- Products
Quantum
Secure the Network IoT Protect Maestro Management OpenTelemetry/Skyline Remote Access VPN SD-WAN Security Gateways SmartMove Smart-1 Cloud SMB Gateways (Spark) Threat PreventionCloudGuard CloudMates
Secure the Cloud CNAPP Cloud Network Security CloudGuard - WAF CloudMates General Talking Cloud Podcast - Learn
- Local User Groups
- Partners
- More
This website uses Cookies. Click Accept to agree to our website's cookie use as described in our Privacy Policy. Click Preferences to customize your cookie settings.
- Products
- Quantum (Secure the Network)
- CloudGuard CloudMates
- Harmony (Secure Users and Access)
- Infinity Core Services (Collaborative Security Operations & Services)
- Developers
- Check Point Trivia
- CheckMates Toolbox
- General Topics
- Infinity Portal
- Products Announcements
- Threat Prevention Blog
- CheckMates for Startups
- Learn
- Local User Groups
- Upcoming Events
- Americas
- EMEA
- Czech Republic and Slovakia
- Denmark
- Netherlands
- Germany
- Sweden
- United Kingdom and Ireland
- France
- Spain
- Norway
- Ukraine
- Baltics and Finland
- Greece
- Portugal
- Austria
- Kazakhstan and CIS
- Switzerland
- Romania
- Turkey
- Belarus
- Belgium & Luxembourg
- Russia
- Poland
- Georgia
- DACH - Germany, Austria and Switzerland
- Iberia
- Africa
- Adriatics Region
- Eastern Africa
- Israel
- Nordics
- Middle East and Africa
- Balkans
- Italy
- APAC
- Partners
- More
- ABOUT CHECKMATES & FAQ
- Sign In
- Leaderboard
- Events
May the 4th (+4)
Roadmap Session and Use Cases for
Cloud Security, SASE, and Email Security
SASE Masters:
Deploying Harmony SASE for a 6,000-Strong Workforce
in a Single Weekend
Paradigm Shifts: Adventures Unleashed!
Capture Your Adventure for a Chance to WIN!
Mastering Compliance
Unveiling the power of Compliance Blade
CPX 2024 Content
is Here!
Harmony SaaS
The most advanced prevention
for SaaS-based threats
CheckMates Go:
CPX 2024 Recap
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- CheckMates
- :
- Products
- :
- Harmony
- :
- Endpoint
- :
- Wildcards in custom Apps
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Are you a member of CheckMates?
×
Sign in with your Check Point UserCenter/PartnerMap account to access more great content and get a chance to win some Apple AirPods! If you don't have an account, create one now for free!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
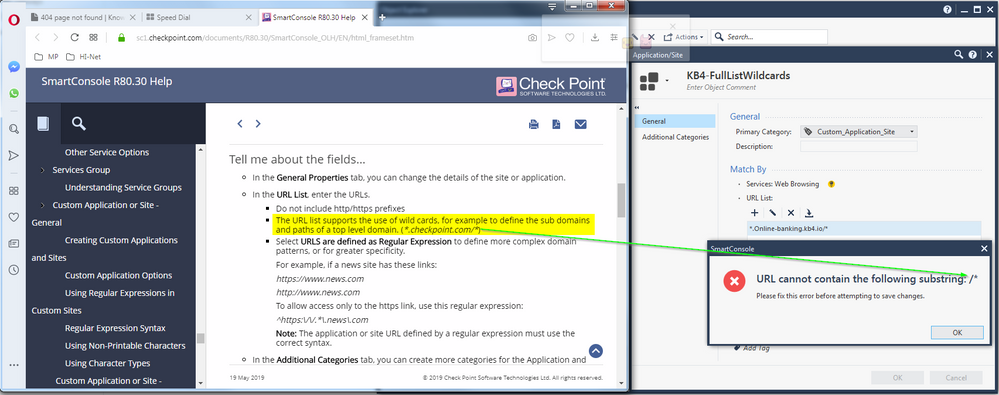
Wildcards in custom Apps
I am attempting to whitelist a long list of domains used by the user awareness training campaign.
And am seeing this:
Can we get some clarity on why this is not working and how to get around this issue.
The lab is 80.30EA, but the client is running 80.20.
