- Products
Quantum
Secure the Network IoT Protect Maestro Management OpenTelemetry/Skyline Remote Access VPN SD-WAN Security Gateways SmartMove Smart-1 Cloud SMB Gateways (Spark) Threat PreventionCloudGuard CloudMates
Secure the Cloud CNAPP Cloud Network Security CloudGuard - WAF CloudMates General Talking Cloud Podcast - Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Quantum (Secure the Network)
- CloudGuard CloudMates
- Harmony (Secure Users and Access)
- Infinity Core Services (Collaborative Security Operations & Services)
- Developers
- Check Point Trivia
- CheckMates Toolbox
- General Topics
- Infinity Portal
- Products Announcements
- Threat Prevention Blog
- CheckMates for Startups
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
May the 4th (+4)
Roadmap Session and Use Cases for
Cloud Security, SASE, and Email Security
SASE Masters:
Deploying Harmony SASE for a 6,000-Strong Workforce
in a Single Weekend
Paradigm Shifts: Adventures Unleashed!
Capture Your Adventure for a Chance to WIN!
Mastering Compliance
Unveiling the power of Compliance Blade
CPX 2024 Content
is Here!
Harmony SaaS
The most advanced prevention
for SaaS-based threats
CheckMates Go:
CPX 2024 Recap
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Quantum
- :
- Threat Prevention
- :
- Re: meaning of Anti-virus blade Log "Action detail...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
meaning of Anti-virus blade Log "Action details = bypass"
Hello Checkmates,
Can you help me understand the value "bypass" under column M "Action details" in the Anti-virus blade Log. And why the traffic was allowed although the rule was to prevent?
The Threat Prevention rule of the Anti-Virus and Anti-Bot rule for "Confidence Level = High" and "severity = High" is to prevent but the traffic was allowed with action "Detect".
| Time | Type | Action | Resource | Protection Name | Destination | Confidence Level | Severity | Blade | Protection Type | Malware Action | Correlation Unit Category | Action Details |
| May 4, 2020 2:36:25 PM | Correlated | Detect | http://googe[.]com/ | Phishing_website.TC.xyuns | 162.243.10.151 | High | High | Anti-Virus | URL Reputation | Access to site known to contain malware | Legacy;Threat Prevention | bypass |
| May 4, 2020 2:36:24 PM | Log | Detect | http://googe[.]com/ | Phishing_website.TC.xyuns | 162.243.10.151 | High | High | Anti-Virus | URL Reputation | Access to site known to contain malware | bypass |
14 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
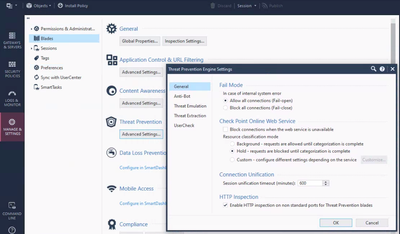
Is the gateway set to Hold or Background?
I could see that happening if set to Background, where there may be a delay before the gateway receives the exact classification and the connection was short (and thus couldn't be prevented in time).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Spot on! - it is set to Background.
What are the pros and cons of setting it to Hold. What is the average delay of a hold?
Thanks
FM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
It's explained here: https://sc1.checkpoint.com/documents/R80.40/WebAdminGuides/EN/CP_R80.40_ThreatPrevention_AdminGuide/...
Let us know if you have any further questions.
It's explained here: https://sc1.checkpoint.com/documents/R80.40/WebAdminGuides/EN/CP_R80.40_ThreatPrevention_AdminGuide/...
Let us know if you have any further questions.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I read the general description of the three different options, but what i am looking for is an expert's insight about setting the Resource categorization mode to "Hold" -- is the latency noticeable to the end user?
- Hold - connections are blocked until categorization is complete - When a connection cannot be categorized with the cached responses, it remains blocked until the Check Point Online Web Service completes categorization.
Thank you
FM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It can be, yes, depending on the circumstances.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We finally changed the setting to HOLD on 2020-07-23 but it allowed 3 in Detect in stead of Prevent. See attached screen capture showing the resource Categorization setting as "Hold"; and a table showing the allowed traffic in Background mode. The traffic fulfill the conditions for the traffic to "Prevented"--Confidence level = "High" and Severity "High" or "Critical". Can you tell me why the vendor list value for one of the events is blank?
| Time | Malware Action | Vendor List | Description |
| Jul 29, 2020 2:04:34 PM | Malicious file/exploit download | ||
| Jul 29, 2020 2:04:31 PM | Malicious file/exploit download | Check Point ThreatCloud | Connection was allowed because background classification mode was set. See sk74120 for more information. |
| Jul 29, 2020 12:43:28 PM | Malicious file/exploit download | Check Point ThreatCloud | Connection was allowed because background classification mode was set. See sk74120 for more information. |
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Did you push policy after making that change?
If so, you may want to involve the TAC.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am waiting for the Network admin to confirm if he did "Push Policy".
