- CheckMates Toolbox
- General Topics
- Infinity Portal
- Products Announcements
- Threat Prevention Blog
- CheckMates for Startups
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
Mastering Compliance
Unveiling the power of Compliance Blade
SASE Masters:
Deploying Harmony SASE for a 6,000-Strong Workforce
in a Single Weekend
May the 4th (+4)
Navigating Paradigm Shifts in Cyber
CPX 2024 Content
is Here!
Harmony SaaS
The most advanced prevention
for SaaS-based threats
CheckMates Go:
CPX 2024 Recap
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Quantum
- :
- Security Gateways
- :
- How to disable SIP ALG inspection in a specific ru...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jump to solution
How to disable SIP ALG inspection in a specific rule in Checkpoint? Also Could this be done globally, like Cisco ASA?
2 Solutions
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
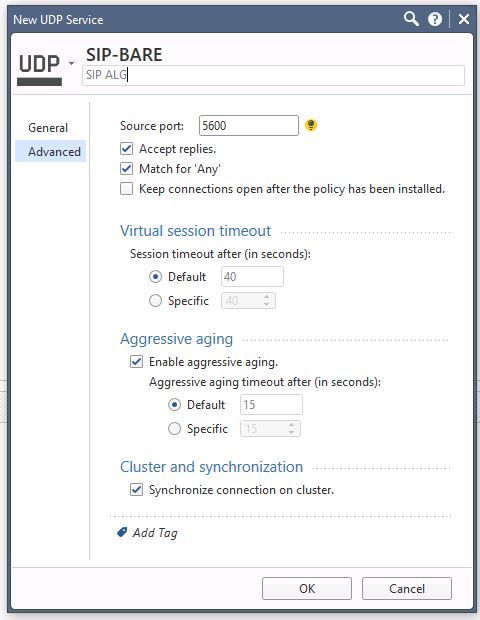
Actually I am not sure Tomer answer will work. After having been on first name bases with R&D VOIP for a year with loads of VOIP tickets in R65 I learned a lot of the background of the code. And I guess most of it is still valid.
At least in R77.30 I always use the following strategy:
- Define your own UDP or TCP object without a protocol handler. For example: Name it SIP-BARE and use UDP/5600
- Make sure you enable "Match for Any" on your own service and disable it on the existing service.
- Make a rule for you own service AND!!!! make sure it is ABOVE any rule that uses the build in SIP services (which contains handlers).
If you forget to put your rule in the right order the whole trick will not work.
As soon as you have a rule that will contain a handler for a specific TCP or UDP port that decision will stick.
So if you have a generic SIP on rule 30 and your own definition on rule 40 you will still see the SIP handler act on those connections.
If you put your own definition in rule 28 and have generic SIP in rule 30 then rule 28 will not act on SIP traffic but rule 30 will still act on SIP traffic and do all sorts of magic.
I must admit this is a tricky concept to understand at first but once you understand these basics you can explain a lot of unexpected behaviour in Check Point firewalls.
So far I have not been able to verify this is still how it works with R80.10 and I have yet to add a PABX to my lab. (Actually I have a 3CX PABX but it has some other issues I need to sort out first.)
<< We make miracles happen while you wait. The impossible jobs take just a wee bit longer. >>
11 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
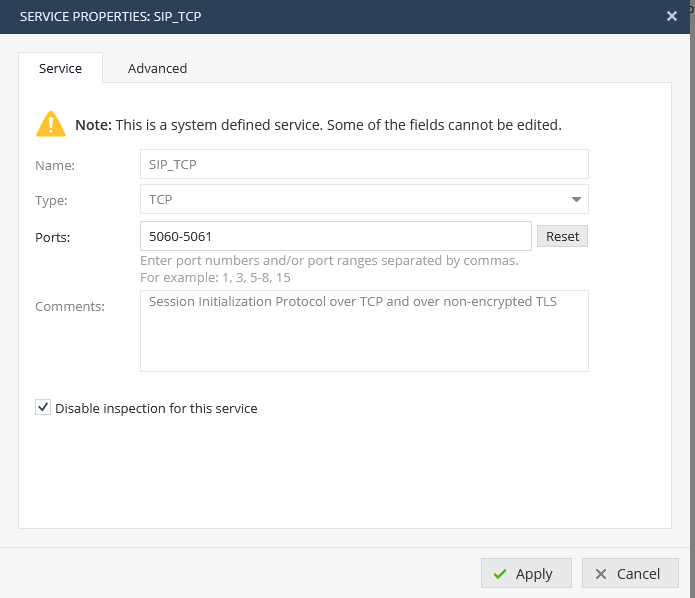
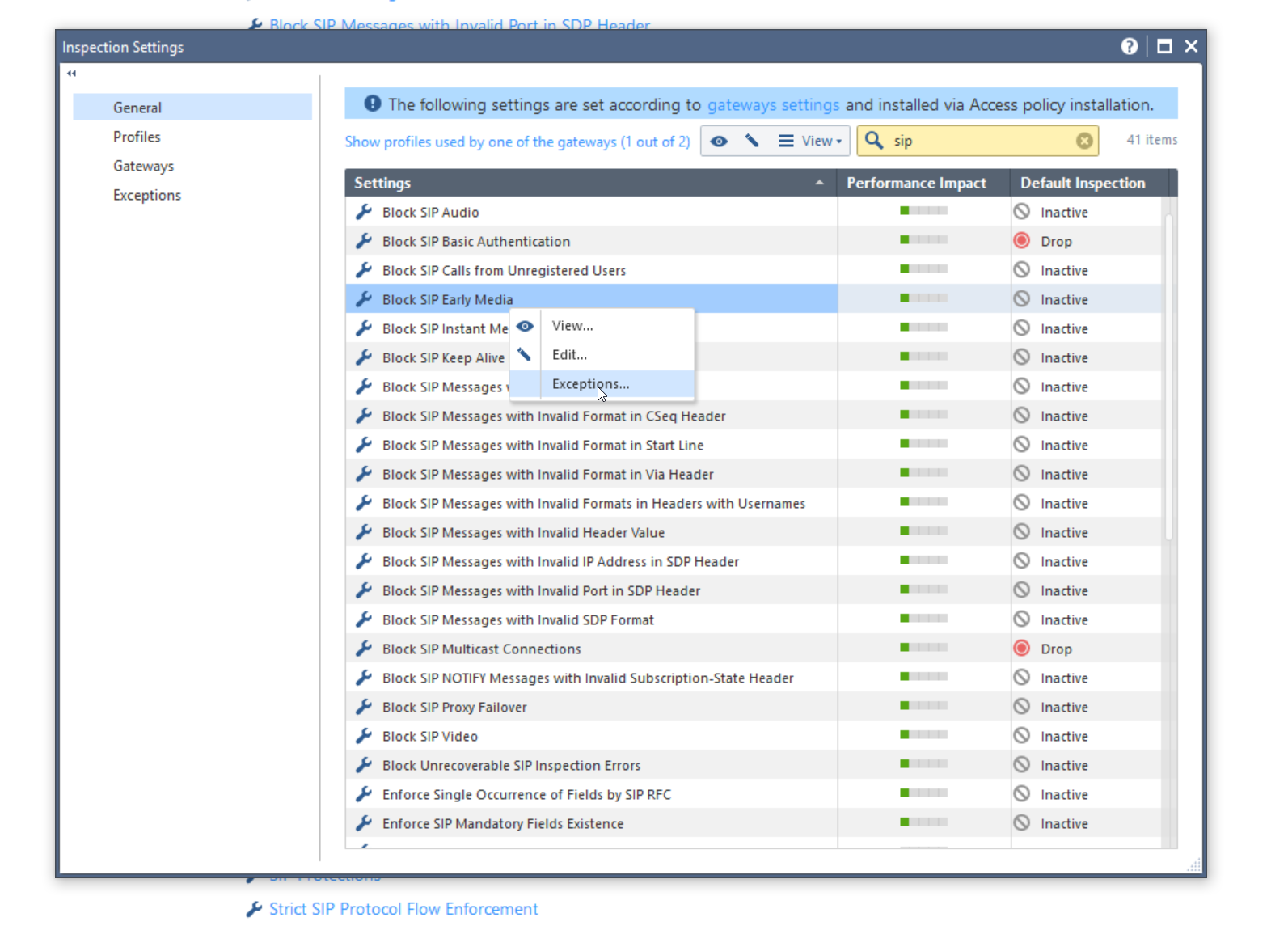
You can do this by creating exception for this inspection setting.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What are the exceptions settings?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You should Disable Inspection for this device in network object menu !