Thank you,
Vladimir
16 Replies
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
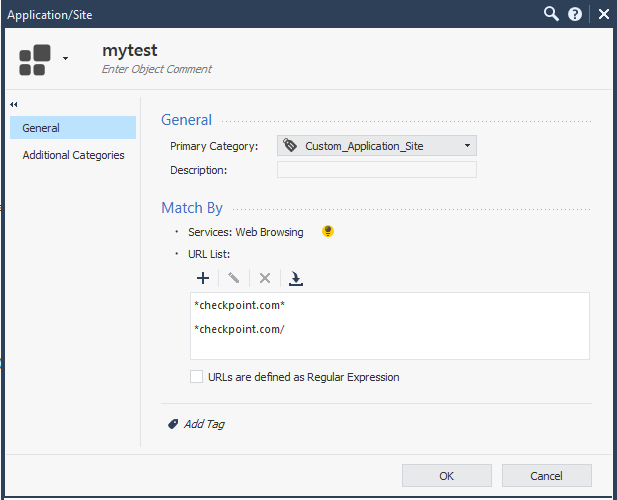
I think the actual issue is the /* at the end of your URL, not the * at the beginning.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I think the docs are in error in this case, the /* isn't required.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
it says it right there, remove / at the end of domain
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The editor will accept both / and * but not together.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Paul_Grigg , can you describe the anticipated behavior in each case?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Reminds me of sk106623 Custom Application/Site that was created to match a domain and sub-domains, is not matched by Application & URL Filtering policy...
CCSE CCTE CCSM SMB Specialist
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you @G_W_Albrecht , but CP puts out a warning sign in the same sk you are referencing.
Specifically, the notion of "not using REGEX with HTTPS sites unless inspection is enabled".
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What i mean is:
Application/Site was created with URL *.example.com to match domain "example.com" and sub-domains "*.example.com".
This will not work, only *example.com* - and this seems like your issue to me, when *example.com/* will not work, only *example.com/ or *example.com*.
RegEx might be helpful here when https inception is used...
CCSE CCTE CCSM SMB Specialist
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@G_W_Albrecht , if HTTPS inspection would've been enabled, perhaps.
This being said, I am hesitant to suggest enabling HTTPS inspection on anything not running R80.30, where it is significantly improved. But R80.30 still has some issues, (you can find one of the threads describing MABDA shortcomings).
Also, one of my acquaintances recently published a paper of how to use REGEX processing as a target for DOS and it was not pretty. So I am trying to stay away from its use unless absolutely necessary.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You did not state in your post that you do not use https, so i did falsely assume that.! R80.30 has several shortcomings - a MABDA HF (sk113410) should only be available in July, also a new build is planned for ca. 2 month from now. At least, we have a R80.30 MTA Update HF...
Using RegEx for DOS sounds interesting, please point out that paper to us all ! Up to now, the danger was that people use RegEx expressions with a wrong syntax (i at least had some customers that did that), so it did not work as expected.
CCSE CCTE CCSM SMB Specialist
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@G_W_Albrecht , I actually see relatively low number of companies adopting HTTPS inspection and am hoping to push them to it once 80.30 matures a bit.
You can read the short write-up here and check the links at the end for additional references:
https://medium.com/@somdevsangwan/exploiting-regular-expressions-2192dbbd6936
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you for the link ! Yes, you always better think twice when using RegEx - and nested repetition ops are not a good idea... But it is like i already said - you have to know a lot before using RexEx...
CCSE CCTE CCSM SMB Specialist
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Again regarding DOS on RegEx: With CP GWs, RegEx is used on the user URLs in APP CTRL and URL filtering. So an attack here has to come from the internal net, as requests from outside do not trigger APP CTRL and URL filtering.
So, the issues with RegEx are clearly not important when used with APP CTRL and URL filtering.
CCSE CCTE CCSM SMB Specialist
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@G_W_Albrecht , I suspect that it is still exploitable from outside using URL encoding, such as those described here:
https://nvisium.com/blog/2015/06/11/regex-regularly-exploitable.html
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It is only exploitable if your servers that can be reached from outside employ such RegEx to filter input - but the RegEx in APP CTRL and URLF will not be exploitable.
CCSE CCTE CCSM SMB Specialist
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 3 | |
| 3 | |
| 2 | |
| 2 | |
| 1 | |
| 1 | |
| 1 | |
| 1 | |
| 1 | |
| 1 |
Upcoming Events
Thu 02 May 2024 @ 10:00 AM (CEST)
CheckMates Live BeLux: How Can Check Point AI Copilot Assist You?Thu 02 May 2024 @ 04:00 PM (CEST)
CheckMates Live DACH - Keine Kompromisse - Sicheres SD-WANThu 02 May 2024 @ 10:00 AM (CEST)
CheckMates Live BeLux: How Can Check Point AI Copilot Assist You?Thu 02 May 2024 @ 04:00 PM (CEST)
CheckMates Live DACH - Keine Kompromisse - Sicheres SD-WANAbout CheckMates
Learn Check Point
Advanced Learning
YOU DESERVE THE BEST SECURITY
©1994-2024 Check Point Software Technologies Ltd. All rights reserved.
Copyright
Privacy Policy
Facts at a Glance
User Center