- Products
Quantum
Secure the Network IoT Protect Maestro Management OpenTelemetry/Skyline Remote Access VPN SD-WAN Security Gateways SmartMove Smart-1 Cloud SMB Gateways (Spark) Threat PreventionCloudGuard CloudMates
Secure the Cloud CNAPP Cloud Network Security CloudGuard - WAF CloudMates General Talking Cloud Podcast - Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Quantum (Secure the Network)
- CloudGuard CloudMates
- Harmony (Secure Users and Access)
- Infinity Core Services (Collaborative Security Operations & Services)
- Developers
- Check Point Trivia
- CheckMates Toolbox
- General Topics
- Infinity Portal
- Products Announcements
- Threat Prevention Blog
- CheckMates for Startups
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
Mastering Compliance
Unveiling the power of Compliance Blade
SASE Masters:
Deploying Harmony SASE for a 6,000-Strong Workforce
in a Single Weekend
May the 4th (+4)
Navigating Paradigm Shifts in Cyber
CPX 2024 Content
is Here!
Harmony SaaS
The most advanced prevention
for SaaS-based threats
CheckMates Go:
CPX 2024 Recap
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Quantum
- :
- Management
- :
- Re: Threat Prevention Cyber-attacks dashboard
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Threat Prevention Cyber-attacks dashboard
****************************************************************update****************************************************************
Hey,
few months ago, we started to work the new dashboard for Threat Prevention Investigation methods.
i am happy to announce that we formally released the version for R80.10 under the following SK - sk134634
you are welcome to look on the related post for this release
****************************************************************update****************************************************************
Hey all,
We are considering adding new dashboards to Smart View, and would love your input.
One of them is the ‘Threat Prevention Cyber-attacks dashboard’ divided to business questions:
- Malicious files
- User received malicious files via mail
- User downloaded malicious files from web
- Hosts exploit attempts
- Hosts scanning
- Users surfed to malicious web-sites
- Infected hosts
For each question – we created a drill-down dashboard (by double clicking the number OR text, you will deep-dive to the next dashboard).
By double clicking again on an IOC (Indicator of compromise), you will get the logs of the attack you are interested to see and related to this IOC. The dashboard is divided into prevent & detect sections.
Examples:
FAQ
How can I upload the dashboard into my environment?
- Download the attached file
- Extract the archive
- Click ‘logs and monitor’ -> open a new tab by clicking
 -> click Views -> Actions -> Import Template
-> click Views -> Actions -> Import Template - Import all the files (they are connected to each other in the dashboard)
- Click on the view ‘Cyber Attack View - Beta’ and start to investigate
If I find a malfunction/have a suggestion for one of the views, what should I do?
- You can edit the queries/delete the non-relevant widgets if you find them not relevant for your network.
- Send me a direct mail : orenkor@checkpoint.com with the malfunction/suggestion so we will be able to fix it(please add your SE/Account to the mail + Screen shot for better understanding)
- Comment in this thread
Can I copy some of the widgets into my own dashboard?
Ofcorse – right click the title of the widget and copy it.
For which versions this dashboard is working?
This dashboard was created for R80.10 version and above
For which blades is this dashboard is relevant?
Anti-Bot, Anti-Virus, IPS, Threat Emulation
Thanks,
Oren
Labels
- Labels:
-
Logging
-
Monitoring
-
Reports
-
SmartEvent
56 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Oren
I see. From a security perspective you would like NOT to add this feature.
It would be okay for me, then please use all existing icons that is used all over the Smart Event in the report.. then I would be happy 🙂
Thanks
Kim
Best Regards
Kim
Kim
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
will do ![]()
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Excellent Dashboard, thanks Oren!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Well. Now I have made User Specific report. We can do so many stuff but need to research.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In regards to User or Computer activity it will be really helpful to get a "Forensics" type of report based on time line. The combination of Firewall and the Endpoint Agent can provide a lot of info.
The ideal is to get a "clean" type of report i.e User opened this word document, then visited this news site (omitting or hiding all the other links called from that news site) then watched this video and then opened this excel document...
I do not know technically how hard and what effort will take to get filtered out this info but will provide a helpful tool for many purposes.
CP has the tools (Firewall, Endpoint, SmartEvent), what is missing is for people to ask for it, please vote if you would like to have this kind of Intelligence reports.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I think you will have to wait for r80.20 because CP need to lift the version for the endpoint mgmt server and first then they can integrate endpoint mgmt logs into smartview.
I will agree that looking on a timeline including Secure gate ways logs with the logs from endpoint can provide a better view of what is going on in the network.
