- Products
Quantum
Secure the Network IoT Protect Maestro Management OpenTelemetry/Skyline Remote Access VPN SD-WAN Security Gateways SmartMove Smart-1 Cloud SMB Gateways (Spark) Threat PreventionCloudGuard CloudMates
Secure the Cloud CNAPP Cloud Network Security CloudGuard - WAF CloudMates General Talking Cloud Podcast - Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Quantum (Secure the Network)
- CloudGuard CloudMates
- Harmony (Secure Users and Access)
- Infinity Core Services (Collaborative Security Operations & Services)
- Developers
- Check Point Trivia
- CheckMates Toolbox
- General Topics
- Infinity Portal
- Products Announcements
- Threat Prevention Blog
- CheckMates for Startups
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
May the 4th (+4)
Roadmap Session and Use Cases for
Cloud Security, SASE, and Email Security
SASE Masters:
Deploying Harmony SASE for a 6,000-Strong Workforce
in a Single Weekend
Paradigm Shifts: Adventures Unleashed!
Capture Your Adventure for a Chance to WIN!
Mastering Compliance
Unveiling the power of Compliance Blade
CPX 2024 Content
is Here!
Harmony SaaS
The most advanced prevention
for SaaS-based threats
CheckMates Go:
CPX 2024 Recap
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Quantum
- :
- Security Gateways
- :
- Re: Not substituted certificate in browser Https I...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Not substituted certificate in browser Https Inspection
Hello everyone!
