- CheckMates
- :
- Products
- :
- CloudMates Products
- :
- Cloud Network Security
- :
- Discussion
- :
- AWS - Finally Allow You to Inspect Traffic Between...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Are you a member of CheckMates?
×- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
AWS - Finally Allow You to Inspect Traffic Between Subnets In a VPC
Until today, AWS didn't allow to add to a routing table a more specific route than the default VPC local route.
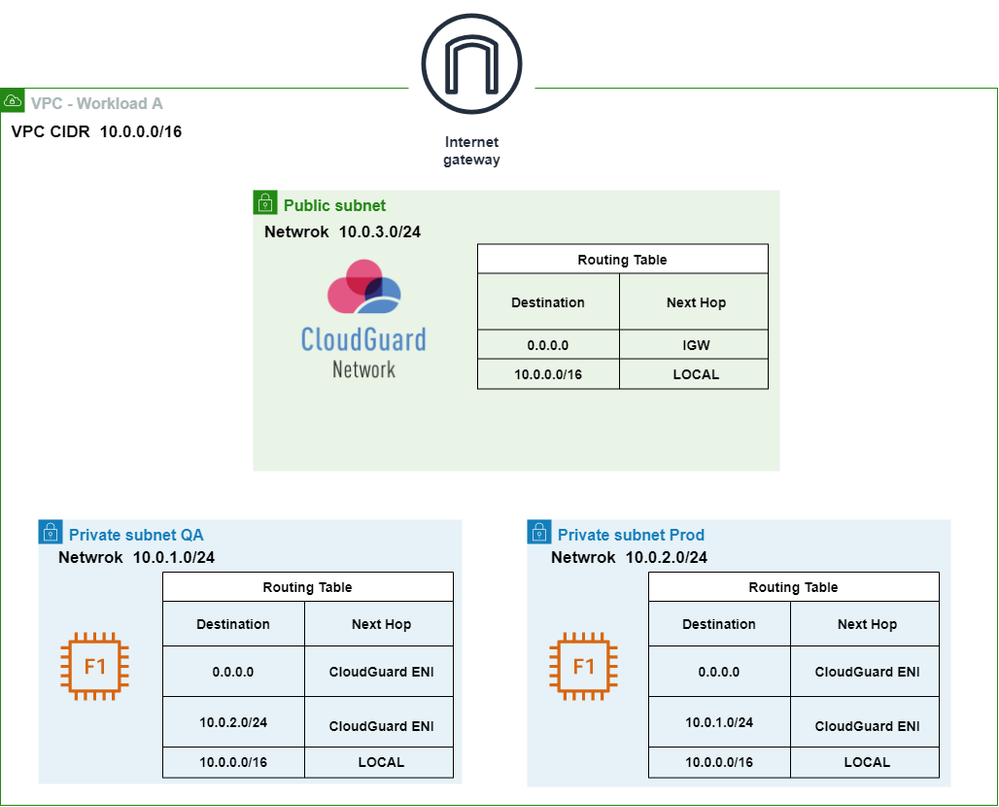
For example, when the VPC range is 10.0.0/16 and a subnet has 10.0.1.0/24, a route to 10.0.1.0/24 is more specific than a route to 10.0.0/16.
Routing tables no longer have this restriction. Routes in a routing table can have routes more specific than the default local route. You can use such a more specific route to send all traffic to a dedicated virtual appliance to inspect, analyze, or filter all traffic flowing between two subnets (east-west traffic). The route target can be the network interface (ENI) attached to a CloudGuard Gateway, an AWS Gateway Load Balancer (GWLB) endpoint to distribute traffic to multiple appliances for performance or high availability reasons.
It also allows inserting a virtual appliance between a subnet and an AWS Transit Gateway.
Check out the bellow simple use case
Traffic that is being sent between Subnet QA and Subnet Prod is now inspected by the CloudGuard Gateway.
This is the most basic use case, you can leverage it and use it in more complex use case where you have multiple VPC, TGW, and Gateway LoadBalnacer.
Feel free to comment and ask any question.
Leaderboard
Epsum factorial non deposit quid pro quo hic escorol.
| User | Count |
|---|---|
| 3 | |
| 2 | |
| 2 | |
| 1 |
Thu 09 May 2024 @ 05:00 PM (CEST)
Under the Hood: Automate Azure Virtual WAN security deployments with Terraform