Best Regards
Kim
Kim
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is great, but I find the reporting for the App Control and URL Filtering blades really lacking. Can Check Point create some reporting templates for these blades that compare to what other Web Filtering products have out of the box? (Forcepoint, Bluecoat, etc) Things like Top 5 internet users by browse time, and detailed browsing logs for users? Something different than just the standard Access Control reports.
I have created some custom templates, but something official from Check Point would be great. This would help make the case for customers to replace their current web filtering solutions with Check Point.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
For this requirement, we need to make custom report where we need to select URL filtering as blade add tables with Browse Time, Destination, source etc..
Yes it would be good if we have ready template ![]()
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can you please send me there templates so I can review and possibly add them to next release?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I don't mind sharing the templates I created with Check Point as an example, but I'd like to see Check Point create something official (like they did with the Cyber Attack View, GDPR, etc.). If you can provide me with your check point email address, I'll send them over.
Aaron
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
I can see a lot of use for this with our customers, so thanks for sharing.
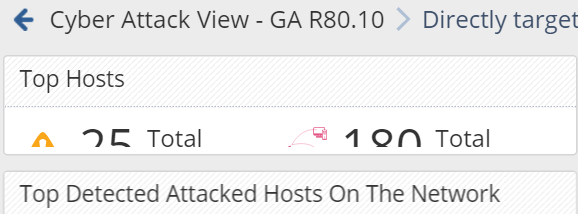
Can I ask I questions over some of the filter logic? On the main screen you have a set of 'Prevented Attacks' infographics which an overall filter of Drop, Reject, Block, Prevent, Redirect. The 'Directly Targeted Hosts' uses this as a a filter to select various blades, excluding some IPS protections. All good so far.
But when you click on it and look at the parent filter on the Directly Targeted Hosts view you see:
(blade:IPS AND action:detect AND...
Is this correct as the Infographic was designed for prevented attacks, not detected attacks. Also, the inherited filter looks for Drop, Reject, Block, Prevent, Redirect - so will this section view ever work
Thanks,
Dave
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
Someone has asked about specific user activity based on time and browsing. Please find below setting which I have done.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hey,
we took it offline in our conversation ![]()
will update in the thread after our session.
Thanks,
Oren
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hey Oren , The template seems to be pretty impressive.
I am facing issue with the font it does not fit into the windows and looks something like the attached screenshots.

If you see that Host Infections , Sandblast section that is how it is displayed.
Few more screenshots.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What are your scaling settings, if viewing this in SmartConsole?
If it is in a browser, try scaling down (zooming out).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I was trying to view in smart console. I tried in the browser it is still the same. In browser after zooming out the view is better. But is there is no way it autoscales based on the application used?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Check your Windows scaling settings for fonts specifically.