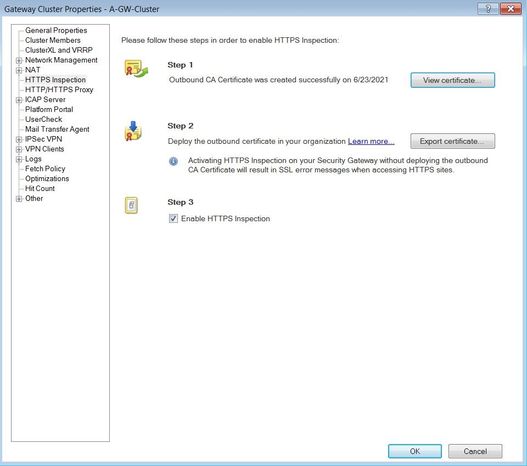
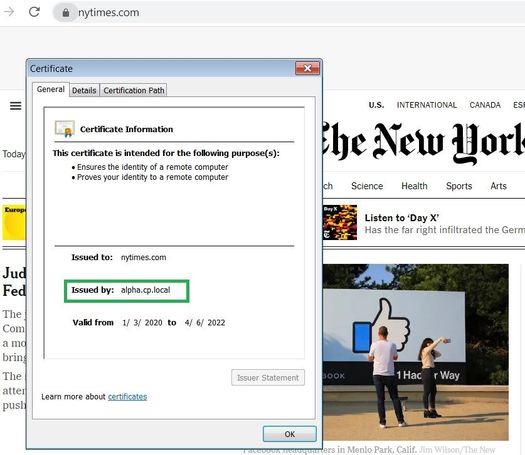
I have Gaia R80.40 distributed deployment (management + clusterXL). I trying enable Https inspection the other day, created self-signed certificate, install this in "trusted root authorities" in Windows machine, but when i open any https site, certificate not substituted in browser.
Please tell me why this can happen?
With Regards, Herman
- Tags:
- https inspection
15 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
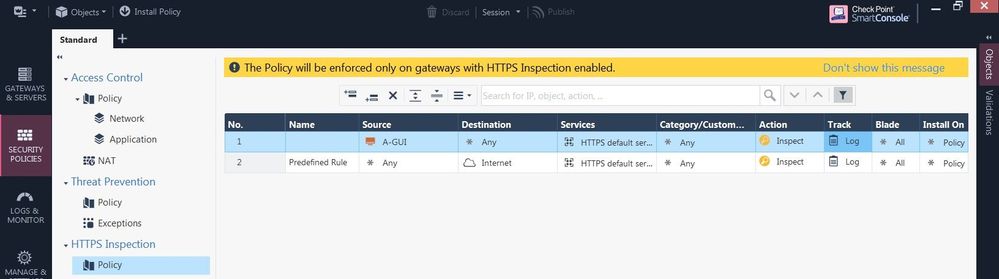
@Wolfgang
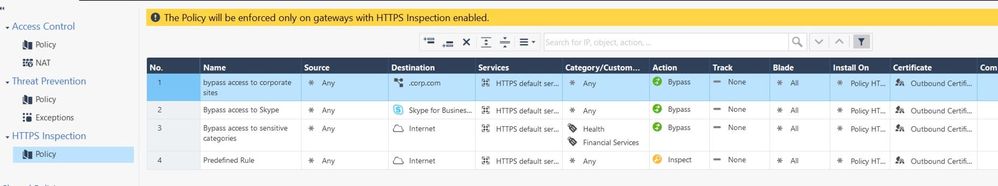
only default predefined rule
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Did you install the policy after enabling HTTPS Inspection in the FW object? 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
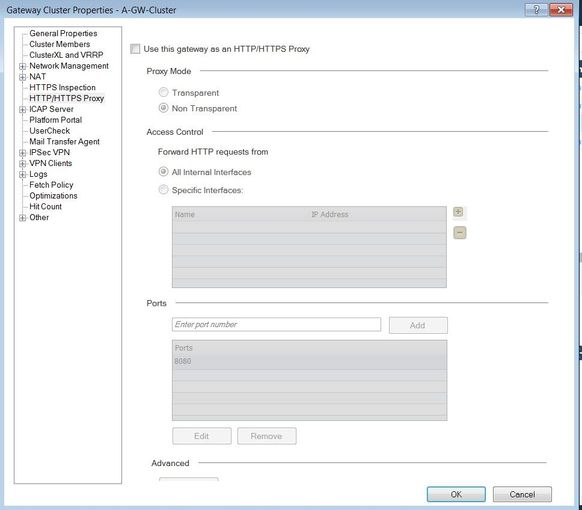
I'm new in checkpoint environment 😁, but if you mean it (see screenshot) then yes
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
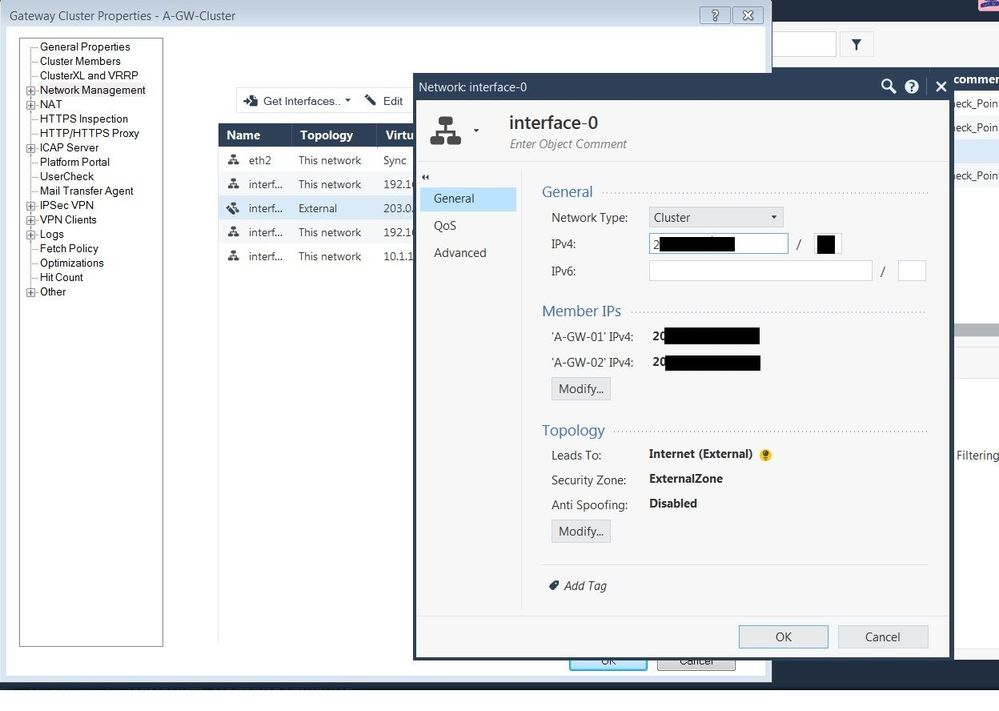
Do you use the gateway as a proxy or transparent proxy? Is the gateway inline en route to the internet? I think the object "Internet" is based on the topology, is your topology correct (edit cluster -> network management -> the interface leading to the WAN should be marked as external) ?
You can set your ssl inspect rule to "log" and create another rule like this below it "Source: any Destination:any Service:any Action:bypass Track:log".