If it has the same effect? we did "Push Policy" after our weekly IDS protection rule update on Wed 7/29/2020 6:10 PM-- the time of the push policy was after the 3 events that were allowed at Jul 29, 2020 2:04:34 PM and could not have applied.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Pretty sure changing the profile requires an explicit policy push versus the automatic update of IPS signatures, which doesn't require an explicit policy push to take effect.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
A side question for you, perhaps you can help.
Some traffic on Anti-bot blade I am monitoring is currently allowing traffic through as Detect and not Prevent even though the gateway is set to 'Hold' and not 'Background'. The Threat Prevention policy is also set to Prevent. I found no exceptions that could interfere with this. On R80.30 btw
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
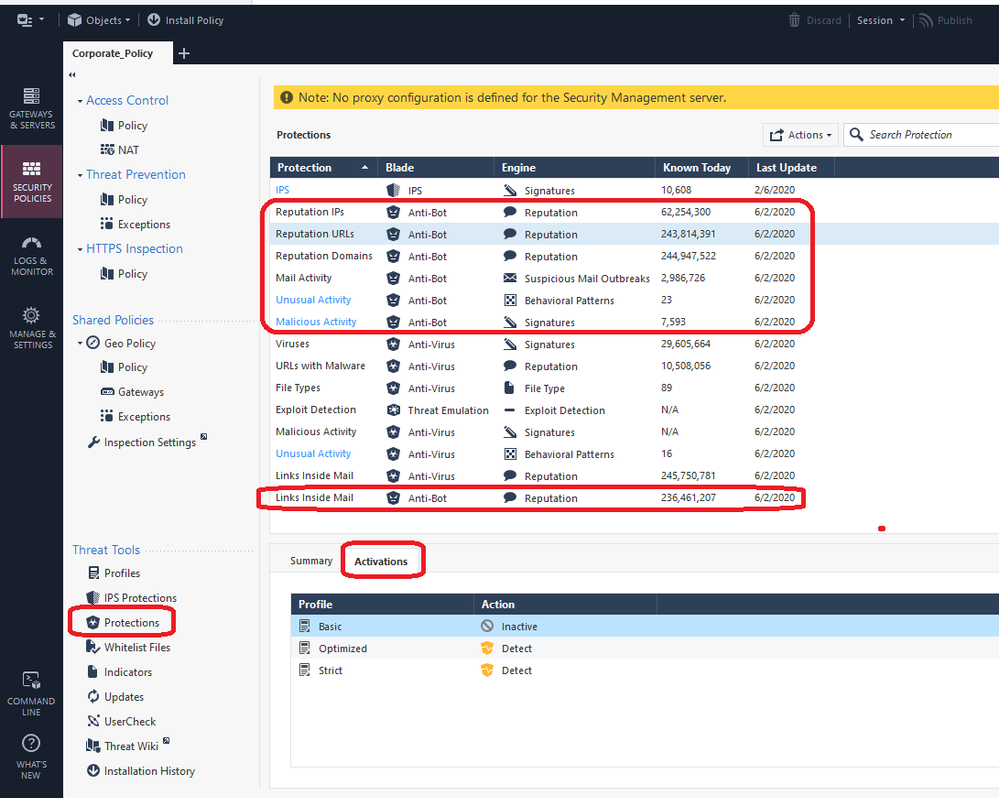
Need to see the redacted log card for this event to assist. In the meantime, check the Activations tab for all the circled Protection classes below:
Gateway Performance Optimization R81.20 Course
now available at maxpowerfirewalls.com
now available at maxpowerfirewalls.com
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
According to the log, the protection type is listed as 'DNS Reputation'.
In the menu you showed above, I do not have a protection with this name. I have only the ones you circled in red.
In the menu you showed above, I do not have a protection with this name. I have only the ones you circled in red.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Pretty sure DNS Reputation is part of "Reputation Domains" or possibly "Reputation IPs". And the Activations for these two categories are set to what for your TP profiles?
Gateway Performance Optimization R81.20 Course
now available at maxpowerfirewalls.com
now available at maxpowerfirewalls.com
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Both categories are set to Prevent.
I did find another source that says that DNS Reputation will always be set to Detect and this config can't be changed.
Perhaps this is the cause?
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 3 | |
| 1 | |
| 1 | |
| 1 |
Upcoming Events
Thu 25 Apr 2024 @ 11:00 AM (CEST)
CheckMates in Russian - Возможности и риски искусственного интеллектаThu 25 Apr 2024 @ 11:00 AM (CEST)
CheckMates in Russian - Возможности и риски искусственного интеллектаThu 02 May 2024 @ 10:00 AM (CEST)
CheckMates Live BeLux: How Can Check Point AI Copilot Assist You?Thu 02 May 2024 @ 04:00 PM (CEST)
CheckMates Live DACH - Keine Kompromisse - Sicheres SD-WANAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2024 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
Facts at a Glance
User Center