- Products
- Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- Bulgaria
- Cyprus
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
Step Into the Future of
AI-Powered Cyber Security
The State of Ransomware Q1 2026
Key Trends and Their Impact
AI Security Masters E8:
Claude Mythos: New Era in Cyber Security
Blueprint Architecture for Securing
The AI Factory & AI Data Center
Call For Papers
Your Expertise. Our Stage
CheckMates Go:
CheckMates Fest
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- General Topics
- :
- The difference between checkpoint creation domain ...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The difference between checkpoint creation domain and Custom Applications/Sites creation URL
Hello, engineers, I would like to know the workflow difference between creating domain and Custom Applications/Sites to create urls
13 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
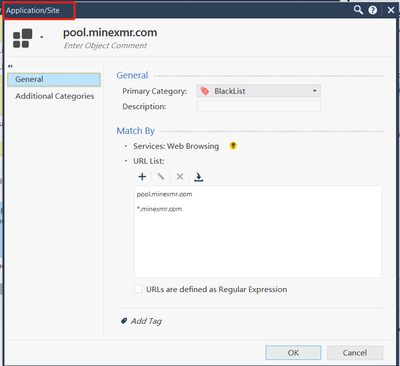
A Custom Application/Site can only be used in an Application policy and column, where the get url command is compared to the URL in the custom Application.
A domain object is used in a source or destination field where the gateway does a resolution of the domain name to IP addresses and then looks if the IP hitting the gateway is in the domain resolution list.
A domain object is used in a source or destination field where the gateway does a resolution of the domain name to IP addresses and then looks if the IP hitting the gateway is in the domain resolution list.
Regards, Maarten
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Okay, thank you very much. Is there an official document describing this problem?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
this is not really a problem, these are just completely different approaches of how to allow something, the one is handled by the FW blade and the other by the URLF blade.
Regards, Maarten
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
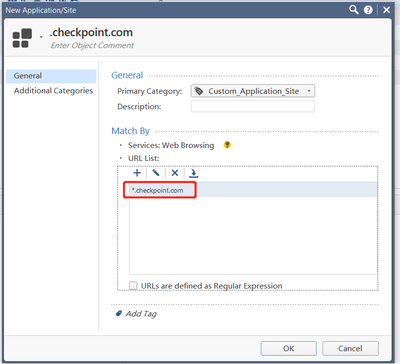
For example, I want to visit ".checkpoint.com" to use the Domain for configuration or the Custom Applications/Sites creation URL?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
For example, I want to visit ".checkpoint.com" to use the Domain for configuration or the Custom Applications/Sites creation URL?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
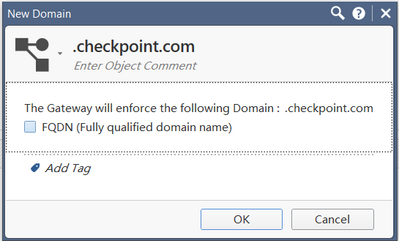
If it is only the site checkpoint.com (and not www.checkpoint.com or somethingelse.checkpoint.com), then you can use a FQDN Domain Object, as that works on being able to resolve checkpoint.com to an IP address.
Non-FQDN Domain Objects rely on being able to reverse-resolve the IP address being accessed to a name that has checkpoint.com in it.
This rarely works in the modern Internet.
The App Control approach works for HTTP/HTTPS traffic.
For HTTPS sites, Categorize HTTPS Sites needs to be enabled and/or HTTPS Inspection must be enabled.
Categorize HTTPS Sites will work much better on R80.40 (or R80.20/R80.30 with latest GA JHF) due to added support for SNI.
Non-FQDN Domain Objects rely on being able to reverse-resolve the IP address being accessed to a name that has checkpoint.com in it.
This rarely works in the modern Internet.
The App Control approach works for HTTP/HTTPS traffic.
For HTTPS sites, Categorize HTTPS Sites needs to be enabled and/or HTTPS Inspection must be enabled.