I am not sure what else may be causing it in your case.
This is a screenshot of the same on my laptop with 1920x1080:
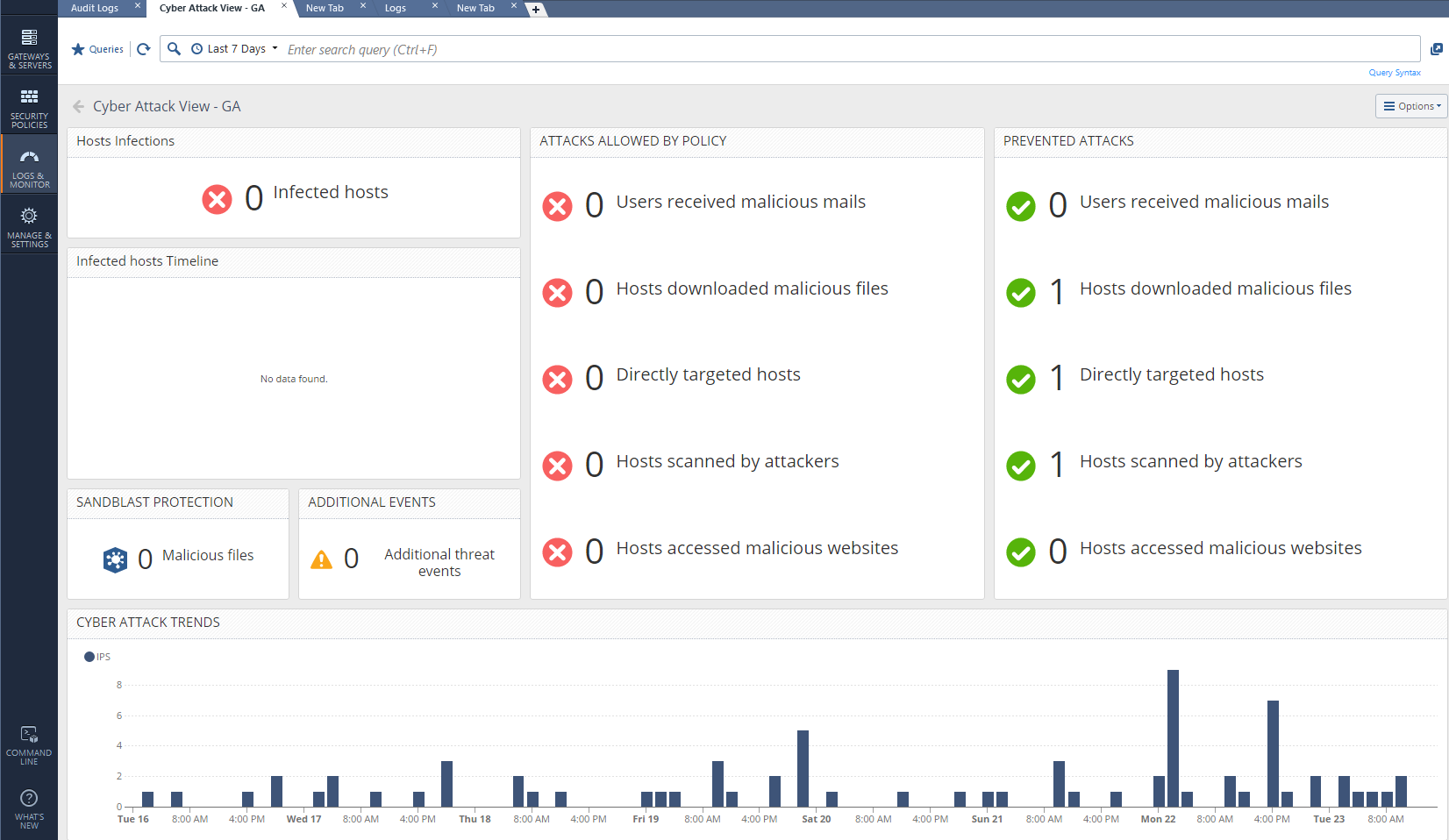
But I do see that the icons and the fonts inside the dashboard are not scalable and it could be an issue if you are running it on a lower resolution display.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you Vladimir. One more query which I have is if I try to export this view in excel sheet , it does not pull up the data but will be blank
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You are correct, the excel export seem to be broken. I am getting the:
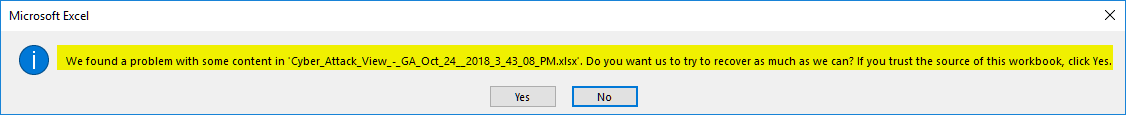
and if I click "Yes" I am informed that the file is corrupted and could not be recovered.
Oren Koren, please have someone look into it.
Thank you,
Vladimir
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hey Gaurav,
Will you be able to share the template which you created?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Any update on the CSV export of this attack template.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Juned,
Please let me know which template you are talking about. Specific user based?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Oren Koren Cyber attach view has stopped working now. If I click on the host infections it does not drill down anymore.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Vladimir Yakovlev - regard exporting, will take it offline and will update
JunedRafeek kittur - can you please share with me more data so i will be able to understand a bit more. have you added something to the queries / change Threat Profile / disable blades in the GW object? (you can share it directly with me orenkor@checkpoint.com) and if needed and your approval, we can have a zoom session and i will have a look in your environment and later on share the relevant insights with the community
Thanks,
Oren
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Appreciate your response. I deleted the Old CPR which I had uploaded and uploaded again and that is working now. I did not change any profile or added any filters. I did enable some new blades I am not sure if that will affect.
I also want to export this in sheet if that is possible.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello Oren,
I am facing the issue again wherein attack view I cannot click on Hosts Infections or Attacks allowed policy. I can just click on Additional threat events and nothing else. We can also do zoom session if you would like to have a look at it.
- « Previous
-
- 1
- 2
- Next »
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 6 | |
| 5 | |
| 5 | |
| 4 | |
| 3 | |
| 3 | |
| 3 | |
| 2 | |
| 2 | |
| 2 |
Upcoming Events
Thu 02 May 2024 @ 04:00 PM (CEST)
CheckMates Live DACH - Keine Kompromisse - Sicheres SD-WANThu 02 May 2024 @ 05:00 PM (CEST)
SASE Masters: Deploying Harmony SASE for a 6,000-Strong Workforce in a Single WeekendAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2024 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
Facts at a Glance
User Center