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
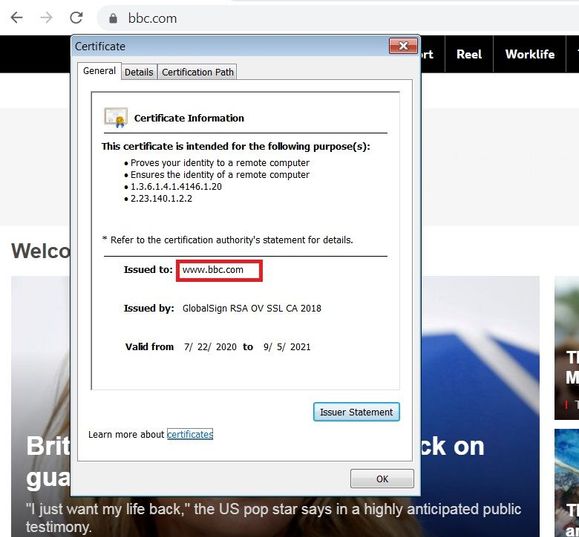
No proxy not used, if i right you understand
Yes, gateway inline en route to the internet. Checked Network topology, and External interface set as External zone (it's has not been mark as External zone), install policy, but it's did not affect
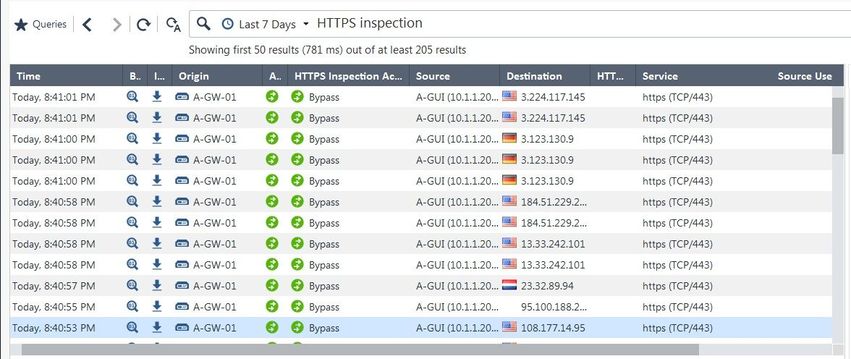
Not sure that right understand, but create bypass "test rule" and enable log tracking:
And now in logs & monitor tab if set filter as HTTPS Inspection may be view this:
But unfortunately certificate not substituted after that
--------
PS English is not my native language, so please be kind to my mistakes )))
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
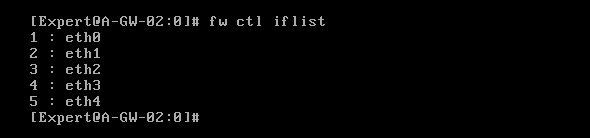
You might wanna redact the public IPs next time and don't worry about your english 🙂 Your Interface names look strange to me, do they match the names as configured on the gateway OS? Can you switch the HTTPS Inspection rules around?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In gateway OS interface have this names, they don't match with names in SmartConsole:
With inspections rules, i try some experiments
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This looks good. HTTPS inspection catches the traffic, but it‘s bypassed regarding your rule. Something with defining the „internet“ as destination in your second rule does work like you want. Have a look at @Danny great post Properly defining the Internet within a security policy
You can try to define another rule first with your client as source and destination any with action „inspect“ to see if this connection will be intercepted.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
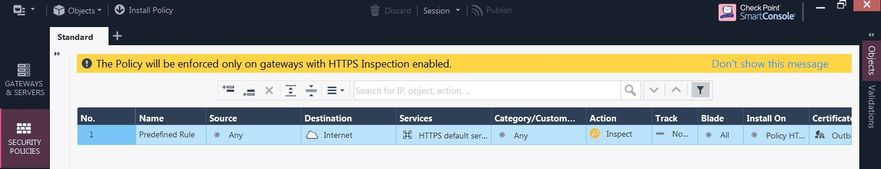
I'm try to define first rule with destination any instead "Internet" for my client machine, but in logs not showing record with "inspect" action for Https inspection. Of course 😀 after create rule and install policy, tried to open some https sites in Chrome
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
By the way, your last rule in the HTTPS Inspection policy should be any any bypass.
Without that, you very likely will have performance issues
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It's another topic but to me in newer versions of the Smart Console it should be the default behaviour with a warning message if it doesn't exist, similar to the message if an inline layer is missing a cleanup rule. It doesn't make sense to have Tech Talks explaining that it's best practices to have any/any/bypass to prevent performance issues due to undefined sessions and have the system out of the box doing the exact opposite, causing issues to unsuspecting customers.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Agree cold heartedly.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I know this may sound like a silly question, but did you make sure that windows machine is actually going through CP firewall? If you do tcpdump -nni host x.x.x.x (with x.x.x.x as windows machine IP address), what do you see? Have you tried another machine or just one? From screenshots you pasted, config looks okay to me.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello everyone!
I fixed this, just add new layer with Application & URL filtering blade in Access Control Policy. Than added three rules and it's work fine
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 14 | |
| 10 | |
| 8 | |
| 5 | |
| 5 | |
| 5 | |
| 3 | |
| 3 | |
| 2 | |
| 2 |
Upcoming Events
Thu 02 May 2024 @ 10:00 AM (CEST)
CheckMates Live BeLux: How Can Check Point AI Copilot Assist You?Thu 02 May 2024 @ 04:00 PM (CEST)
CheckMates Live DACH - Keine Kompromisse - Sicheres SD-WANAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2024 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
Facts at a Glance
User Center