- CheckMates
- :
- Products
- :
- CloudMates Products
- :
- Cloud Network Security
- :
- Discussion
- :
- Re: Improving CloudGuard IaaS SKs
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Are you a member of CheckMates?
×- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Improving CloudGuard IaaS SKs
Hello Everyone,
Have you tried to deploy a CloudGuard IaaS solution and had a hard time? The SK was unclear? Had to ask someone to help you get it up and running?
I'm trying to find examples where the existing CloudGuard IaaS SKs were insufficient in helping you deploy the solution - either because your use case was complicated, or because the SK didn't go into enough details or was too hard to follow.
I'm trying to see if there are features or use cases where a video guide/walkthrough might help make a challenging solution SK easier to deploy.
If you have personal examples which you can share or ideas on how to improve existing SKs, please share them with us.
Help us improve ![]()
Yonatan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Yonatan,
Thanks for your constant push to improve cloud guard products. Usually the SK's generally discuss an ideal scenario and sometimes not based on customers use cases.
One example is - CHECK POINT CLOUDGUARD IAAS HIGH AVAILABILITY FOR MICROSOFT AZURE
R80.10 Deployment guide, it says the template will deploy two new subnets, it doesn't mention if it will let the users to deploy the clusters in an existing VNET and front and backend subnets
Another example is CDT sk111158. I am trying to see if I can use CDT for Azure CloudGuard IaaS clusters, but it doesn't provide more information
Under limitations, it mentions, CDT supports only CloudGuard for NSX Security Gateways.
Note: CDT recognizes each CloudGuard for NSX Security Gateway as a single Security Gateway, so do I have to assume it wont work for Azure IaaS clusters
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello Chandhrasekar,
First off - thank you for your feedback!
Regarding your comment about the CDT - the CDT is supported in Azure. The SK is indeed unclear, and I've passed your comment along to the SK owner we'll address this item.
Regarding your first comment about the HA solution - I'd appreciate some clarification. I looked at the solution and under "Step 1: Deploy with a Template in Azure" I found the following note:
Important - If you deploy the solution to an existing Virtual Network, confirm that there is an NSG associated with the frontend subnet that allows all inbound and outbound TCP and UDP traffic. An NSG is necessary to connect to Cluster Members successfully.
Is it because this note was at the bottom of the page? I've spoken to the SK owner and we'll move the note so that's it's easier to notice.
I'll also suggest a rewording of the text to make it clearer.
Is there anything else you can suggest?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,
Thanks for the reply. Glad to know CDT can support Azure clusters. We will use them for patching our gateways
Yes, I missed this section. Thanks for clarifying.
Important - If you deploy the solution to an existing Virtual Network, confirm that there is an NSG associated with the frontend subnet that allows all inbound and outbound TCP and UDP traffic. An NSG is necessary to connect to Cluster Members successfully.
Chandru
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Not sure if it is mentioned in the latest iteration of the SK, but it used to be that if we are to deploy AWS IaaS from the templates in the SK in the AWS account that DID NOT yet accepted Check Point's terms and conditions, the Cloud Formation would fail and you'd have to dig through its logs to figure out what was wrong.
Wouldn't be a bad thing to implement agreement check in the playbook and automatically prompt to accept terms and conditions as a part of a workflow.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello Vladimir,
Thanks for your feedback!
This information is mentioned in our deployment guide (if you find one where it's missing please let us know).
Your suggestion to add it to the template is a good one, but unfortunately, this is actually something that is forced on us by AWS.
However, there is a way to make it easier to find the reason for the failure.
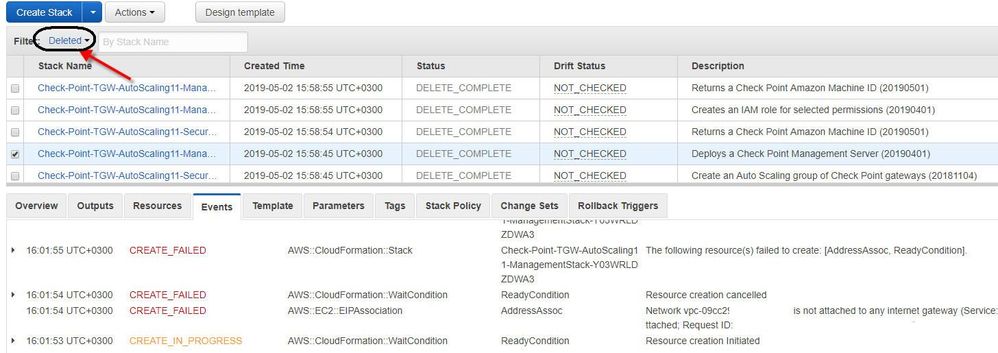
Often times the difficulty is from the fact that the errors are saved in nested stacks which are deleted, making the debugging process much harder.
However, if you check the upper right corner of your CloufFormation-Stacks page you'll notice that there is a filter option.
You can simply search through your deleted stacks to find the relevant error.
Please let me know if this information was helpful, and if you have any more questions or suggestions we'll be more than happy to address them!