- Products
- Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- Bulgaria
- Cyprus
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
Stop Babysitting Rules.
Go Agentic
Step Into the Future of
AI-Powered Cyber Security
The State of Ransomware Q1 2026
Key Trends and Their Impact
AI Security Masters E8:
Claude Mythos: New Era in Cyber Security
Blueprint Architecture for Securing
The AI Factory & AI Data Center
Call For Papers
Your Expertise. Our Stage
CheckMates Go:
CheckMates Fest
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Hybrid Mesh
- :
- Firewall and Security Management
- :
- Re: Configure Public IP address directly on a serv...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Jump to solution
Configure Public IP address directly on a server behind Checkpoint
Hi Everyone,
We are in process of implementing Mitel MiCollab and the requirement is the WAN interface of the Micollab server should have public ip assigned directly on it. NATting from public ip to private ip does not support.
The MiCollab server is a VM behind the Checkpoint.
How could I achieve this setup with Checkpoint?
Thank you.
1 Solution
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Chris_Atkinson wrote:
Having public address on only the external interface cannot achieve this if the objective is not to use NAT.
Sure you can. It's really easy.
- Pick a new network which will contain the MiCollab box. It can be private, and should be at least a /30 for a single firewall or a /29 for a two-member cluster.
- Assign an IP in this network for the firewall. If using a cluster, also assign an IP for each member.
- Assign the public IP to the MiCollab box.
- Set the MiCollab box's default route to the private IP on the firewall's interface.
- Add a 32-bit interface route pointing the public address out the firewall's interface connected to the network with the MiCollab box. The command to add this route will look like this:
set static-route 1.2.3.4/32 nexthop gateway logical eth1.2345 on
Due to a complicated set of requirements, I have a firewall which works like this in my environment. It's a bit weird to get used to, but pretty solid.
12 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
setup a DMZ
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
As Val has hinted another interface/VLAN from the Check Point addressed with the public subnet and configuration pertinent for a DMZ.
CCSM R77/R80/ELITE
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you all for your comments.
Sorry I am new to Checkpoint so needing your help further.
We currently have DMZ with a different subnet.
All public IPs have been forwarded to External on a bond Interface.
So I don't know how another DMZ network/Interface will work as what would be the IP address/subnet for them?. What I am understanding is each Interface should have a different subnet.
Could you please help explaining further?
Thank you very much.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Having public address on only the external interface cannot achieve this if the objective is not to use NAT.
The vendor of Firewall doesn't matter in this context.
Does the existing DMZ have/use public addresses (Y/N)?
Yes - Connect the Mitel here with an IP from that subnet.
No - You will likely have to create a new DMZ involving networking/routing changes & possibly requesting extra or new IP addresses from your ISP.
CCSM R77/R80/ELITE
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Chris_Atkinson wrote:
Having public address on only the external interface cannot achieve this if the objective is not to use NAT.
Sure you can. It's really easy.
- Pick a new network which will contain the MiCollab box. It can be private, and should be at least a /30 for a single firewall or a /29 for a two-member cluster.
- Assign an IP in this network for the firewall. If using a cluster, also assign an IP for each member.
- Assign the public IP to the MiCollab box.
- Set the MiCollab box's default route to the private IP on the firewall's interface.
- Add a 32-bit interface route pointing the public address out the firewall's interface connected to the network with the MiCollab box. The command to add this route will look like this:
set static-route 1.2.3.4/32 nexthop gateway logical eth1.2345 on
Due to a complicated set of requirements, I have a firewall which works like this in my environment. It's a bit weird to get used to, but pretty solid.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks Bob, I was making an assumption from what was said that routing changes were out of scope or not possible due to the size of the existing external subnet.