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello
I have a question about security risk from disabling SIP ALG inspection. to disable SIP ALG by creating an exception for Block SIP Early Media on this inspection setting
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
how about 1800 series ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Actually I am not sure Tomer answer will work. After having been on first name bases with R&D VOIP for a year with loads of VOIP tickets in R65 I learned a lot of the background of the code. And I guess most of it is still valid.
At least in R77.30 I always use the following strategy:
- Define your own UDP or TCP object without a protocol handler. For example: Name it SIP-BARE and use UDP/5600
- Make sure you enable "Match for Any" on your own service and disable it on the existing service.
- Make a rule for you own service AND!!!! make sure it is ABOVE any rule that uses the build in SIP services (which contains handlers).
If you forget to put your rule in the right order the whole trick will not work.
As soon as you have a rule that will contain a handler for a specific TCP or UDP port that decision will stick.
So if you have a generic SIP on rule 30 and your own definition on rule 40 you will still see the SIP handler act on those connections.
If you put your own definition in rule 28 and have generic SIP in rule 30 then rule 28 will not act on SIP traffic but rule 30 will still act on SIP traffic and do all sorts of magic.
I must admit this is a tricky concept to understand at first but once you understand these basics you can explain a lot of unexpected behaviour in Check Point firewalls.
So far I have not been able to verify this is still how it works with R80.10 and I have yet to add a PABX to my lab. (Actually I have a 3CX PABX but it has some other issues I need to sort out first.)
<< We make miracles happen while you wait. The impossible jobs take just a wee bit longer. >>
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Your solution should work on R80.10 as well.
Please make sure that voip_multik_enable_forwarding param is off when no SIP inspection needed to avoid heavy performance issues.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Are you replying to Hugo's method or Tomer?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
SIP works on UDP 5060 port.
How to disable SIP ALG inspection in a specific rule in Checkpoint? Also Could this be done globally, like Cisco ASA?
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 13 | |
| 11 | |
| 8 | |
| 6 | |
| 5 | |
| 5 | |
| 5 | |
| 3 | |
| 3 | |
| 3 |
Upcoming Events
Thu 02 May 2024 @ 04:00 PM (CEST)
CheckMates Live DACH - Keine Kompromisse - Sicheres SD-WANThu 02 May 2024 @ 05:00 PM (CEST)
SASE Masters: Deploying Harmony SASE for a 6,000-Strong Workforce in a Single WeekendAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2024 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
Facts at a Glance
User Center