Categorize HTTPS Sites will work much better on R80.40 (or R80.20/R80.30 with latest GA JHF) due to added support for SNI.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm very sorry, but I still don't understand. Could you tell me more details? Thank you very much。
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
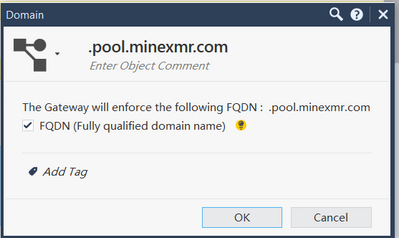
In very simple terms, a Domain Object attempts to make an association between a DNS name and an IP address.
- An FQDN Domain Object translates the FQDN to an IP address.
- A non-FQDN Domain Object confirms that an IP address is associated with a given domain by doing a reverse DNS lookup
You can use a Domain Object in the rulebase similar to a host object that represents a single IP address.
As such, it can be used in a pure firewall rulebase without App Control or other advanced blades as it doesn't require any Layer 7 inspection.
The (reverse) DNS resolution effectively happens "out of band."
This approach has a couple limitations:
- These objects only work with IPv4, if I remember correctly.
- Many sites actually share the same IPv4 address and you'd be allowing (or blocking) all of those sites if you use these objects in a rule.
- Non-FQDN Domain Objects incur a fairly significant performance penalty and, in the end, usually doesn't work as the reverse DNS rarely matches the DNS name you're trying to match (if such records even exist at all).
An Application/Site is effectively an App Control signature that operates at Layer 7.
It's a fairly simplistic App Control signature that identifies that traffic is:
- Web-based (i.e. regular HTTP or HTTPS)
- Is destined to one of the domains you've listed in the definition.
If the traffic is not web-based and/or App Control can't determine it's destined for one of the domains listed, then it will not match the traffic.
There are reasons that both approaches are available.
You have to use the one that is appropriate for the problem you're trying to solve.
The more information you can provide about your environment and precisely what your goal is, the more likely we can tell you what approach will work best.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you very much for your reply
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hey Daemon, I should have asked you this one 20 years ago. I kept meaning to test it to see how it operated, but it was never important enough to spend the time on.... I mean, who actually USES domain objects? I have some follow up questions for clarity if I may...
- When did the FQDN checkbox appear? Was it always there?
- I thought the prefixed "." differentiated whether it was a forward or reverse lookup... is this true?
- Did it ALWAYS have both forward and reverse options?
- With reverse lookup, when does the lookup take place? What process does it? While the lookup is happening, is it a default match, no match, or are connections held?
- Finally, any insight on why the third option is not provided that some other firewalls offer, which is to cache relevant forward lookups that the firewalls sees passing through and use them to inform a list of possible IP addresses?
Thanks! Hope you're well 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The FQDN checkbox (and related functionality) appeared in R80.10.
The . in front of the name also premiered in R80.10.
Without FQDN, the packet is held while the lookup takes place.
Don't recall what process is doing it.
Caching DNS lookups happening through the gateway is an R80.40 feature, but only to ones the gateway is configured to trust--either to same DNS server gateway uses or specific DNS objects created in SmartConsole.
The . in front of the name also premiered in R80.10.
Without FQDN, the packet is held while the lookup takes place.
Don't recall what process is doing it.
Caching DNS lookups happening through the gateway is an R80.40 feature, but only to ones the gateway is configured to trust--either to same DNS server gateway uses or specific DNS objects created in SmartConsole.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Also, look here: https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solut...
It sums up the case quite well
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Why hostnames are not supported by FQDN domain objects? So why I could create .checkpoint.com and not .community.checkpoint.com?
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 5 | |
| 4 | |
| 4 | |
| 3 | |
| 3 | |
| 3 | |
| 3 | |
| 3 | |
| 2 | |
| 2 |
Upcoming Events
Tue 12 May 2026 @ 10:00 AM (CEST)
The Cloud Architects Series: Check Point Cloud Firewall delivered as a serviceWed 13 May 2026 @ 11:00 AM (EDT)
TechTalk: The State of Ransomware Q1 2026: Key Trends and Their ImpactThu 14 May 2026 @ 07:00 PM (EEST)
Under the Hood: Presentando Check Point Cloud Firewall como ServicioTue 12 May 2026 @ 10:00 AM (CEST)
The Cloud Architects Series: Check Point Cloud Firewall delivered as a serviceAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2026 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
About Us
UserCenter