CCSM R77/R80/ELITE
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Bob,
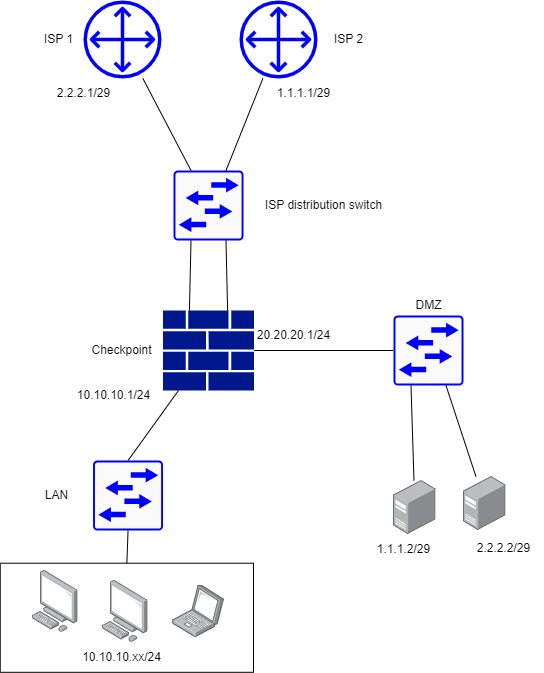
I'm fairly new with checkpoint, i just have few clarifications with this solution. let me know if my assumptions are correct.
4. I am using a layer 2 switch on the DMZ, would this solution still work
5. Im a bit confused on the command will it be something like this based on the diagram
set static-route 1.1.1.2/32 nexthop gateway logical eth.xx (WAN) on
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
4. Yes, you would need to use a switch. Having a router in the path makes things a bit more complicated, but still possible.
5. You don't have interface names on that diagram, but it would be 'set static-route 1.1.1.2/32 nexthop gateway logical <interface leading to the switch labeled DMZ> on'. You would then need to set the default route on 1.1.1.2 to be the cluster VIP on that interface. You should not use a public IP for that VIP.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
btw, this is not a part of a cluster. so it would be something like this ? since I dont have any VIP
'set static-route 1.1.1.2/32 nexthop gateway eth3 (20.20.20.1 interface) on'
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
set static-route 1.1.1.2/32 nexthop gateway logical eth3 on
And remember, you need to set the endpoint's default route to the firewall's address on eth3. You may also need to give the endpoint a route to the firewall's address telling it to go out a particular interface. The right way to set all that up depends on the OS on the endpoint.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Depending on the size of your public IP network, this could be accomplished by breaking it into smaller subnets.
Create DMZ using one of the small subnets with public IPs and place your Mitel unit in it.
You will have to configure static routes on the ISP router to forward traffic destined to individual subnets to use Check Point's external IP as the gateway.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you @Bob_Zimmerman , @Chris_Atkinson and everyone for tipping the idea.
I now understand how it can be done. It is more complicated that I first thought where it could be just simply a special config in Checkpoint to bridge the traffic directly to Micollab in DMZ.
Will need to involve more parties into the solution.
Much appreciated.
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 19 | |
| 18 | |
| 9 | |
| 9 | |
| 8 | |
| 7 | |
| 5 | |
| 5 | |
| 4 | |
| 4 |
Upcoming Events
Fri 29 May 2026 @ 09:00 AM (EDT)
Caracas: Executive Breakfast: Innovación en Ciberseguridad – IA y Threat IntelligenceTue 02 Jun 2026 @ 10:00 AM (AEST)
The Cloud Architect Series: Check Point WAF. The next generation of AI-Powered Protection - APACTue 02 Jun 2026 @ 06:00 PM (IDT)
Under the Hood | Check Point SASE: Identity Integration & Access Policy Design Best PracticesTue 02 Jun 2026 @ 10:00 AM (AEST)
The Cloud Architect Series: Check Point WAF. The next generation of AI-Powered Protection - APACTue 02 Jun 2026 @ 06:00 PM (IDT)
Under the Hood | Check Point SASE: Identity Integration & Access Policy Design Best PracticesThu 04 Jun 2026 @ 02:00 PM (CEST)
Deep Dive Webinar: New CloudGuard GWLB Deployment Without NAT Gateways - EuropeThu 04 Jun 2026 @ 07:00 PM (IDT)
Deep Dive Webinar: New CloudGuard GWLB Deployment Without NAT Gateways - AmericaFri 29 May 2026 @ 09:00 AM (EDT)
Caracas: Executive Breakfast: Innovación en Ciberseguridad – IA y Threat IntelligenceAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2026 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
About Us
UserCenter