I love the new colors - great job!
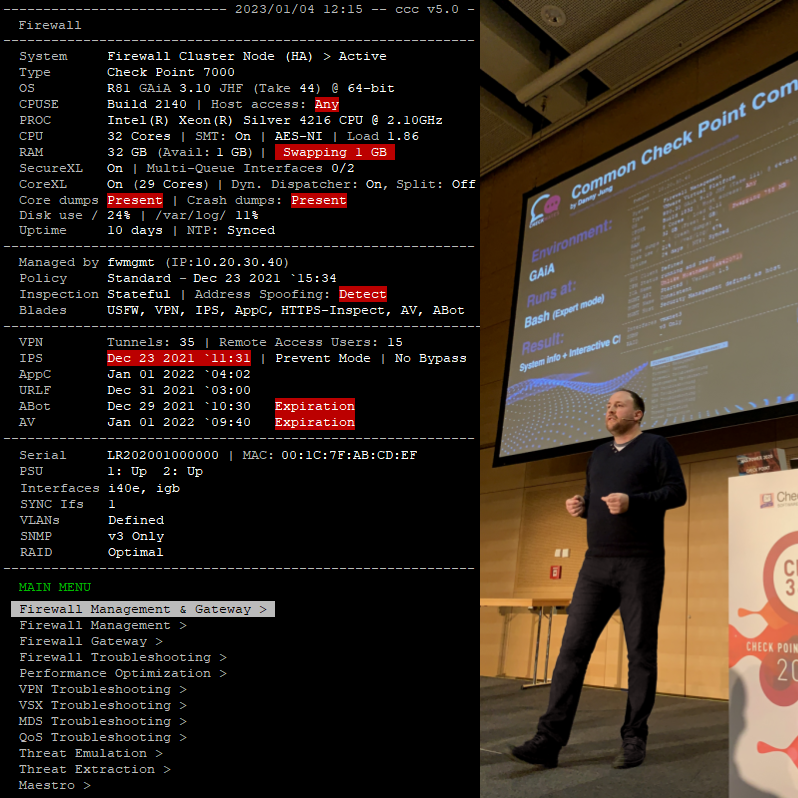
At the moment the script shows all commands an all devices even if there are no relevant blades active on the device where you are executing the script.
For example: with "enabled_blades" you can check if vpn is active or not. If not you do not need th offer vpn relevant commands.
The same I can imagine with ips, threatemulation etc...
BTW: I am missing threatemulation commands. Do you need some? 
Further it would be helpful to identify when the script starts if the system where the script is running on is a management, a log server or a gateway.
If it is a gateway: is it a cluster, is it vsx and which blades are active?
With this set of information you can choose which commands you will show in the menu.
Maybe I can build some code on the weekend.
Cheers
Sven