- Products
Quantum
Secure the Network IoT Protect Maestro Management OpenTelemetry/Skyline Remote Access VPN SD-WAN Security Gateways SmartMove Smart-1 Cloud SMB Gateways (Spark) Threat PreventionCloudGuard CloudMates
Secure the Cloud CNAPP Cloud Network Security CloudGuard - WAF CloudMates General Talking Cloud Podcast - Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Quantum (Secure the Network)
- CloudGuard CloudMates
- Harmony (Secure Users and Access)
- Infinity Core Services (Collaborative Security Operations & Services)
- Developers
- Check Point Trivia
- CheckMates Toolbox
- General Topics
- Infinity Portal
- Products Announcements
- Threat Prevention Blog
- CheckMates for Startups
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
May the 4th (+4)
Roadmap Session and Use Cases for
Cloud Security, SASE, and Email Security
SASE Masters:
Deploying Harmony SASE for a 6,000-Strong Workforce
in a Single Weekend
Paradigm Shifts: Adventures Unleashed!
Capture Your Adventure for a Chance to WIN!
Mastering Compliance
Unveiling the power of Compliance Blade
CPX 2024 Content
is Here!
Harmony SaaS
The most advanced prevention
for SaaS-based threats
CheckMates Go:
CPX 2024 Recap
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Quantum
- :
- Management
- :
- Re: SecureXL qouta violatation
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jump to solution
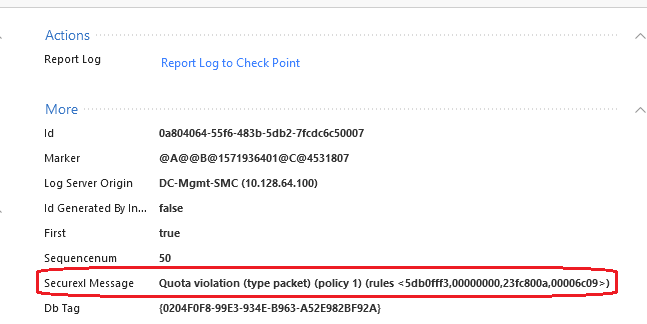
SecureXL qouta violatation
Hello Mates,
Today my website experimented a DDOS attack. I use R80.10 firewall.
When search on smartlog, I see that CP had blocked Malicious IPs but I dont know why CP also blocked almost normal user IPs from internet who normal access to my website.
The log is below:
(P/S: I do not use Network quota of IPS blade)
Please help to explain!!!
1 Solution
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank phone boy,
After I issue command : fw samp del "uuid" ; the samp rule STILL has effect. Then I search on below link; they said we need more command to actual delete samp rule:
fw samp add -t 2 quota flush true (I did and now actually deleted samp rule)
Link : https://sc1.checkpoint.com/documents/R77/CP_R77_SecurityGatewayTech_WebAdmin/96330.htm
P/S : I am still looking for command to limit number of connections for EACH IP client to connect to my website
Thanks!
8 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Have a look at sk103154 and sk112454. Did you implement rate limiting or custom IP feeds?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
Also in my case, CP block almost all normal IP, which access my website, not only some known malicious IPs as in sk103154.
I dont use rate limit connection :
[Expert@DC-Internet-Fw-01:0]# fw samp get
Get operation succeeded
no corresponding SAM policy requests
[Expert@DC-Internet-Fw-01:0]#
After I manual blocked malicious IPs from DDOS by adding rule in rulebase, the internet users can access my website normally
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
what output you see when run "fw samp get"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
The output here
[Expert@DC-Internet-Fw-01:0]# fw samp get
Get operation succeeded
no corresponding SAM policy requests
[Expert@DC-Internet-Fw-01:0]#
Before the dropping happen, I issue command:
fw samp add -a d -l r quota service 6/443 source any destination cidr:<MY_WEBSITE_IP> concurrent-conns 50 flush true
but I deleted it right after with "fw samp del "uuid"
So, i dont know if this command has still have effect?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The above command would cause the log you mentioned.
It would also apply for ALL traffic to your webserver, even if it was from a trusted IP.
Are those logs still generated from the time AFTER you deleted the samp rule?
It would also apply for ALL traffic to your webserver, even if it was from a trusted IP.
Are those logs still generated from the time AFTER you deleted the samp rule?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank phone boy,
After I issue command : fw samp del "uuid" ; the samp rule STILL has effect. Then I search on below link; they said we need more command to actual delete samp rule:
fw samp add -t 2 quota flush true (I did and now actually deleted samp rule)
Link : https://sc1.checkpoint.com/documents/R77/CP_R77_SecurityGatewayTech_WebAdmin/96330.htm
P/S : I am still looking for command to limit number of connections for EACH IP client to connect to my website
Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm pretty sure you cannot limit the number of connections to a destination IP address individually by unique source address in a single rule with fw samp in R80.10 and earlier. Doesn't look possible in R80.20+ either. The best you could do is specify multiple rules with different ranges or networks of source IPs and have a concurrent connection limit for each of those individual rules matching the same destination. The SAM rule matching here is relatively simple, and doesn't really track stateful elements like the number of concurrent connections to a destination by individual source address.
Gateway Performance Optimization R81.20 Course
now available at maxpowerfirewalls.com
now available at maxpowerfirewalls.com
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I believe you can pass "track source" as a parameter to the command.
This should track per source IP versus per rule.
This should track per source IP versus per rule.
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 6 | |
| 3 | |
| 3 | |
| 2 | |
| 2 | |
| 2 | |
| 2 | |
| 1 | |
| 1 | |
| 1 |
Upcoming Events
Thu 25 Apr 2024 @ 11:00 AM (CEST)
CheckMates in Russian - Возможности и риски искусственного интеллектаThu 25 Apr 2024 @ 11:00 AM (CEST)
CheckMates in Russian - Возможности и риски искусственного интеллектаThu 02 May 2024 @ 10:00 AM (CEST)
CheckMates Live BeLux: How Can Check Point AI Copilot Assist You?About CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2024 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
Facts at a Glance
User Center